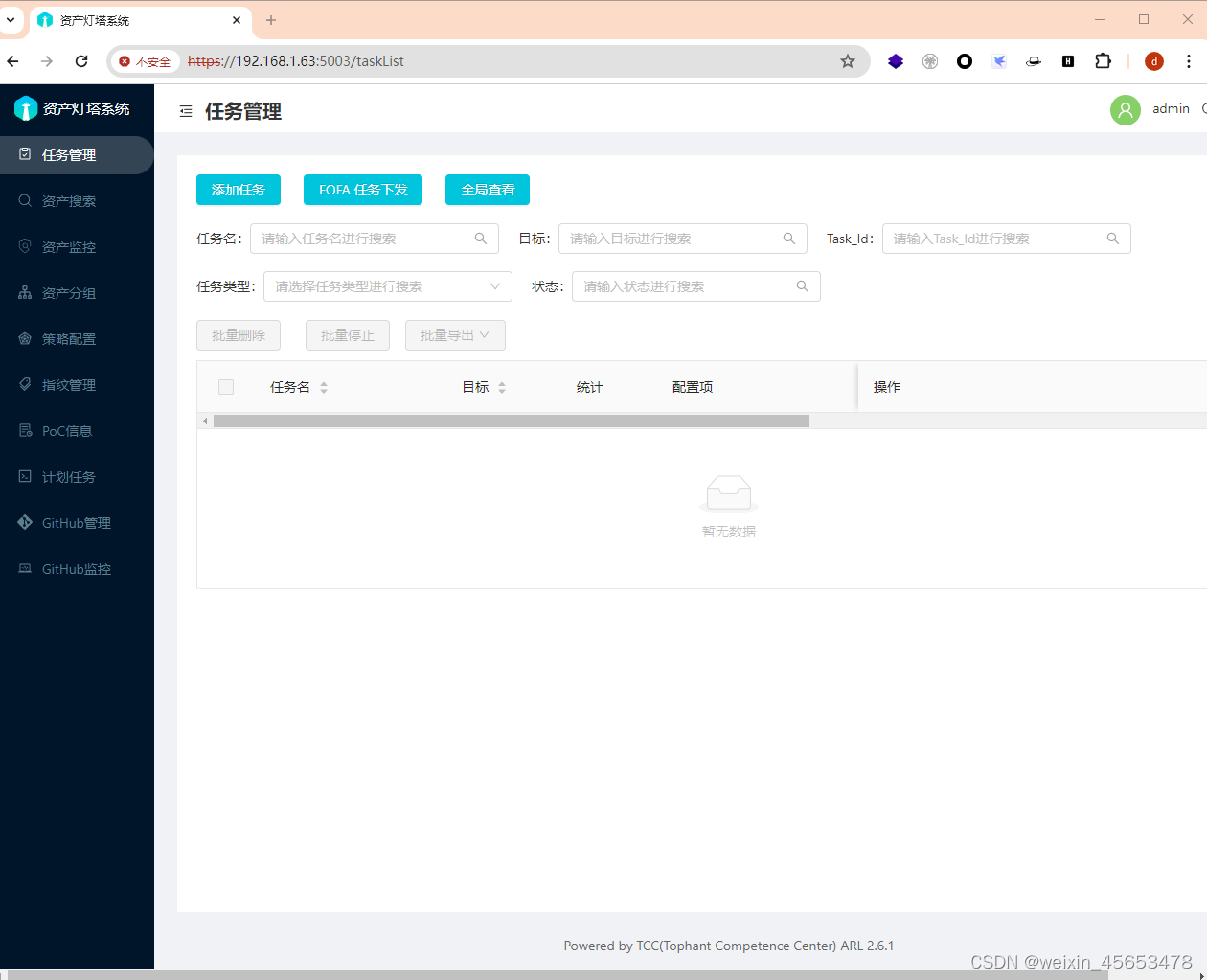
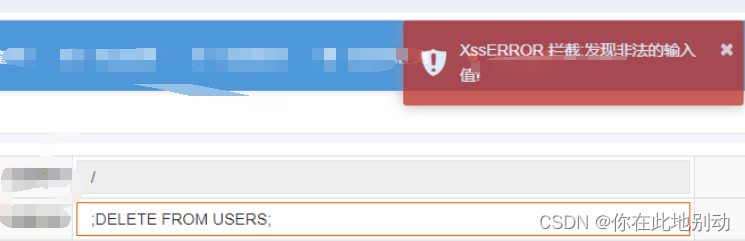
先看效果:
1.js注入拦截:

2.sql注入拦截
生效只需要两步:
1.创建Filter类,粘贴如下代码:
package cn.你的包命.filter;
import java.io.BufferedReader;
import java.io.ByteArrayInputStream;
import java.io.IOException;
import java.io.InputStreamReader;
import java.io.PrintWriter;
import java.util.*;
import java.util.regex.Pattern;
import javax.servlet.DispatcherType;
import javax.servlet.Filter;
import javax.servlet.FilterChain;
import javax.servlet.FilterConfig;
import javax.servlet.ServletException;
import javax.servlet.ServletInputStream;
import javax.servlet.ServletRequest;
import javax.servlet.ServletResponse;
import javax.servlet.annotation.WebFilter;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletRequestWrapper;
import javax.servlet.http.HttpServletResponse;
import com.alibaba.fastjson.JSON;
import org.slf4j.Logger;
import org.slf4j.LoggerFactory;
import org.springframework.util.StreamUtils;
import org.springframework.util.StringUtils;
/**
* LX:XSS对输入值进行过滤,包括数据库关键词、js注入关键词
*/
@WebFilter(filterName = "xssFilter",urlPatterns = "/*",dispatcherTypes = DispatcherType.REQUEST)
public class CrosXssFilter implements Filter {
private static final Logger logger = LoggerFactory.getLogger(CrosXssFilter.class);
private static final String xssMsg = "XssERROR 拦截:发现非法的输入值!";
@Override
public void init(FilterConfig filterConfig) throws ServletException {
}
@Override
public void doFilter(ServletRequest servletRequest, ServletResponse servletResponse, FilterChain filterChain) throws IOException, ServletException {
HttpServletRequest request = (HttpServletRequest) servletRequest;
HttpServletResponse response = (HttpServletResponse) servletResponse;
if(servletResponse instanceof HttpServletResponse){
HttpServletResponse httpServletResponse=(HttpServletResponse)servletResponse;
httpServletResponse.setHeader("Access-Control-Allow-Origin", "*");
httpServletResponse.setHeader("Access-Control-Allow-Methods", "*");
httpServletResponse.setHeader("Access-Control-Max-Age", "86400");
httpServletResponse.setHeader("Access-Control-Allow-Headers", "*");
}
XssAndSqlHttpServletRequestWrapper xssRequest=new XssAndSqlHttpServletRequestWrapper(request);
String method = ((HttpServletRequest) request).getMethod();
String param = "";
if ("POST".equalsIgnoreCase(method)) {
param = this.getBodyString(xssRequest.getReader());
if(StringUtils.hasText(param)){
if(xssRequest.checkXSSAndSql(param)){
response.setCharacterEncoding("UTF-8");
response.setStatus(200);
response.setContentType("application/json;charset=UTF-8");
PrintWriter out = servletResponse.getWriter();
Map res = new LinkedHashMap();
res.put("status","0");
