好久好久没有更新了。。。你们等的急不急。。这不,我就姗姗来迟了。。。本文重点讲解一下iOS系统下的RSA加密解密问题。
一般为了安全,私钥是不会给前端暴露出来 的,只会通过私钥生成一个公开的公钥提供给外部对数据进行加密。将加密后的数据传给后端,后端使用私钥解密。比如支付宝支付,对接过这个支付的前端应该都知道。RSA的加密强度又有1024、2048之分,值越大,加密强度越高。
具体的使用场景分为两种:
1、自己有公钥文件,即后端生成的给你的一个.der文件,你将其放到你的项目中读取使用
2、你调用接口给你直接返回公钥内容,你只是根据公钥直接加密数据
针对以上两种使用场景,特封装以下两组方法,自己根据实际具体使用。
先上代码:头文件RSATools.h
//
// RSAtools.h
// SGBProject
//
// Created by carbonzhao on 2022/11/23.
// Copyright © 2022 ZJKJ. All rights reserved.
//
#import <Foundation/Foundation.h>
#import <UIKit/UIKit.h>
NS_ASSUME_NONNULL_BEGIN
@interface RSATools : NSObject
#pragma mark -公钥、私钥文件
/**
* 加密方法,如果你使用的是公钥文件
*
* @param str 需要加密的字符串
* @param path '.der'格式的公钥文件路径
*/
+ (NSString *)encryptPlainText:(NSString *)str publicKeyWithContentsOfFile:(NSString *)path;
/**
* 解密方法,如果你使用的是私钥文件,密码可为空,根据具体实际使用场景传值
*
* @param str 需要解密的字符串
* @param path '.p12'格式的私钥文件路径
* @param password 私钥文件密码
*/
+ (NSString *)decryptPlainText:(NSString *)str privateKeyWithContentsOfFile:(NSString *)path password:(NSString *)password;
#pragma mark - 公钥私钥数据
/**
* 加密方法
*
* @param str 需要加密的字符串,此时不存在文件访问密码,故而不需要设置密码
* @param pubKey 公钥字符串
*/
+ (NSString *)encryptPlainText:(NSString *)str publicKey:(NSString *)pubKey;
/**
* 解密方法
*
* @param str 需要解密的字符串
* @param privKey 私钥字符串
*/
+ (NSString *)decryptPlainText:(NSString *)str privateKey:(NSString *)privKey;
@end
NS_ASSUME_NONNULL_END
实现文件:RSATools.m
//
// RSATools.m
// RSA
//
// Created by carbonzhao on 2022/11/23.
//
#import "RSATools.h"
#import <Security/Security.h>
static NSString *base64_encode_data(NSData *data){
data = [data base64EncodedDataWithOptions:0];
NSString *ret = [[NSString alloc] initWithData:data encoding:NSUTF8StringEncoding];
return ret;
}
static NSData *base64_decode(NSString *str){
NSData *data = [[NSData alloc] initWithBase64EncodedString:str options:NSDataBase64DecodingIgnoreUnknownCharacters];
return data;
}
@implementation RSATools
#pragma mark - 使用'.der'公钥文件加密
//加密
+ (NSString *)encryptPlainText:(NSString *)str publicKeyWithContentsOfFile:(NSString *)path
{
if (!str || !path) return nil;
return [self encryptPlainText:str publicKeyRef:[self getPublicKeyRefWithContentsOfFile:path]];
}
//获取公钥
+ (SecKeyRef)getPublicKeyRefWithContentsOfFile:(NSString *)filePath
{
NSData *certData = [NSData dataWithContentsOfFile:filePath];
if (!certData) {
return nil;
}
SecCertificateRef cert = SecCertificateCreateWithData(NULL, (CFDataRef)certData);
SecKeyRef key = NULL;
SecTrustRef trust = NULL;
SecPolicyRef policy = NULL;
if (cert != NULL) {
policy = SecPolicyCreateBasicX509();
if (policy) {
if (SecTrustCreateWithCertificates((CFTypeRef)cert, policy, &trust) == noErr) {
CFErrorRef errRef;
if (SecTrustEvaluateWithError(trust, &errRef))
{
key = SecTrustCopyKey(trust);
}
}
}
}
if (policy) CFRelease(policy);
if (trust) CFRelease(trust);
if (cert) CFRelease(cert);
return key;
}
+ (NSString *)encryptPlainText:(NSString *)str publicKeyRef:(SecKeyRef)publicKeyRef
{
if(![str dataUsingEncoding:NSUTF8StringEncoding] || !publicKeyRef)
{
return nil;
}
