目录
一、前言
二、ElasticSearch的安全认证配置
设置ElasticSearch的安全认证功能(最低)
启用TLS/SSL加密通信
(1)生成CA证书
(2)生成transport证书
(3)生成http证书
(4)完整配置ES
三、Kibana 安全配置
四、Logstash配置补充
五、后记
一、前言
在数字化转型的浪潮中,企业对于数据的依赖日益增强,而日志数据作为业务运行的“脉络图”,其重要性不言而喻。ELFK(Elasticsearch, Logstash, Filebeat, Kibana)作为一套强大的日志监控系统,为企业提供了从数据采集、处理到可视化的完整解决方案。然而,随着数据价值的提升,安全问题也日益凸显,如何在享受ELFK带来的高效与便捷的同时,确保数据的安全与合规,成为了企业必须面对的挑战。
安全认证,作为守护数据安全的第一道防线,其在ELFK系统中的必要性不容忽视。上文笔者介绍的ELFK的基础搭建流程以及日志采集方式配置过程,但是整个日志监控系统是完全没有安全性可言的。kibana也是没有任何访问认证就能直接访问,显然这与实际使用是有较大差别的。一般企业级的日志监控系统可能需要满足一下要求:
-
数据保护
-
防止未经授权的访问:ELFK系统通常处理敏感的日志数据,包括用户活动、系统错误和应用程序运行状态。安全认证可以防止未经授权的用户访问这些数据,保护企业机密。
-
数据完整性:通过认证机制,确保所有的日志数据来源是可信的,避免恶意用户篡改日志内容。
-
合规要求
-
满足法规标准:许多行业法规(如GDPR、HIPAA等)要求企业保护用户数据隐私及其访问控制。通过实施安全认证,ELFK系统可以帮助企业满足这些合规要求。
-
访问控制
-
分层权限管理:ELFK的安全认证可以实现细粒度的权限控制,确保不同角色或用户组只能访问其权限范围内的数据。例如,仅限运维人员可查看系统级日志,而开发人员可以访问应用程序日志。
-
保护完整基础设施
-
防止攻击:加强ELFK各组件的安全认证可以减少被攻击的风险。比如,防止Elasticsearch暴露在公网上而被攻击者利用。
-
防止日志注入:对日志输入进行验证,通过安全认证措施,防止恶意代码通过日志注入而影响系统。
-
安全审计
-
追踪和记录访问行为:安全认证可以帮助记录和监控用户访问日志的行为,提供详细的日志访问历史记录。这在需要进行安全审计或调查时非常有用。
因此本文将深入探讨如何通过实施有效的安全认证措施,为企业构建一个既高效又安全的日志监控环境。
二、ElasticSearch的安全认证配置
设置ElasticSearch的安全认证功能(最低)
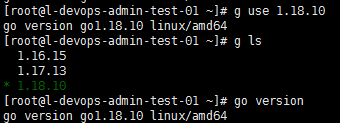
ElasticSearch的安全访问需要开启x-pack安全验证:xpack.security.enabled: true。X-Pack是Elasticsearch的一个插件,提供了安全、监控、报警和报告等功能。承接上文ELFK基础搭建流程及在SpringBoot项目中进行日志采集的简单实践,笔者在搭建简易版的时候是设置为false给关闭了,那么现在需要让他正常开启。然后需要进行一个内置账户密码的配置,Elasticsearch提供了一些内置用户(如elastic、kibana、logstash_system等),我们需要为这些用户设置密码,否则普通访问就会访问失败。
root@master01:~# su elasticsearch
elasticsearch@master01:/root$ cd /data/elk/es
elasticsearch@master01:/data/elk/es$ vi config/elasticsearch.yml
elasticsearch@master01:/data/elk/es$ sudo docker restart es
[sudo] elasticsearch 的密码:
es
elasticsearch@master01:/data/elk/es$ curl http://192.168.1.200:9200
{"error":{"root_cause":[{"type":"security_exception","reason":"missing authentication credentials for REST request [/]","header":{"WWW-Authenticate":["Basic realm=\"security\", charset=\"UTF-8\"","ApiKey"]}}],"type":"security_exception","reason":"missing authentication credentials for REST request [/]","header":{"WWW-Authenticate":["Basic realm=\"security\", charset=\"UTF-8\"","ApiKey"]}},"status":401}elasticsearch@master01:/data/elk/es$ 正常初始运行ElasticSearch时他会在控制台提供一个账号信息,但是由于我们一开始就关闭了,并且不太方便追踪,所以在开启认证后需要重新设置一下。
设置步骤如下:
1,进入es容器内部
elasticsearch@master01:/root$ sudo docker exec -it es /bin/bash
[sudo] elasticsearch 的密码:
elasticsearch@master01:~$ ls
LICENSE.txt NOTICE.txt README.asciidoc bin config data jdk lib logs modules plugins
elasticsearch@master01:~$ ll
total 2312
drwxrwxr-x 1 root root 4096 Aug 17 14:47 ./
drwxr-xr-x 1 root root 4096 Aug 5 10:12 ../
-rw-r--r-- 1 root root 220 Aug 5 10:12 .bash_logout
-rw-r--r-- 1 root root 3771 Aug 5 10:12 .bashrc
drwxrwxr-x 3 elasticsearch root 4096 Aug 17 14:47 .cache/
-rw-r--r-- 1 root root 807 Aug 5 10:12 .profile
-r--r--r-- 1 root root 3860 Aug 5 10:11 LICENSE.txt
-r--r--r-- 1 root root 2285006 Aug 5 10:11 NOTICE.txt
-r--r--r-- 1 root root 9111 Aug 5 10:11 README.asciidoc
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:12 bin/
drwxrwxr-x 1 elasticsearch root 4096 Aug 17 14:47 config/
drwxrwxrwx 5 1001 1001 4096 Aug 21 12:29 data/
dr-xr-xr-x 1 root root 4096 Aug 5 10:11 jdk/
dr-xr-xr-x 6 root root 4096 Aug 5 10:11 lib/
drwxrwxrwx 2 1001 1001 4096 Aug 21 12:25 logs/
dr-xr-xr-x 83 root root 4096 Aug 5 10:11 modules/
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:11 plugins/2,设置密码操作
elasticsearch除了开启安全自动配置可自动生成初始密码外,手动设置一般有三种方式。由于自动配置需要在es启动控制台查看输出的密码信息,不便于查看,因此这块不做主要解释,仅以手动配置为主:
-
Elastic bootstrap password
-
bin/elasticsearch-reset-password -u elastic
-
elasticsearch-setup-passwords interactive
在安装 Elasticsearch 时,启用安全认证后如果 elastic 用户还没有密码,它将使用默认的 bootstrap。 bootstrap 是一种临时密码,使我们可以运行设置所有内置用户密码的工具。默认情况下,bootstrap 密码来自于随机化的 keystore.seed 设置,该设置在安装过程中添加到了密钥库中。 我们不需要知道或更改此 bootstrap 密码。 但是,如果我们在密钥库中定义了 bootstrap.password 设置,则将使用该值。但是实际keystore.seed中我们并不知道密码是多少,所以需要我们自己设置bootstrap.password。
另外如果我们为内置用户(尤其是 elastic 用户)设置密码后,bootstrap 密码将不再使用。这里我们可以进入es容器后使用 -x 选项从 stdin 中读取密码并配置bootstrap密码:
elasticsearch@master01:/data/elk/es/data$ sudo docker exec -it es /bin/bash
elasticsearch@master01:~$ pwd
/usr/share/elasticsearch
elasticsearch@master01:~$ bin/elasticsearch-keystore list
keystore.seed
elasticsearch@master01:~$ echo "elastic" |bin/elasticsearch-keystore add -x "bootstrap.password"
elasticsearch@master01:~$ bin/elasticsearch-keystore list
bootstrap.password
keystore.seed然后需要重启es,因为所有对keystore的修改需要重启Elasticsearch后才能生效。这些设置,就像elasticsearch中对Yml配置文件的修改,需要在集群的每个节点上指定,并重启后才会生效。这个密钥库也是如此,对密钥库的任何更改都将在重新启动Elasticsearch时生效。然后就可以通过我们这个初步配置的密码进行访问了:
elasticsearch@master01:/data/elk/es/data$ sudo docker restart es
es
elasticsearch@master01:/data/elk/es/data$ curl http://192.168.1.200:9200 -u elastic:elastic
{
"name" : "master01",
"cluster_name" : "es-master",
"cluster_uuid" : "SPlA9bg2Sly4fKzvbQbzTA",
"version" : {
"number" : "8.15.0",
"build_flavor" : "default",
"build_type" : "docker",
"build_hash" : "1a77947f34deddb41af25e6f0ddb8e830159c179",
"build_date" : "2024-08-05T10:05:34.233336849Z",
"build_snapshot" : false,
"lucene_version" : "9.11.1",
"minimum_wire_compatibility_version" : "7.17.0",
"minimum_index_compatibility_version" : "7.0.0"
},
"tagline" : "You Know, for Search"
}第二种就是通过运行elasticsearch-reset-password实用程序为弹性内置用户设置密码。该命令将密码重置为自动生成的值。如果需要将密码设置为一个特定的值,可以使用带interactive (-i)参数的命令:./bin/elasticsearch-reset-password -u elastic。同时也可以用这个命令为其他内置用户设置密码:./bin/elasticsearch-reset-password -u kibana_system
最后一种elasticsearch-setup-passwords interactive用于一次性批量设置密码。这里为了方便我们用第三种方式设置即可。
此时需要我们依次设置用户:elastic、apm_system、kibana_system、logstash_system、beats_system、remote_monitoring_user共6个用户,并为每个内置用户设置密码。
elasticsearch@master01:/data/elk/es/data$ sudo docker exec -it es /bin/bash bin/elasticsearch-setup-passwords interactive
******************************************************************************
Note: The 'elasticsearch-setup-passwords' tool has been deprecated. This command will be removed in a future release.
