曾几何时,我翻版了 Xposed 的 just_trust_me.apk, just_trust_me.js 脚本仿佛是一张通行证,让我们在 SSL Pinning 的高墙前轻松穿越。
但时代变了。BoringSSL、Cronet、静态 inline hook、动态 verify callback……一切都变得更加隐蔽和棘手。
今天,hooker 终于补上了这块拼图 —— 支持 BoringSSL 的 unpinning。
这不仅是一小步的补丁,更是对抗“新时代证书信仰”的一次温柔叛逆。
我们不再只是 hook checkServerTrusted,而是深入到了 SSL_set_custom_verify、ssl_verify_cert_chain,直面 Cronet / Chromium 的加固体系。
世界依旧在加密,但我们依旧可以选择相信自己。
Hello again, BoringSSL.
And this time — Just Trust Me.
项目地址:
https://github.com/CreditTone/hooker
just_trust_me脚本地址:
https://github.com/CreditTone/hooker/blob/master/js/just_trust_me.js
hooker的just_trust_me依然深度绑定hooker,不能直接拷贝运行哦!得按hooker的使用指南来
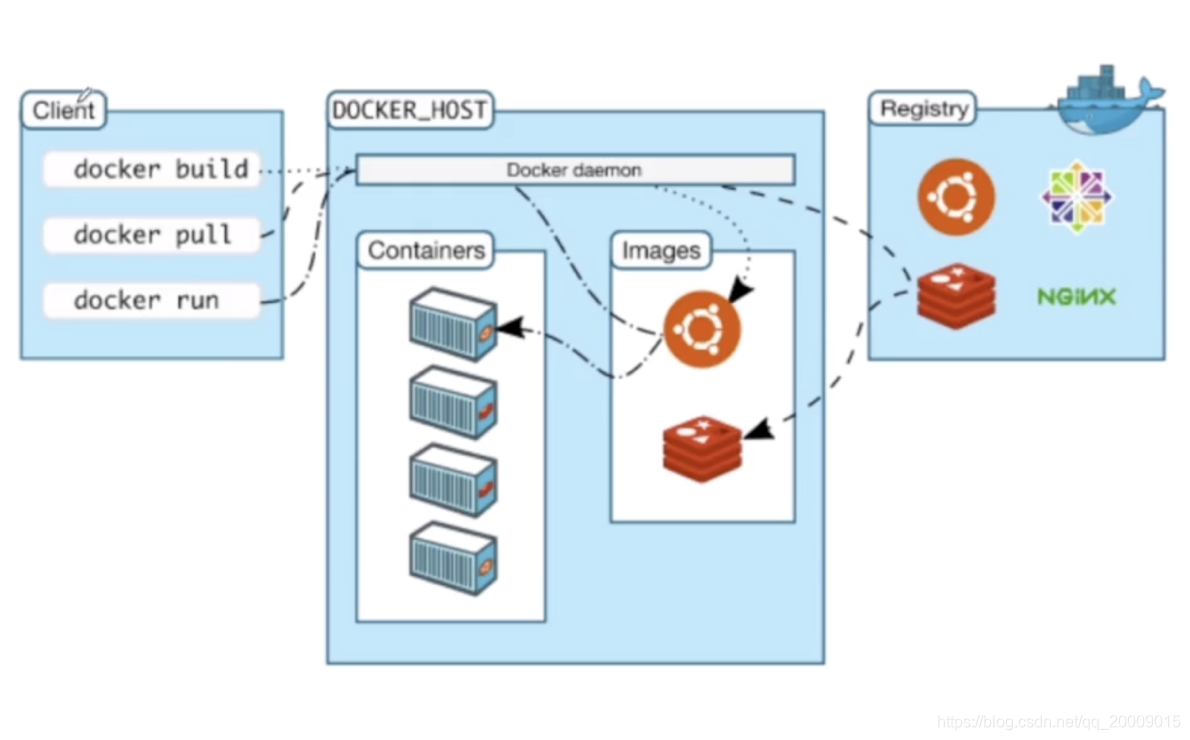
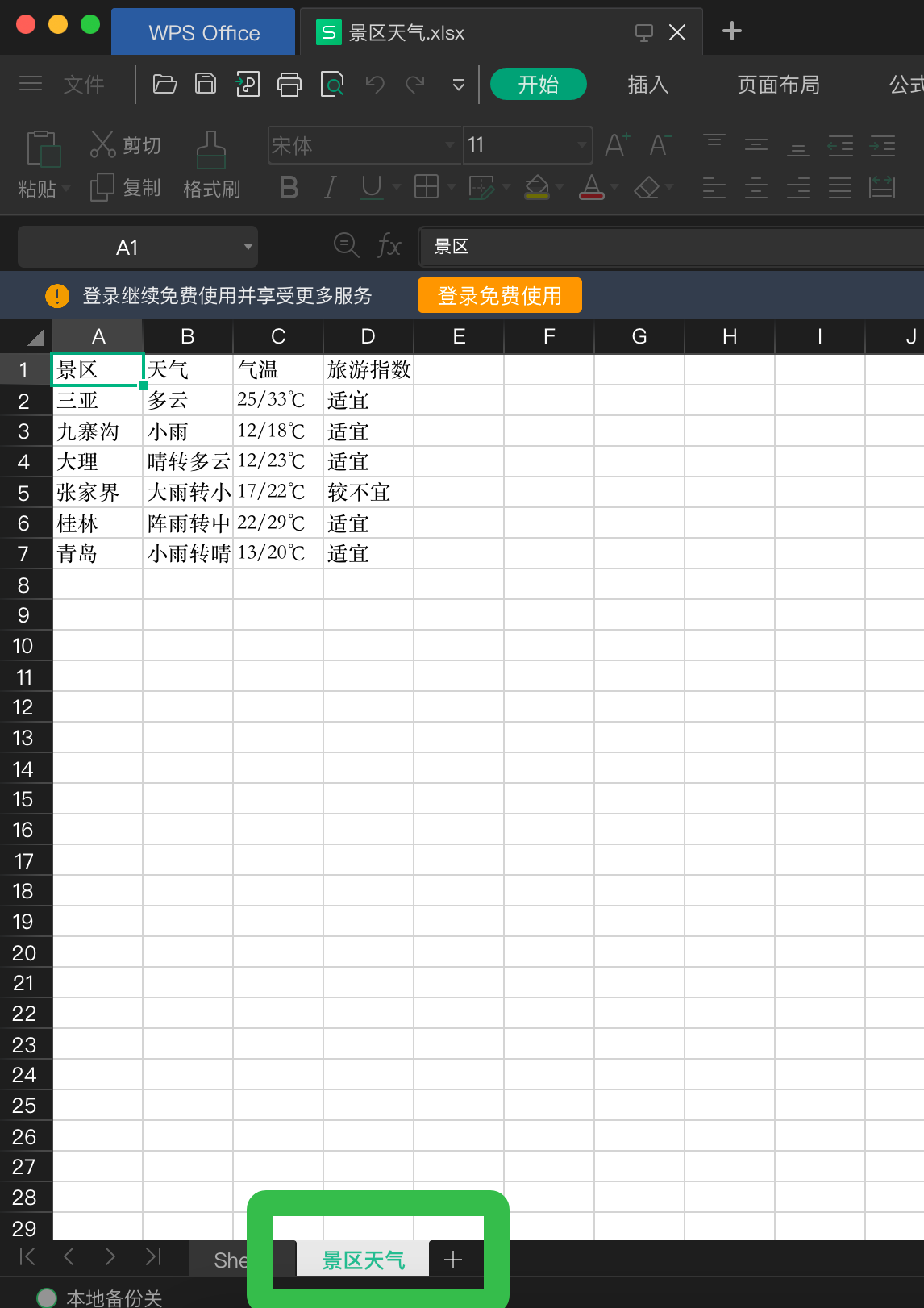
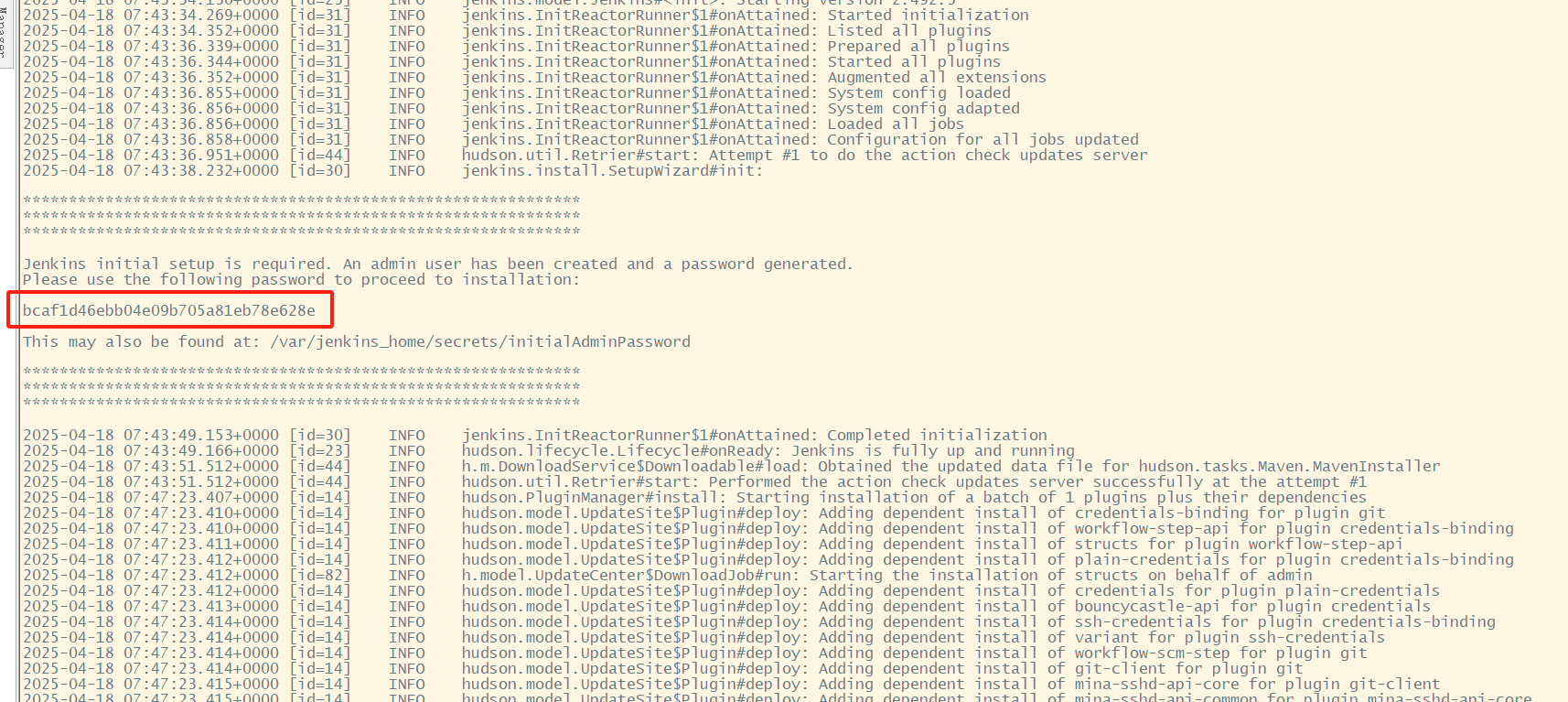
环境部署
1. git clone项目
stephen@ubuntu:~$ git clone https://github.com/CreditTone/hooker.git
stephen@ubuntu:~$ cd hooker
stephen@ubuntu:~$ ls
colorful.py com.xxxx.aegis mobile-deploy.tar
com.xxxx.wireless com.xxxx.meituan org.mokee.lawnchair
com.changba com.xxxx.kt.ktandroid org.mokee.weatherservice
com.google.android.youtube com.xxxx.gifmaker __pycache__
com.xxx.qukan com.ss.xxxx.xxx.news radar.dex
com.jzg.jzgoto.phone com.ss.xxx.xx.aweme README.md
com.xxx.weidian.buyer com.xxx.karaoke run_env.py
com.xxx.shiqutouch com.xxx.mm sogou.mobile.explorer
com.xx.shop hooker spider.py
com.xxxx.mall hooker.py traceJNI
com.xxx.meipaimv js xapk
com.miui.screenrecorder mobile-deploy.sh xinitdeploy.py
2. 安装依赖
stephen@ubuntu:~/hooker$ pip3 install -r requirements.txt
3. frida-server环境部署
stephen@ubuntu:~/hooker$ adb push mobile-deploy/ /sdcard/
stephen@ubuntu:~/hooker$ adb shell #进入手机命令行界面
sailfish:/ $ su
sailfish:/ $ cd /sdcard/mobile-deploy/
sailfish:/ $ sh deploy2.sh
start frida-server
deploy successfull.
