文章目录
- 一、建立HTTPS链接
- 1.在仓库服务器上获取TLS证书
- 1.1 生成证书颁发机构证书
- 1.2 生成服务器证书
- 1.3 利用证书运行仓库容器
- 2.让私有仓库支持HTTPS
- 3.客户端端配置
- 二、基本身份验证
- 三、对外隐藏仓库服务器
- 3.1 在服务器端
- 3.2 在客户端进行
- 四、仓库可视化
在前面的学习中,我们可以知道,我们所使用上传的镜像全都是公共镜像,镜像如果是商业机密,只能供公司内部人员使用,怎么办,这个就涉及到我们私有仓库的搭建。
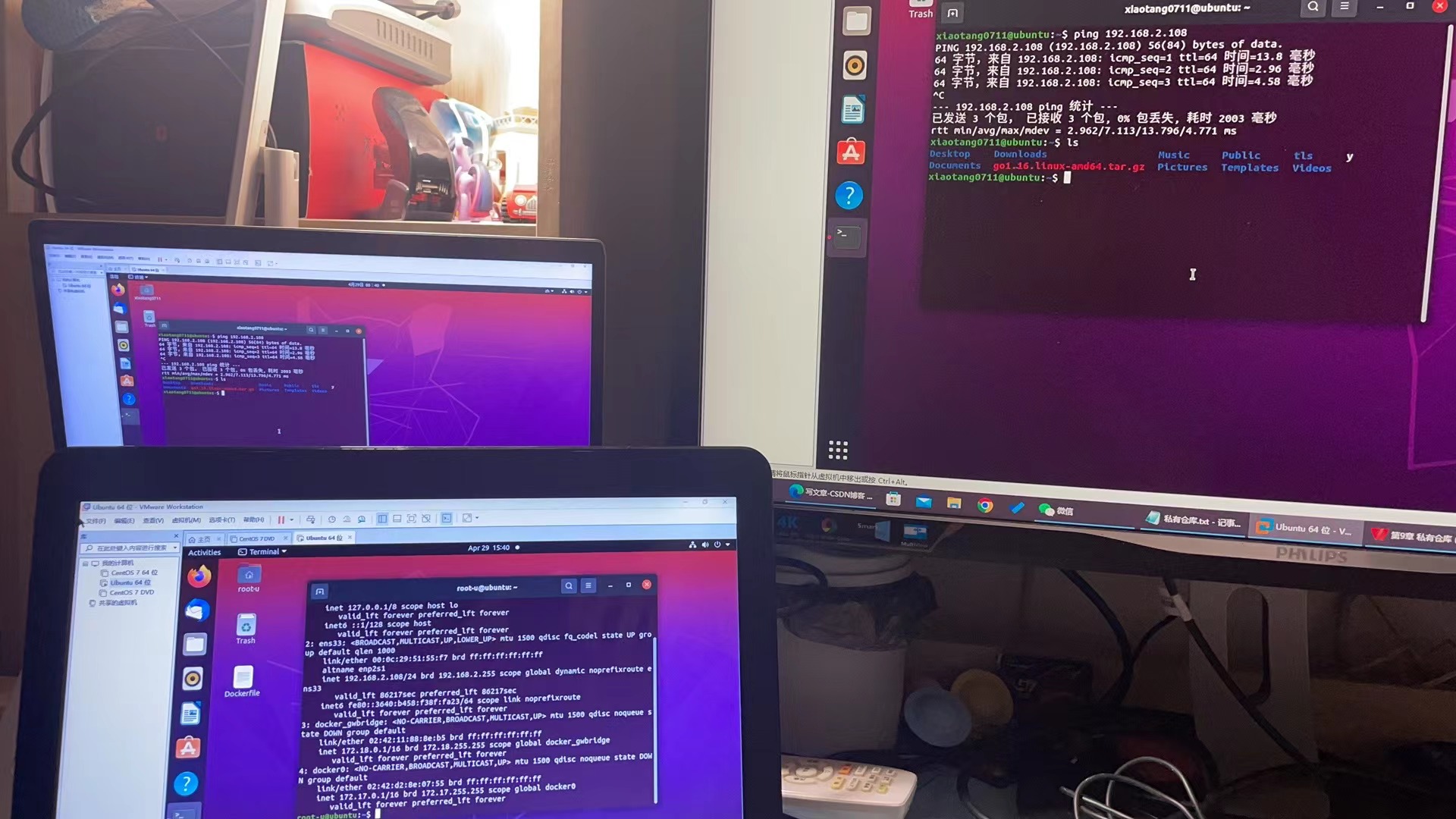
在这一章的学习中,我们就用两台主机,分别作为服务器端和客户端,现在我们开始吧!