******************************************************************************
Initiating the setup of passwords for reserved users elastic,apm_system,kibana,kibana_system,logstash_system,beats_system,remote_monitoring_user.
You will be prompted to enter passwords as the process progresses.
Please confirm that you would like to continue [y/N]y
Enter password for [elastic]:
Reenter password for [elastic]:
Enter password for [apm_system]:
Reenter password for [apm_system]:
Enter password for [kibana_system]:
Reenter password for [kibana_system]:
Enter password for [logstash_system]:
Reenter password for [logstash_system]:
Enter password for [beats_system]:
Reenter password for [beats_system]:
Enter password for [remote_monitoring_user]:
Reenter password for [remote_monitoring_user]:
Changed password for user [apm_system]
Changed password for user [kibana_system]
Changed password for user [kibana]
Changed password for user [logstash_system]
Changed password for user [beats_system]
Changed password for user [remote_monitoring_user]
Changed password for user [elastic]然后就可以通过账号密码进行访问了。
root@master01:~# curl http://localhost:9200 -u elastic:elastic
{
"name" : "master01",
"cluster_name" : "es-master",
"cluster_uuid" : "SPlA9bg2Sly4fKzvbQbzTA",
"version" : {
"number" : "8.15.0",
"build_flavor" : "default",
"build_type" : "docker",
"build_hash" : "1a77947f34deddb41af25e6f0ddb8e830159c179",
"build_date" : "2024-08-05T10:05:34.233336849Z",
"build_snapshot" : false,
"lucene_version" : "9.11.1",
"minimum_wire_compatibility_version" : "7.17.0",
"minimum_index_compatibility_version" : "7.0.0"
},
"tagline" : "You Know, for Search"
}当然这从 ES官方文档角度而言只是最小安全配置,如果向把安全配置程度提高,我们一般还可以继续配置TLS和HTTPS。
启用TLS/SSL加密通信
TLS(Transport Layer Security)和 HTTPS 主要是为了确保数据在传输过程中的安全性和保护敏感信息不被窃取或篡改。而在ElasticSearch中,数据传输是通过网络进行的,对于某些敏感信息,例如用户凭据、个人身份信息等。如果不通过加密方式传输数据,那么在传输过程中可能会被恶意用户截获或窃取。因此通过配置 TLS 和使用 HTTPS 协议,可以加密通信内容,确保数据传输过程中的安全性。
在 Elasticsearch 中,安全通信也需要使用TLS/SSL证书。这些证书可以用于保护Elasticsearch节点之间的通信(Transport层)以及客户端与Elasticsearch之间的通信(HTTP层)。特别是生产环境中的ES集群我们必须在节点之间配置传输层安全性(TLS)。如果不启用TLS,生产模式集群将不会启动。

所以很多情况下都需要我们自己去配置Certificates and Keys。证书和密钥是配置 TLS 和 HTTPS 的基础,用于加密通信和验证身份。
ElasticSearch中使用的证书一般有3种:
CA是一个颁发和验证数字证书的可信任实体,用于确保通信双方身份的合法性。在配置 TLS 时,通常需要生成自签名证书或向第三方 CA 申请证书。在ES中就可以通过elasticsearch-certutil工具自生成CA证书,并以它为基础去生成其他证书。
transport证书,用于ES节点之间通讯。
http证书,用于client访问,包括ES自带的/bin下的脚本文件也会依赖这个证书调用当前ES的API
根据ES官网文档指导,一般生成证书的方式有两种:
(1)生成CA证书
elasticsearch@master01:~$ bin/elasticsearch-certutil ca
This tool assists you in the generation of X.509 certificates and certificate
signing requests for use with SSL/TLS in the Elastic stack.
The 'ca' mode generates a new 'certificate authority'
This will create a new X.509 certificate and private key that can be used
to sign certificate when running in 'cert' mode.
Use the 'ca-dn' option if you wish to configure the 'distinguished name'
of the certificate authority
By default the 'ca' mode produces a single PKCS#12 output file which holds:
* The CA certificate
* The CA's private key
If you elect to generate PEM format certificates (the -pem option), then the output will
be a zip file containing individual files for the CA certificate and private key
#取名,默认为elastic-stack-ca.p12
Please enter the desired output file [elastic-stack-ca.p12]: es-ca.p12
#设置证书密码,默认为空
Enter password for es-ca.p12 :
elasticsearch@master01:~$ ls -l
total 2284
-r--r--r-- 1 root root 3860 Aug 5 10:11 LICENSE.txt
-r--r--r-- 1 root root 2285006 Aug 5 10:11 NOTICE.txt
-r--r--r-- 1 root root 9111 Aug 5 10:11 README.asciidoc
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:12 bin
drwxrwxr-x 1 elasticsearch root 4096 Aug 17 14:47 config
drwxrwxrwx 5 1001 1001 4096 Aug 21 12:41 data
-rw------- 1 elasticsearch root 2672 Aug 21 12:42 es-ca.p12
dr-xr-xr-x 1 root root 4096 Aug 5 10:11 jdk
dr-xr-xr-x 6 root root 4096 Aug 5 10:11 lib
drwxrwxrwx 2 1001 1001 4096 Aug 21 12:25 logs
dr-xr-xr-x 83 root root 4096 Aug 5 10:11 modules
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:11 plugins默认情况下,“ca” 模式生成一个 P12 输出文件,其中包含:
-
CA 证书
-
CA 的私钥
这里可以选择添加证书密码,如果添加密码的话,后续使用CA证书去生成其他证书都需要先校验密码。默认会在es根目录(/usr/share)下生成 elastic-stack-ca.p12 这个CA证书文件,在实际操作中可根据自己的实际情况进行调整。
这里笔者建议设置密码,不然可能会没有证书链信息。顺序操作后就能看到生成的elastic-stack-ca.p12文件了。
我们可以通过如下方式检查证书信息:
1.1,openssl查看
elasticsearch@master01:~$ openssl pkcs12 -info -nodes -in es-ca.p12
Enter Import Password:
MAC: sha256, Iteration 10000
MAC length: 32, salt length: 20
PKCS7 Data
Shrouded Keybag: PBES2, PBKDF2, AES-256-CBC, Iteration 10000, PRF hmacWithSHA256
Bag Attributes
friendlyName: ca
localKeyID: 54 69 6D 65 20 31 37 32 34 32 34 34 31 34 35 36 32 31
Key Attributes: <No Attributes>
-----BEGIN PRIVATE KEY-----
MIIEvAIBADANBgkqhkiG9w0BAQEFAASCBKYwggSiAgEAAoIBAQCkvzQRIfKTKiek
zLGqjZ3Rttw9z/wKWF1w9rnQtTuaPa9ov3ZZLs462FSYnI/6ivkI90WEK5znbd87
Vlw55nVYFVe3LCRLDOqA1rarvgaZ9NhtGwePejHpeg6bE6RZlhMVqlCr4Hh7yW+M
6zlRi5MamdB8BJ8/T8U0BLnVGGcPq4Hg8d2kmnCrkxQ5fBM9eUQba0PFQsuXcBs9
1NePUhcU4ckBw4/oG0lKlDz8/5Sp1150Ahb1S2Y0X1FveoNb5eu/9mh7bhTX7owO
MIyvJDuGQ0IKqcccaEN+IiQeTX2OB4HgqXZVzDri1zz7E7k8LbwMXcVj6waK9vQR
7ptKrk6/AgMBAAECggEAD5tfctoM8V0WeVm84QPedg4FKkPoRBCf9YIiEzol
Al7U9tjkx5VT2ktGpn0A35URPFanXBNACQ6C2SdYaXpIH32qiIOWOZNdpcJwPKiB
0kAzxKdWUCB0fsNrF+OMNkq2rrmqoEtyal6kRPHcgzIcGouTjHthmq5x7lqL9ONr
EOksS6LYYFyETI1GFCxMICzyvAVbmxxbO/m405852hv4Rx1O/+T/Ju234rjaSPpO
3XT1WhoZzMmQ7xT6Xwm+4IhIgrWYb7R5TOnE9H0MpOsjIN3oeOkLlqa7/Muf8uPi
AL5kZl9FdAJjGJYuKvrjd2mRxga1s0AgDJzqO+pTRQKBgQDGZtv6izyfh9+4orBV
MdO8v1Cxt3olD/pegGlOoFc2n9LAIUG0lF0KP3Nn34XIdfLBGDOXJtNOdDzGIXS7
Y+tcDOQmq0080hU8rBq5mBkYf2csRVh+pKDoA3oKhWjgrG9drZsZ8b+0ENHmhif0
SRNeY77GcJZcvdBIx+knA7wEEwKBgQDUkyAK8FVCqw4QxHrbXWsWkNwAf/TTyNZv
2Ih3853au4jdVKN/sn+hfgLNI4xFJf5PUA/x9bR71F2aOa1l/xt9cSxQqFAM7xy0
3Toi6HL6iVph2NHQwMhORrWZLGG0wUYhvaWu2PXVqx+UJMBHHjswrkoL72oInr/m
8dLd3P5oJQKBgE7wxj4eAHUJPv7b3IVJWhITnSvY8QSmItxPA5eBPLJDTTuc/+O1
1H8rV+PQkA5+v6QM2RofHJxuq2+6CBQ3YYIyruSj7AtzG3gUkl2eIv4YUxjOTrO1
FUC7gWeGRYB/m6AOX1QnWDtxJdMvNd6A5O/9h/609V7ZN3J9+ErJtZl5AoGAeoNs
xUEsMmc5jQpgMEuP64qDcTpN1T178SwfwtpCEQ1iXQVp0bADhQSGAsrJDhVOk1F2
TyIn6fJEHB2/xPgZVNvECZxnvnyU09xopDPKCIDe+WOn0SM6jnqMMQJ2MWHu1IVj
lvjt/j5Ize28b4CJ5o2cmXJbbypnOWgH+txiN40CgYBVlU6MDbUXtBLuuQX2nLlz
J+cAN2T5NgamZpozW+w9cBlqQ6OnVmUMI1mIeY3ypY2BgHauChkM+vEk5Z1nLcD8
dXlYwSxfFhaOtTT2ezMqg4/pvSObOEwrCvWn6cSHd5rGTmyN2aIBgT7GDoQ/Fw9N
X4rAjIW7B14Dbmlw3FDDPA==
-----END PRIVATE KEY-----
