ModSecurity安装教程加核心防御规则
资源宝分享:www.httple.net
ModSecurity简介
ModSecurity-官网: http://www.modsecurity.cn
ModSecurity是目前世界上使用最多的开源WAF产品,可谓是WAF界的鼻祖,跨平台的Web应用防火墙(WAF),被称为WAF界的“瑞士军刀”。它可以通过检查Web服务接收到的数据,以及发送出去的数据来对网站进行安全防护
功能介绍
SQL Injection (SQLi):阻止SQL注入
Cross Site Scripting (XSS):阻止跨站脚本攻击
Local File Inclusion (LFI):阻止利用本地文件包含漏洞进行攻击
Remote File Inclusione(RFI):阻止利用远程文件包含漏洞进行攻击
Remote Code Execution (RCE):阻止利用远程命令执行漏洞进行攻击
PHP Code Injectiod:阻止PHP代码注入
HTTP Protocol Violations:阻止违反HTTP协议的恶意访问
HTTPoxy:阻止利用远程代理感染漏洞进行攻击
Sshllshock:阻止利用Shellshock漏洞进行攻击
Session Fixation:阻止利用Session会话ID不变的漏洞进行攻击
Scanner Detection:阻止黑客扫描网站
Metadata/Error Leakages:阻止源代码/错误信息泄露
Project Honey Pot Blacklist:蜜罐项目黑名单
GeoIP Country Blocking:根据判断IP地址归属地来进行IP阻断
下面来实战
准备一个纯洁系统,如果安装nginx先卸载
nginx 卸载
ps -ef | grep nginx
kill -9 pid
删除nginx文件夹whereis nginx
whereis nginx
rm -rf *
yum清理nginx
yum remove nginx
相关依赖安装
yum install -y wget epel-release
yum install -y gcc-c++ flex bison yajl yajl-devel curl-devel curl GeoIP-devel doxygen zlib-devel pcre-devel lmdb-devel libxml2-devel ssdeep-devel lua-devel libtool autoconf automake
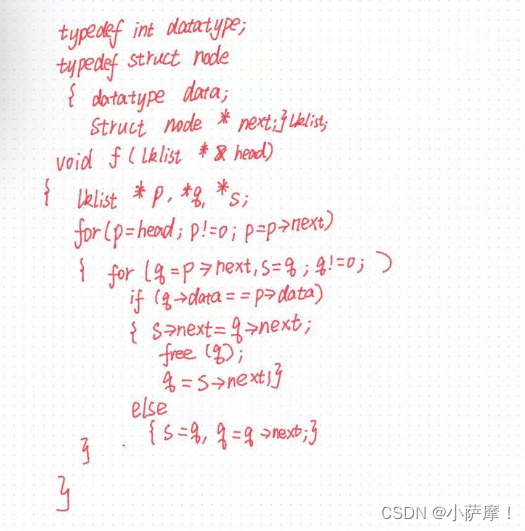
Modsecurity 安装
cd /home/modsecurity
wget http://www.modsecurity.cn/download/modsecurity/modsecurity-v3.0.4.tar.gz
tar -zxvf modsecurity-v3.0.4.tar.gz
mv modsecurity-v3.0.4 /usr/local/modsecurity/modsecurity
sh build.sh
./configure
make
make install
请忽略 sh build.sh 中有关的git错误:
fatal: Not a git repository (or any of the parent directories): .git
ModSecurity-nginx 安装
ModSecurity-nginx 下载地址:
https://github.com/SpiderLabs/ModSecurity-nginx
mkdir modsecurity-nginx
unzip ModSecurity-nginx-master.zip
mv ModSecurity-nginx-master /usr/local/modsecurity-nginx
nginx 安装
mkdir /home/nginx
cd /home/nginx
wget http://nginx.org/download/nginx-1.16.1.tar.gz
tar -zxvf nginx-1.16.1.tar.gz
cd nginx-1.16.1/
./configure --add-module=/usr/local/modsecurity-nginx