| 名称 | IP地址 |
|---|---|
| 服务端 | 192.168.2.109 |
| 客户端 | 192.168.2.108 |
一、建立HTTPS链接
<registry.xinhua.com>可以替换
/opt/docker/registry/certs也地址可以进行修改
1.在仓库服务器上获取TLS证书
新建一个目录
sudo su
mkdir -p /opt/docker/registry/certs
cd /opt/docker/registry/certs
ls
1.1 生成证书颁发机构证书
生成 CA 证书私钥
openssl genrsa -out ca.key 4096
生成ca证书
openssl req -x509 -new -nodes -sha512 -days 3650 \
-subj "/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=registry.xinhua.com" \
-key ca.key \
-out ca.crt
1.2 生成服务器证书
生成私钥
openssl genrsa -out registry.xinhua.com.key 4096
生成证书签名请求 (CSR)
openssl req -sha512 -new \
-subj "/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=registry.xinhua.com" \
-key registry.xinhua.com.key \
-out registry.xinhua.com.csr
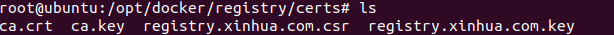
生成 x509 v3 扩展文件
cat > v3.ext <<-EOF
authorityKeyIdentifier=keyid,issuer
basicConstraints=CA:FALSE
keyUsage = digitalSignature, nonRepudiation, keyEncipherment, dataEncipherment
extendedKeyUsage = serverAuth
subjectAltName = @alt_names
[alt_names]
DNS.1=registry.xinhua.com
DNS.2=registry.xinhua
DNS.3=hostname
EOF
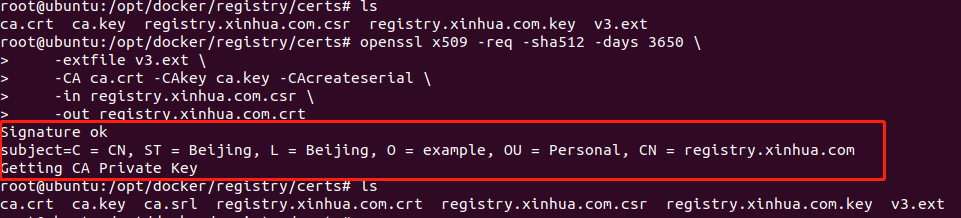
使用该文件为 主机生成证书v3.ext
openssl x509 -req -sha512 -days 3650 \
-extfile v3.ext \
-CA ca.crt -CAkey ca.key -CAcreateserial \
-in registry.xinhua.com.csr \
-out registry.xinhua.com.crt
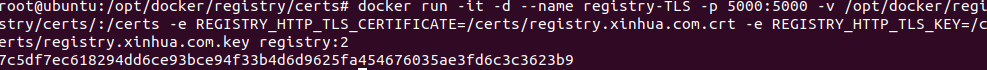
1.3 利用证书运行仓库容器
docker run -it -d --name registry-TLS -p 5000:5000 -v /opt/docker/registry/certs/:/certs -e REGISTRY_HTTP_TLS_CERTIFICATE=/certs/registry.xinhua.com.crt -e REGISTRY_HTTP_TLS_KEY=/certs/registry.xinhua.com.key registry:2
2.让私有仓库支持HTTPS
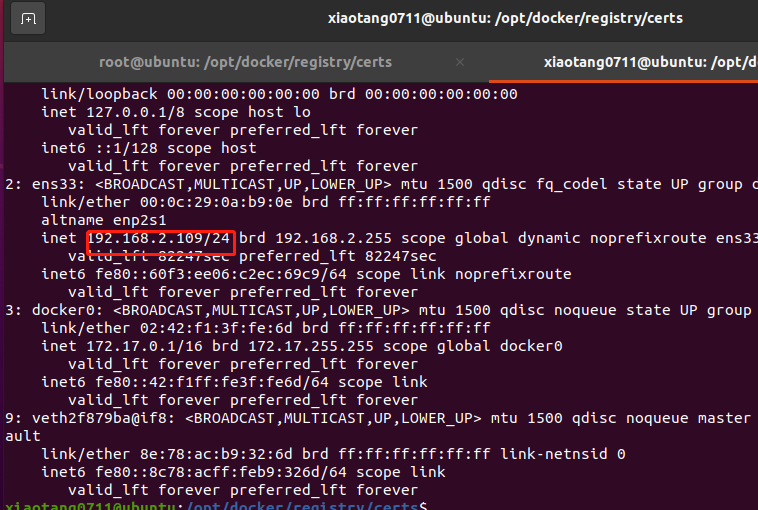
ip addr
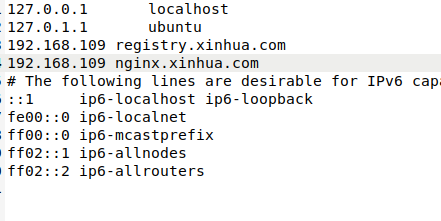
在仓库服务器和客户端配置域名解析
sudo gedit /etc/hosts
192.168.2.109 registry.xinhua.com
192.168.2.109 nginx.xinhua.com
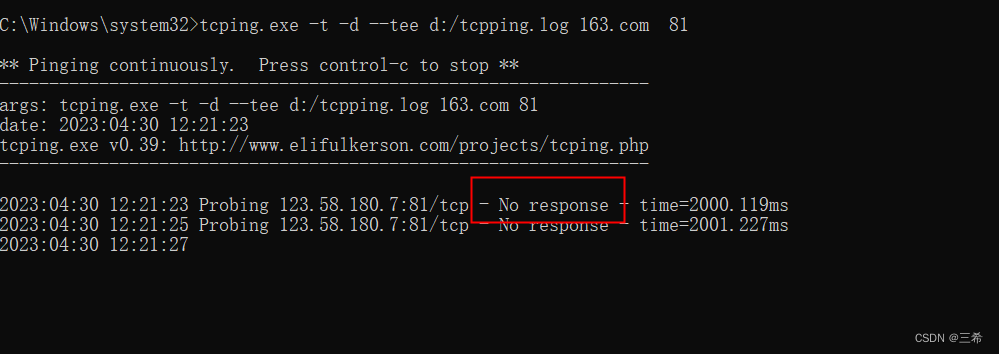