PKCS7 Encrypted data: PBES2, PBKDF2, AES-256-CBC, Iteration 10000, PRF hmacWithSHA256
Certificate bag
Bag Attributes
friendlyName: ca
localKeyID: 54 69 6D 65 20 31 37 32 34 32 34 34 31 34 35 36 32 31
subject=CN = Elastic Certificate Tool Autogenerated CA
issuer=CN = Elastic Certificate Tool Autogenerated CA
-----BEGIN CERTIFICATE-----
MIIDSTCCAjGgAwIBAgIUdsC4uxTo/rzDM/J7znsoS68v1pQwDQYJKoZIhvcNAQEL
BQAwNDEyMDAGA1UEAxMpRWxhc3RpYyBDZXJ0aWZpY2F0ZSBUb29sIEF1dG9nZW5l
cmF0ZWQgQ0EwHhcNMjQwODIxMTI0MTQwWhcNMjcwODIxMTI0MTQwWjA0MTIwMAYD
VQQDEylFbGFzdGljIENlcnRpZmljYXRlIFRvb2wgQXV0b2dlbmVyYXRlZCBDQTCC
ASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAKS/NBEh8pMqJ6TMsaqNndG2
3D3P/ApYXXD2udC1O5o9r2i/dlkuzjrYVJicj/qK+Qj3RYQrnOdt3ztWXDnmdVgV
V7csJEsM6oDWtqu+Bpn02G0bB496Mel6DpsTpFmWExWqUKvgeHvJb4zrOVGLkxqZ
0HwEnz9PxTQEudUYZw+rgeDx3aSacKuTFDl8Ez15RBtrQ8VCy5dwGz3U149SFxTh
yQHDj+gbSUqUPPz/lKnXXnQCFvVLZjRfUW96g1vl67/2aHtuFNfujA4wjK8kO4ZD
QgqpxxxoQ34iJB5NfY4HgeCpdlXMOuLXPPsTuTwtvAxdxWPrBor29BHum0quTr8C
AwEAAaNTMFEwHQYDVR0OBBYEFIaNPD+qx/HNPjx7ATpBSJDX6JMgMB8GA1UdIwQY
MBaAFIaNPD+qx/HNPjx7ATpBSJDX6JMgMA8GA1UdEwEB/wQFMAMBAf8wDQYJKoZI
hvcNAQELBQADggEBAA/by7yposgbigBLuR+XhmZYfbBJS8NgJ7b8VGtFLRjgJubD
r/YBgGbIGzx1Mhn0PbOUsSimXuHcs8ZOZGOLXASJioIkh7kW08p2xJe1SAGqwPx+
pDcc6EgWaVmZMXcvQwy+ExD+5otjge5MSHA7swAIiZ0y1OwifnrIVVBlfmw2lZIm
E+JOCKsjs85H2msYRdoB3ELdXKGt27xvQV5V2WP0fTgkiUmkLfWM5PU3XrYMEiDs
FCacWYL0PcnVTTHMXdtIkaAhxnpfGdCaUBEsR5v+LDn97K7PozeQdxF2k0HrxN11
a+WpQ8myoX6lIZ6Oaq4KyFALXIhmaf5HBlAoZOE=
-----END CERTIFICATE-----也可以查询证书的到期时间:
elasticsearch@master01:~$ openssl pkcs12 -in es-ca.p12 -nodes -nokeys -clcerts | openssl x509 -enddate -noout
Enter Import Password:
notAfter=Aug 21 12:41:40 2027 GMT这里可以看到证书有效期大概是3年。
1.2,keytool
keytool这个工具是es内jdk自带的,也可以进行证书信息查看。
elasticsearch@master01:~$ jdk/bin/keytool -keystore es-ca.p12 -list
Enter keystore password:
Keystore type: PKCS12
Keystore provider: SUN
Your keystore contains 1 entry
ca, Aug 21, 2024, PrivateKeyEntry,
Certificate fingerprint (SHA-256): 60:95:CD:3B:4E:A0:D7:43:13:C2:F1:D9:11:B1:AA:B8:02:BB:2D:0E:3E:C5:CE:82:F5:8A:D7:49:99:A5:70:A7然后就可以通过这个文件去生成其他证书了。
(2)生成transport证书
常见的证书格式包括PKCS#12(.p12)和PEM(.pem)。这里需要利用得到的ca来创建transports证书,这里分别展示p12与pem格式的生成方式:
1、p12证书生成
elasticsearch@master01:~$ bin/elasticsearch-certutil cert --ca es-ca.p12
This tool assists you in the generation of X.509 certificates and certificate
signing requests for use with SSL/TLS in the Elastic stack.
The 'cert' mode generates X.509 certificate and private keys.
* By default, this generates a single certificate and key for use
on a single instance.
* The '-multiple' option will prompt you to enter details for multiple
instances and will generate a certificate and key for each one
* The '-in' option allows for the certificate generation to be automated by describing
the details of each instance in a YAML file
* An instance is any piece of the Elastic Stack that requires an SSL certificate.
Depending on your configuration, Elasticsearch, Logstash, Kibana, and Beats
may all require a certificate and private key.
* The minimum required value for each instance is a name. This can simply be the
hostname, which will be used as the Common Name of the certificate. A full
distinguished name may also be used.
* A filename value may be required for each instance. This is necessary when the
name would result in an invalid file or directory name. The name provided here
is used as the directory name (within the zip) and the prefix for the key and
certificate files. The filename is required if you are prompted and the name
is not displayed in the prompt.
* IP addresses and DNS names are optional. Multiple values can be specified as a
comma separated string. If no IP addresses or DNS names are provided, you may
disable hostname verification in your SSL configuration.
* All certificates generated by this tool will be signed by a certificate authority (CA)
unless the --self-signed command line option is specified.
The tool can automatically generate a new CA for you, or you can provide your own with
the --ca or --ca-cert command line options.
By default the 'cert' mode produces a single PKCS#12 output file which holds:
* The instance certificate
* The private key for the instance certificate
* The CA certificate
If you specify any of the following options:
* -pem (PEM formatted output)
* -multiple (generate multiple certificates)
* -in (generate certificates from an input file)
then the output will be be a zip file containing individual certificate/key files
#输入ca证书密码
Enter password for CA (es-ca.p12) :
#输入cert证书名称,默认为elastic-certificates.p12
Please enter the desired output file [elastic-certificates.p12]: es-cert.p12
#设置cert证书密码,默认为空
Enter password for es-cert.p12 :
Certificates written to /usr/share/elasticsearch/es-cert.p12
This file should be properly secured as it contains the private key for
your instance.
This file is a self contained file and can be copied and used 'as is'
For each Elastic product that you wish to configure, you should copy
this '.p12' file to the relevant configuration directory
and then follow the SSL configuration instructions in the product guide.
For client applications, you may only need to copy the CA certificate and
configure the client to trust this certificate.
elasticsearch@master01:~$ ls -l
total 2288
-r--r--r-- 1 root root 3860 Aug 5 10:11 LICENSE.txt
-r--r--r-- 1 root root 2285006 Aug 5 10:11 NOTICE.txt
-r--r--r-- 1 root root 9111 Aug 5 10:11 README.asciidoc
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:12 bin
drwxrwxr-x 1 elasticsearch root 4096 Aug 17 14:47 config
drwxrwxrwx 5 1001 1001 4096 Aug 21 12:45 data
-rw------- 1 elasticsearch root 2672 Aug 21 12:42 es-ca.p12
-rw------- 1 elasticsearch root 3596 Aug 21 12:46 es-cert.p12
dr-xr-xr-x 1 root root 4096 Aug 5 10:11 jdk
dr-xr-xr-x 6 root root 4096 Aug 5 10:11 lib
drwxrwxrwx 2 1001 1001 4096 Aug 21 12:25 logs
dr-xr-xr-x 83 root root 4096 Aug 5 10:11 modules
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:11 plugins设置密码后,一路回车就可以通过CA文件在该目录下生成 elastic-certificates.p12文件。就是es配置需要的文件了。
2、pem 和 key 证书生成
这种证书和HTTPS配置的证书文件类似,也能支持es进行安全配置。与上面的p12不同的是,它需要使用的是ca的压缩文件中的crt、key文件去生成对应的实例证书文件:
elasticsearch@es:~$ bin/elasticsearch-certutil ca --pem
This tool assists you in the generation of X.509 certificates and certificate
signing requests for use with SSL/TLS in the Elastic stack.
