实验环境:(每个服务器推荐内存为8G)
服务器 ip地址 主机名
centos7 192.168.80.171 k8s-master
centos7 192.168.80.172 k8s-node1
centos7 192.168.80.173 k8s-node2
目录
实验环境:(每个服务器推荐内存为8G)
一、安装docker——脚本安装
二、安装Kubernetes
1.基本环境——脚本部署
2、安装kubelet、kubeadm、kubectl——脚本安装
3、初始化master节点
1、初始化(注意pod和主机ip网段不能重复,我就是重复了,找半天问题md)
2、记录关键信息
3、安装Calico网络插件
4、加入worker节点(node1和node2上面执行)
三、安装KubeSphere前置环境
1、NFS文件系统
1、安装NFS-server
2、配置nfs-client(选做)(在node1和node2 )
3、配置默认存储(将ip改为自己master的)
2、metrics-server 集群指标监控组件
四、安装KubeSphere
1、下载核心文件
2、修改cluster-configuration
3、执行安装
4、查看安装进度
访问任意机器的 30880端口
一、安装docker——脚本安装
vim install_docker.sh
#!/bin/bash
# 移除旧版本docker
sudo yum remove docker*
# 安装yum-utils
sudo yum install -y yum-utils
# 配置docker的yum地址
sudo yum-config-manager --add-repo http://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo
# 安装指定版本的docker
sudo yum install -y docker-ce-20.10.7 docker-ce-cli-20.10.7 containerd.io-1.4.6
# 启动&设置开机启动docker
sudo systemctl enable docker --now
# 配置docker加速
sudo mkdir -p /etc/docker
sudo tee /etc/docker/daemon.json <<-'EOF'
{
"registry-mirrors": ["https://ij054rhe.mirror.aliyuncs.com"],
"exec-opts": ["native.cgroupdriver=systemd"],
"log-driver": "json-file",
"log-opts": {
"max-size": "100m"
},
"storage-driver": "overlay2"
}
EOF
sudo systemctl daemon-reload
sudo systemctl restart docker
chmod +x install_docker.sh && bash install_docker.sh
二、安装Kubernetes
1.基本环境——脚本部署
Vim k8s-envconf.sh
#!/bin/bash
# 临时关闭SELinux
sudo setenforce 0
sudo systemctl stop firewalld
sudo systemctl disable firewalld
# 修改SELinux配置文件
sudo sed -i 's/^SELINUX=enforcing$/SELINUX=permissive/' /etc/selinux/config
# 关闭swap
sudo swapoff -a
sudo sed -ri 's/.*swap.*/#&/' /etc/fstab
# 允许iptables检查桥接流量
cat <<EOF | sudo tee /etc/modules-load.d/k8s.conf
br_netfilter
EOF
cat <<EOF | sudo tee /etc/sysctl.d/k8s.conf
net.bridge.bridge-nf-call-ip6tables = 1
net.bridge.bridge-nf-call-iptables = 1
EOF
sudo sysctl --system
chmod +x k8s-envconf.sh && bash k8s-envconf.sh
2、安装kubelet、kubeadm、kubectl——脚本安装
Vim install-k8s.sh
#!/bin/bash
# 添加Kubernetes的yum源
cat <<EOF | sudo tee /etc/yum.repos.d/kubernetes.repo
[kubernetes]
name=Kubernetes
baseurl=http://mirrors.aliyun.com/kubernetes/yum/repos/kubernetes-el7-x86_64
enabled=1
gpgcheck=0
repo_gpgcheck=0
gpgkey=http://mirrors.aliyun.com/kubernetes/yum/doc/yum-key.gpg
http://mirrors.aliyun.com/kubernetes/yum/doc/rpm-package-key.gpg
EOF
# 安装kubelet,kubeadm,kubectl
sudo yum install -y kubelet-1.20.9 kubeadm-1.20.9 kubectl-1.20.9
# 启动kubelet并设置开机启动
sudo systemctl enable --now kubelet
echo "192.168.80.171 k8s-master" >> /etc/hostschmod +x install-k8s.sh && bash install-k8s.sh
3、初始化master节点
1、初始化(注意pod和主机ip网段不能重复,我就是重复了,找半天问题md)
kubeadm init \
--apiserver-advertise-address=192.168.80.171 \
--control-plane-endpoint=k8s-master \
--image-repository registry.cn-hangzhou.aliyuncs.com/lfy_k8s_images \
--kubernetes-version v1.20.9 \
--service-cidr=10.96.0.0/16 \
--pod-network-cidr=10.244.0.0/162、记录关键信息
Your Kubernetes control-plane has initialized successfully!