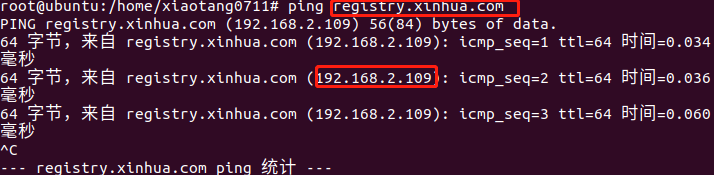
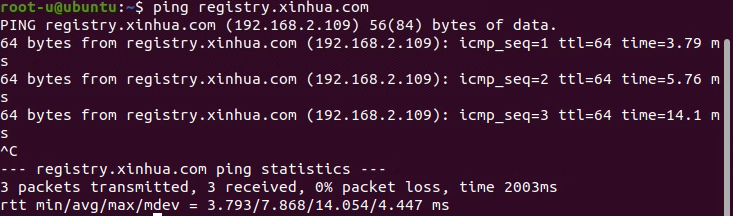
验证一下
ping registry.xinhua.com
3.客户端端配置
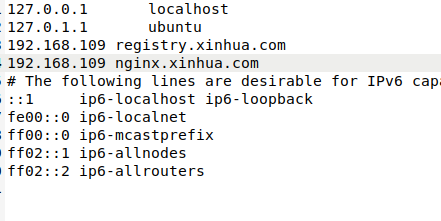
在仓库服务器和客户端配置域名解析
sudo gedit /etc/hosts
<服务器ip>
192.168.2.109 registry.xinhua.com
192.168.2.109 nginx.xinhua.com
验证一下
ping registry.xinhua.com
客户端安装open-ssh server
apt-get install openssh-server
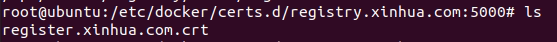
在客户端上创建存储证书的目录
mkdir -p /etc/docker/certs.d/registry.xinhua.com\:5000
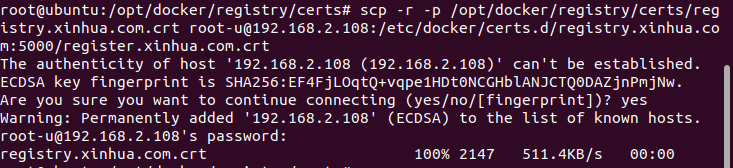
将服务器上的所有证书/opt/docker/registry/certs(.cert .key .crt)通过scp拷贝到创建客户端存储证书的目录服务端执行
修改服务端权限:chmod 777 /opt/docker/registry/certs
修改客户机权限:chmod 777 /etc/docker/certs.d/registry.xinhua.com:5000
scp -r -p /etc/docker/certs.d/registry.xinhua.com:5000/register.xinhua.com.crt username@serverip: /opt/docker/registry/certs/register.xinhua.com.crt
username<登录用户名你服务器的名字【就是你直接打开控制台的名字】>
serverip<客户端ip(ip addr查看)> 192.168.2.108
scp -r -p /opt/docker/registry/certs/registry.xinhua.com.crt root-u@192.168.2.108:/etc/docker/certs.d/registry.xinhua.com:5000/register.xinhua.com.crt
客户端
下面我们就来演示吧
| 名称 | IP地址 |
|---|---|
| 服务端 | 192.168.2.109 |
| 客户端 | 192.168.2.108 |
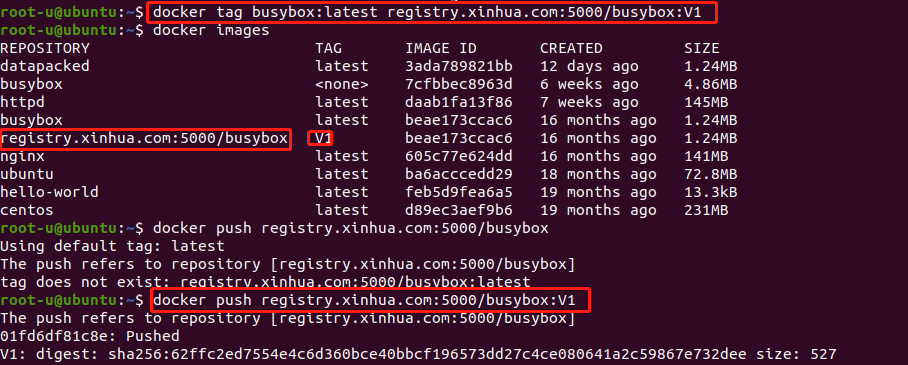
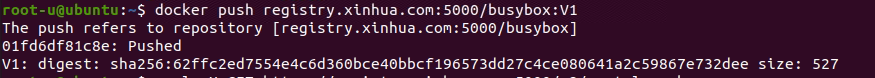
在客户端推送镜像
代码解释参考:Ubantu docker学习笔记(三)docker账号push及Dockerfile优化
docker tag busybox:latest registry.xinhua.com:5000/busybox:V1
docker push registry.xinhua.com:5000/busybox:V1
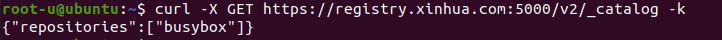
curl -X GET https://registry.xinhua.com:5000/v2/_catalog -k
二、基本身份验证
创建目录及用户密码文件
mkdir /opt/docker/registry/auth
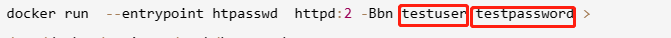
docker run --entrypoint htpasswd httpd:2 -Bbn testuser testpassword > /opt/docker/registry/auth/htpasswd
这里注意testuser testpassword 就是我们后面登录的账号密码了
停止之前镜像(直接把所有关了)
docker stop $(docker ps -q) & docker rm $(docker ps -aq)