NSData *data = [self encryptData:[str dataUsingEncoding:NSUTF8StringEncoding] withKeyRef:publicKeyRef];
NSString *ret = base64_encode_data(data);
return ret;
}
#pragma mark - 使用'.12'私钥文件解密
//解密
+ (NSString *)decryptPlainText:(NSString *)str privateKeyWithContentsOfFile:(NSString *)path password:(NSString *)password
{
if (!str || !path)
{
return nil;
}
if (!password)
{
password = @"";
}
return [self decryptPlainText:str privateKeyRef:[self getPrivateKeyRefWithContentsOfFile:path password:password]];
}
//获取私钥
+ (SecKeyRef)getPrivateKeyRefWithContentsOfFile:(NSString *)filePath password:(NSString*)password{
NSData *p12Data = [NSData dataWithContentsOfFile:filePath];
if (!p12Data)
{
return nil;
}
SecKeyRef privateKeyRef = NULL;
NSMutableDictionary * options = [[NSMutableDictionary alloc] init];
[options setObject: password forKey:(__bridge id)kSecImportExportPassphrase];
CFArrayRef items = CFArrayCreate(NULL, 0, 0, NULL);
OSStatus securityError = SecPKCS12Import((__bridge CFDataRef) p12Data, (__bridge CFDictionaryRef)options, &items);
if (securityError == noErr && CFArrayGetCount(items) > 0)
{
CFDictionaryRef identityDict = CFArrayGetValueAtIndex(items, 0);
SecIdentityRef identityApp = (SecIdentityRef)CFDictionaryGetValue(identityDict, kSecImportItemIdentity);
securityError = SecIdentityCopyPrivateKey(identityApp, &privateKeyRef);
if (securityError != noErr)
{
privateKeyRef = NULL;
}
}
CFRelease(items);
return privateKeyRef;
}
+ (NSString *)decryptPlainText:(NSString *)str privateKeyRef:(SecKeyRef)privKeyRef{
NSData *data = [[NSData alloc] initWithBase64EncodedString:str options:NSDataBase64DecodingIgnoreUnknownCharacters];
if (!privKeyRef)
{
return nil;
}
data = [self decryptData:data withKeyRef:privKeyRef];
NSString *ret = [[NSString alloc] initWithData:data encoding:NSUTF8StringEncoding];
return ret;
}
#pragma mark - 使用公钥字符串加密
/* START: Encryption with RSA public key */
//使用公钥字符串加密
+ (NSString *)encryptPlainText:(NSString *)str publicKey:(NSString *)pubKey
{
NSData *data = [self encryptData:[str dataUsingEncoding:NSUTF8StringEncoding] publicKey:pubKey];
NSString *ret = base64_encode_data(data);
return ret;
}
+ (NSData *)encryptData:(NSData *)data publicKey:(NSString *)pubKey
{
if(!data || !pubKey){
return nil;
}
SecKeyRef keyRef = [self addPublicKey:pubKey];
if(!keyRef){
return nil;
}
return [self encryptData:data withKeyRef:keyRef];
}
+ (SecKeyRef)addPublicKey:(NSString *)key
{
NSRange spos = [key rangeOfString:@"-----BEGIN PUBLIC KEY-----"];
NSRange epos = [key rangeOfString:@"-----END PUBLIC KEY-----"];
if(spos.location != NSNotFound && epos.location != NSNotFound){
NSUInteger s = spos.location + spos.length;
NSUInteger e = epos.location;
NSRange range = NSMakeRange(s, e-s);
key = [key substringWithRange:range];
}
key = [key stringByReplacingOccurrencesOfString:@"\r" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@"\n" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@"\t" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@" " withString:@""];
// This will be base64 encoded, decode it.
