文章目录
- TH_Curve
- baby_Curve
- RSA_loss
- TheoremPlus
TH_Curve
题目描述:
from Crypto.Util.number import *
from secret import flag
def add_THcurve(P, Q):
if P == (0, 0):
return Q
if Q == (0, 0):
return P
x1, y1 = P
x2, y2 = Q
x3 = (x1 - y1 ** 2 * x2 * y2) * pow(a * x1 * y1 * x2 ** 2 - y2, -1, p) % p
y3 = (y1 * y2 ** 2 - a * x1 ** 2 * x2) * pow(a * x1 * y1 * x2 ** 2 - y2, -1, p) % p
return x3, y3
def mul_THcurve(n, P):
R = (0, 0)
while n > 0:
if n % 2 == 1:
R = add_THcurve(R, P)
P = add_THcurve(P, P)
n = n // 2
return R
p = 10297529403524403127640670200603184608844065065952536889
a = 2
G = (8879931045098533901543131944615620692971716807984752065, 4106024239449946134453673742202491320614591684229547464)
FLAG = flag.lstrip(b'DASCTF{').rstrip(b'}')
assert len(FLAG) == 15
m = bytes_to_long(FLAG)
assert m < p
Q = mul_THcurve(m, G)
print("Q =", Q)
# Q = (6784278627340957151283066249316785477882888190582875173, 6078603759966354224428976716568980670702790051879661797)
题目分析:
映射关系如下:
https://hyperelliptic.org/EFD/g1p/data/twistedhessian/coordinates
故该曲线为:
a
x
3
+
y
3
+
1
=
d
x
y
2
x
3
+
y
3
+
1
=
d
x
y
a x^3+y^3+1=d x y\\ 2 x^3+y^3+1=d x y
ax3+y3+1=dxy2x3+y3+1=dxy
通过点Q求出d来从而得到完整的曲线方程
d = (a * Q[0] ** 3 + Q[1] ** 3 + 1) * inverse(Q[0] * Q[1], p) % p
接下来解题思路参考:https://tangcuxiaojikuai.xyz/post/a6ee3e0e.html
通过以下方式换元: x = x ′ z ′ , y = y ′ z ′ x = \frac{x'}{z'},y = \frac{y'}{z'} x=z′x′,y=z′y′
从而转换成以下三次齐次方程形式: 2 x ′ 3 + y ′ 3 + z ′ 3 ≡ d x ′ y ′ z ′ ( m o d p ) 2x'^3 + y'^3 + z'^3 \equiv dx'y'z' \pmod p 2x′3+y′3+z′3≡dx′y′z′(modp)
构建出椭圆曲线后使用 Pohlig Hellman 即可解出 Q = mG 中的 m
exp:
from Crypto.Util.number import *
p = 10297529403524403127640670200603184608844065065952536889
a = 2
P = (8879931045098533901543131944615620692971716807984752065, 4106024239449946134453673742202491320614591684229547464)
Q = (6784278627340957151283066249316785477882888190582875173, 6078603759966354224428976716568980670702790051879661797)
d = (a * Q[0] ** 3 + Q[1] ** 3 + 1) * inverse(Q[0] * Q[1], p) % p
# construct ECC to get a solution of 2X^3+Y^3+Z^3=dXYZ
R.<x,y,z> = Zmod(p)[]
cubic = 2 * x^3 + y^3 + z^3 - d*x*y*z
E = EllipticCurve_from_cubic(cubic,morphism=True)
P = E(P)
Q = E(Q)
P_ord = P.order()
def Pohlig_Hellman(n,P,Q):
factors, exponents = zip(*factor(n))
primes = [factors[i] ^ exponents[i] for i in range(len(factors))][:-1]