To start using your cluster, you need to run the following as a regular user:
mkdir -p $HOME/.kube
sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
sudo chown $(id -u):$(id -g) $HOME/.kube/config
Alternatively, if you are the root user, you can run:
export KUBECONFIG=/etc/kubernetes/admin.conf
You should now deploy a pod network to the cluster.
Run "kubectl apply -f [podnetwork].yaml" with one of the options listed at:
https://kubernetes.io/docs/concepts/cluster-administration/addons/
You can now join any number of control-plane nodes by copying certificate authorities
and service account keys on each node and then running the following as root:
kubeadm join k8s-master:6443 --token 0yiilp.p7x4rgys0niv52yn \
--discovery-token-ca-cert-hash sha256:c93074aeb47bebf72978db3dc45812d516d614a56614535dbe8cc4867b1f110b \
--control-plane
Then you can join any number of worker nodes by running the following on each as root:
kubeadm join k8s-master:6443 --token 0yiilp.p7x4rgys0niv52yn \
--discovery-token-ca-cert-hash sha256:c93074aeb47bebf72978db3dc45812d516d614a56614535dbe8cc4867b1f110b
将k8s核心管理员配置文件移动到当前root用户.kube/config下
mkdir -p $HOME/.kube
sudo cp -i /etc/kubernetes/admin.conf $HOME/.kube/config
sudo chown $(id -u):$(id -g) $HOME/.kube/config显示节点

3、安装Calico网络插件
curl https://docs.projectcalico.org/v3.20/manifests/calico.yaml -O
kubectl apply -f calico.yaml4、加入worker节点(node1和node2上面执行)
kubeadm join k8s-master:6443 --token 0yiilp.p7x4rgys0niv52yn \
--discovery-token-ca-cert-hash sha256:c93074aeb47bebf72978db3dc45812d516d614a56614535dbe8cc4867b1f110b 三、安装KubeSphere前置环境
1、NFS文件系统
1、安装NFS-server
# 在每个机器。
yum install -y nfs-utils# 在master 执行以下命令
echo "/nfs/data/ *(insecure,rw,sync,no_root_squash)" > /etc/exports
# 执行以下命令,启动 nfs 服务;创建共享目录
mkdir -p /nfs/data
# 在master执行
systemctl enable rpcbind
systemctl enable nfs-server
systemctl start rpcbind
systemctl start nfs-server
# 使配置生效
exportfs -r
#检查配置是否生效
exportfs2、配置nfs-client(选做)(在node1和node2 )
showmount -e 192.168.80.171
mkdir -p /nfs/data
mount -t nfs 192.168.80.171:/nfs/data /nfs/data3、配置默认存储(将ip改为自己master的)
## 创建了一个存储类
apiVersion: storage.k8s.io/v1
kind: StorageClass
metadata:
name: nfs-storage
annotations:
storageclass.kubernetes.io/is-default-class: "true"
provisioner: k8s-sigs.io/nfs-subdir-external-provisioner
parameters:
archiveOnDelete: "true" ## 删除pv的时候,pv的内容是否要备份
---
apiVersion: apps/v1
kind: Deployment
metadata:
name: nfs-client-provisioner
labels:
app: nfs-client-provisioner
# replace with namespace where provisioner is deployed
namespace: default
spec:
replicas: 1
strategy:
type: Recreate
selector:
matchLabels:
app: nfs-client-provisioner
template:
metadata:
labels:
app: nfs-client-provisioner
spec:
serviceAccountName: nfs-client-provisioner
containers:
- name: nfs-client-provisioner
image: registry.cn-hangzhou.aliyuncs.com/lfy_k8s_images/nfs-subdir-external-provisioner:v4.0.2
# resources:
# limits:
# cpu: 10m
# requests:
# cpu: 10m
volumeMounts:
- name: nfs-client-root
mountPath: /persistentvolumes
env:
- name: PROVISIONER_NAME
value: k8s-sigs.io/nfs-subdir-external-provisioner
- name: NFS_SERVER
value: 192.168.80.171 ## 指定自己nfs服务器地址
- name: NFS_PATH
value: /nfs/data ## nfs服务器共享的目录
volumes:
- name: nfs-client-root
nfs:
server: 192.168.80.171
path: /nfs/data
---
apiVersion: v1
kind: ServiceAccount
metadata:
name: nfs-client-provisioner