NSData *data = base64_decode(key);
data = [self stripPublicKeyHeader:data];
if(!data){
return nil;
}
//a tag to read/write keychain storage
NSString *tag = @"RSAUtil_PubKey";
NSData *d_tag = [NSData dataWithBytes:[tag UTF8String] length:[tag length]];
// Delete any old lingering key with the same tag
NSMutableDictionary *publicKey = [[NSMutableDictionary alloc] init];
[publicKey setObject:(__bridge id) kSecClassKey forKey:(__bridge id)kSecClass];
[publicKey setObject:(__bridge id) kSecAttrKeyTypeRSA forKey:(__bridge id)kSecAttrKeyType];
[publicKey setObject:d_tag forKey:(__bridge id)kSecAttrApplicationTag];
SecItemDelete((__bridge CFDictionaryRef)publicKey);
// Add persistent version of the key to system keychain
[publicKey setObject:data forKey:(__bridge id)kSecValueData];
[publicKey setObject:(__bridge id) kSecAttrKeyClassPublic forKey:(__bridge id)
kSecAttrKeyClass];
[publicKey setObject:[NSNumber numberWithBool:YES] forKey:(__bridge id)
kSecReturnPersistentRef];
CFTypeRef persistKey = nil;
OSStatus status = SecItemAdd((__bridge CFDictionaryRef)publicKey, &persistKey);
if (persistKey != nil){
CFRelease(persistKey);
}
if ((status != noErr) && (status != errSecDuplicateItem)) {
return nil;
}
[publicKey removeObjectForKey:(__bridge id)kSecValueData];
[publicKey removeObjectForKey:(__bridge id)kSecReturnPersistentRef];
[publicKey setObject:[NSNumber numberWithBool:YES] forKey:(__bridge id)kSecReturnRef];
[publicKey setObject:(__bridge id) kSecAttrKeyTypeRSA forKey:(__bridge id)kSecAttrKeyType];
// Now fetch the SecKeyRef version of the key
SecKeyRef keyRef = nil;
status = SecItemCopyMatching((__bridge CFDictionaryRef)publicKey, (CFTypeRef *)&keyRef);
if(status != noErr){
return nil;
}
return keyRef;
}
+ (NSData *)stripPublicKeyHeader:(NSData *)d_key{
// Skip ASN.1 public key header
if (d_key == nil) return(nil);
unsigned long len = [d_key length];
if (!len) return(nil);
unsigned char *c_key = (unsigned char *)[d_key bytes];
unsigned int idx = 0;
if (c_key[idx++] != 0x30) return(nil);
if (c_key[idx] > 0x80) idx += c_key[idx] - 0x80 + 1;
else idx++;
// PKCS #1 rsaEncryption szOID_RSA_RSA
static unsigned char seqiod[] =
{ 0x30, 0x0d, 0x06, 0x09, 0x2a, 0x86, 0x48, 0x86, 0xf7, 0x0d, 0x01, 0x01,
0x01, 0x05, 0x00 };
if (memcmp(&c_key[idx], seqiod, 15)) return(nil);
idx += 15;
if (c_key[idx++] != 0x03) return(nil);
if (c_key[idx] > 0x80) idx += c_key[idx] - 0x80 + 1;
else idx++;
if (c_key[idx++] != '\0') return(nil);
// Now make a new NSData from this buffer
return ([NSData dataWithBytes:&c_key[idx] length:len - idx]);
}
+ (NSData *)encryptData:(NSData *)data withKeyRef:(SecKeyRef) keyRef{
const uint8_t *srcbuf = (const uint8_t *)[data bytes];
size_t srclen = (size_t)data.length;
size_t block_size = SecKeyGetBlockSize(keyRef) * sizeof(uint8_t);