print(primes)
dlogs = []
for fac in primes:
t = int(int(P.order()) // int(fac))
dlog = discrete_log(t*Q,t*P,operation="+")
dlogs += [dlog]
print("factor: "+str(fac)+", Discrete Log: "+str(dlog)) #calculates discrete logarithm for each prime order
num2 = crt(dlogs,primes)
return num2
num2 = Pohlig_Hellman(P_ord,P,Q)
print(long_to_bytes(num2))
baby_Curve
题目描述:
#!/usr/bin/env python
# -*- coding: UTF-8 -*-
import os
import hashlib
from sage.all import *
from Crypto.Cipher import AES
from Crypto.Util.Padding import pad
from secret import c, b, key, FLAG
def add_curve(P, Q, K):
a, d, p = K
if P == (0, 0):
return Q
if Q == (0, 0):
return P
x1, y1 = P
x2, y2 = Q
x3 = (x1 * y2 + y1 * x2) * pow(1 - d * x1 ** 2 * x2 ** 2, -1, p) % p
y3 = ((y1 * y2 + 2 * a * x1 * x2) * (1 + d * x1 ** 2 * x2 ** 2) + 2 * d * x1 * x2 * (x1 ** 2 + x2 ** 2)) * pow(
(1 - d * x1 ** 2 * x2 ** 2) ** 2, -1, p) % p
return x3, y3
def mul_curve(n, P, K):
R = (0, 0)
while n > 0:
if n % 2 == 1:
R = add_curve(R, P, K)
P = add_curve(P, P, K)
n = n // 2
return R
def AES_encrypt(k):
key = hashlib.sha256(str(k).encode()).digest()[:16]
iv = os.urandom(16)
cipher = AES.new(key, AES.MODE_CBC, iv)
cipher = cipher.encrypt(pad(FLAG, 16))
data = {}
data["iv"] = iv.hex()
data["cipher"] = cipher.hex()
return data
a = 46
d = 20
p1 = 826100030683243954408990060837
K1 = (a, d, p1)
G1 = (560766116033078013304693968735, 756416322956623525864568772142)
P1 = mul_curve(c, G1, K1)
Q1 = mul_curve(b, G1, K1)
print("P1 =", P1)
print("Q1 =", Q1)
# P1 = (528578510004630596855654721810, 639541632629313772609548040620)
# Q1 = (819520958411405887240280598475, 76906957256966244725924513645)
p = 770311352827455849356512448287
E = EllipticCurve(GF(p), [-c, b])
G = E.gens()[0]
P = G * key
data = AES_encrypt(key)
print("G =", G)
print("P =", P)
print("data =",data)
# G = (584273268656071313022845392380 : 105970580903682721429154563816 : 1)
# P = (401055814681171318348566474726 : 293186309252428491012795616690 : 1)
# data = {'iv': 'bae1b42f174443d009c8d3a1576f07d6', 'cipher': 'ff34da7a65854ed75342fd4ad178bf577bd622df9850a24fd63e1da557b4b8a4'}
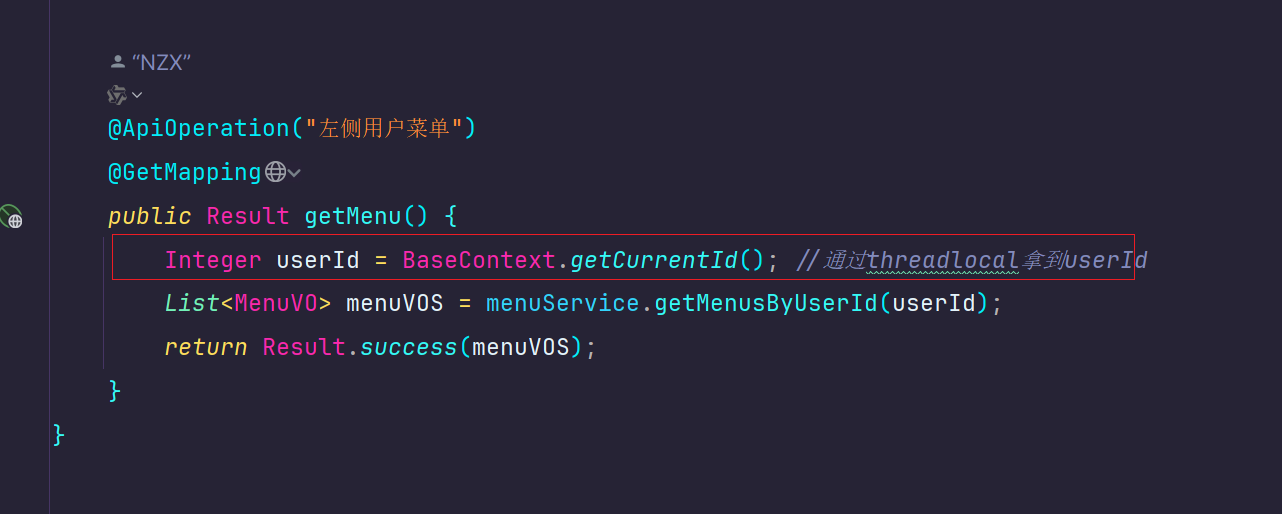
题目分析:
解方程得c,b(或者爆破),然后。。。sagemath10.4解、、
from Crypto.Util.number import *
import hashlib
p = 770311352827455849356512448287
x1, y1 = (584273268656071313022845392380, 105970580903682721429154563816)