The 'ca' mode generates a new 'certificate authority'
This will create a new X.509 certificate and private key that can be used
to sign certificate when running in 'cert' mode.
Use the 'ca-dn' option if you wish to configure the 'distinguished name'
of the certificate authority
By default the 'ca' mode produces a single PKCS#12 output file which holds:
* The CA certificate
* The CA's private key
If you elect to generate PEM format certificates (the -pem option), then the output will
be a zip file containing individual files for the CA certificate and private key
Please enter the desired output file [elastic-stack-ca.zip]:
elasticsearch@es:~$ ll
total 2272
drwxrwxr-x 1 root root 4096 Mar 8 09:16 ./
drwxr-xr-x 1 root root 4096 Sep 14 20:23 ../
-rw------- 1 elasticsearch root 101 Mar 8 02:16 .bash_history
-rw-r--r-- 1 root root 220 Sep 14 20:23 .bash_logout
-rw-r--r-- 1 root root 3771 Sep 14 20:23 .bashrc
drwxrwxr-x 3 elasticsearch root 4096 Mar 8 01:46 .cache/
-rw-r--r-- 1 root root 807 Sep 14 20:23 .profile
-r--r--r-- 1 root root 3860 Sep 14 20:22 LICENSE.txt
-r--r--r-- 1 root root 2231504 Sep 14 20:22 NOTICE.txt
-r--r--r-- 1 root root 8157 Sep 14 20:22 README.asciidoc
drwxrwxr-x 1 elasticsearch root 4096 Sep 14 20:23 bin/
drwxrwxr-x 1 elasticsearch root 4096 Mar 8 02:04 config/
drwxrwxrwx 5 777 root 4096 Mar 8 09:15 data/
-rw------- 1 elasticsearch root 2514 Mar 8 09:16 elastic-stack-ca.zip
dr-xr-xr-x 1 root root 4096 Sep 14 20:22 jdk/
dr-xr-xr-x 5 root root 4096 Sep 14 20:22 lib/
drwxrwxrwx 2 777 root 4096 Mar 8 06:23 logs/
dr-xr-xr-x 76 root root 4096 Sep 14 20:22 modules/
drwxrwxr-x 1 elasticsearch root 4096 Sep 14 20:22 plugins/这种方式会生成一个存放ca文件的zip压缩文件,解压后继续生成实际的证书文件:
elasticsearch@es:~$ bin/elasticsearch-certutil cert -ca-cert ca/ca.crt -ca-key ca/ca.key --pem
This tool assists you in the generation of X.509 certificates and certificate
signing requests for use with SSL/TLS in the Elastic stack.
The 'cert' mode generates X.509 certificate and private keys.
* By default, this generates a single certificate and key for use
on a single instance.
* The '-multiple' option will prompt you to enter details for multiple
instances and will generate a certificate and key for each one
* The '-in' option allows for the certificate generation to be automated by describing
the details of each instance in a YAML file
* An instance is any piece of the Elastic Stack that requires an SSL certificate.
Depending on your configuration, Elasticsearch, Logstash, Kibana, and Beats
may all require a certificate and private key.
* The minimum required value for each instance is a name. This can simply be the
hostname, which will be used as the Common Name of the certificate. A full
distinguished name may also be used.
* A filename value may be required for each instance. This is necessary when the
name would result in an invalid file or directory name. The name provided here
is used as the directory name (within the zip) and the prefix for the key and
certificate files. The filename is required if you are prompted and the name
is not displayed in the prompt.
* IP addresses and DNS names are optional. Multiple values can be specified as a
comma separated string. If no IP addresses or DNS names are provided, you may
disable hostname verification in your SSL configuration.
* All certificates generated by this tool will be signed by a certificate authority (CA)
unless the --self-signed command line option is specified.
The tool can automatically generate a new CA for you, or you can provide your own with
the --ca or --ca-cert command line options.
By default the 'cert' mode produces a single PKCS#12 output file which holds:
* The instance certificate
* The private key for the instance certificate
* The CA certificate
If you specify any of the following options:
* -pem (PEM formatted output)
* -multiple (generate multiple certificates)
* -in (generate certificates from an input file)
then the output will be be a zip file containing individual certificate/key files
Please enter the desired output file [certificate-bundle.zip]:
Certificates written to /usr/share/elasticsearch/certificate-bundle.zip
This file should be properly secured as it contains the private key for
your instance.
After unzipping the file, there will be a directory for each instance.
Each instance has a certificate and private key.
For each Elastic product that you wish to configure, you should copy
the certificate, key, and CA certificate to the relevant configuration directory
and then follow the SSL configuration instructions in the product guide.
For client applications, you may only need to copy the CA certificate and
configure the client to trust this certificate.
elasticsearch@es:~$ ls
LICENSE.txt ca/ elastic-certificates.p12 lib/
NOTICE.txt certificate-bundle.zip elastic-stack-ca.p12 logs/
README.asciidoc config/ elastic-stack-ca.zip modules/
bin/ data/ jdk/ plugins/这样会生成最终的一个 名为certificate-bundle.zip的压缩包,解压后即可得到我们需要的配置文件:
elasticsearch@es:~$ unzip certificate-bundle.zip
Archive: certificate-bundle.zip
creating: instance/
inflating: instance/instance.crt
inflating: instance/instance.key
elasticsearch@es:~$ cd instance/
elasticsearch@es:~/instance$ ll
total 20
drwxr-xr-x 2 elasticsearch root 4096 Mar 8 09:20 ./
drwxrwxr-x 1 root root 4096 Mar 8 09:21 ../
-rw-r--r-- 1 elasticsearch root 1147 Mar 8 09:20 instance.crt
-rw-r--r-- 1 elasticsearch root 1679 Mar 8 09:20 instance.key同样可以通过openssl查看证书信息:
elasticsearch@es:~$ openssl x509 -in instance/instance.crt -text -noout
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
d4:80:94:4c:38:b5:67:ae:c5:b1:38:25:2c:2c:fe:a2:71:b0:6b:b6
Signature Algorithm: sha256WithRSAEncryption
Issuer: CN = Elastic Certificate Tool Autogenerated CA
Validity
Not Before: Mar 8 09:20:09 2024 GMT
Not After : Mar 8 09:20:09 2027 GMT
Subject: CN = instance
Subject Public Key Info:
Public Key Algorithm: rsaEncryption
RSA Public-Key: (2048 bit)
Modulus:
00:c7:ed:e3:5b:72:6e:c8:a7:5f:d6:8f:a2:99:3a:
62:18:fe:fd:b8:18:4f:c8:af:59:1d:cd:9c:fc:fb:
de:49:df:a3:d1:35:06:68:e6:76:6d:7f:fb:0e:88:
d8:ff:62:9f:52:9c:8b:a3:a7:10:89:72:98:9c:01:
d3:60:44:07:64:ad:d3:ce:f4:ce:d3:e9:a5:81:30:
40:0e:3d:c9:29:ac:36:33:28:19:d1:aa:2f:87:17:
4a:a7:6d:65:29:96:24:31:3e:01:f8:4f:04:f3:a3:
20:a0:eb:21:36:f9:f0:e6:cb:b6:8f:fc:7d:dc:4f:
af:f5:e1:95:e0:9e:84:42:b7:5b:ad:67:7d:e1:59:
9c:7b:28:d6:01:54:d7:0f:ad:86:ce:38:33:8c:86:
4d:e9:46:89:c0:70:31:1e:03:e4:41:19:63:ab:dc:
4a:50:d7:02:91:b7:70:15:f7:61:61:4f:3e:14:31:
0f:74:11:9f:2e:e4:56:d4:97:2e:78:81:f7:48:f8:
15:55:a7:c5:57:19:ef:5e:62:b8:8b:3f:e6:be:c5:
04:2d:41:72:14:a9:e9:e7:be:08:03:39:d8:8b:94:
d7:ec:10:24:8a:ac:32:b9:0b:5b:ef:7e:33:4f:b0:
76:24:97:52:f4:8d:b7:2c:cb:f4:89:fe:38:45:44:
5b:a1
Exponent: 65537 (0x10001)
X509v3 extensions:
X509v3 Subject Key Identifier:
FC:02:3C:5E:9B:4B:35:54:96:AB:5D:AB:7E:C7:08:CE:2C:94:05:CE
X509v3 Authority Key Identifier:
keyid:7E:52:11:3B:5C:88:9D:6A:27:2D:27:28:60:2F:34:E5:C4:0C:68:9A
X509v3 Basic Constraints:
CA:FALSE
Signature Algorithm: sha256WithRSAEncryption
6b:e3:ed:40:50:59:3f:3f:b3:7a:5a:a5:b9:ab:06:d5:28:18:
4d:17:89:ad:ab:dc:3d:0f:38:18:e9:82:0b:8a:b3:05:5f:4b:
1a:5a:44:46:8c:ac:df:28:41:1a:76:b4:95:51:86:c0:2a:bf:
13:47:0e:76:6b:08:d8:aa:06:ba:5c:50:11:a9:71:3b:9d:77:
24:ac:bb:c2:06:85:d8:01:ec:4a:e4:75:ae:29:66:84:0f:ad:
c6:83:8e:5b:61:23:74:af:44:7c:9b:8a:47:b2:fb:a3:3f:f8:
c0:dc:37:36:38:d7:d2:e5:8e:8c:9b:64:3b:ae:26:41:6b:42:
dc:f4:e3:d9:83:fe:f9:d9:2d:b2:7a:dc:74:74:f2:bd:5f:5f:
37:5b:ad:b5:02:20:3a:33:cd:76:d1:0c:8d:84:61:b2:5d:a7:
80:59:9a:e0:bd:d3:ba:ee:a3:8b:47:f0:07:08:53:7d:98:8e:
2a:06:2d:a8:aa:54:45:f7:ae:af:42:dd:80:b1:15:4d:a9:36:
46:ce:9c:8c:1c:74:7b:19:41:d4:aa:f1:65:ef:c9:c8:6c:44:
b1:49:66:56:f8:fd:e3:c5:0a:7b:1c:76:77:05:37:a7:77:4c:
a1:47:45:b8:49:55:b6:3c:f6:1c:64:a9:16:cc:7e:2c:57:a9:
72:15:ad:16然后我们可以将上述过程涉及到的密码存储到es的密钥库。bin/elasticsearch-keystore 是 Elasticsearch 提供的一个命令行工具,用于管理 Elasticsearch 的密钥库(keystore)。密钥库用于存储敏感配置,如密码、API 密钥等,以确保这些敏感信息在配置文件中不会以明文形式出现。
