oscp_靶场练习_Lame
1. nmap扫描:
└─# nmap 10.10.10.3
Starting Nmap 7.92 ( https://nmap.org ) at 2023-02-20 23:21 EST
Nmap scan report for 10.10.10.3
Host is up (0.22s latency).
Not shown: 996 filtered tcp ports (no-response)
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
139/tcp open netbios-ssn
445/tcp open microsoft-ds

看端看情况是Windows系统。
2. nmap使用默认的脚本进行安全性检测
┌──(root㉿kali)-[~/Desktop]
└─# nmap 10.10.10.3 -sC
Starting Nmap 7.92 ( https://nmap.org ) at 2023-02-20 23:50 EST
Nmap scan report for 10.10.10.3
Host is up (0.23s latency).
Not shown: 996 filtered tcp ports (no-response)
PORT STATE SERVICE
21/tcp open ftp
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 10.10.14.4
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| vsFTPd 2.3.4 - secure, fast, stable
|_End of status
22/tcp open ssh
| ssh-hostkey:
| 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA)
|_ 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA)
139/tcp open netbios-ssn
445/tcp open microsoft-ds
Host script results:
| smb-os-discovery:
| OS: Unix (Samba 3.0.20-Debian)
| Computer name: lame
| NetBIOS computer name:
| Domain name: hackthebox.gr
| FQDN: lame.hackthebox.gr
|_ System time: 2023-02-20T23:50:59-05:00
|_smb2-time: Protocol negotiation failed (SMB2)
|_clock-skew: mean: 2h30m27s, deviation: 3h32m10s, median: 25s
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
Nmap done: 1 IP address (1 host up) scanned in 55.29 seconds
3.发现ftp可以匿名登陆,尝试利用
利用:
vsFTPd 2.3.4 笑脸后门,利用失败
https://blog.csdn.net/weixin_52347768/article/details/124594516
https://blog.csdn.net/zwm_20211031_475/article/details/126692988
ftp命令
操作:https://blog.csdn.net/weixin_50196615/article/details/122153604

3. 22端口利用
使用hydra 对ssh 22端口爆破,略…
4. 139,445端口利用
445端口的理解与利用:
https://blog.csdn.net/hanghangaidoudou/article/details/75102940
smbclient使用 #
https://www.bbsmax.com/A/KE5QN8n0dL/
smbclient匿名登陆尝试
smbclient -N -L 10.10.10.3 -N 匿名无密码登陆, -L 列出目标主机的共享
smbclient -N //10.10.10.3/tmp
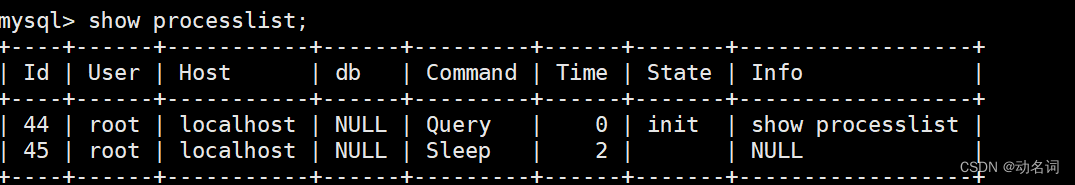
smb: \> ls # 列出共享目录ls中的内容


nmap看到samba是3.0.20版本,使用msf进行payload搜索利用:

发现漏洞模块利用成功:

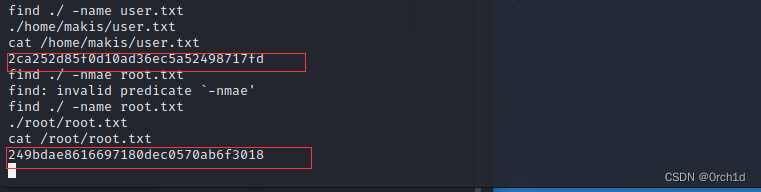
获得root权限,寻找flag:
2ca252d85f0d10ad36ec5a52498717fd
249bdae8616697180dec0570ab6f3018
参考:
https://www.cnblogs.com/chengwenjun/p/16548138.html
https://infosecwriteups.com/htb-lame-writeup-e47100aea88b
https://0xdf.gitlab.io/2020/04/07/htb-lame.html
总结:
ftp的利用
smbclient利用