void *outbuf = malloc(block_size);
size_t src_block_size = block_size - 11;
NSMutableData *ret = [[NSMutableData alloc] init];
for(int idx=0; idx<srclen; idx+=src_block_size){
//NSLog(@"%d/%d block_size: %d", idx, (int)srclen, (int)block_size);
size_t data_len = srclen - idx;
if(data_len > src_block_size){
data_len = src_block_size;
}
size_t outlen = block_size;
OSStatus status = noErr;
status = SecKeyEncrypt(keyRef,
kSecPaddingPKCS1,
srcbuf + idx,
data_len,
outbuf,
&outlen
);
if (status != 0) {
NSLog(@"SecKeyEncrypt fail. Error Code: %d", status);
ret = nil;
break;
}else{
[ret appendBytes:outbuf length:outlen];
}
}
free(outbuf);
CFRelease(keyRef);
return ret;
}
/* END: Encryption with RSA public key */
#pragma mark - 使用私钥字符串解密
/* START: Decryption with RSA private key */
//使用私钥字符串解密
+ (NSString *)decryptPlainText:(NSString *)str privateKey:(NSString *)privKey
{
if (!str) return nil;
NSData *data = [[NSData alloc] initWithBase64EncodedString:str options:NSDataBase64DecodingIgnoreUnknownCharacters];
data = [self decryptData:data privateKey:privKey];
NSString *ret = [[NSString alloc] initWithData:data encoding:NSUTF8StringEncoding];
return ret;
}
+ (NSData *)decryptData:(NSData *)data privateKey:(NSString *)privKey
{
if(!data || !privKey){
return nil;
}
SecKeyRef keyRef = [self addPrivateKey:privKey];
if(!keyRef){
return nil;
}
return [self decryptData:data withKeyRef:keyRef];
}
+ (SecKeyRef)addPrivateKey:(NSString *)key
{
NSRange spos = [key rangeOfString:@"-----BEGIN RSA PRIVATE KEY-----"];
NSRange epos = [key rangeOfString:@"-----END RSA PRIVATE KEY-----"];
if(spos.location != NSNotFound && epos.location != NSNotFound){
NSUInteger s = spos.location + spos.length;
NSUInteger e = epos.location;
NSRange range = NSMakeRange(s, e-s);
key = [key substringWithRange:range];
}
key = [key stringByReplacingOccurrencesOfString:@"\r" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@"\n" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@"\t" withString:@""];
key = [key stringByReplacingOccurrencesOfString:@" " withString:@""];
// This will be base64 encoded, decode it.
NSData *data = base64_decode(key);
data = [self stripPrivateKeyHeader:data];
if(!data){
return nil;
}
//a tag to read/write keychain storage
NSString *tag = @"RSAUtil_PrivKey";
NSData *d_tag = [NSData dataWithBytes:[tag UTF8String] length:[tag length]];
// Delete any old lingering key with the same tag
NSMutableDictionary *privateKey = [[NSMutableDictionary alloc] init];
[privateKey setObject:(__bridge id) kSecClassKey forKey:(__bridge id)kSecClass];
[privateKey setObject:(__bridge id) kSecAttrKeyTypeRSA forKey:(__bridge id)kSecAttrKeyType];
[privateKey setObject:d_tag forKey:(__bridge id)kSecAttrApplicationTag];
SecItemDelete((__bridge CFDictionaryRef)privateKey);