elasticsearch@master01:~$ bin/elasticsearch-keystore add xpack.security.transport.ssl.keystore.secure_password
Enter value for es-ca-pwd:
elasticsearch@master01:~$ bin/elasticsearch-keystore add xpack.security.transport.ssl.truststore.secure_password
Enter value for es-pwd:
elasticsearch@master01:~$ bin/elasticsearch-keystore list
bootstrap.password
keystore.seed
xpack.security.transport.ssl.keystore.secure_password
xpack.security.transport.ssl.truststore.secure_password将生成的p12文件拷贝到config目录下,怕容器文件丢失的话也可以将生成的证书文件拷贝到宿主机的es/config文件下,重新修改yml配置文件,增加transport.ssl配置:
#将容器内的p12文件拷贝的容器内的config目录下,以便es识别
elasticsearch@master01:/data/elk/es$ sudo docker exec -i es cp es-cert.p12 config/
elasticsearch@master01:/data/elk/es$ cat config/elasticsearch.yml
#集群名称
cluster.name: "es-master"
# 0.0.0.0为不限制,生产环境请设置为固定IP
network.host: 192.168.1.200
#设置对外服务的http端口,默认为9200
http.port: 9200
http.cors.enabled: true
#允许REST请求来自何处
http.cors.allow-origin: "*"
# 开启x-pack安全验证 访问时需要密码
xpack.security:
enabled: true
transport.ssl:
enabled: true
verification_mode: certificate
client_authentication: required
keystore.path: es-cert.p12
truststore.path: es-cert.p12
elasticsearch@master01:/data/elk/es$ sudo docker restart es
es此时访问kibana的话就需要进行配置了:

如果不继续进行https配置就可以到此为止了,不过这里咱们继续配置下去~
(3)生成http证书
执行http生成命令,具体生成过程如下:
elasticsearch@es:~$ bin/elasticsearch-certutil http
## Elasticsearch HTTP Certificate Utility
The 'http' command guides you through the process of generating certificates
for use on the HTTP (Rest) interface for Elasticsearch.
This tool will ask you a number of questions in order to generate the right
set of files for your needs.
## Do you wish to generate a Certificate Signing Request (CSR)?
A CSR is used when you want your certificate to be created by an existing
Certificate Authority (CA) that you do not control (that is, you don't have
access to the keys for that CA).
If you are in a corporate environment with a central security team, then you
may have an existing Corporate CA that can generate your certificate for you.
Infrastructure within your organisation may already be configured to trust this
CA, so it may be easier for clients to connect to Elasticsearch if you use a
CSR and send that request to the team that controls your CA.
If you choose not to generate a CSR, this tool will generate a new certificate
for you. That certificate will be signed by a CA under your control. This is a
quick and easy way to secure your cluster with TLS, but you will need to
configure all your clients to trust that custom CA.
Generate a CSR? [y/N]N #不用生成,我们用自己的CA
## Do you have an existing Certificate Authority (CA) key-pair that you wish to use to sign your certificate?
If you have an existing CA certificate and key, then you can use that CA to
sign your new http certificate. This allows you to use the same CA across
multiple Elasticsearch clusters which can make it easier to configure clients,
and may be easier for you to manage.
If you do not have an existing CA, one will be generated for you.
Use an existing CA? [y/N]y #用自己的CA
## What is the path to your CA?
Please enter the full pathname to the Certificate Authority that you wish to
use for signing your new http certificate. This can be in PKCS#12 (.p12), JKS
(.jks) or PEM (.crt, .key, .pem) format.
CA Path: /usr/share/elasticsearch/elastic-stack-ca.p12 #填CA地址
Reading a PKCS12 keystore requires a password.
It is possible for the keystore's password to be blank,
in which case you can simply press <ENTER> at the prompt
Password for elastic-stack-ca.p12:
## How long should your certificates be valid?
Every certificate has an expiry date. When the expiry date is reached clients
will stop trusting your certificate and TLS connections will fail.
Best practice suggests that you should either:
(a) set this to a short duration (90 - 120 days) and have automatic processes
to generate a new certificate before the old one expires, or
(b) set it to a longer duration (3 - 5 years) and then perform a manual update
a few months before it expires.
You may enter the validity period in years (e.g. 3Y), months (e.g. 18M), or days (e.g. 90D)
For how long should your certificate be valid? [5y] 5y #填过期时间
## Do you wish to generate one certificate per node?
If you have multiple nodes in your cluster, then you may choose to generate a
separate certificate for each of these nodes. Each certificate will have its
own private key, and will be issued for a specific hostname or IP address.
Alternatively, you may wish to generate a single certificate that is valid
across all the hostnames or addresses in your cluster.
If all of your nodes will be accessed through a single domain
(e.g. node01.es.example.com, node02.es.example.com, etc) then you may find it
simpler to generate one certificate with a wildcard hostname (*.es.example.com)
and use that across all of your nodes.
However, if you do not have a common domain name, and you expect to add
additional nodes to your cluster in the future, then you should generate a
certificate per node so that you can more easily generate new certificates when
you provision new nodes.
Generate a certificate per node? [y/N]y #添加节点了
## What is the name of node #1?
This name will be used as part of the certificate file name, and as a
descriptive name within the certificate.
You can use any descriptive name that you like, but we recommend using the name
of the Elasticsearch node.
node #1 name: es-master #单机的话就取个配置文件中的主节点名称,保持一致
## Which hostnames will be used to connect to es-master?
These hostnames will be added as "DNS" names in the "Subject Alternative Name"
(SAN) field in your certificate.
You should list every hostname and variant that people will use to connect to
your cluster over http.
Do not list IP addresses here, you will be asked to enter them later.
If you wish to use a wildcard certificate (for example *.es.example.com) you
can enter that here.
Enter all the hostnames that you need, one per line.
When you are done, press <ENTER> once more to move on to the next step.
www.myes.com #填连接到node的主机名
192.168.1.200
You entered the following hostnames.
- www.myes.com
Is this correct [Y/n]Y
## Which IP addresses will be used to connect to es-master?
If your clients will ever connect to your nodes by numeric IP address, then you
can list these as valid IP "Subject Alternative Name" (SAN) fields in your
certificate.
If you do not have fixed IP addresses, or not wish to support direct IP access
to your cluster then you can just press <ENTER> to skip this step.
Enter all the IP addresses that you need, one per line.
When you are done, press <ENTER> once more to move on to the next step.
192.168.1.200 #填连接到node的ip,如果没有固定ip获取,不希望ip访问就回车跳过
You entered the following IP addresses.
- 192.168.1.200
Is this correct [Y/n]Y
## Other certificate options
The generated certificate will have the following additional configuration
values. These values have been selected based on a combination of the
information you have provided above and secure defaults. You should not need to
change these values unless you have specific requirements.
Key Name: es-master
Subject DN: CN=es-master
Key Size: 2048
Do you wish to change any of these options? [y/N]N #还改不改这些选项
Generate additional certificates? [Y/n]N #还生成其他证书吗?一般集群用
## What password do you want for your private key(s)?
Your private key(s) will be stored in a PKCS#12 keystore file named "http.p12".
This type of keystore is always password protected, but it is possible to use a
blank password.
If you wish to use a blank password, simply press <enter> at the prompt below.
Provide a password for the "http.p12" file: [<ENTER> for none]#添加http.p12证书密码
Repeat password to confirm: #确认密码
## Where should we save the generated files?
A number of files will be generated including your private key(s),
public certificate(s), and sample configuration options for Elastic Stack products.
These files will be included in a single zip archive.