res.put("msg",xssMsg);
out.print(JSON.toJSON(res));
out.flush();
out.close();
return;
}
}
}
if (xssRequest.checkParameter()) {
response.setCharacterEncoding("UTF-8");
response.setStatus(200);
response.setContentType("application/json;charset=UTF-8");
PrintWriter out = servletResponse.getWriter();
Map res = new LinkedHashMap();
res.put("status","0");
res.put("msg",xssMsg);
out.print(JSON.toJSON(res));
out.flush();
out.close();
return;
}
filterChain.doFilter(xssRequest, servletResponse);
}
// 获取request请求body中参数
public String getBodyString(BufferedReader br) {
String inputLine;
String str = "";
try {
while ((inputLine = br.readLine()) != null) {
str += inputLine;
}
br.close();
} catch (IOException e) {
logger.error("IOException: " ,e);
}
return str;
}
@Override
public void destroy() {
}
private class XssAndSqlHttpServletRequestWrapper extends HttpServletRequestWrapper {
private final Logger logger = LoggerFactory.getLogger(XssAndSqlHttpServletRequestWrapper.class);
//在这里配置要防的词汇
private String key = "insert|select|delete|drop|update|truncate";
private Set<String> notAllowedKeyWords = new HashSet<String>(0);
HttpServletRequest orgRequest = null;
private Map<String, String[]> parameterMap;
private final byte[] body; //用于保存读取body中数据
public XssAndSqlHttpServletRequestWrapper(HttpServletRequest request) throws IOException{
super(request);
orgRequest = request;
parameterMap = request.getParameterMap();
body = StreamUtils.copyToByteArray(request.getInputStream());
String keyStr[] = key.split("\\|");
for (String str : keyStr) {
notAllowedKeyWords.add(str);
}
}
@Override
public Enumeration<String> getParameterNames() {
Vector<String> vector = new Vector<String>(parameterMap.keySet());
return vector.elements();
}
/**
* 参数值进行检查
*/
@Override
public String getParameter(String name) {
String[] results = parameterMap.get(name);
if (results == null || results.length == 0)
return null;
else {
String value = results[0];
if (value != null) {
value = xssEncode(value);
}
return value;
}
}
/**
* 对于数组型的参数值进行检查
*/
@Override
public String[] getParameterValues(String name) {
String[] results = parameterMap.get(name);
if (results == null || results.length == 0)
return null;
else {
int length = results.length;
for (int i = 0; i < length; i++) {
results[i] = xssEncode(results[i]);
}
return results;
}
}
/**
* 对参数名进行检查
*/
@Override
public String getHeader(String name) {
String value = super.getHeader(xssEncode(name));
if (value != null) {
value = xssEncode(value);
}
return value;
}
/**
* LX:在这儿,就可以防住有时候客户输入了单双引号,导致页面的js被截断的问题
*
* @param s
* @return
*/
private String xssEncode(String s) {
if (s == null || s.isEmpty()) {
return s;
} else {