x2, y2 = (401055814681171318348566474726, 293186309252428491012795616690)
c = ((y1 ** 2 - x1 ** 3) - (y2 ** 2 - x2 ** 3)) * inverse(x1 - x2, p) % p
b = (y1 ** 2 - x1 ** 3 - c * x1) % p
E = EllipticCurve(GF(p), [c, b])
G = E(x1 ,y1)
P = E(x2 ,y2)
k = P.log(G) # 2951856998192356
iv = 0xbae1b42f174443d009c8d3a1576f07d6
cipher = 0xff34da7a65854ed75342fd4ad178bf577bd622df9850a24fd63e1da557b4b8a4
key = hashlib.sha256(str(k).encode()).digest()[:16]
aes = AES.new(key, AES.MODE_CBC, long_to_bytes(iv))
m = aes.decrypt(long_to_bytes(cipher))
print(m)
或者网页版https://sagecell.sagemath.org/
p = 770311352827455849356512448287
E = EllipticCurve(GF(p), [-35, 98])
G = E(584273268656071313022845392380, 105970580903682721429154563816)
P = E(401055814681171318348566474726, 293186309252428491012795616690)
k = G.discrete_log(P)
print(k) # 2951856998192356
RSA_loss
题目描述:
from Crypto.Util.number import *
from gmpy2 import *
p = getPrime(100)
q = getPrime(100)
n = p * q
e = 65537
message = b""
m = bytes_to_long(message)
c = pow(m, e, n)
print(f'c = {c}')
print(f'p = {p}')
print(f'q = {q}')
d = invert(e,(p-1)*(q-1))
newm = pow(c, d, n)
print(long_to_bytes(newm))
# c = 356435791209686635044593929546092486613929446770721636839137
# p = 898278915648707936019913202333
# q = 814090608763917394723955024893
# newm = b'X\xee\x1ey\x88\x01dX\xf6i\x91\x80h\xf4\x1f!\xa7"\x0c\x9a\x06\xc8\x06\x81\x15'
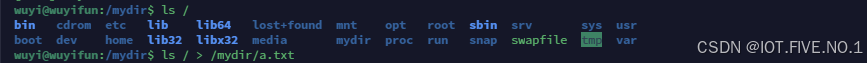
题目分析:
得 到 的 n e w m ! = m e s s a g e , 说 明 m e s s a g e 比 n 大 , 试 着 去 简 单 ( + k n ) 爆 破 一 下 没 有 爆 出 来 , 说 明 m e s s a g e 应 该 比 n 大 不 少 既 然 如 此 那 就 去 爆 破 m e s s a g e 里 面 的 每 一 位 得到的newm != message,说明message比n大,\\试着去简单(+kn)爆破一下没有爆出来,说明message应该比n大不少\\既然如此那就去爆破message里面的每一位 得到的newm!=message,说明message比n大,试着去简单(+kn)爆破一下没有爆出来,说明message应该比n大不少既然如此那就去爆破message里面的每一位
参考:https://tangcuxiaojikuai.xyz/post/94c7e291.html
猜测
m
e
s
s
a
g
e
∈
[
0
−
9
,
a
−
z
,
A
−
Z
,
_
]
message \in [0-9, a-z, A-Z, \_]
message∈[0−9,a−z,A−Z,_]
那么对应的ascii码就在48~128里面
假设message长度为le
那么:
n
e
w
m
=
c
=
25
6
(
l
e
−
7
)
∗
p
r
e
+
256
∗
m
0
+
s
u
f
newm = c = 256^{(le - 7)} * pre + 256 * m_0 + suf
newm=c=256(le−7)∗pre+256∗m0+suf
(其中pre = b’DASCTF{’,suf = b’}’,m0为中间未知的数字串)
得到: m 0 ≡ 25 6 − 1 ∗ ( c − 25 6 ( l e − 7 ) ∗ p r e − s u f ) ( m o d p ) m_0 \equiv 256^{-1} * (c - 256^{(le - 7)} * pre - suf) \pmod p m0≡256−1∗(c−256(le−7)∗pre−suf)(modp)