再次运行我们的服务镜像
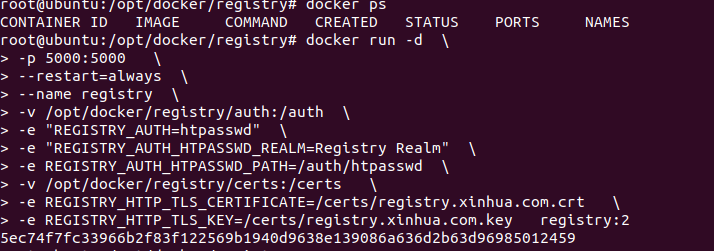
docker run -d \
-p 5000:5000 \
--restart=always \
--name registry \
-v /opt/docker/registry/auth:/auth \
-e "REGISTRY_AUTH=htpasswd" \
-e "REGISTRY_AUTH_HTPASSWD_REALM=Registry Realm" \
-e REGISTRY_AUTH_HTPASSWD_PATH=/auth/htpasswd \
-v /opt/docker/registry/certs:/certs \
-e REGISTRY_HTTP_TLS_CERTIFICATE=/certs/registry.xinhua.com.crt \
-e REGISTRY_HTTP_TLS_KEY=/certs/registry.xinhua.com.key registry:2
去我们客户端进行镜像上传
docker push registry.xinhua.com:5000/busybox:V1
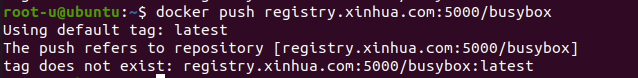
可以看到我们上传不了,接着我们登录
登录
docker login registry.xinhua.com:5000
账号:testuser
密码:testpassword
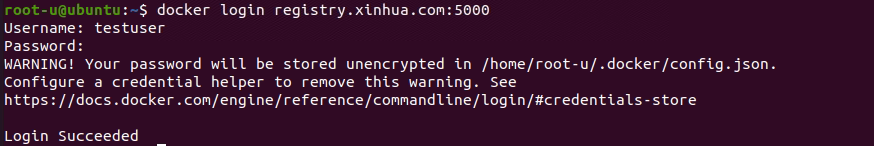
我们再去上传我们的镜像
docker push registry.xinhua.com:5000/busybox:V1
三、对外隐藏仓库服务器
3.1 在服务器端
安装nginx
apt install nginx
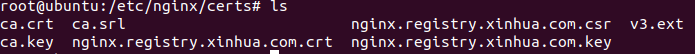
为nginx创建SSL秘钥和证书到/etc/nginx/certs/目录下
mkdir -p /etc/nginx/certs/
cd /etc/nginx/certs/
ls
开始参考https的方式啦,也就是相当于把registry.xinhua.com全都替换成nginx.xinhua.com
生成ca证书私钥
openssl genrsa -out ca.key 4096
生成ca证书
openssl req -x509 -new -nodes -sha512 -days 3650 \
-subj "/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=nginx.xinhua.com" \
-key ca.key \
-out ca.crt
生成服务器证书,私钥
openssl genrsa -out nginx.xinhua.com.key 4096
生成证书签名请求 (CSR)
openssl req -sha512 -new \
-subj "/C=CN/ST=Beijing/L=Beijing/O=example/OU=Personal/CN=nginx.xinhua.com" \
-key nginx.xinhua.com.key \
-out nginx.xinhua.com.csr
生成 x509 v3 扩展文件
cat > v3.ext <<-EOF
authorityKeyIdentifier=keyid,issuer
basicConstraints=CA:FALSE
keyUsage = digitalSignature, nonRepudiation, keyEncipherment, dataEncipherment
extendedKeyUsage = serverAuth
subjectAltName = @alt_names
[alt_names]
DNS.1=nginx.xinhua.com
DNS.2=nginx.xinhua
DNS.3=hostname
EOF
使用该文件为 主机生成证书v3.ext
openssl x509 -req -sha512 -days 3650 \