What filename should be used for the output zip file? [/usr/share/elasticsearch/elasticsearch-ssl-http.zip]
Zip file written to /usr/share/elasticsearch/elasticsearch-ssl-http.zip解压文件,生成一个文件夹,里面包含两个文件夹:
-
elasticsearch文件夹包含http.p12及elasticsearch.yml的配置参考
-
kibana文件夹包含elasticsearch-ca.pem及kibana.yml的配置参考
elasticsearch@master01:~$ unzip elasticsearch-ssl-http.zip
Archive: elasticsearch-ssl-http.zip
creating: elasticsearch/
inflating: elasticsearch/README.txt
inflating: elasticsearch/http.p12
inflating: elasticsearch/sample-elasticsearch.yml
creating: kibana/
inflating: kibana/README.txt
inflating: kibana/elasticsearch-ca.pem
inflating: kibana/sample-kibana.yml
elasticsearch@master01:~$ ls -l elasticsearch
total 12
-rw-r--r-- 1 elasticsearch root 1378 Aug 21 13:28 README.txt
-rw-r--r-- 1 elasticsearch root 3636 Aug 21 13:28 http.p12
-rw-r--r-- 1 elasticsearch root 858 Aug 21 13:28 sample-elasticsearch.yml
#拷贝到config下
elasticsearch@master01:~$ cp elasticsearch/http.p12 config/
elasticsearch@master01:~$ ls -l config/
total 72
-rw-rw-r-- 1 root root 1042 Aug 5 10:11 elasticsearch-plugins.example.yml
-rw-rw---- 1 elasticsearch root 425 Aug 22 05:52 elasticsearch.keystore
-rwxrwxrwx 1 1001 1001 581 Aug 22 06:28 elasticsearch.yml
-rw------- 1 elasticsearch root 3596 Aug 22 05:31 es-cert.p12
-rw-r--r-- 1 elasticsearch root 3652 Aug 22 06:30 http.p12
-rw-rw-r-- 1 root root 2727 Aug 5 10:11 jvm.options
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:11 jvm.options.d
-rw-rw-r-- 1 root root 17969 Aug 5 10:11 log4j2.file.properties
-rw-rw-r-- 1 root root 12549 Aug 5 10:11 log4j2.properties
-rw-rw-r-- 1 root root 473 Aug 5 10:11 role_mapping.yml
-rw-rw-r-- 1 root root 197 Aug 5 10:11 roles.yml
-rw-rw-r-- 1 root root 0 Aug 5 10:11 users
-rw-rw-r-- 1 root root 0 Aug 5 10:11 users_roles后者kibana目录,其中包含一个elasticsearch-ca.pem文件。主要用于配置Kibana,使其信任HTTP层的Elasticsearch CA。两个目录下都给出了具体的配置方式:
elasticsearch@master01:~$ cat elasticsearch/sample-elasticsearch.yml
#
# SAMPLE ELASTICSEARCH CONFIGURATION FOR ENABLING SSL ON THE HTTP INTERFACE
#
# This is a sample configuration snippet for Elasticsearch that enables and configures SSL for the HTTP (Rest) interface
#
# This was automatically generated at: 2024-08-22 05:47:20Z
# This configuration was intended for Elasticsearch version 8.15.0
#
# You should review these settings, and then update the main configuration file at
# /usr/share/elasticsearch/config/elasticsearch.yml
#
# This turns on SSL for the HTTP (Rest) interface
xpack.security.http.ssl.enabled: true
# This configures the keystore to use for SSL on HTTP
# Because your keystore has a password, you will also need to add the password to the Elasticsearch keystore
# elasticsearch-keystore add "xpack.security.http.ssl.keystore.secure_password"
xpack.security.http.ssl.keystore.path: "http.p12"
elasticsearch@master01:~$ cat kibana/sample-kibana.yml
#
# SAMPLE KIBANA CONFIGURATION FOR ENABLING SSL TO ELASTICSEARCH
#
# This is a sample configuration snippet for Kibana that configures SSL for connections to Elasticsearch
#
# This was automatically generated at: 2024-08-22 05:47:20Z
# This configuration was intended for version 8.15.0
#
# You should review these settings, and then update the main kibana.yml configuration file.
#
#-------------------------------------------------------------------------------------------------
# You also need to update the URLs in your "elasticsearch.hosts" setting to use the "https" URL.
# e.g. If your kibana.yml file currently has
#
# elasticsearch.hosts: [ "http://localhost:9200" ]
#
# then you should change this to:
#
# elasticsearch.hosts: [ "https://localhost:9200" ]
#
#-------------------------------------------------------------------------------------------------
# This configures Kibana to trust a specific Certificate Authority for connections to Elasticsearch
elasticsearch.ssl.certificateAuthorities: [ "config/elasticsearch-ca.pem" ]因此生成的kibana的文件信息建议拷贝到容器外面的kibana目录下,后面方便使用。
root@master01:/data/elk/kibana/config# docker cp es:/usr/share/elasticsearch/kibana/elasticsearch-ca.pem /data/elk/kibana/config/
Successfully copied 3.07kB to /data/elk/kibana/config/
root@master01:/data/elk/kibana/config# docker cp es:/usr/share/elasticsearch/kibana/sample-kibana.yml /data/elk/kibana/config/
Successfully copied 3.07kB to /data/elk/kibana/config/
root@master01:/data/elk/kibana/config# ls
elasticsearch-ca.pem kibana.yml sample-kibana.yml现在可以验证一下证书信息:
elasticsearch@master01:~$ jdk/bin/keytool -keystore elasticsearch/http.p12 -list
Enter keystore password:
Keystore type: PKCS12
Keystore provider: SUN
Your keystore contains 2 entries
ca, Aug 21, 2024, trustedCertEntry,
Certificate fingerprint (SHA-256): 60:95:CD:3B:4E:A0:D7:43:13:C2:F1:D9:11:B1:AA:B8:02:BB:2D:0E:3E:C5:CE:82:F5:8A:D7:49:99:A5:70:A7
http, Aug 21, 2024, PrivateKeyEntry,
Certificate fingerprint (SHA-256): 78:48:07:F3:C8:1B:50:08:72:65:4A:19:F4:23:26:0D:BA:7F:1F:BE:11:87:74:8E:82:B7:27:D5:04:B4:03:8B
#添加http.p12密码到密钥库
elasticsearch@master01:~$ ./bin/elasticsearch-keystore add xpack.security.http.ssl.keystore.secure_password
Enter value for xpack.security.http.ssl.keystore.secure_password:(4)完整配置ES
将http.p12证书放到配置文件内,重新更新配置文件并重启ES:
elasticsearch@master01:/data/elk/es$ cat es/config/elasticsearch.yml
#集群名称
cluster.name: "es-master"
# 0.0.0.0为不限制,生产环境请设置为固定IP
network.host: 192.168.1.200
#设置对外服务的http端口,默认为9200
http.port: 9200
search.allow_expensive_queries: true
http.cors.enabled: true
#允许REST请求来自何处
http.cors.allow-origin: "*"
# 开启x-pack安全验证 访问时需要密码
xpack.security:
enabled: true
#generater kibana token,一般配合es的自动配置使用
# enrollment.enabled: true
#用于在传输网络层上启用或禁用 TLS/SSL,节点使用该层相互通信。 默认值为 。false
transport.ssl:
enabled: true
verification_mode: certificate
#full:验证提供的证书:是否具有颁发日期且在日期内;链接到受信任的证书权威(CA);检查证书。
#certificate:验证提供的证书,并验证它是否由受信任的颁发机构 (CA),但不检查证书。
#none:不执行证书验证
client_authentication: required
keystore.path: es-cert.p12
truststore.path: es-cert.p12
# Enable encryption for HTTP API client connections, such as Kibana, Logstash
http.ssl:
enabled: true
verification_mode: certificate
keystore.path: http.p12最后就可以通过https+ip:端口以密码的形式访问ES了。

 然后就可以进入kibana页面进行es连接配置了。可以通过es获取注册令牌进行配置:
然后就可以进入kibana页面进行es连接配置了。可以通过es获取注册令牌进行配置:

也可以直接手动配置:

这里我们没有填写es配置情况下可以直接进行手动配置:
-
填写es的地址,笔者的是https:192.168.31.133:9200(没有配置https也可用http的)
-
输入kibana_system的密码
-
之后界面会提示我们通过一个命令获取验证码并填写,进入kibana容器按要求获取填写即可。

root@master01:/data/elk/kibana/config# docker exec -i kibana bin/kibana-verification-code
Kibana is currently running with legacy OpenSSL providers enabled! For details and instructions on how to disable see https://www.elastic.co/guide/en/kibana/8.15/production.html#openssl-legacy-provider
Your verification code is: 920 675 然后静等配置完成即可重新访问kibana可视化界面了。


如果登录不上可根据kibana日志和es日志一起解决。比如笔者使用的时候因为虚拟机内存不够导致ElasticSerach 出现 high disk watermark [90%]出现磁盘内存不足的问题,导致kibana登录不上。后面在elasticsearch.yml上配置cluster.routing.allocation.disk.threshold_enabled: false解决了。所以如果有问题,咱们多看日志都是可以认证登录成功的。
此时查看一下本地的kibana配置文件可以发现,之前kibana配置中注销的es配置信息已经自动生成了。
root@master01:/data/elk/kibana/config# cat kibana.yml
server.name: kibana
server.port: 5601
server.host: "0.0.0.0"
xpack.monitoring.ui.container.elasticsearch.enabled: true
telemetry.enabled: false
i18n.locale: "zh-CN"
# This section was automatically generated during setup.
elasticsearch.hosts: ['https://192.168.1.200:9200']
elasticsearch.username: kibana_system
elasticsearch.password: elastic
elasticsearch.ssl.certificateAuthorities: [/usr/share/kibana/data/ca_1724313143926.crt]
xpack.fleet.outputs: [{id: fleet-default-output, name: default, is_default: true, is_default_monitoring: true, type: elasticsearch, hosts: ['https://192.168.1.200:9200'], ca_trusted_fingerprint: 510c488576597352b09386b903a90e0c6c0ea030daa3328edb386a49298e7c1e}]三、Kibana 安全配置

这里笔者以es内部签名的证书来生成kibana的认证,但是官方也说到了,对于开发环境和构建概念证明是可以接受,但不应该在生产环境中使用。在投入生产之前,需要使用可信CA(如Let’s Encrypt)或组织的内部CA对证书进行签名。使用签名证书为Kibana内部访问或公共互联网的连接建立浏览器信任。毕竟这块我们没买正经证书,所以勉强把流程介绍一下吧。
首先我们需要在es中使用工具使用如下的命令为 Kibana 生成服务器证书和私钥:
#根据证书适配的ip生成,也可使用-dns形式的-dns 域名1,域名2
elasticsearch@master01:~$ bin/elasticsearch-certutil csr -name kibana -ip 192.168.1.200
This tool assists you in the generation of X.509 certificates and certificate
signing requests for use with SSL/TLS in the Elastic stack.