又: m 0 ≡ ∑ i = 0 l e n − 7 − 1 − 1 25 6 i ∗ s i ( m o d p ) m_0 \equiv \sum_{i = 0}^{len - 7 - 1 - 1} 256^i * s_i \pmod p m0≡∑i=0len−7−1−1256i∗si(modp)
得到: m 0 ≡ ∑ i = 0 l e n − 7 − 1 − 1 25 6 i ∗ s i + k ∗ p m_0 \equiv \sum_{i = 0}^{len - 7 - 1 - 1} 256^i * s_i + k * p m0≡∑i=0len−7−1−1256i∗si+k∗p
构造如下格(为了保证能规约出0,做题时可以给格的最后一列配上个大系数):
M
=
(
1
1
1
256
⋱
⋮
1
25
6
l
e
−
9
1
−
m
0
p
)
M = \begin{pmatrix} 1&&&&&1\\ &1&&&&256\\ &&\ddots&&&\vdots\\ &&&1&&256^{le - 9}\\ &&&&1&-m_0\\ &&&&&p \end{pmatrix}
M=⎝⎜⎜⎜⎜⎜⎜⎜⎛11⋱111256⋮256le−9−m0p⎠⎟⎟⎟⎟⎟⎟⎟⎞
有: ( s 0 , s 1 , . . . , s ( l e − 9 ) , 1 , k ) ∗ M = ( s 0 , s 1 , . . . , s ( l e − 9 ) , 1 , 0 ) (s_0,s_1,...,s_{(le - 9)}, 1, k) * M = (s_0,s_1,...,s_{(le-9)}, 1, 0) (s0,s1,...,s(le−9),1,k)∗M=(s0,s1,...,s(le−9),1,0)
此时: s i ∈ ( 48 , 128 ) s_i \in (48, 128) si∈(48,128)
有点大,优化一下: t i = s i − 48 t_i = s_i - 48 ti=si−48
得到: m 0 ≡ ∑ i = 0 l e n − 9 25 6 i ∗ ( t i + 48 ) ( m o d p ) m_0 \equiv \sum_{i = 0}^{len - 9} 256^i * (t_i + 48) \pmod p m0≡∑i=0len−9256i∗(ti+48)(modp)
得到: m 0 − 48 ∗ ∑ i = 0 l e n − 9 25 6 i = ∑ i = 0 l e n − 9 25 6 i ∗ t i = m 1 m_0 - 48 * \sum_{i = 0}^{len - 9} 256^i = \sum_{i = 0}^{len - 9} 256^i * t_i = m_1 m0−48∗∑i=0len−9256i=∑i=0len−9256i∗ti=m1
此时 t i ∈ ( 0 , 80 ) , 目 标 向 量 为 : ( t 0 , t 1 , . . . , t ( l e − 9 ) , 1 , 0 ) t_i \in (0, 80),目标向量为:(t_0,t_1,...,t_{(le-9)}, 1, 0) ti∈(0,80),目标向量为:(t0,t1,...,t(le−9),1,0)
测试之后发现只有在 l e < = 33 le <= 33 le<=33 才能出结果,带入题中数据没得到结果说明 l e n ( f l a g ) > 33 len(flag) > 33 len(flag)>33
既然如此,再优化下: t i = s i − 48 − 40 t_i = s_i - 48 - 40 ti=si−48−40
得到: m 0 ≡ ∑ i = 0 l e n − 9 25 6 i ∗ ( t i + 48 + 40 ) ( m o d p ) m_0 \equiv \sum_{i = 0}^{len - 9} 256^i * (t_i + 48 + 40) \pmod p m0≡∑i=0len−9256i∗(ti+48+40)(modp)
此时: t i ∈ ( − 40 , 40 ) , 目 标 向 量 为 : ( t 0 , t 1 , . . . , t ( l e − 9 ) , 1 , 0 ) t_i \in (-40, 40),目标向量为:(t_0,t_1,...,t_{(le-9)}, 1, 0) ti∈(−40,40),目标向量为:(t0,t1,...,t(le−9),1,0)
正好,能出
exp:
from Crypto.Util.number import *
p1 = 898278915648707936019913202333
q1 = 814090608763917394723955024893
newm = bytes_to_long(b'X\xee\x1ey\x88\x01dX\xf6i\x91\x80h\xf4\x1f!\xa7"\x0c\x9a\x06\xc8\x06\x81\x15')
p = p1 * q1
c = newm
prefix = b"DASCTF{"
suffix = b"}"
for le in range(33, 40):
length = le - len(prefix) - len(suffix)
#part1 remove prefix and suffix
c -= 256^(len(suffix) + length) * bytes_to_long(prefix)