make
make install
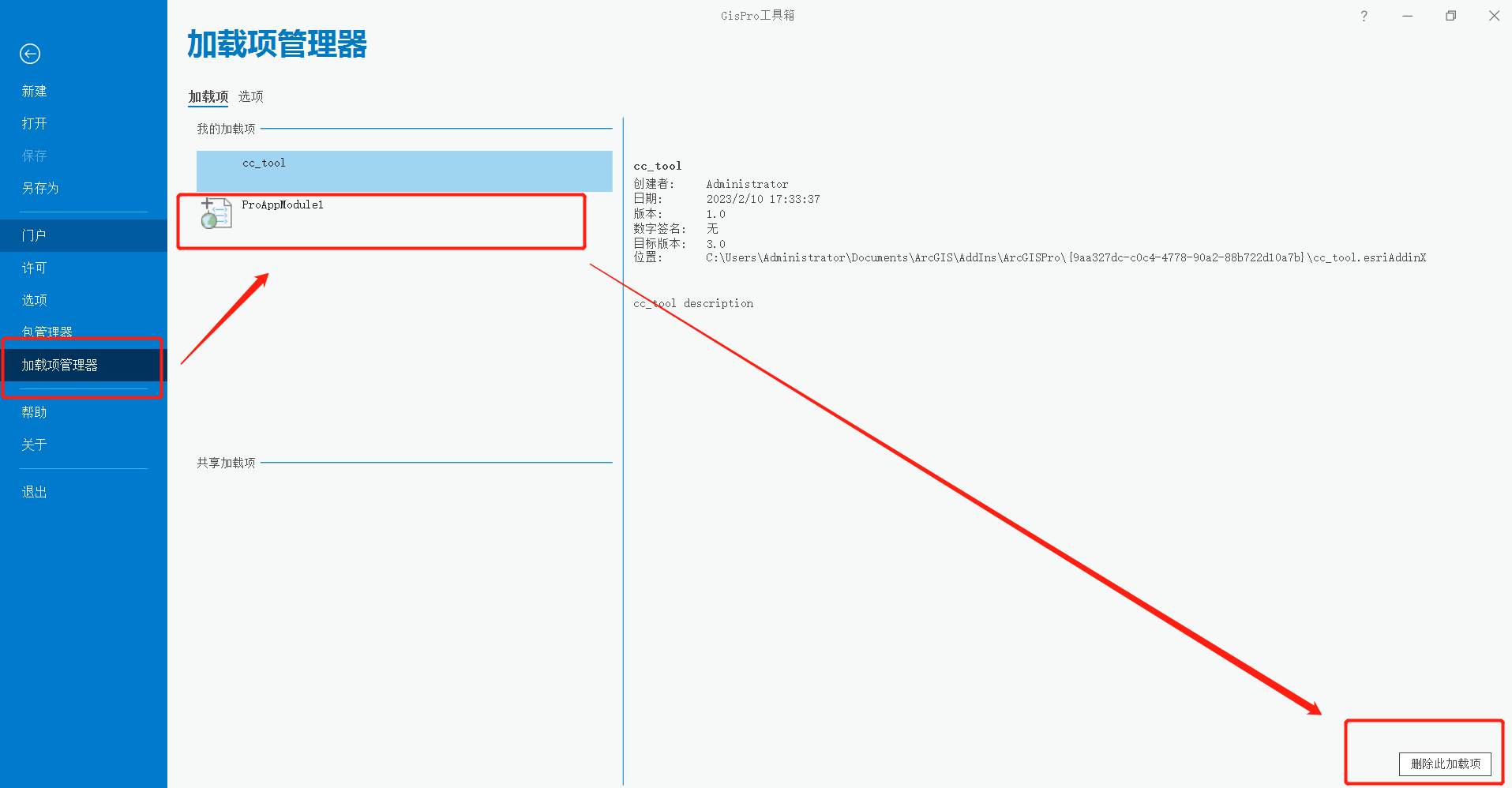
nginx + ModSecurity-nginx 配置
在nginx的conf下创建文件夹modsecurity
并把 /usr/local/modsecurity/ 下的配置文件
modsecurity.conf-recommended > /usr/local/nginx/conf/modsecurity/modsecurity.conf 移动并重命名
unicode.mapping > /usr/local/nginx/conf/modsecurity
mkdir /usr/local/nginx/conf/modsecurity
cd /usr/local/modsecurity/
cp modsecurity.conf-recommended /usr/local/nginx/conf/modsecurity/modsecurity.conf
cp unicode.mapping /usr/local/nginx/conf/modsecurity
nginx.conf
在http或server节点中添加以下内容(在http节点添加表示全局配置,在server节点添加表示为指定网站配置)
modsecurity on;
modsecurity_rules_file /usr/local/nginx/conf/modsecurity/modsecurity.conf;
modsecurity.conf
SecRuleEngine DetectionOnly > SecRuleEngine On
#SecRuleEngine DetectionOnly
SecRuleEngine On
确保ModSecurity在记录审计日志时保存请求体IJ 改为 C
#SecAuditLogParts ABIJDEFHZ
SecAuditLogParts ABCDEFHZ
添加以下内容:
Include /usr/local/nginx/conf/modsecurity/crs-setup.conf
Include /usr/local/nginx/conf/modsecurity/rules/*.conf
配置防御规则文件
下载规则文件压缩包
cd /home/modsecurity
wget http://www.modsecurity.cn/download/corerule/owasp-modsecurity-crs-3.3-dev.zip
unzip owasp-modsecurity-crs-3.3-dev.zip
cd owasp-modsecurity-crs-3.3-dev
复制crs-setup.conf.example到/usr/local/nginx/conf/modsecurity/下并重命名为crs-setup.conf
cp crs-setup.conf.example /usr/local/nginx/conf/modsecurity/crs-setup.conf
复制rules文件夹到==/usr/local/nginx/conf/modsecurity/=
修改文件名称,去掉 .example
REQUEST-900-EXCLUSION-RULES-BEFORE-CRS.conf.example
RESPONSE-999-EXCLUSION-RULES-AFTER-CRS.conf.example
cp -r rules /usr/local/nginx/conf/modsecurity/
cd /usr/local/nginx/conf/modsecurity/rules
mv REQUEST-900-EXCLUSION-RULES-BEFORE-CRS.conf.example REQUEST-900-EXCLUSION-RULES-BEFORE-CRS.conf
mv RESPONSE-999-EXCLUSION-RULES-AFTER-CRS.conf.example RESPONSE-999-EXCLUSION-RULES-AFTER-CRS.conf
重启nginx
/usr/local/nginx/sbin/nginx -c /usr/local/nginx/conf/nginx.conf