s = stripXSSAndSql(s);
}
StringBuilder sb = new StringBuilder(s.length() + 16);
for (int i = 0; i < s.length(); i++) {
char c = s.charAt(i);
switch (c) {
case '\'':
sb.append("'");// 转义单引号
break;
case '\"':
sb.append(""");// 转义双引号
break;
case '&':
sb.append("&");// 转义&
break;
default:
sb.append(c);
break;
}
}
return sb.toString();
}
public HttpServletRequest getOrgRequest() {
return orgRequest;
}
@SuppressWarnings("unused")
public HttpServletRequest getOrgRequest(HttpServletRequest req) {
if (req instanceof XssAndSqlHttpServletRequestWrapper) {
return ((XssAndSqlHttpServletRequestWrapper) req).getOrgRequest();
}
return req;
}
/**
*
* 防止xss跨脚本攻击(替换,根据实际情况调整)
*/
public String stripXSSAndSql(String value) {
if (value != null) {
/** value = value.replaceAll("", ""); ***/
Pattern scriptPattern = Pattern.compile(
"<[\r\n| | ]*script[\r\n| | ]*>(.*?)<!--[\r\n| | ]*script[\r\n| | ]*-->", Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
scriptPattern = Pattern.compile("src[\r\n| | ]*=[\r\n| | ]*[\\\"|\\\'](.*?)[\\\"|\\\']",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Remove any lonesome tag
scriptPattern = Pattern.compile("<!--[\r\n| | ]*script[\r\n| | ]*-->", Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Remove any lonesome <script ...> tag
scriptPattern = Pattern.compile("<[\r\n| | ]*script(.*?)>",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid eval(...) expressions
scriptPattern = Pattern.compile("eval\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid e-xpression(...) expressions
scriptPattern = Pattern.compile("e-xpression\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid javascript:... expressions
scriptPattern = Pattern.compile("javascript[\r\n| | ]*:[\r\n| | ]*", Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid vbscript:... expressions
scriptPattern = Pattern.compile("vbscript[\r\n| | ]*:[\r\n| | ]*", Pattern.CASE_INSENSITIVE);
value = scriptPattern.matcher(value).replaceAll("");
// Avoid οnlοad= expressions
scriptPattern = Pattern.compile("onload(.*?)=",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
value = scriptPattern.matcher(value).replaceAll("");
}
return value;
}
public boolean checkXSSAndSql(String value) {
boolean flag = false;
if (value != null) {
// Avoid anything between script tags
Pattern scriptPattern = Pattern.compile(
"<[\r\n| | ]*script[\r\n| | ]*>(.*?)</[\r\n| | ]*script[\r\n| | ]*>", Pattern.CASE_INSENSITIVE);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
// Avoid anything in a
// src="http://www.yihaomen.com/article/java/..." type of
// e-xpression
scriptPattern = Pattern.compile("src[\r\n| | ]*=[\r\n| | ]*[\\\"|\\\'](.*?)[\\\"|\\\']",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