sailfish:/ $ exit4. 查看可调试进程
stephen@ubuntu:~/hooker$ ./hooker
PID Name Identifier
----- ----------------------------- -------------------------------------------------------------
2857 Android Auto com.google.android.projection.gearhead
1779 Android Services Library com.google.android.ext.services
929 Android 系统 android
5073 Carrier Services com.google.android.ims
11051 Device Health Services com.google.android.apps.turbo
2913 Device Personalization S… com.google.android.as
2522 Google com.google.android.googlequicksearchbox
15189 Google Play 商店 com.android.vending
2101 Google Play 服务 com.google.android.gms
2833 Google VR 服务 com.google.vr.vrcore
7710 Google 服务框架 com.google.android.gsf
2546 NFC服务 com.android.nfc
929 NetworkStack com.android.networkstack.inprocess
929 一体化位置信息 com.android.location.fused
14468 云端硬盘 com.google.android.apps.docs
14403 信息 com.google.android.apps.messaging
12073 存储已屏蔽的号码 com.android.providers.blockednumber
1574 实时数据壁纸 com.ustwo.lwp
12073 用户字典 com.android.providers.userdictionary
13362 电话 com.google.android.dialer
1704 电话和短信存储 com.android.providers.telephony
1704 电话服务 com.android.phone
Enter the need to attach package.
: 5. attach一个应用
stephen@ubuntu:~/hooker$ ./hooker
Enter the need to attach package.
: com.ss.xxx.xxxx.xxxme #在此处输入进程的Identifier即可调试应用
It'scom.ss.xxx.xxxx.xxxme that you have attached app.6. 进入应用工作目录
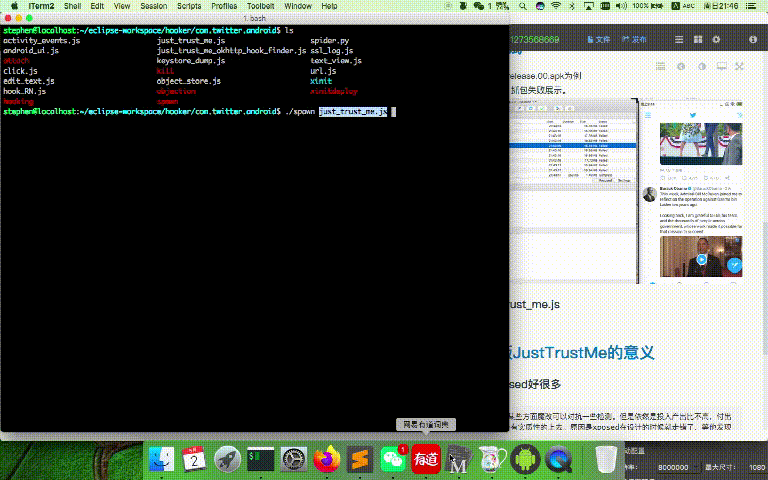
这里我们可以看到hooker为我们的app逆向环境提供了非常多的工具,这里有板子、螺丝刀、老虎钳、热风枪、示波器、钛合金撬棍、八合一电动螺丝刀。不过本章节您只需要知道just_trust_me.js
bogon:com.ss.xxx.xxxx.xxxme stephen256$ ll
total 360
-rw-r--r-- 1 stephen256 staff 7669 4 17 17:11 activity_events.js
-rw-r--r-- 1 stephen256 staff 5793 4 17 17:11 android_ui.js
-rwxrwxrwx 1 stephen256 staff 105 4 17 17:11 attach
-rw-r--r-- 1 stephen256 staff 2242 4 17 17:11 click.js
-rwxrwxrwx 1 stephen256 staff 374 4 17 17:11 disable_sslpinning
-rw-r--r-- 1 stephen256 staff 5836 4 17 17:11 dump_dex.js
-rw-r--r-- 1 stephen256 staff 4322 4 17 17:11 edit_text.js
-rw-r--r-- 1 stephen256 staff 0 4 17 17:11 empty.js
-rw-r--r-- 1 stephen256 staff 634 4 17 17:11 find_anit_frida_so.js
-rw-r--r-- 1 stephen256 staff 3016 4 17 17:11 find_boringssl_custom_verify_func.js
-rw-r--r-- 1 stephen256 staff 2531 4 17 17:11 hook_artmethod_register.js
-rw-r--r-- 1 stephen256 staff 14229 4 17 17:11 hook_jni_method_trace.js
-rw-r--r-- 1 stephen256 staff 2108 4 17 17:11 hook_register_natives.js