-extfile v3.ext \
-CA ca.crt -CAkey ca.key -CAcreateserial \
-in nginx.xinhua.com.csr \
-out nginx.xinhua.com.crt
在客户端上创建存储证书的目录
mkdir -p /etc/docker/certs.d/nginx.xinhua.com\:443
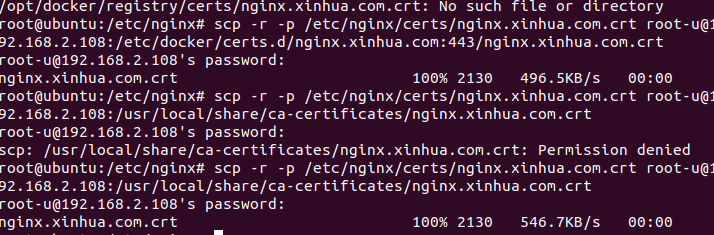
将服务器上的所有证书/opt/docker/registry/certs(.cert .key .crt)通过scp拷贝到创建客户端存储证书的目录服务端执行
修改服务端权限:
chmod 777 /etc/nginx/certs/
修改客户机权限:
chmod 777 /etc/docker/certs.d/nginx.xinhua.com:443
chmod 777 /usr/local/share/ca-certificates
username<登录用户名你服务器的名字【就是你直接打开控制台的名字】>
serverip<客户端ip(ip addr查看)> 192.168.2.108
scp -r -p /etc/nginx/certs/nginx.xinhua.com.crt root-u@192.168.2.108:/etc/docker/certs.d/nginx.xinhua.com:443/nginx.xinhua.com.crt
scp -r -p /etc/nginx/certs/nginx.xinhua.com.crt root-u@192.168.2.108:/usr/local/share/ca-certificates/nginx.xinhua.com.crt
修改nginx配置/etc/nginx/nginx.conf让nginx的支持SSL的反向代理和身份验证
user www-data;
worker_processes auto;
pid /run/nginx.pid;
include /etc/nginx/modules-enabled/*.conf;
events {
worker_connections 768;
# multi_accept on;
}
http {
upstream docker-register {
server registry.xinhua.com:5000;
}
server {
listen 443 ssl;
server_name nginx.xinhua.com;
#修改
ssl_certificate /etc/nginx/certs/nginx.xinhua.com.crt;
#修改
ssl_certificate_key /etc/nginx/certs/nginx.xinhua.com.key;
ssl_session_cache builtin:1000 shared:SSL:10m;
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
ssl_ciphers HIGH:!aNULL:!eNULL:!EXPORT:!CAMELLIA:!DES:!MD5:!PSK:!RC4;
ssl_prefer_server_ciphers on;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
add_header 'Docker-Distribution-Api-Version' 'registry/2.0' always;
location / {
auth_basic "Restricted";
auth_basic_user_file /etc/nginx/auth/htpasswd.txt;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
proxy_pass https://docker-register;
proxy_read_timeout 900;
}
location /v2 {
auth_basic off;
proxy_pass https://docker-register;