# replace with namespace where provisioner is deployed
namespace: default
---
kind: ClusterRole
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: nfs-client-provisioner-runner
rules:
- apiGroups: [""]
resources: ["nodes"]
verbs: ["get", "list", "watch"]
- apiGroups: [""]
resources: ["persistentvolumes"]
verbs: ["get", "list", "watch", "create", "delete"]
- apiGroups: [""]
resources: ["persistentvolumeclaims"]
verbs: ["get", "list", "watch", "update"]
- apiGroups: ["storage.k8s.io"]
resources: ["storageclasses"]
verbs: ["get", "list", "watch"]
- apiGroups: [""]
resources: ["events"]
verbs: ["create", "update", "patch"]
---
kind: ClusterRoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: run-nfs-client-provisioner
subjects:
- kind: ServiceAccount
name: nfs-client-provisioner
# replace with namespace where provisioner is deployed
namespace: default
roleRef:
kind: ClusterRole
name: nfs-client-provisioner-runner
apiGroup: rbac.authorization.k8s.io
---
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: leader-locking-nfs-client-provisioner
# replace with namespace where provisioner is deployed
namespace: default
rules:
- apiGroups: [""]
resources: ["endpoints"]
verbs: ["get", "list", "watch", "create", "update", "patch"]
---
kind: RoleBinding
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: leader-locking-nfs-client-provisioner
# replace with namespace where provisioner is deployed
namespace: default
subjects:
- kind: ServiceAccount
name: nfs-client-provisioner
# replace with namespace where provisioner is deployed
namespace: default
roleRef:
kind: Role
name: leader-locking-nfs-client-provisioner
apiGroup: rbac.authorization.k8s.io#确认配置是否生效
kubectl get sc

编辑测试 vi pvc.yaml
kind: PersistentVolumeClaim
apiVersion: v1
metadata:
name: nginx-pvc
spec:
accessModes:
- ReadWriteMany
resources:
requests:
storage: 200Mi
kubectl apply -f pvc.yaml


2、metrics-server 集群指标监控组件
vi metrics.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: metrics-server
name: metrics-server
namespace: kube-system
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
k8s-app: metrics-server
rbac.authorization.k8s.io/aggregate-to-admin: "true"
rbac.authorization.k8s.io/aggregate-to-edit: "true"
rbac.authorization.k8s.io/aggregate-to-view: "true"
name: system:aggregated-metrics-reader
rules:
- apiGroups:
- metrics.k8s.io
resources:
- pods
- nodes
verbs:
- get
- list
- watch
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
labels:
k8s-app: metrics-server
name: system:metrics-server
rules:
- apiGroups:
- ""
resources:
- pods
- nodes
- nodes/stats
- namespaces
- configmaps
verbs:
- get
- list
- watch
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
labels:
k8s-app: metrics-server
name: metrics-server-auth-reader
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: extension-apiserver-authentication-reader
subjects:
- kind: ServiceAccount
name: metrics-server
namespace: kube-system
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
k8s-app: metrics-server
name: metrics-server:system:auth-delegator
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: system:auth-delegator
subjects:
- kind: ServiceAccount
name: metrics-server
namespace: kube-system
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
labels:
k8s-app: metrics-server
name: system:metrics-server