// Add persistent version of the key to system keychain
[privateKey setObject:data forKey:(__bridge id)kSecValueData];
[privateKey setObject:(__bridge id) kSecAttrKeyClassPrivate forKey:(__bridge id)
kSecAttrKeyClass];
[privateKey setObject:[NSNumber numberWithBool:YES] forKey:(__bridge id)
kSecReturnPersistentRef];
CFTypeRef persistKey = nil;
OSStatus status = SecItemAdd((__bridge CFDictionaryRef)privateKey, &persistKey);
if (persistKey != nil){
CFRelease(persistKey);
}
if ((status != noErr) && (status != errSecDuplicateItem)) {
return nil;
}
[privateKey removeObjectForKey:(__bridge id)kSecValueData];
[privateKey removeObjectForKey:(__bridge id)kSecReturnPersistentRef];
[privateKey setObject:[NSNumber numberWithBool:YES] forKey:(__bridge id)kSecReturnRef];
[privateKey setObject:(__bridge id) kSecAttrKeyTypeRSA forKey:(__bridge id)kSecAttrKeyType];
// Now fetch the SecKeyRef version of the key
SecKeyRef keyRef = nil;
status = SecItemCopyMatching((__bridge CFDictionaryRef)privateKey, (CFTypeRef *)&keyRef);
if(status != noErr){
return nil;
}
return keyRef;
}
+ (NSData *)stripPrivateKeyHeader:(NSData *)d_key
{
// Skip ASN.1 private key header
if (d_key == nil) return(nil);
unsigned long len = [d_key length];
if (!len) return(nil);
unsigned char *c_key = (unsigned char *)[d_key bytes];
unsigned int idx = 22; //magic byte at offset 22
if (0x04 != c_key[idx++]) return nil;
//calculate length of the key
unsigned int c_len = c_key[idx++];
int det = c_len & 0x80;
if (!det) {
c_len = c_len & 0x7f;
} else {
int byteCount = c_len & 0x7f;
if (byteCount + idx > len) {
//rsa length field longer than buffer
return nil;
}
unsigned int accum = 0;
unsigned char *ptr = &c_key[idx];
idx += byteCount;
while (byteCount) {
accum = (accum << 8) + *ptr;
ptr++;
byteCount--;
}
c_len = accum;
}
// Now make a new NSData from this buffer
return [d_key subdataWithRange:NSMakeRange(idx, c_len)];
}
+ (NSData *)decryptData:(NSData *)data withKeyRef:(SecKeyRef) keyRef{
const uint8_t *srcbuf = (const uint8_t *)[data bytes];
size_t srclen = (size_t)data.length;
size_t block_size = SecKeyGetBlockSize(keyRef) * sizeof(uint8_t);
UInt8 *outbuf = malloc(block_size);
size_t src_block_size = block_size;
NSMutableData *ret = [[NSMutableData alloc] init];
for(int idx=0; idx<srclen; idx+=src_block_size){
//NSLog(@"%d/%d block_size: %d", idx, (int)srclen, (int)block_size);
size_t data_len = srclen - idx;
if(data_len > src_block_size){
data_len = src_block_size;
}
size_t outlen = block_size;
OSStatus status = noErr;
status = SecKeyDecrypt(keyRef,
kSecPaddingNone,
srcbuf + idx,
data_len,
outbuf,
&outlen
);
if (status != 0) {
NSLog(@"SecKeyEncrypt fail. Error Code: %d", status);
ret = nil;
break;
}else{
//the actual decrypted data is in the middle, locate it!