// Remove any lonesome </script> tag
scriptPattern = Pattern.compile("<!--[\r\n| | ]*script[\r\n| | ]*-->", Pattern.CASE_INSENSITIVE);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
// Remove any lonesome <script ...> tag
scriptPattern = Pattern.compile("<[\r\n| | ]*script(.*?)>",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
// Avoid eval(...) expressions
scriptPattern = Pattern.compile("eval\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
// Avoid e-xpression(...) expressions
scriptPattern = Pattern.compile("e-xpression\\((.*?)\\)",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
// Avoid javascript:... expressions
scriptPattern = Pattern.compile("javascript[\r\n| | ]*:[\r\n| | ]*", Pattern.CASE_INSENSITIVE);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
// Avoid vbscript:... expressions
scriptPattern = Pattern.compile("vbscript[\r\n| | ]*:[\r\n| | ]*", Pattern.CASE_INSENSITIVE);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
// Avoid οnlοad= expressions
scriptPattern = Pattern.compile("onload(.*?)=",
Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL);
flag = scriptPattern.matcher(value).find();
if (flag) {
return flag;
}
flag=checkSqlKeyWords(value);
}
return flag;
}
public boolean checkSqlKeyWords(String value){
String paramValue = value.toLowerCase();//转成小写
for (String keyword : notAllowedKeyWords) {
if (paramValue.length() > keyword.length() + 4
&& (paramValue.contains(" "+keyword)||paramValue.contains(keyword+" ")||paramValue.contains(" "+keyword+" "))) {
logger.error(this.getRequestURI()+ "SQL参数中包含敏感词汇(" + keyword
+ ")");
return true;
}
}
return false;
}
public final boolean checkParameter() {
@SuppressWarnings({ "unchecked", "rawtypes" })
Map<String, String[]> submitParams = new HashMap(parameterMap);
Set<String> submitNames = submitParams.keySet();
for (String submitName : submitNames) {
Object submitValues = submitParams.get(submitName);
if ((submitValues instanceof String)) {
if (checkXSSAndSql((String) submitValues)) {
return true;
}
} else if ((submitValues instanceof String[])) {
for (String submitValue : (String[])submitValues){
if (checkXSSAndSql(submitValue)) {
return true;
}
}
}
}
return false;
}
@Override
public BufferedReader getReader() throws IOException {
return new BufferedReader(new InputStreamReader(getInputStream()));
}
@Override
public ServletInputStream getInputStream() throws IOException {
final ByteArrayInputStream bais = new ByteArrayInputStream(body);
return new ServletInputStream() {
@Override
public int read() throws IOException {
return bais.read();
}
};
}
}
}
2.springboot启动类上加上扫描注解:
@ServletComponentScan