目录
Low难度
medium难度
Cross Site Request Forgery跨站的请求伪造
原理:利用受害者尚未失效的身份认证信息、会话;诱骗其访问黑客设计号的页面,在受害人不知情的情况下以受害人的身份向服务器发送请求完成非法操作
Low难度
源代码
<?php
if( isset( $_GET[ 'Change' ] ) ) {
// Get input
$pass_new = $_GET[ 'password_new' ];
$pass_conf = $_GET[ 'password_conf' ];
// Do the passwords match?
if( $pass_new == $pass_conf ) {
// They do!
$pass_new = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass_new ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$pass_new = md5( $pass_new );
// Update the database
$insert = "UPDATE `users` SET password = '$pass_new' WHERE user = '" . dvwaCurrentUser() . "';";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $insert ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
// Feedback for the user
echo "<pre>Password Changed.</pre>";
}
else {
// Issue with passwords matching
echo "<pre>Passwords did not match.</pre>";
}
((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}
?> 可以看见这模拟的是一个修改密码,代码的意思就是先判断输入的两个密码是否相等,如果一样的话就修改密码成功了否则就输出这个前后密码不匹配
我们随便输入两个123,查看网址
http://127.0.0.1/dvwa/vulnerabilities/csrf/?password_new=123&password_conf=123&Change=Change#
会返回一个change=change ,可以使用第一道题的暴力破解测试密码是否被成功修改
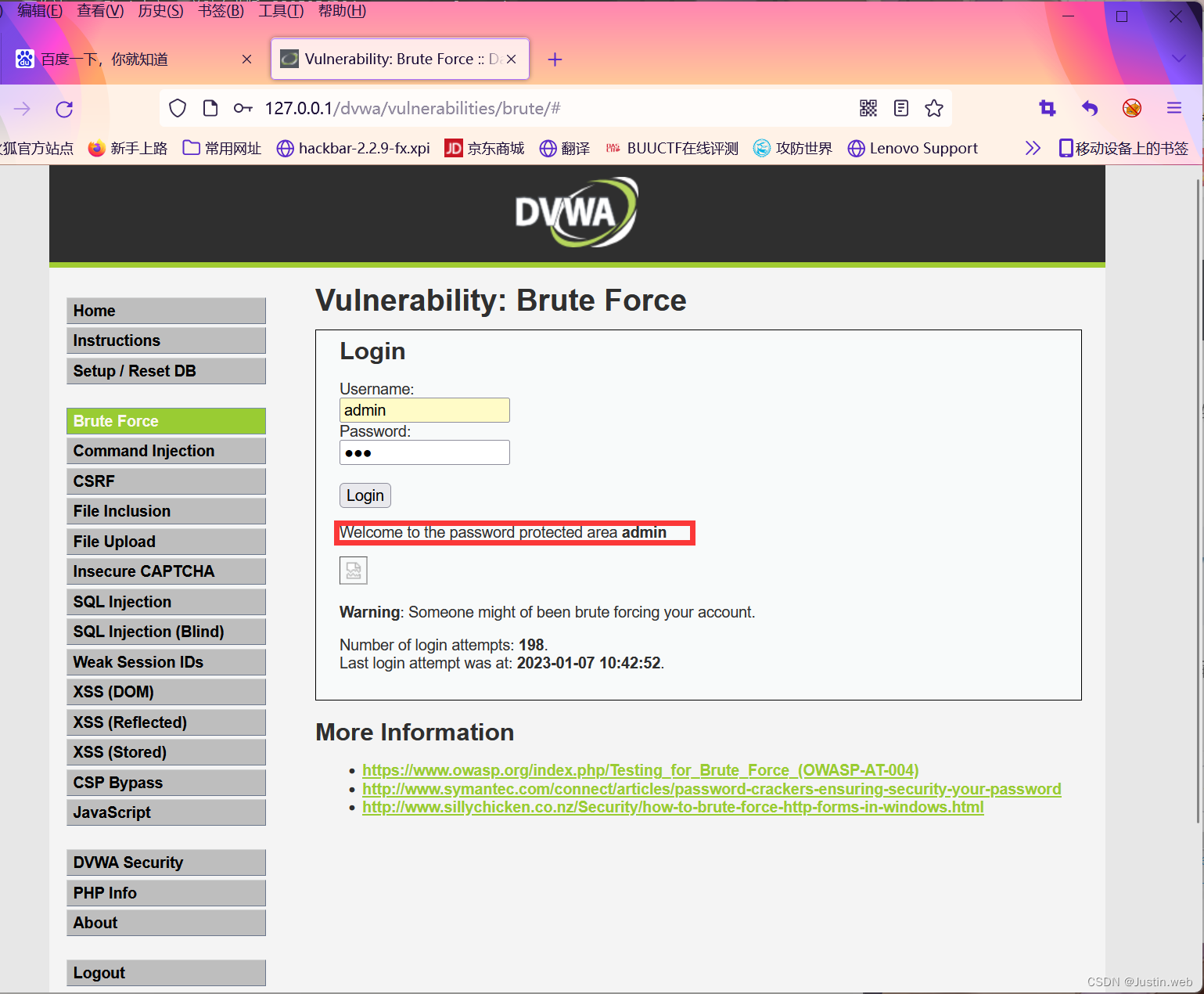
登陆成功,也就是密码被成功修改
我们修改网址中的123为456
http://127.0.0.1/dvwa/vulnerabilities/csrf/?password_new=456&password_conf=456&Change=Change#
再开一个网页进行测试,发现成功修改密码,注意要在同一个浏览器中进行,否则要重新修改cookie
由于这个链接太长,安全意识较高的人很容易识破,那么如果不被简单识破呢,我们直接百度生成短链接
http://ruyi.tv/7UNJn8
这个就是我们的诱骗网站,不容易被看出来
注意一个实例啊,前端时间一些人的企鹅留言板上出现一些短链接,说是什么老朋友的照片,点了之后QQ号就会被盗,这个就是利用了一个csrf的漏洞