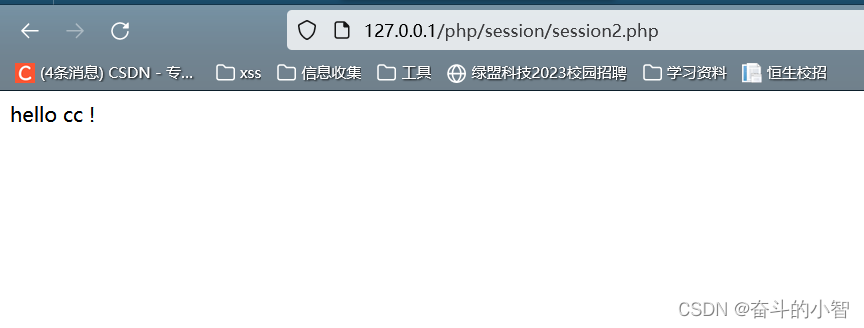
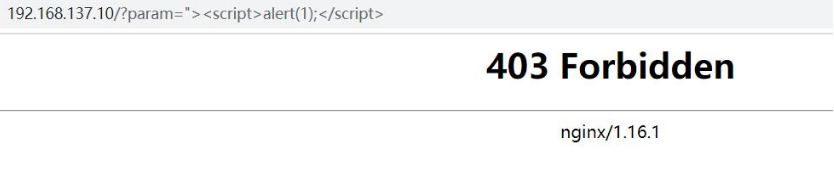
测试是否安装成功
可以清楚的看到后两条测试结果403,被拦截成功
Modsecurity的规则库生成的规则内容参考
Modsecurity规则库功能说明
- 请求的URI为“/admin”
- 描述为"测试"
- 请求方式为POST
- 请求体中的参数为“id”
SecRule REQUEST_FILENAME "@beginsWith /admin" "chain,msg:测试,phase:2,deny,nolog,auditlog,id:450003,t:lowercase"
SecRule REQUEST_METHOD "^(?:POST)$" "chain,t:none"
SecRule REQUEST_BODY "@containsWord id" "t:lowercase"
0x01 Apache Cocoon Xml 注入 CVE-2020-11991
防御规则链如下:
-
规则设置请求方式为POST,在使用规则之前验证有效请求POST
-
规则设置访问路径为“/v2/api/product/manger/getInfo”
-
规则设置访问的数据传输的内容正则匹配是否存在系统字段
SecRule REQUEST_METHOD "^POST$" "chain,msg: 'Apache Cocoon Xml Injection(CVE-2020-1191)',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/v2/api/product/manger/getInfo" "chain"
SecRule REQUEST_BODY:data "@rx (?!)system"
0x02 Apache Solr任意文件读取漏洞
防御规则链如下:
-
规则设置请求方式为GET,在使用规则之前验证有效请求GET
-
规则设置访问路径为“/solr/admin/cores?indexInfo=false&wt=json”
-
规则设置检测数据字段中有无文件参数
SecRule REQUEST_METHOD "^GET$" "chain,msg: 'Apache Solr 任意文件读取',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/solr/admin/cores?indexInfo=false&wt=json" "chain"
SecRule REQUEST_BODY:data "@rx /file\:/g"
0x03集群引擎V4.0 RCE
防御规则链如下:
-
规则设置请求方式为POST,在使用规则之前验证有效请求POST
-
规则设置访问路径为“/login”
-
规则设置检测请求体中有无用户名字段,并且检测是否存在特殊字符“$”
0x04 Atlassian Jira 信息泄露漏洞 CVE-2020-14181
防御规则链如下:
-
规则设置请求方式为GET,在使用规则之前验证有效请求GET
-
规则设置访问路径为“/secure/ViewUserHover.jspa”
-
规则设置检测请求体中有无用户名字段,以及匹配传入的参数用户名值
SecRule REQUEST_FILENAME "@beginWith /secure/ViewUserHover.jspa""chain,msg: 'Atlassian Jira information Link Attack(CVE-2020-14181)',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_METHOD "^GET$" "chain"
SecRule REQUEST_BODY "@containsWord username=[a-zA-Z_\-]+"
0x05 弹性搜索远程执行代码CVE-2014-3120
-
规则设置请求方式为POST,在使用规则之前验证有效请求POST
-
规则设置访问路径为“/_search?pretty”
-
规则设置访问的数据传输的内容正则匹配是否存在系统字段以及“command”等