The 'csr' mode generates certificate signing requests that can be sent to
a trusted certificate authority
* By default, this generates a single CSR for a single instance.
* You can use the '-multiple' option to generate CSRs for multiple
instances, each with their own private key.
* The '-in' option allows for the CSR generation to be automated
by describing the details of each instance in a YAML file
* An instance is any piece of the Elastic Stack that requires an SSL certificate.
Depending on your configuration, Elasticsearch, Logstash, Kibana, and Beats
may all require a certificate and private key.
* The minimum required value for each instance is a name. This can simply be the
hostname, which will be used as the Common Name of the certificate. A full
distinguished name may also be used.
* A filename value may be required for each instance. This is necessary when the
name would result in an invalid file or directory name. The name provided here
is used as the directory name (within the zip) and the prefix for the key and
certificate files. The filename is required if you are prompted and the name
is not displayed in the prompt.
* IP addresses and DNS names are optional. Multiple values can be specified as a
comma separated string. If no IP addresses or DNS names are provided, you may
disable hostname verification in your SSL configuration.
The 'csr' mode produces a single zip file which contains the certificate
signing requests and private keys for each instance.
* Each certificate signing request is provided as a standard PEM encoding of a PKCS#10 CSR.
* Each key is provided as a PEM encoding of an RSA private key
Please enter the desired output file [csr-bundle.zip]:
Certificate signing requests have been written to /usr/share/elasticsearch/csr-bundle.zip
This file should be properly secured as it contains the private keys for all
instances.
After unzipping the file, there will be a directory for each instance containing
the certificate signing request and the private key. Provide the certificate
signing requests to your certificate authority. Once you have received the
signed certificate, copy the signed certificate, key, and CA certificate to the
configuration directory of the Elastic product that they will be used for and
follow the SSL configuration instructions in the product guide.
elasticsearch@master01:~$ ls -l
total 2308
-r--r--r-- 1 root root 3860 Aug 5 10:11 LICENSE.txt
-r--r--r-- 1 root root 2285006 Aug 5 10:11 NOTICE.txt
-r--r--r-- 1 root root 9111 Aug 5 10:11 README.asciidoc
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:12 bin
drwxrwxr-x 1 elasticsearch root 4096 Aug 22 09:24 config
-rw------- 1 elasticsearch root 2392 Aug 22 09:41 csr-bundle.zip
drwxrwxrwx 5 1001 1001 4096 Aug 22 09:41 data
drwxr-xr-x 2 elasticsearch root 4096 Aug 22 05:47 elasticsearch
-rw------- 1 elasticsearch root 7605 Aug 22 05:47 elasticsearch-ssl-http.zip
-rw------- 1 elasticsearch root 2672 Aug 22 05:05 es-ca.p12
-rw------- 1 elasticsearch root 3596 Aug 22 05:06 es-cert.p12
dr-xr-xr-x 1 root root 4096 Aug 5 10:11 jdk
drwxr-xr-x 2 elasticsearch root 4096 Aug 22 05:47 kibana
dr-xr-xr-x 6 root root 4096 Aug 5 10:11 lib
drwxrwxrwx 2 1001 1001 4096 Aug 22 09:24 logs
dr-xr-xr-x 83 root root 4096 Aug 5 10:11 modules
drwxrwxr-x 1 elasticsearch root 4096 Aug 5 10:11 plugins执行完成后会生成一个叫做 csr-bundle.zip 的文件,解压后的到kibana.csr(未签名安全证书),kibana.key(密钥未加密的私钥)文件。
elasticsearch@master01:~$ unzip csr-bundle.zip
Archive: csr-bundle.zip
inflating: kibana/kibana.csr
inflating: kibana/kibana.key
elasticsearch@master01:~$ ls -l kibana/
total 20
-rw-r--r-- 1 elasticsearch root 1306 Aug 22 05:47 README.txt
-rw-r--r-- 1 elasticsearch root 1200 Aug 22 05:47 elasticsearch-ca.pem
-rw-r--r-- 1 elasticsearch root 932 Aug 22 09:41 kibana.csr
-rw-r--r-- 1 elasticsearch root 1675 Aug 22 09:41 kibana.key
-rw-r--r-- 1 elasticsearch root 1052 Aug 22 05:47 sample-kibana.yml然后用这两个文件向您的内部CA或受信任的CA请求进行签名,以获得已签名的证书。签名的文件可以是不同的格式,例如.crt文件,如kibana-server.crt。这里我们用openssl通过命令生成kibana.crt:
elasticsearch@master01:~$ cd kibana/
elasticsearch@master01:~/kibana$ openssl x509 -req -in kibana.csr -signkey kibana.key -out kibana.crt
Signature ok
subject=CN = kibana
Getting Private key
elasticsearch@master01:~/kibana$ ls -l
total 24
-rw-r--r-- 1 elasticsearch root 1306 Aug 22 05:47 README.txt
-rw-r--r-- 1 elasticsearch root 1200 Aug 22 05:47 elasticsearch-ca.pem
-rw-r--r-- 1 elasticsearch root 985 Aug 22 09:48 kibana.crt
-rw-r--r-- 1 elasticsearch root 932 Aug 22 09:41 kibana.csr
-rw-r--r-- 1 elasticsearch root 1675 Aug 22 09:41 kibana.key
-rw-r--r-- 1 elasticsearch root 1052 Aug 22 05:47 sample-kibana.yml
elasticsearch@master01:/data/elk/es$ su
密码:
root@master01:/data/elk/kibana/config# ls
elasticsearch-ca.pem kibana.yml sample-kibana.yml
root@master01:/data/elk/kibana/config# docker cp es:/usr/share/elasticsearch/kibana/kibana.crt ./
Successfully copied 2.56kB to /data/elk/kibana/config/./
root@master01:/data/elk/kibana/config# docker cp es:/usr/share/elasticsearch/kibana/kibana.key ./
Successfully copied 3.58kB to /data/elk/kibana/config/./
root@master01:/data/elk/kibana/config# ls -l
总计 20
-rw-r--r-- 1 root root 1200 8月 22 13:47 elasticsearch-ca.pem
-rw-r--r-- 1 root root 985 8月 22 17:48 kibana.crt
-rw-r--r-- 1 root root 1675 8月 22 17:41 kibana.key
-rwxrwxrwx 1 root root 697 8月 22 17:28 kibana.yml
-rw-r--r-- 1 root root 1052 8月 22 13:47 sample-kibana.yml接下来在 Kibana 的配置文件 kibana.yml 中添加如下的配置:
server.ssl:
enbled: true
certificate: kibana.crt
key: kibana.key然后重启kibana,却发现kibana控制台会一直报这个问题:no such file or directory, open 'kibana.key'

但是这个文件实际上是存在的,于是笔者尝试把kibana的这两个文件放在容器外的kibana/config配置目录下,并给足777的权限,并将kibana.yml配置文件中的crt和key文件用本地全路径名显示,然后重启~
2024-08-22T10:29:13.994158970Z Error: ENOENT: no such file or directory, open '/data/elk/kibana/config/kibana.key'
2024-08-22T10:29:13.994161535Z at readFileSync (node:fs:448:20)
2024-08-22T10:29:13.994163709Z at readFile (/usr/share/kibana/node_modules/@kbn/server-http-tools/src/ssl/ssl_config.js:156:47)
2024-08-22T10:29:13.994165853Z at new SslConfig (/usr/share/kibana/node_modules/@kbn/server-http-tools/src/ssl/ssl_config.js:111:18)
2024-08-22T10:29:13.994167987Z at new HttpConfig (/usr/share/kibana/node_modules/@kbn/core-http-server-internal/src/http_config.js:356:16)
2024-08-22T10:29:13.994170132Z at /usr/share/kibana/node_modules/@kbn/core-http-server-internal/src/http_service.js:51:163
2024-08-22T10:29:13.994172215Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/map.js:10:37
2024-08-22T10:29:13.994174299Z at OperatorSubscriber._this._next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/OperatorSubscriber.js:33:21)
2024-08-22T10:29:13.994176464Z at OperatorSubscriber.Subscriber.next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Subscriber.js:51:18)
2024-08-22T10:29:13.994178598Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/observable/combineLatest.js:51:40
2024-08-22T10:29:13.994180702Z at OperatorSubscriber._this._next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/OperatorSubscriber.js:33:21)
2024-08-22T10:29:13.994182826Z at OperatorSubscriber.Subscriber.next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Subscriber.js:51:18)
2024-08-22T10:29:13.994184950Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/map.js:10:24
2024-08-22T10:29:13.994187034Z at OperatorSubscriber._this._next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/OperatorSubscriber.js:33:21)
2024-08-22T10:29:13.994189178Z at OperatorSubscriber.Subscriber.next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Subscriber.js:51:18)
2024-08-22T10:29:13.994191282Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/distinctUntilChanged.js:18:28
2024-08-22T10:29:13.994193386Z at OperatorSubscriber._this._next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/OperatorSubscriber.js:33:21)
2024-08-22T10:29:13.994195510Z at OperatorSubscriber.Subscriber.next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Subscriber.js:51:18)
2024-08-22T10:29:13.994198405Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/map.js:10:24
2024-08-22T10:29:13.994200539Z at OperatorSubscriber._this._next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/OperatorSubscriber.js:33:21)