medium难度
源代码
<?php
if( isset( $_GET[ 'Change' ] ) ) {
// Checks to see where the request came from
if( stripos( $_SERVER[ 'HTTP_REFERER' ] ,$_SERVER[ 'SERVER_NAME' ]) !== false ) {
// Get input
$pass_new = $_GET[ 'password_new' ];
$pass_conf = $_GET[ 'password_conf' ];
// Do the passwords match?
if( $pass_new == $pass_conf ) {
// They do!
$pass_new = ((isset($GLOBALS["___mysqli_ston"]) && is_object($GLOBALS["___mysqli_ston"])) ? mysqli_real_escape_string($GLOBALS["___mysqli_ston"], $pass_new ) : ((trigger_error("[MySQLConverterToo] Fix the mysql_escape_string() call! This code does not work.", E_USER_ERROR)) ? "" : ""));
$pass_new = md5( $pass_new );
// Update the database
$insert = "UPDATE `users` SET password = '$pass_new' WHERE user = '" . dvwaCurrentUser() . "';";
$result = mysqli_query($GLOBALS["___mysqli_ston"], $insert ) or die( '<pre>' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '</pre>' );
// Feedback for the user
echo "<pre>Password Changed.</pre>";
}
else {
// Issue with passwords matching
echo "<pre>Passwords did not match.</pre>";
}
}
else {
// Didn't come from a trusted source
echo "<pre>That request didn't look correct.</pre>";
}
((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res);
}
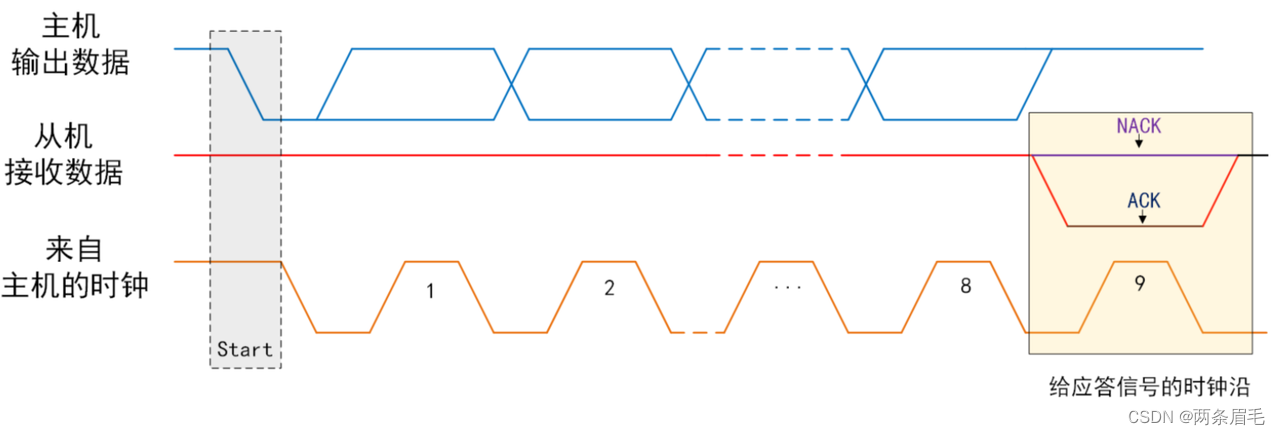
?> 用老办法尝试,不能就修改密码,因为增加了referer判断(通过抓包对比判断,不做演示了)
我们可以抓取low级别攻击代码的包增加referer,重新法宝即可成功绕过修改
![[Android Studio] 如何查看Android Studio的版本信息](https://img-blog.csdnimg.cn/24b696d76d374a9992017e1625389592.gif)