c -= bytes_to_long(suffix)
c = c * inverse(256,p) % p
L = Matrix(ZZ,length+2,length+2)
for i in range(length):
L[i,i] = 1
L[i,-1] = 256^i
c -= 256^i*48
c -= 256^i*40
L[-2,-2] = 1
L[-2,-1] = -c
L[-1,-1] = p
L[:,-1:] *= p
res = L.BKZ()
for i in res[:-1]:
flag = ""
if(all(abs(j) <= 40 for j in i[:-2])):
if(i[-2] == 1):
for j in i[:-2][::-1]:
flag += chr(48 + 40 + j)
elif i[-2] == -1:
for j in i[:-2][::-1]:
flag += chr(48 + 40 - j)
if(flag != ""):
print(flag)
c = newm
# o0p5_m3ssaGe_to0_b1g_nv93nd0
TheoremPlus
题目描述:
from Crypto.Util.number import *
from gmpy2 import *
from secret import flag
def decode_e(e):
if e > 1:
mul = 1
for i in range(1, e):
mul *= i
if e - mul % e - 1 == 0:
mulmod = mul % e - e
else:
mulmod = mul % e
return mulmod + decode_e(e - 1)
else:
return 0
q = getPrime(1024)
p = next_prime(q)
n = p * q
phi = (p - 1) * (q - 1)
e = abs(decode_e(703440151))
c = pow(bytes_to_long(flag), e, n)
print('n = {}\n'
'c = {}'.format(n, c))
'''
n = 18770575776346636857117989716700159556553308603827318013591587255198383129370907809760732011993542700529211200756354110539398800399971400004000898098091275284235225898698802555566416862975758535452624647017057286675078425814784682675012671384340267087604803050995107534481069279281213277371234272710195280647747033302773076094600917583038429969629948198841325080329081838681126456119415461246986745162687569680825296434756908111148165787768172000131704615314046005916223370429567142992192702888820837032850104701948658736010527261246199512595520995042205818856177310544178940343722756848658912946025299687434514029951
c = 2587907790257921446754254335909686808394701314827194535473852919883847207482301560195700622542784316421967768148156146355099210400053281966782598551680260513547233270646414440776109941248869185612357797869860293880114609649325409637239631730174236109860697072051436591823617268725493768867776466173052640366393488873505207198770497373345116165334779381031712832136682178364090547875479645094274237460342318587832274304777193468833278816459344132231018703578274192000016560653148923056635076144189403004763127515475672112627790796376564776321840115465990308933303392198690356639928538984862967102082126458529748355566
'''
题目分析:
函数 decode_e(a) 中的逻辑:
如 果 ( a − 1 ) 的 阶 乘 m u l ≡ ( a − 1 ) ! ≡ − 1 ( m o d a ) , 那 么 m u l m o d = − 1 , 否 则 m u l m o d = m u l % a 如果(a - 1)的阶乘\ mul \equiv (a - 1)! \equiv -1 \pmod a, 那么\ mulmod = -1,否则\ mulmod = mul \%a 如果(a−1)的阶乘 mul≡(a−1)!≡−1(moda),那么 mulmod=−1,否则 mulmod=mul%a
威尔逊定理:对于素数 p 有 ( p − 1 ) ! ≡ − 1 ( m o d p ) \text{威尔逊定理:对于素数 }p\text{ 有 }(p-1)!\equiv-1\pmod{p} 威尔逊定理:对于素数 p 有 (p−1)!≡−1(modp)
所以(1, a)范围内的数字中,素数的mulmod = -1
那么接下来看看合数的mulmod,合数一定能由小于它的数组成,或者说合数一定能由小于它的素数组成,比如 6 = 2 * 3,8 = 2 * 4 = 2 * 2 * 2,…
故
如
果
e
为
合
数
,
那
么
一
定
有
(
e
−
1
)
!
=
k
∗
e
(
感
叹
号
为
阶
乘
符
号
)
,
所
以
此
时
的
m
u
l
m
o
d
=
m
u
l
%
e
=
k
∗
e
%
e
=
0
(
4
先
除
外
)
故 如果e为合数,那么一定有(e - 1) ! = k * e(感叹号为阶乘符号),所以此时的\ mulmod = mul \% e =k * e \%e = 0(4先除外)
故如果e为合数,那么一定有(e−1)!=k∗e(感叹号为阶乘符号),所以此时的 mulmod=mul%e=k∗e%e=0(4先除外)
可以去打印一下看看,也是符合的:

既然如此,那么我们只要知道在1~703440151中有多少个素数,我们就能求出e
exp:
from Crypto.Util.number import *
from sympy import primepi
from gmpy2 import *
n = 18770575776346636857117989716700159556553308603827318013591587255198383129370907809760732011993542700529211200756354110539398800399971400004000898098091275284235225898698802555566416862975758535452624647017057286675078425814784682675012671384340267087604803050995107534481069279281213277371234272710195280647747033302773076094600917583038429969629948198841325080329081838681126456119415461246986745162687569680825296434756908111148165787768172000131704615314046005916223370429567142992192702888820837032850104701948658736010527261246199512595520995042205818856177310544178940343722756848658912946025299687434514029951
c = 2587907790257921446754254335909686808394701314827194535473852919883847207482301560195700622542784316421967768148156146355099210400053281966782598551680260513547233270646414440776109941248869185612357797869860293880114609649325409637239631730174236109860697072051436591823617268725493768867776466173052640366393488873505207198770497373345116165334779381031712832136682178364090547875479645094274237460342318587832274304777193468833278816459344132231018703578274192000016560653148923056635076144189403004763127515475672112627790796376564776321840115465990308933303392198690356639928538984862967102082126458529748355566
e = primepi(703440151) - 2
p = next_prime(iroot(n,2)[0])
q = n // p
phi = (p - 1) * (q - 1)
d = invert(int(e), phi)
print(long_to_bytes(pow(c, d, n)))
浅记一下:
关键词: ECC,curve,G.discrete_log( P),Pohlig Hellman,解方程,格,优化,阶乘,primepi