}
location /_ping {
auth_basic off;
proxy_pass https://docker-register;
}
location /v2/_ping {
auth_basic off;
proxy_pass https://docker-register;
}
location /v2/_catalog {
auth_basic off;
proxy_pass https://docker-register;
}
}
##
# Basic Settings
##
sendfile on;
tcp_nopush on;
types_hash_max_size 2048;
# server_tokens off;
# server_names_hash_bucket_size 64;
# server_name_in_redirect off;
include /etc/nginx/mime.types;
default_type application/octet-stream;
##
# SSL Settings
##
ssl_protocols TLSv1 TLSv1.1 TLSv1.2 TLSv1.3; # Dropping SSLv3, ref: POODLE
ssl_prefer_server_ciphers on;
##
# Logging Settings
##
access_log /var/log/nginx/access.log;
error_log /var/log/nginx/error.log;
##
# Gzip Settings
##
gzip on;
# gzip_vary on;
# gzip_proxied any;
# gzip_comp_level 6;
# gzip_buffers 16 8k;
# gzip_http_version 1.1;
# gzip_types text/plain text/css application/json application/javascript text/xml application/xml application/xml+rss text/javascript;
##
# Virtual Host Configs
##
include /etc/nginx/conf.d/*.conf;
include /etc/nginx/sites-enabled/*;
}
#mail {
# # See sample authentication script at:
# # http://wiki.nginx.org/ImapAuthenticateWithApachePhpScript
#
# # auth_http localhost/auth.php;
# # pop3_capabilities "TOP" "USER";
# # imap_capabilities "IMAP4rev1" "UIDPLUS";
#
# server {
# listen localhost:110;
# protocol pop3;
# proxy on;
# }
#
# server {
# listen localhost:143;
# protocol imap;
# proxy on;
# }
#}
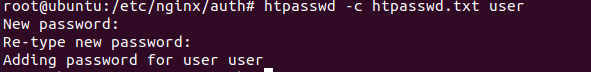
使用htpasswd去生成用户账号,设置密码
mkdir /etc/nginx/auth
cd /etc/nginx/auth
apt install apache2-utils
htpasswd -c htpasswd.txt user
输入你的密码
重启Nginx服务
sudo /etc/init.d/nginx restart
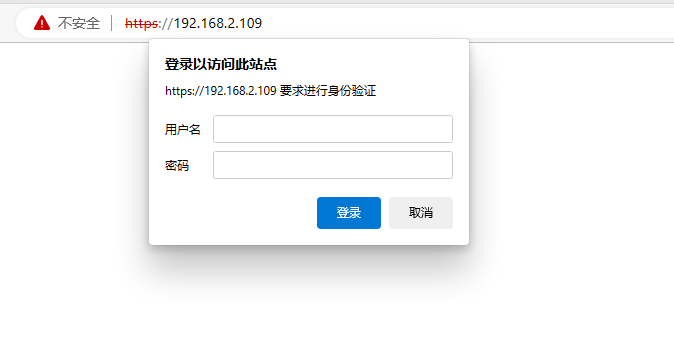
注意!!!
一定要打全
https://192.168.2.109:443
直接输入域名可能出现以下错误
没有打端口号
没有用http连接
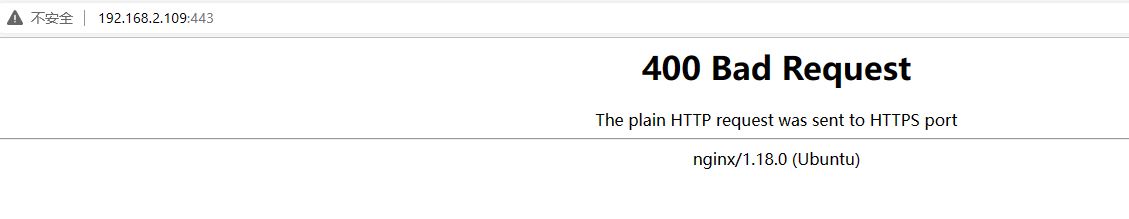
正确!!!
