可信计算组织(Ttrusted Computing Group,TCG)是一个非盈利的工业标准组织,它的宗旨是加强在相异计算机平台上的计算环境的安全性。TCG于2003年春成立,并采纳了由可信计算平台联盟(the Trusted Computing Platform Alliance,TCPA)所开发的规范。现在的规范都不是最终稿,都还在不断的更新中,比如:TPM的规范就从原来的v1.0更新到v1.2,现在还在不断的修订。

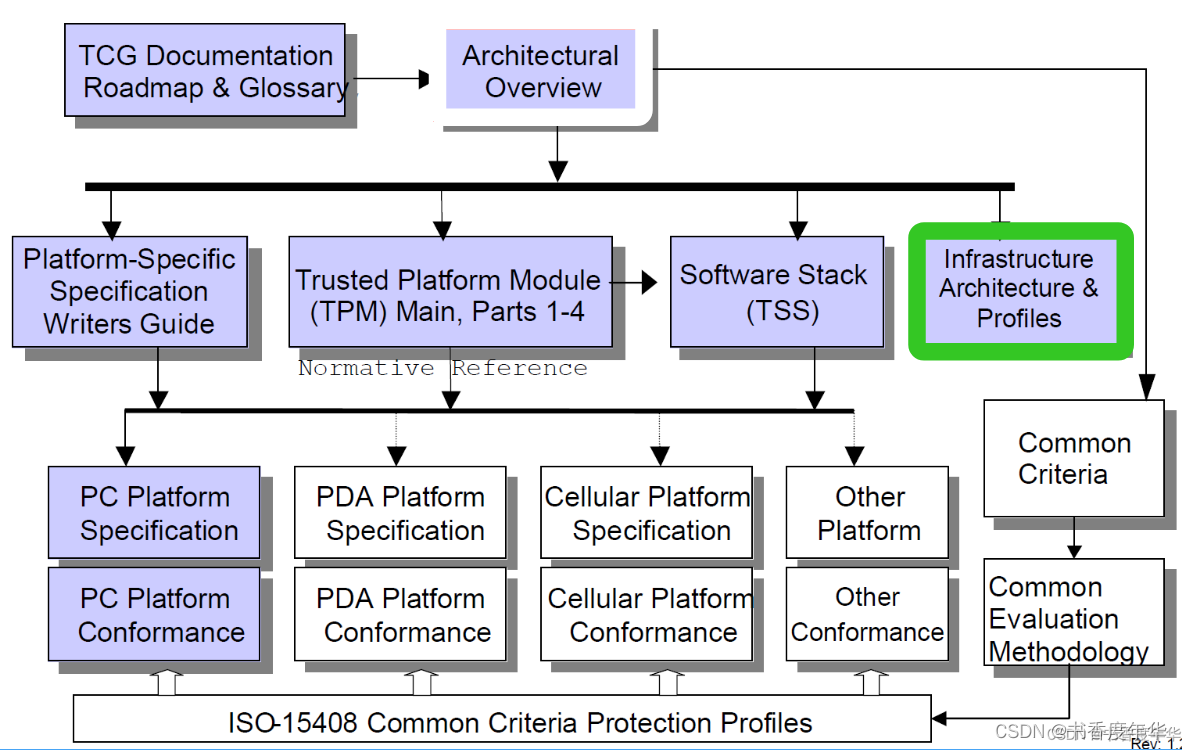
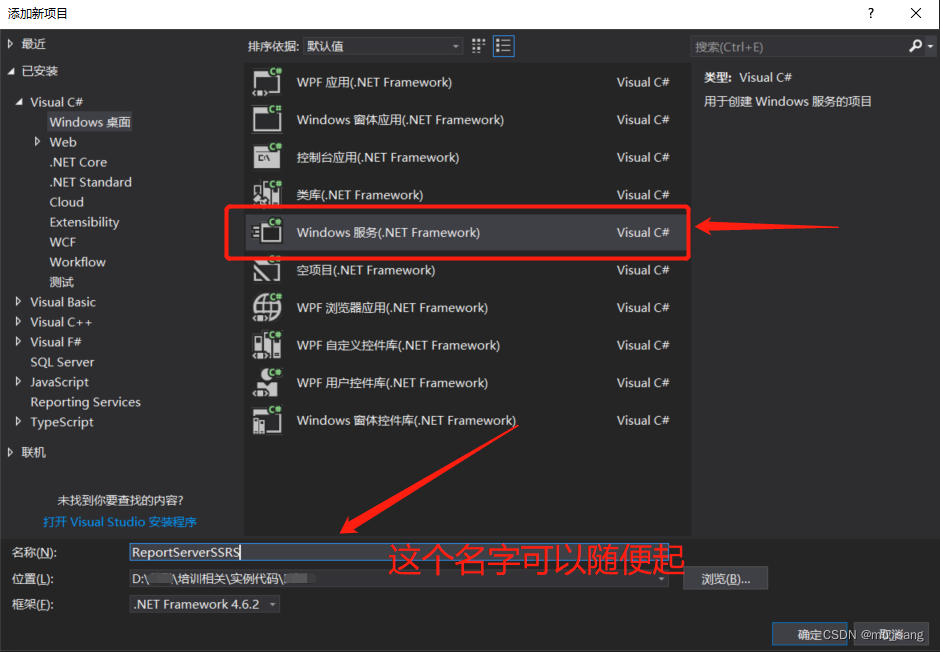
该规范在文档路线图中的位置
TCG 定义了 5 种类型的凭证,每种类型用来提供执行特定操作所必须的信息。
凭证采用 ASN.1 表示,这个借用了公钥基础设施中的元素。
凭证类型包括:
背书或 EK 凭证
符合性凭证
平台凭证
验证凭证
身份或 AIK 凭证
1. 背书凭证
背书凭证由生成背书密钥 EK 方颁发,EK 是在制作过程中生成的,即 TPM 制造商会生成 EK。不过,EK 可以在发给终端用户前的任意点生成,只要 TPM 制造商声明 EK 已经正常创建并嵌入到可用的 TPM 中。
EK密钥对在客户拿到平台后生成的话,密钥生成的条件可能会影响背书的提供。
背书凭证包含的信息有:
TPM 制造商名称
TPM 零件号
TPM 版本或阶段
EK 公钥
虽然 EK 公钥是公开的,但因为其和 TPM 一一绑定并会对平台进行扩展,所以属于敏感隐私。TCG 预期每个 TPM 需要有一个 EK 凭证。
2. 符合性凭证
这些证书由具有足够可信度的任何人发布,以评估TPM或包含TPM的平台。这些评估可以由平台制造商、供应商或独立实体来进行。这个符合性凭证表明评估方根据评估指南同意可信构建元素TBB 的设计和实现。通过签发凭证,评估者可以证明评估结果,这些会被用于后期的检查。TCG 通过定义有意义的评估标准和准则来促进评估。
评估方可以像一个平台签发多个符合性凭证,一个是给 TPM 的,其他是签给各个可信构成元素 TBB 组件的。
符合性凭证可能包含以下信息:
评估方名称
平台制造商名称
平台型号
平台版本(如果有的话)
TPM 制造商名称
TPM 型号
TPM 版本号或阶段
符合性凭证不包含任何唯一识别任何平台特定的信息。
TCG设想每个平台模型可能存在多个一致性证书,但同一品牌和型号的多个平台只需要一组证书。
3. 平台凭证
平台凭证由平台制造商、供应商或者任何具有足够信用的相关方颁发,平台凭证能够唯一识别平台的制造商并描述平台属性。平台凭证会引用 TPM 背书凭证以及相关的符合性凭证。这些引用由引用凭证的消息签名构成。平台凭证可以被看做是隐私敏感信息,这个凭证和特定平台相关,而不是和一类平台相关。
平台凭证包含如下信息:
平台制造商名称
平台型号
平台版本(如果适用)
背书凭证
符合性凭证
平台凭证根据背书凭证证明平台包含一个 TPM。TCG 建议每个平台实例只有一个平台凭证。
4. 验证(资格)凭证
TCG 建议可测量组件(软硬件)能够在功能测试后能够生成其度量值,形成对应的凭证。当然,这只是对那些能够对安全造成威胁的组件。这些度量值需要在安全环境下生成,并形成签名文档,即验证凭证,在运行时进行度量值比较。
以下一些组件通常需要验证证书:
视频适配器
磁盘存储适配器
通信控制器/网络适配器
处理器
键盘和鼠标
软件
验证凭证由验证实体颁发,任何愿意并有能力度量、证明这些度量值的实体都可以视作验证实体。通常,组件制作商产生这些值的最佳选择。组件描述中的任何一部分可能成为信任决策的原料。然而,验证凭证的候选组件可能会造成安全威胁。
组件描述至少包含如下元素:
验证实体名称
组件制造商名称
组件型号
组件版本或阶段
度量值
组件能力(比如不可改,这个是可选的)
一个型号中的一组组件可以颁布一份凭证,也可以颁发多个凭证。
组件更新、升级流程由供应商自定义,比如如何使原来的验证凭证无效等。
5. 身份证明凭证
证明身份凭证(身份证)是用来证明 AIK 私钥的凭证,由 AIK 公钥和其他签发者认为有用的信息组成,证明凭证是由可信服务方颁发并能验证各种凭证同时保证客户端的隐私条款。
通过签发证明身份凭证,签发者能够证明 TPM 的真实性,证明 TPM 的一些事实。证明的目的是 TPM 拥有 AIK 并且这个 AIK 绑定了有效的背书凭证、符合性凭证、平台凭证。受信方进一步保证了其遵守的隐私保护满足用户期望,这些隐私包括在注册过程中暴漏的个人隐私数据。
证明身份凭证参考其他凭证如下:
证明身份凭证包含了一个TPM 制造商和型号的引用,如下图中 C,没有引用隐私敏感的 EK
证明身份凭证同时包含了平台制造商和型号如图 D,值得注意的是这个引用并不是引用平台凭证本身,而是引用平台凭证中信息不敏感的信息
最后,证明身份凭证包含一个指向 TPM 和平台符合性的条目,如图 E
挑战者可以使用该信息以及证书中的其他信息,通过认证协议信任平台。
附录
The TCG TPM 1.2 Main specification defines a subsystem with protected storage and protected capabilities. This subsystem is the Trusted Platform Module (TPM). Since the TPM is both a subsystem intended to provide trust and to be an inexpensive component, resources within it are restricted.