int idxFirstZero = -1;
int idxNextZero = (int)outlen;
for ( int i = 0; i < outlen; i++ ) {
if ( outbuf[i] == 0 ) {
if ( idxFirstZero < 0 ) {
idxFirstZero = i;
} else {
idxNextZero = i;
break;
}
}
}
[ret appendBytes:&outbuf[idxFirstZero+1] length:idxNextZero-idxFirstZero-1];
}
}
free(outbuf);
CFRelease(keyRef);
return ret;
}
@end
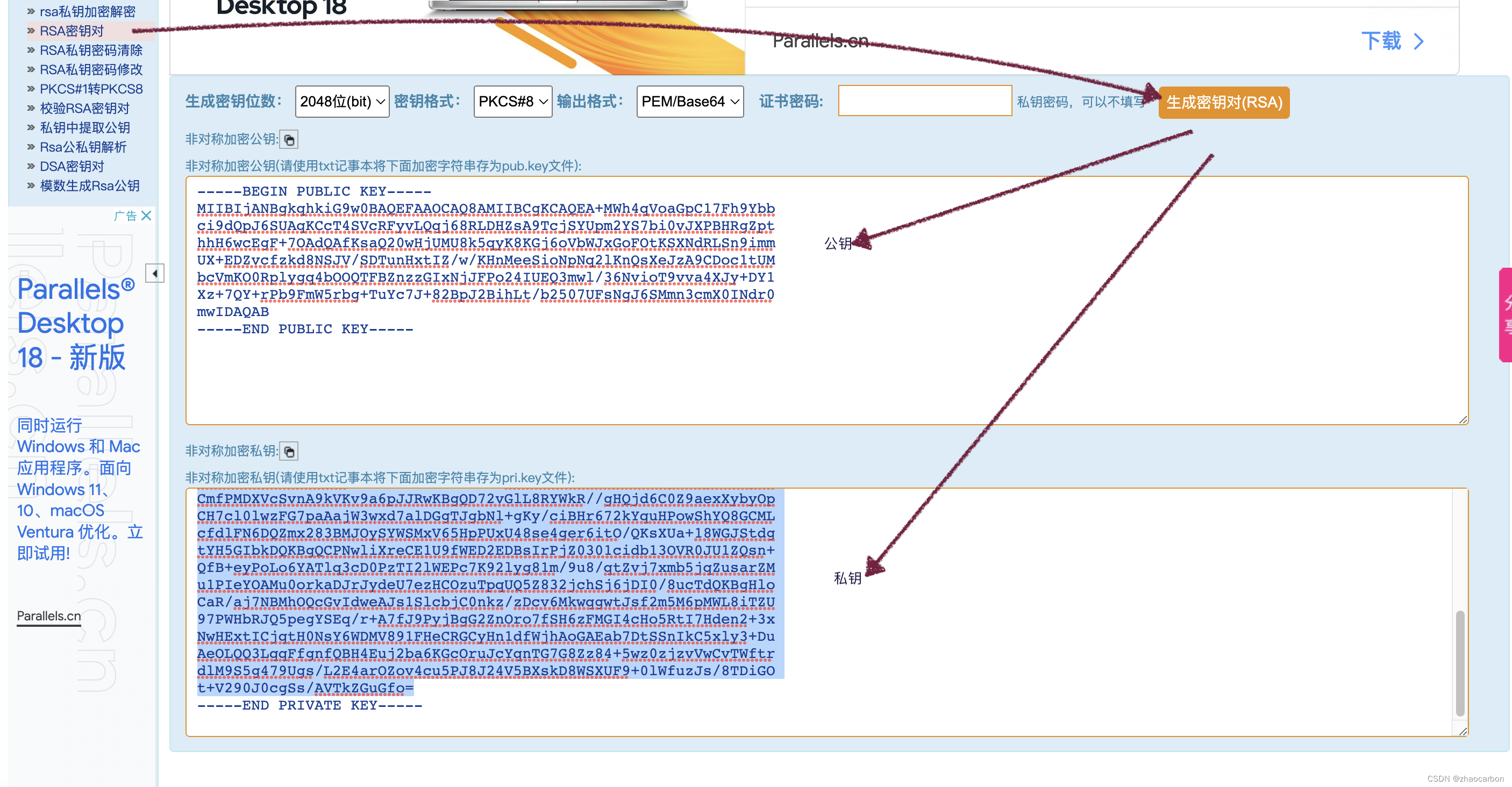
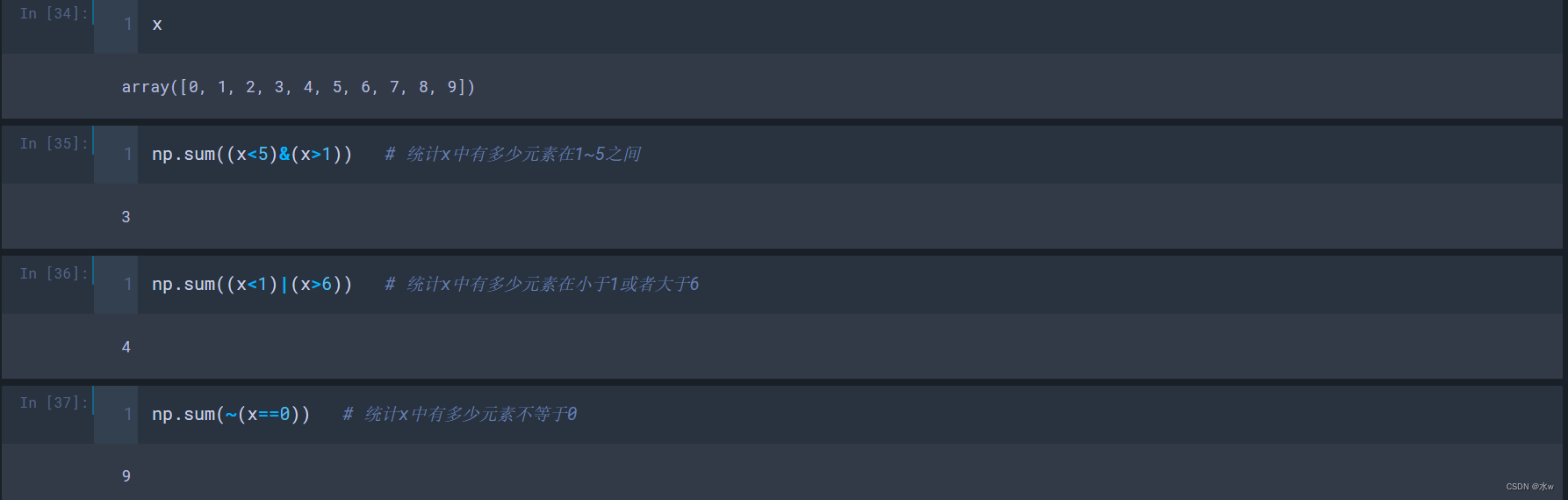
测试方法:首先先登录下面的网站:http://web.chacuo.net/netrsakeypair, ,这是一个在线生成RSA秘钥的网站, 生成公钥和秘钥后, 复制出来用于测试.注意使用时要删除掉前面:
-----BEGIN PUBLIC KEY-----
-----END PUBLIC KEY-----
-----BEGIN PRIVATE KEY-----
-----END PRIVATE KEY-----
这两组标签,同时删除回车换行符!!!!。
NSString *encryptStr = [RSATools encryptPlainText:originalString publicKey:@"MIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEA+MWh4qVoaGpC17Fh9Ybbci9dQpJ6SUAqKCcT4SVcRFyvLQqj68RLDHZsA9TcjSYUpm2YS7bi0vJXPBHRgZpthhH6wcEgF+7OAdQAfKsaQ20wHjUMU8k5qyK8KGj6oVbWJxGoFOtKSXNdRLSn9immUX+EDZvcfzkd8NSJV/SDTunHxtIZ/w/KHnMeeSioNpNq2lKnQsXeJzA9CDoc1tUMbcVmKO0Rplygq4bOOQTFBZnzzGIxNjJFPo24IUEQ3mwl/36NvioT9vva4XJy+DY1Xz+7QY+rPb9FmW5rbg+TuYc7J+82BpJ2BihLt/b2507UFsNgJ6SMmn3cmX0INdr0mwIDAQAB"];