3.2 在客户端进行
配置
sudo vi /etc/docker/daemon.json
{
"registry-mirrors": ["https://8f6a79wk.mirror.aliyuncs.com"],
"insecure-registries":["私库地址(可以域名也可以ip)"]
}
我的配置
{
"registry-mirrors": ["https://8f6a79wk.mirror.aliyuncs.com"],
"insecure-registries":["https://nginx.xinhua.com"]
}
如果不配置就会出现
Error response from daemon: Get "https://nginx.xinhua.com/v2/": x509: certificate signed by unknown authority
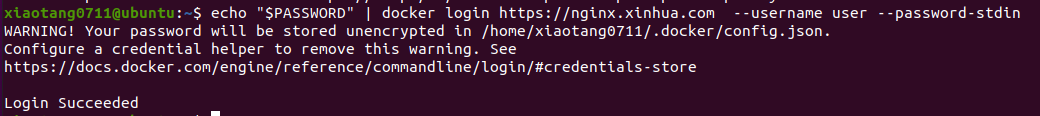
登录
update-ca-certificates
systemctl daemon-reload
systemctl restart docker
第一种:
docker login https://192.168.2.109:443 -u user -p "123456"
第二种:
#设置环境变量
export PASSWORD=123456
#以环境变量的方式读入
echo "$PASSWORD" | docker login https://https://nginx.xinhua.com --username user --password-stdin
我们再去上传我们的镜像
docker tag busybox:latest 192.168.2.109:443/busybox:V1
docker push 192.168.2.109:443/busybox:V1
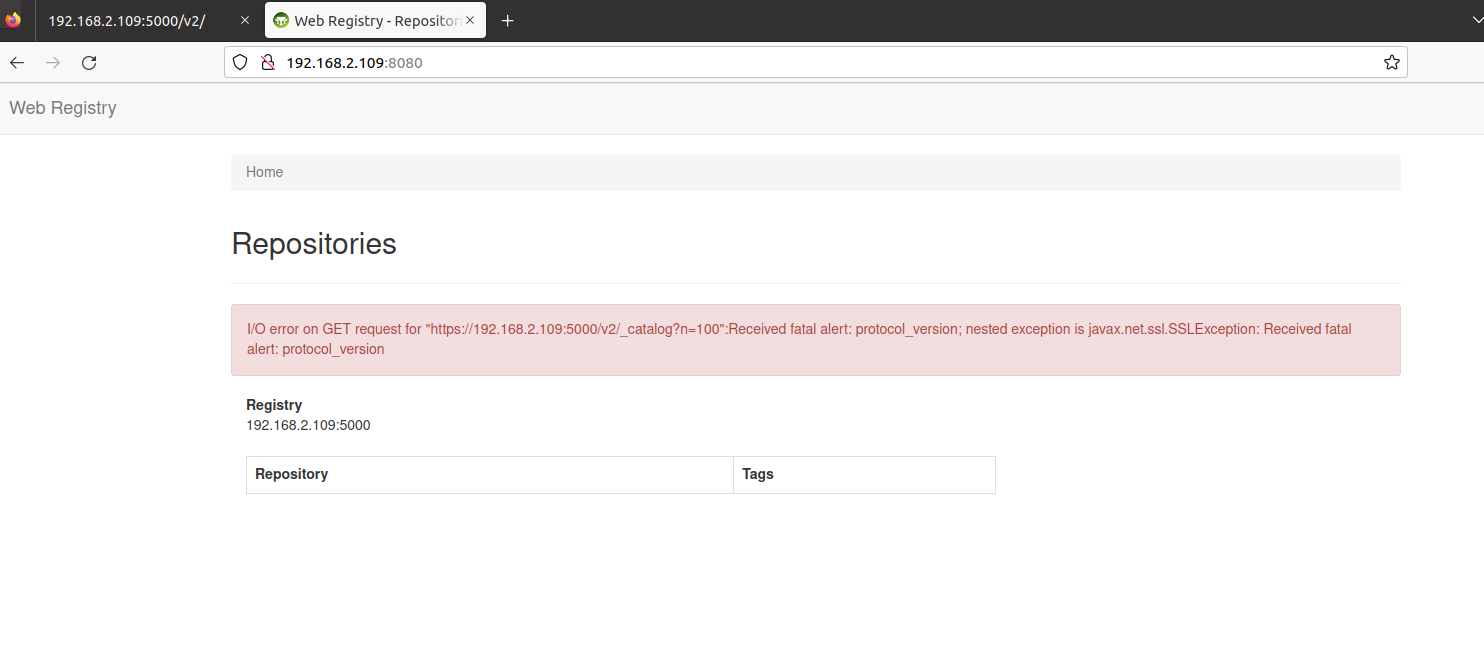