This narrowing of the resources, while making the security properties easier and cheaper to build and verify, causes the interfaces and capabilities to be cumbersome. The TCG architecture has solved this by separating the functions requiring the protected storage and capabilities from the functions that do not; putting those that do not into the platformÍs main processor and memory space where processing power and storage exceed that of the TPM. The modules and components that provide this supporting functionality comprise the TSS.
Latest Version:
TCG Software Stack (TSS) Specification, Version 1.2, Errata A
- Header File: TCG Software Stack (TSS) Specification, Version 1.2 (ZIP)
Previous Version:
TCG Software Stack (TSS) Specification Version 1.2
- Header File: TCG Software Stack (TSS) Specification, Version 1.2, Errata A
TCG Software Stack (TSS) Specification Version 1.10
- Header File: TCG Software Stack (TSS) Specification, Version 1.1
TCG Software Stack Specification 1.2 FAQs
What are we announcing?
TCG is announcing the Trusted Computing Group Software Stack Specification (TSS) 1.2. Applications based on this will be able to access the many features of the Trusted Platform Module (TPM) 1.2. These features include Direct Anonymous Attestation (DAA) and the ability to run and generate a new Attestation Identity Key (AIK); locality; delegation; non-volatile storage; optimized transport protection; and time stamping.
How is this version different from the existing one?
We have added support for all the new functionality that was added into the TPM 1.2 from 1.1, while maintaining backwards compatibility for TPMs based on the 1.1 specification.
Will applications developed based on this be compatible with applications based on a previous version of the TSS?
1.1 applications will continue to run with the exception of those using the GetCapabilitySigned function, which was eliminated in TPM 1.2.
Will TSS 1.2 support only TPM 1.2? Will it support TPM 1.1?
Applications based on the TSS 1.2 using the specific features of the TPM 1.2 will only work on platforms with the TPM 1.2. Applications compiled with the TSS 1.2 but using functions of the TPM 1.1 will work on either TSS 1.1 or TSS 1.2 software stacks. Applications that were compiled with the TSS 1.1 will continue to work on either TSS 1.1 or TSS 1.2.
What is required of developers to start using the spec?
Developers need the header file, which TCG will make available in March of this year, and a 1.2 TSS DLL, which should be shipping soon from many members.
What applications are anticipated to be developed?
New applications that can be developed using TSS 1.2 include those supporting features of the TPM 1.2, such as delegation functions, DAA (using group signature like structure for anonymity), time stamping, or non-volatile storage on the TPM should use this new spec.
What are some new features in the TSS 1.2?
One of these is extensions to DAA, or Direct Anonymous Attestation.
What extension to DAA have been incorporated into TSS that are not available with the TPM itself?
The original mechanism of DAA was to allow for privacy-friendly (anonymous) attestation. That is, it allows a TPM to prove that it is a certified TPM without being identified or transactions being linkable. For TSS, DAA has been extended to include arbitrary attributes in the certificates issued to the TPM. This extension allows for a fine-grained privacy-friendly attestation as well as to prove properties about the included attributes (e.g., that the date included in the certificate is still valid). Finally, in order to comply with regulations in some countries, anonymity revocation is supported: at the time a TPM proves that it is certified, a third (passive) party can be designed who will later on be able to identify the TPM in case of misuse.
What applications can be developed using DAA?
Any applications that wants to support privacy-friendly authentication. An example would be an anonymous yet restricted web access to a newspaper or patent database.
When will we see these new applications?
Some members have started shipping applications based on preliminary specifications. NTRU and Infineon support the TSS 1.2 with its products. It is expected that all new applications will take advantage of the additional functionality provided in the specification, especially as many of these have been added based on demands from the market.
Are there any tools or other requirements to start using the new TSS? If so, who is providing and when are the necessary tools available?
TCG is making available a header file for developers, which will be available in March 2006 via the TCG website, https://trustedcomputinggroup.org/developers/software_stack.
皮格马利翁效应心理学指出,赞美、赞同能够产生奇迹,越具体,效果越好~
“收藏夹吃灰”是学“器”练“术”非常聪明的方法,帮助我们避免日常低效的勤奋~
下一篇 「TCG 规范解读」TCG 软件栈 TSS (中)