SecRule REQUEST_FILENAME "@beginWith /_search?pretty""chain,msg: 'Elasticsearch Remote Code Execution RCE Attack(CVE-2020-14181)',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_METHOD "^POST$" "chain"
SecRule REQUEST_BODY:data "@rx (?!)system|(?!)command|(?!)size|(?!)query"
哆哆邮件系统RCE
-
规则设置请求方式为POST,在使用规则之前验证有效请求POST
-
规则设置访问路径为“/webadm/?q=moni_detail.do&action=gragh”
-
规则设置匹配data内容是否有linx的相关命令字符
SecRule REQUEST_METHOD "^POST$" "chain,msg: 'Eyou Mail system RCE',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/webadm/?q=moni_detail.do&action=gragh" "chain"
SecRule REQUEST_BODY:data "@rx (?!)system|(?!)ls|(?!)cat|\{/"
F5 BIG-IP代码执行漏洞(CVE-2021-22986)
1.规则设置请求方式为POST,在使用规则之前验证有效请求POST
2.规则设置访问路径为“/mgmt/tm/util/bash”
3.规则设置匹配data内容是否有linx的相关命令字符command以及run等字符串以及“|”特殊字符
SecRule REQUEST_METHOD "^POST$" "chain,msg: 'BIG-IP代码执行漏洞(CVE-2021-22986) Attack',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/mgmt/tm/util/bash" "chain"
SecRule REQUEST_BODY:data "@rx (?!)command|(?!)run|\|/"
GitLab Graphql邮箱信息泄露漏洞(CVE-2020-26413)
1.规则设置请求方式为POST,在使用规则之前验证有效请求POST
2.规则设置访问路径为“/api/graphql”
3.规则设置匹配data内容username以及email等字符串以及“{”特殊字符
SecRule REQUEST_METHOD "^POST$" "chain,msg: 'GitLab Graphql information Link',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/api/graphql" "chain"
SecRule REQUEST_BODY:data "@rx (?!)username&(?!)eamil&\{/"
H3C IMC远程命令执行
1.规则设置请求方式为POST,在使用规则之前验证有效请求POST
2.规则设置访问路径为“imc/javax.faces.resource/dynamiccontent.properties.xhtml”
3.规则设置匹配data内容cmd
SecRule REQUEST_METHOD "^POST$" "chain,msg: 'H3C IMC远程命令执行',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/imc/javax.faces.resource/dynamiccontent.properties.xhtml" "chain"
SecRule REQUEST_BODY:data "@rx (?!)cmd"
景和OAC6默认密码
1.规则设置请求方式为POST,在使用规则之前验证有效请求POST
2.规则设置访问路径为“/C6/Jhsoft.Web.login/AjaxForLogin.aspx”
3.规则设置匹配data内容存在base64(000000)即MDAwMDAw