2024-08-22T10:29:13.994202673Z at OperatorSubscriber.Subscriber.next (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Subscriber.js:51:18)
2024-08-22T10:29:13.994204797Z at ReplaySubject._subscribe (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/ReplaySubject.js:54:24)
2024-08-22T10:29:13.994218644Z at ReplaySubject.Observable._trySubscribe (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:41:25)
2024-08-22T10:29:13.994220918Z at ReplaySubject.Subject._trySubscribe (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Subject.js:123:47)
2024-08-22T10:29:13.994223072Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:35:31
2024-08-22T10:29:13.994225156Z at Object.errorContext (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/errorContext.js:22:9)
2024-08-22T10:29:13.994227260Z at ReplaySubject.Observable.subscribe (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:26:24)
2024-08-22T10:29:13.994229354Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/share.js:65:18
2024-08-22T10:29:13.994231428Z at OperatorSubscriber.<anonymous> (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/lift.js:14:28)
2024-08-22T10:29:13.994233963Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:30:30
2024-08-22T10:29:13.994236077Z at Object.errorContext (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/errorContext.js:22:9)
2024-08-22T10:29:13.994238191Z at Observable.subscribe (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:26:24)
2024-08-22T10:29:13.994240335Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/map.js:9:16
2024-08-22T10:29:13.994242399Z at OperatorSubscriber.<anonymous> (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/lift.js:14:28)
2024-08-22T10:29:13.994244583Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:30:30
2024-08-22T10:29:13.994246647Z at Object.errorContext (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/errorContext.js:22:9)
2024-08-22T10:29:13.994248771Z at Observable.subscribe (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:26:24)
2024-08-22T10:29:13.994250875Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/distinctUntilChanged.js:13:16
2024-08-22T10:29:13.994253179Z at OperatorSubscriber.<anonymous> (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/lift.js:14:28)
2024-08-22T10:29:13.994255343Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:30:30
2024-08-22T10:29:13.994257447Z at Object.errorContext (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/errorContext.js:22:9)
2024-08-22T10:29:13.994259561Z at Observable.subscribe (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:26:24)
2024-08-22T10:29:13.994261665Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/operators/map.js:9:16
2024-08-22T10:29:13.994263729Z at OperatorSubscriber.<anonymous> (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/lift.js:14:28)
2024-08-22T10:29:13.994265873Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:30:30
2024-08-22T10:29:13.994267947Z at Object.errorContext (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/util/errorContext.js:22:9)
2024-08-22T10:29:13.994273688Z at Observable.subscribe (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/Observable.js:26:24)
2024-08-22T10:29:13.994275882Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/observable/combineLatest.js:44:28
2024-08-22T10:29:13.994277996Z at maybeSchedule (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/observable/combineLatest.js:72:9)
2024-08-22T10:29:13.994280110Z at _loop_1 (/usr/share/kibana/node_modules/rxjs/dist/cjs/internal/observable/combineLatest.js:41:17)
2024-08-22T10:29:13.994282224Z at /usr/share/kibana/node_modules/rxjs/dist/cjs/internal/observable/combineLatest.js:61:17
2024-08-22T10:29:13.995961809Z
2024-08-22T10:29:13.995983350Z FATAL Error: ENOENT: no such file or directory, open '/data/elk/kibana/config/kibana.key'仍然不行,突然想起当初在kibana容器内部生成后没有cp到容器内的config目录下,而是拷贝出来了。所以那里没有文件,所以笔者考虑先拷贝进去重启试试:
root@master01:/data/elk/kibana/config# docker exec -i kibana ls -l config
total 8
-rwxrwxrwx 1 root root 775 Aug 22 09:54 kibana.yml
-rw-rw-r-- 1 kibana root 447 Aug 5 11:20 node.options
root@master01:/data/elk/kibana/config# docker cp kibana.key kibana:/usr/share/kibana/config
Successfully copied 3.58kB to kibana:/usr/share/kibana/config
root@master01:/data/elk/kibana/config# docker cp kibana.crt kibana:/usr/share/kibana/config
Successfully copied 2.56kB to kibana:/usr/share/kibana/config
root@master01:/data/elk/kibana/config# docker exec -i kibana ls -l config
total 16
-rw-r--r-- 1 root root 985 Aug 22 09:48 kibana.crt
-rwxrwxrwx 1 root root 1675 Aug 22 09:41 kibana.key
-rwxrwxrwx 1 root root 775 Aug 22 09:54 kibana.yml
-rw-rw-r-- 1 kibana root 447 Aug 5 11:20 node.options但是还是不对,仍然报错:

最后只有最后一个办法,将那两个文件全用容器内的绝对路径地址在kibana.yml文件中标识。
server.name: kibana
server.port: 5601
server.host: "0.0.0.0"
xpack.monitoring.ui.container.elasticsearch.enabled: true
telemetry.enabled: false
i18n.locale: "zh-CN"
# This section was automatically generated during setup.
elasticsearch.hosts: ['https://192.168.1.200:9200']
elasticsearch.username: kibana_system
elasticsearch.password: elastic
elasticsearch.ssl.certificateAuthorities: [/usr/share/kibana/data/ca_1724318819681.crt]
xpack.fleet.outputs: [{id: fleet-default-output, name: default, is_default: true, is_default_monitoring: true, type: elasticsearch, hosts: ['https://192.168.1.200:9200'], ca_trusted_fingerprint: 510c488576597352b09386b903a90e0c6c0ea030daa3328edb386a49298e7c1e}]
server.ssl:
enabled: true
certificate: /usr/share/kibana/config/kibana.crt
key: /usr/share/kibana/config/kibana.key得以解决。然后就能以https的形式访问kibana界面了~


四、Logstash配置补充
当我们在自己的硬件上运行Elasticsearch,并使用Elasticsearch集群的默认自签名证书,则需要以下步骤,以在Logstash和Elasticsearch之间建立安全通信。
首先需要将elasticsearch生成的部分证书文件从es容器内传到logstash的配置文件区。这里我们用的p12生成方式,所以包含es-cert.p12证书和http.p12证书。如果用的pem,那么就是crt的。
elasticsearch@master01:/root$ sudo docker cp es:/usr/share/elasticsearch/config/es-cert.p12 /data/elk/logstash/config
[sudo] elasticsearch 的密码:
Successfully copied 5.63kB to /data/elk/logstash/config
elasticsearch@master01:/root$ sudo docker cp es:/usr/share/elasticsearch/config/http.p12 /data/elk/logstash/config
Successfully copied 5.63kB to /data/elk/logstash/config
root@master01:/data/elk/logstash/config# chmod 777 es-cert.p12 http.p12
root@master01:/data/elk/logstash/config# ls -l
总计 20
-rwxrwxrwx 1 root root 3596 8月 22 13:31 es-cert.p12
-rwxrwxrwx 1 root root 3652 8月 22 16:46 http.p12
-rwxrwxrwx 1 root root 18 8月 18 13:00 jvm.options
-rwxrwxrwx 1 root root 60 8月 20 14:22 logstash.yml
-rwxrwxrwx 1 root root 66 8月 22 19:18 pipelines.yml然后修改管道配置文件中的output的es配置,添加ssl:
root@master01:/data/elk/logstash/config# vi ../pipeline/pipeline-springboot-log.conf
root@master01:/data/elk/logstash/config# cat ../pipeline/pipeline-springboot-log.conf
# 输入配置
input {
# beats {
# port => 5044
# client_inactivity_timeout => 36000
# }
redis {
host => "192.168.1.200"
port => "6379"
data_type => "list"
key => "filebeat-redis"
batch_count => "100"
db => "1"
}
}
# 过滤配置
filter {
grok {
match => { "message" => "%{SYSLOGTIMESTAMP:syslog_timestamp} %{SYSLOGHOST:syslog_hostname} %{DATA:syslog_program}(?:$%{POSINT:syslog_pid}$)?: %{GREEDYDATA:syslog_message}" }
}
date {
match => [ "syslog_timestamp", "MMM d HH:mm:ss", "MMM dd HH:mm:ss" ]
}
}
# 输出配置
output {
elasticsearch {
hosts => ["https://192.168.1.200:9200"]
user => "elastic"
password => "elastic"
ssl => true
ssl_certificate_verification =>true
keystore => "/usr/share/logstash/config/http.p12"
keystore_password => "elastic"
truststore => "/usr/share/logstash/config/es-cert.p12"
truststore_password => "elastic"
index => "logstash-addssl-%{+YYYY.MM.dd}"
}
stdout {
codec => rubydebug
}
}
root@master01:/data/elk/logstash/config# docker restart logstash
logstash配置说明
-
hosts:Elasticsearch的地址,使用HTTPS协议。 -
user和password:Logstash连接Elasticsearch时使用的用户名和密码。 -
ssl:启用SSL。 -
ssl_certificate_verification:启用证书验证。 -
keystore和keystore_password:Logstash使用的密钥库文件路径和密码。 -
truststore和truststore_password:Logstash使用的信任库文件路径和密码。
最后等待运行成功即可。有日志文件更新后便能在kibana中收集到最新的日志信息了:

五、后记
至于最后的Filebeat,由于不会直面kibana和ElasticSearch,因此也就没有配置的必要了。到此为止,整个日志系统的基础安全认证设置流程就结束了。当然这只是一个模拟ELFK搭建的配置情况,并没有涉及到集群管理,正式环境上可能面对的问题会更多,多看日志结合官方文档查找即可。如果不足之处,欢迎指正~