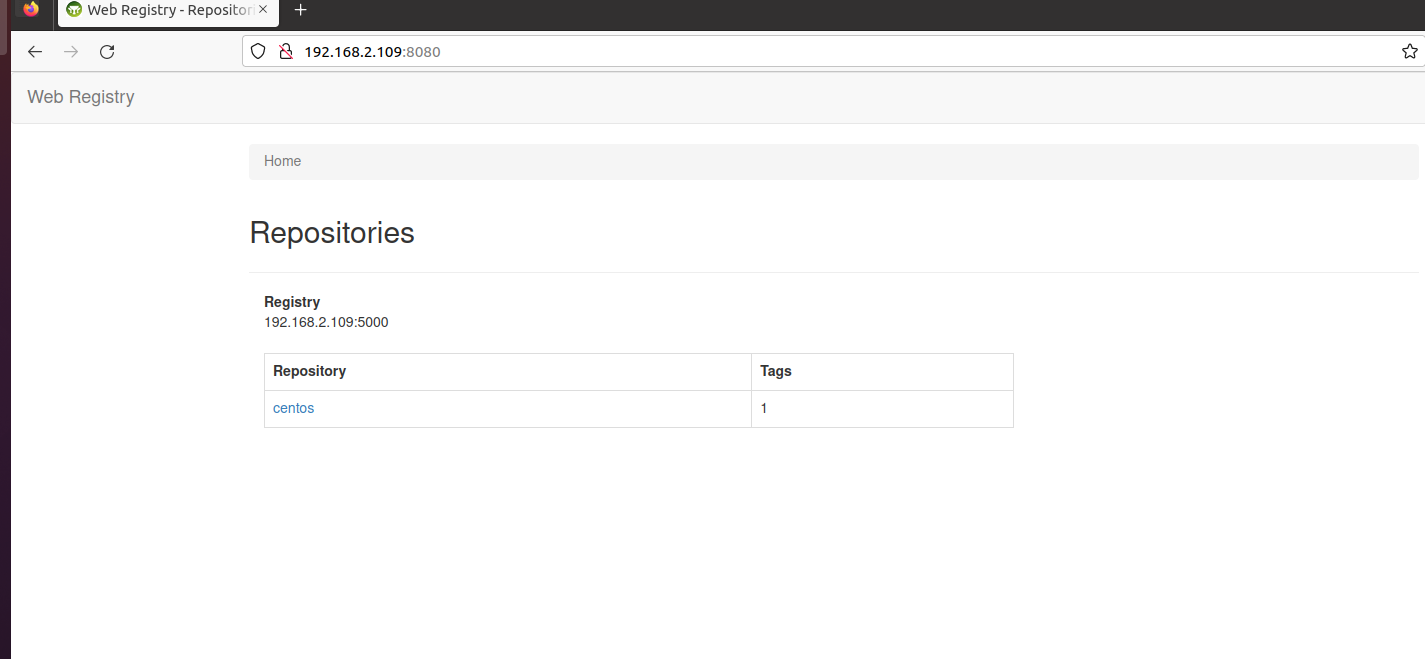
四、仓库可视化
http:
docker run --name registry -d -p 5000:5000 --restart=always -v /opt/data/registry:/var/lib/registry registry
docker run -it -d -p 8080:8080 --name registry-web --link registry \
-e REGISTRY_URL=http://192.168.2.109:5000/v2 \
-e REGISTRY_TRUST_ANY_SSL=true \
-e REGISTRY_BASIC_AUTH="cm9vdDoxMjM0NTY" \
-e REGISTRY_NAME=192.168.2.109:5000 hyper/docker-registry-web
https:(未实现)
docker run -it -d --name registry-TLS -p 5000:5000 -v /opt/docker/registry/certs/:/certs -e REGISTRY_HTTP_TLS_CERTIFICATE=/certs/registry.xinhua.com.crt -e REGISTRY_HTTP_TLS_KEY=/certs/registry.xinhua.com.key registry:2
docker run -it -d -p 8080:8080 --name registry-web --link registry-TLS \
-e REGISTRY_URL=https://192.168.2.109:5000/v2 \
-e REGISTRY_TRUST_ANY_SSL=true \
-e REGISTRY_BASIC_AUTH="cm9vdDoxMjM0NTY" \
-e REGISTRY_NAME=192.168.2.109:5000 hyper/docker-registry-web