NSLog(@"加密前:%@", originalString);
NSLog(@"加密后:%@", encryptStr);
NSString *deText = [RSATools decryptPlainText:encryptStr privateKey:@"MIIEvQIBADANBgkqhkiG9w0BAQEFAASCBKcwggSjAgEAAoIBAQD4xaHipWhoakLXsWH1httyL11CknpJQCooJxPhJVxEXK8tCqPrxEsMdmwD1NyNJhSmbZhLtuLS8lc8EdGBmm2GEfrBwSAX7s4B1AB8qxpDbTAeNQxTyTmrIrwoaPqhVtYnEagU60pJc11EtKf2KaZRf4QNm9x/OR3w1IlX9INO6cfG0hn/D8oecx55KKg2k2raUqdCxd4nMD0IOhzW1QxtxWYo7RGmXKCrhs45BMUFmfPMYjE2MkU+jbghQRDebCX/fo2+KhP2+9rhcnL4NjVfP7tBj6s9v0WZbmtuD5O5hzsn7zYGknYGKEu39vbnTtQWw2AnpIyafdyZfQg12vSbAgMBAAECggEAUlBqiWj7zBjk9yO9axVtRTIA5Mc86UHu8QxFGqlXB1O3ruqnZJq1znDcusPTGm0wRgVbcCoakXwYe0rWDNFBTixi0XuKmACvb5Fre9TNwuO9GTGqW4ropwS+R4y86WenQpQoDovwL6+Ze+Ne9CfB3ZOY6TvaUMpgatCYhV7ll9VCAMn3+KB6cxZPqByx3W0MdGt7LlKENGs7ARrSxfd33WHSQMfVGhTmt1or6OC+kVZ1rXNkuGVuQzBqA4iVKbDAhly9sTmyUPUaDloVrG2FH7+Ab2d9G/GLt22xU7Om8HlWTmGJGIy4F9/a53Kzx5NYwHpKLdDAzyAuziSS8nyF6QKBgQD83bLm7/FwbPd3n9/JODbNdFrDoJRZVTKKDgqnzsD1YIaeN2QU4ifBu2fnhOUwSn8f7VJniafps/wSnfXhcrLdQw0jJEFccvzmM+WuJu0ZLHsHCZr/Y/ex2l7GiawFNc3iDFCspWnnpJxLSyzWCmfPMDXVcSvnA9kVKv9a6pJJRwKBgQD72vGlL8RYWkR//gHQjd