4.(或者存在关键词类型=login&loginCode=YWRtaW4=&&pwd=MDAwMDAw)
5.或者正则匹配type=login&loginCode=YWRtaW4=&&pwd=MDAwMDAw
SecRule REQUEST_METHOD "^POST$" "chain,msg: 'JingHe OA C6 Default password',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/C6/Jhsoft.Web.login/AjaxForLogin.aspx" "chain"
SecRule REQUEST_BODY "@containsWord type=login&loginCode=YWRtaW4=&&pwd=MDAwMDAw"
景河OA下载.asp文件读取
- 规则设置请求方式为GET,在使用规则之前验证有效请求GET
- 规则设置访问路径为“/C6/Jhsoft.Web.module/testbill/dj/download.asp?filename=/c6/web.config”
- 规则设置访问的参数文件名后面跟随的路径
- 设置规则只要读取文件就存在"."
SecRule REQUEST_METHOD "^GET$" "chain,msg: 'JingHe OA download.asp File read',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/C6/Jhsoft.Web.login/AjaxForLogin.aspx" "chain"
SecRule REQUEST_BODY "@contains filename" "chain"
SecRule REQUEST_LINE "@rx (?!)filename\=\[a-Z.]+/"
极通EWEBS任意文件读取
- 规则设置请求方式为POST,在使用规则之前验证有效请求POST
- 规则设置访问路径为“/casmain.xgi”
- 规则设置匹配访问的data中参数Language_S的值匹配特殊字符“.”
- 规则设置匹配Language_S的值以…/开头
SecRule REQUEST_METHOD "^POST$" "chain,msg: '极通EWEBS任意文件读取',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_URI "/casmain.xgi" "chain"
SecRule REQUEST_BODY "@cantains Language_S" "chain"
SecRule ARGS:/^\.\.\// Language_S
极通EWEBS phpinfo泄露
- 规则设置请求方式为GET,在使用规则之前验证有效请求GET
- 规则设置访问路径为“/testweb.php”
SecRule REQUEST_FILENAME "@beginWith /testweb.php" "chain,msg: '极通EWEBS phpinfo Link',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_METHOD "^GET$"
金山V8任意文件读取
- 规则设置请求方式为GET,在使用规则之前验证有效请求GET
- 规则设置访问路径为“/htmltopdf/downfile.php?filename=downfile.php”
SecRule REQUEST_URI "/htmltopdf/downfile.php?filename=downfile.php" "chain,msg:'Kingsoft V8 Arbitrary file read',severity:ERROR,deny,status:404,id:xxx"
SecRule REQUEST_METHOD "^GET$"
总结
这里只是一部分根据网上的POC自己根据规则自建的,当然,没有与之匹配的环境这个规则也是无法使用的,,,,。但是扩展的思路倒是很多,看自己怎么使用了!!!
![学习open62541 --- [75] 生成namespace文件的简便方法](https://img-blog.csdnimg.cn/4152a82e3dcd414a9ed1ebac058e4894.png)