-rwxrwxrwx 1 stephen256 staff 162 4 17 17:11 hooking
-rw-r--r-- 1 stephen256 staff 32661 4 17 17:11 just_trust_me.js
-rw-r--r-- 1 stephen256 staff 3281 4 17 17:11 just_trust_me_for_ios.js
-rw-r--r-- 1 stephen256 staff 3180 4 17 17:11 just_trust_me_okhttp_hook_finder_for_android.js
-rw-r--r-- 1 stephen256 staff 4495 4 17 17:11 keystore_dump.js
-rwxrwxrwx 1 stephen256 staff 104 4 17 17:11 kill
-rw-r--r-- 1 stephen256 staff 1529 4 17 17:11 object_store.js
-rwxrwxrwx 1 stephen256 staff 102 4 17 17:11 objection
-rw-r--r-- 1 stephen256 staff 2353 4 17 17:11 replace_dlsym_get_pthread_create.js
-rwxrwxrwx 1 stephen256 staff 120 4 17 17:11 spawn
-rw-r--r-- 1 stephen256 staff 2561 4 17 17:11 spider.py
-rw-r--r-- 1 stephen256 staff 768 4 17 17:11 ssl_log.js
-rw-r--r-- 1 stephen256 staff 2371 4 17 17:11 text_view.js
-rw-r--r-- 1 stephen256 staff 3725 4 17 17:11 trace_initproc.js
-rw-r--r-- 1 stephen256 staff 4789 4 17 17:11 url.js
drwxr-xr-x 4 stephen256 staff 128 4 17 17:11 xinit
-rwxrwxrwx 1 stephen256 staff 5846 4 17 17:11 xinitdeploy7. 使用just_trust_me.js
命令行执行 ./spawn just_trust_me.js 启动
bogon:com.ss.xxx.xxxx.xxxme stephen256$ ./spawn just_trust_me.js
____
/ _ | Frida 14.2.2 - A world-class dynamic instrumentation toolkit
| (_| |
> _ | Commands:
/_/ |_| help -> Displays the help system
. . . . object? -> Display information about 'object'
. . . . exit/quit -> Exit
. . . .
. . . . More info at https://www.frida.re/docs/home/
Spawned `com.ss.xxx.xxxx.xxxme`. Resuming main thread!
[MI MAX 3::com.ss.xxx.xxxx.xxxme]-> android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
javax.net.ssl.SSLContext.init('[Ljavax.net.ssl.KeyManager;', '[Ljavax.net.ssl.TrustManager;', 'java.security.SecureRandom') was hooked!
android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
javax.net.ssl.TrustManagerFactory.getTrustManagers() was hooked!
android.net.http.X509TrustManagerExtensions.checkServerTrusted('[Ljava.security.cert.X509Certificate;', 'java.lang.String', 'java.lang.String') was hooked!
javax.net.ssl.SSLContext.init('[Ljavax.net.ssl.KeyManager;', '[Ljavax.net.ssl.TrustManager;', 'java.security.SecureRandom') was hooked!
javax.net.ssl.TrustManagerFactory.getTrustManagers() was hooked!
javax.net.ssl.SSLContext.init('[Ljavax.net.ssl.KeyManager;', '[Ljavax.net.ssl.TrustManager;', 'java.security.SecureRandom') was hooked!
javax.net.ssl.TrustManagerFactory.getTrustManagers() was hooked!