6C0Z9aexXybyOpCH7cl0lwzFG7paAajW3wxd7alDGgTJgbNl+gKy/ciBHr672kYquHPowShYQ8GCMLcfdlFN6DQZmx283BMJOySYWSMxV65HpPUxU48se4ger6itO/QKsXUa+18WGJStdgtYH5GIbkDQKBgQCPNwliXreCE1U9fWED2EDBsIrPjZ0301cidb13OVR0JU1ZQsn+QfB+eyPoLo6YATlq3cD0PzTI2lWEPc7K92lyg81m/9u8/qtZvj7xmb5jqZusarZMu1PIeYOAMu0orkaDJrJydeU7ezHCOzuTpqUQ5Z832jchSj6jDI0/8ucTdQKBgHloCaR/aj7NBMhOQcGvIdweAJs1SlcbjC0nkz/zDcv6MkwqgwtJsf2m5M6pMWL8iTZU97PWHbRJQ5pegYSEq/r+A7fJ9PyjBgG2ZnOro7fSH6zFMGI4cHo5RtI7Hden2+3xNwHExtICjqtH0NsY6WDMV891FHeCRGCyHn1dfWjhAoGAEab7DtSSnIkC5xly3+DuAeOLQQ3LqqFfgnfQBH4Euj2ba6KGcOruJcYqnTG7G8Zz84+5wz0zjzvVwCvTWftrdlM9S5g479Ugs/L2E4arOZov4cu5PJ8J24V5BXskD8WSXUF9+0lWfuzJs/8TDiGOt+V290J0cgSs/AVTkZGuGfo="];
NSLog(@"解密后:%@", deText);


![[附源码]SSM计算机毕业设计基于的花店后台管理系统JAVA](https://img-blog.csdnimg.cn/d8ad966834bc4016960c63adf5ad82bf.png)

![[附源码]计算机毕业设计JAVA课后作业提交系统关键技术研究与系统实现](https://img-blog.csdnimg.cn/b9656591cae548028c70b0fd0b15f724.png)
![[附源码]计算机毕业设计JAVA课堂点名系统](https://img-blog.csdnimg.cn/3a015597afd94e18a2cda5488d2c7dc6.png)

![[附源码]计算机毕业设计JAVA科院垃圾分类系统](https://img-blog.csdnimg.cn/7f49d79f67324a979be7256b57cbc4cd.png)