javax.net.ssl.SSLContext.init('[Ljavax.net.ssl.KeyManager;', '[Ljavax.net.ssl.TrustManager;', 'java.security.SecureRandom') was hooked!板子、螺丝刀、热风枪、抓包钩子、动态脚本……连高温焊台和逻辑分析仪都给你安排得明明白白。普通应用?一套脚本过去直接开盖验芯。复杂点的?比如那些加了“加密外壳”的“短视频类社交平台”,你懂的——也不过是多拧几颗螺丝罢了。
至于某些深藏 BoringSSL 的“重量级工程”,hooker 里那份 just_trust_me.js 就像个万能钳,哪怕目标系统关得像保险柜,只要插进去一点缝,它就能让你“放心探索”整个流程逻辑,TLS握手仿佛穿了隐形斗篷,一切安全校验都悄悄按下了“稍后再提醒”。
我们当然不会说它能干什么,只能说——你不妨亲手试试,说不定,会有点小惊喜。

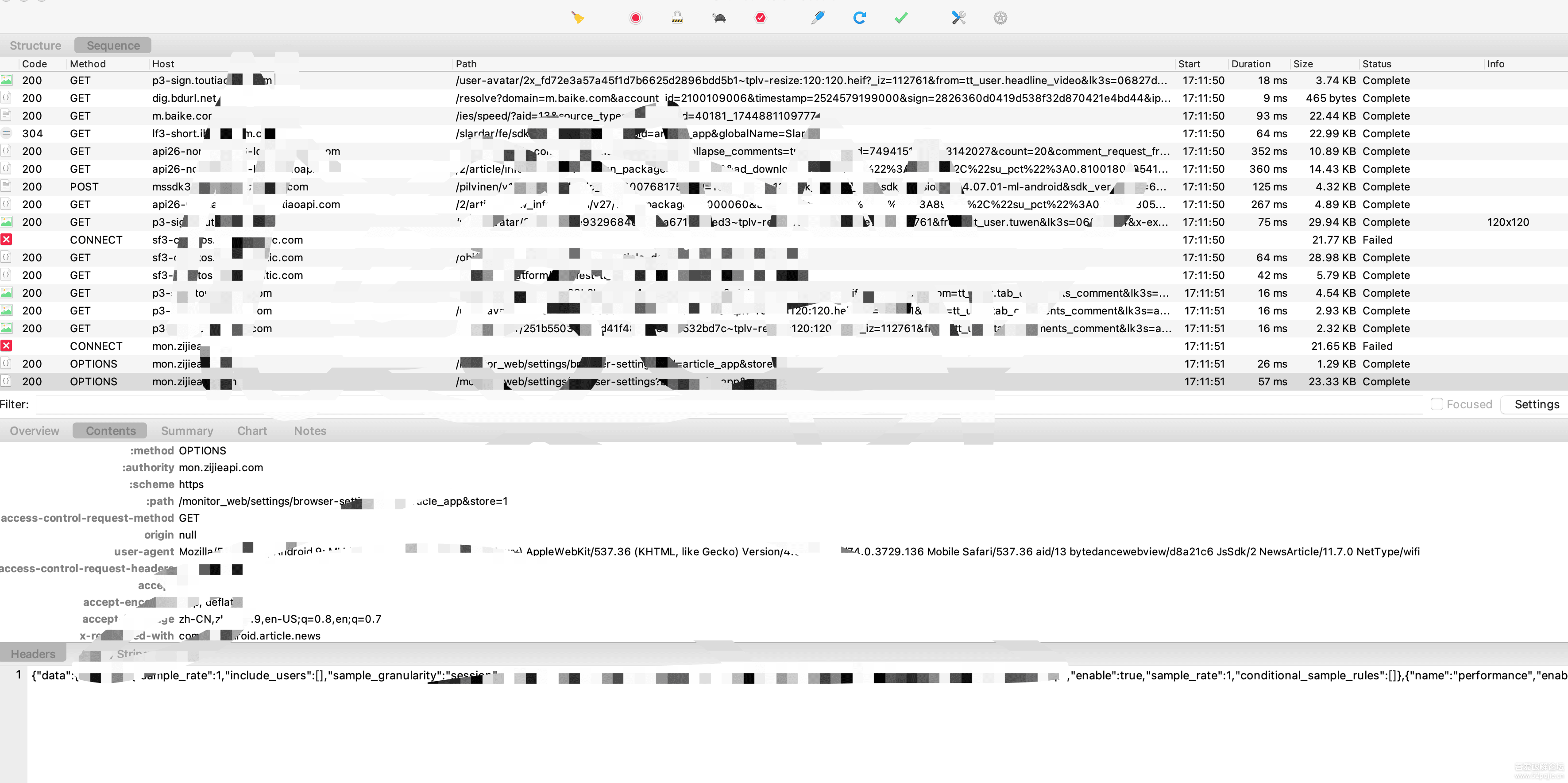
祝大家抓包愉快!!!