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: system:metrics-server
subjects:
- kind: ServiceAccount
name: metrics-server
namespace: kube-system
---
apiVersion: v1
kind: Service
metadata:
labels:
k8s-app: metrics-server
name: metrics-server
namespace: kube-system
spec:
ports:
- name: https
port: 443
protocol: TCP
targetPort: https
selector:
k8s-app: metrics-server
---
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
k8s-app: metrics-server
name: metrics-server
namespace: kube-system
spec:
selector:
matchLabels:
k8s-app: metrics-server
strategy:
rollingUpdate:
maxUnavailable: 0
template:
metadata:
labels:
k8s-app: metrics-server
spec:
containers:
- args:
- --cert-dir=/tmp
- --kubelet-insecure-tls
- --secure-port=4443
- --kubelet-preferred-address-types=InternalIP,ExternalIP,Hostname
- --kubelet-use-node-status-port
image: registry.cn-hangzhou.aliyuncs.com/lfy_k8s_images/metrics-server:v0.4.3
imagePullPolicy: IfNotPresent
livenessProbe:
failureThreshold: 3
httpGet:
path: /livez
port: https
scheme: HTTPS
periodSeconds: 10
name: metrics-server
ports:
- containerPort: 4443
name: https
protocol: TCP
readinessProbe:
failureThreshold: 3
httpGet:
path: /readyz
port: https
scheme: HTTPS
periodSeconds: 10
securityContext:
readOnlyRootFilesystem: true
runAsNonRoot: true
runAsUser: 1000
volumeMounts:
- mountPath: /tmp
name: tmp-dir
nodeSelector:
kubernetes.io/os: linux
priorityClassName: system-cluster-critical
serviceAccountName: metrics-server
volumes:
- emptyDir: {}
name: tmp-dir
---
apiVersion: apiregistration.k8s.io/v1
kind: APIService
metadata:
labels:
k8s-app: metrics-server
name: v1beta1.metrics.k8s.io
spec:
group: metrics.k8s.io
groupPriorityMinimum: 100
insecureSkipTLSVerify: true
service:
name: metrics-server
namespace: kube-system
version: v1beta1
versionPriority: 100kubectl apply -f metrics.yaml
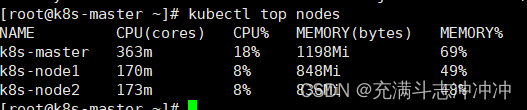
运行命令就可以查看主机信息啦
四、安装KubeSphere
KubeSphere_企业级云原生产品与服务_技术赋能数字化转型与商业运营
1、下载核心文件
wget https://github.com/kubesphere/ks-installer/releases/download/v3.1.1/kubesphere-installer.yaml
wget https://github.com/kubesphere/ks-installer/releases/download/v3.1.1/cluster-configuration.yaml2、修改cluster-configuration
在 cluster-configuration.yaml中指定我们需要开启的功能
参照官网“启用可插拔组件”
https://kubesphere.com.cn/docs/pluggable-components/overview/
---
apiVersion: installer.kubesphere.io/v1alpha1
kind: ClusterConfiguration
metadata:
name: ks-installer
namespace: kubesphere-system
labels:
version: v3.1.1
spec:
persistence:
storageClass: "" # If there is no default StorageClass in your cluster, you need to specify an existing StorageClass here.
authentication:
jwtSecret: "" # Keep the jwtSecret consistent with the Host Cluster. Retrieve the jwtSecret by executing "kubectl -n kubesphere-system get cm kubesphere-config -o yaml | grep -v "apiVersion" | grep jwtSecret" on the Host Cluster.
local_registry: "" # Add your private registry address if it is needed.
etcd:
monitoring: true # Enable or disable etcd monitoring dashboard installation. You have to create a Secret for etcd before you enable it.
endpointIps: 192.168.80.171 # etcd cluster EndpointIps. It can be a bunch of IPs here.
port: 2379 # etcd port.
tlsEnable: true
common:
redis:
enabled: true
openldap:
enabled: true
minioVolumeSize: 20Gi # Minio PVC size.
openldapVolumeSize: 2Gi # openldap PVC size.
redisVolumSize: 2Gi # Redis PVC size.
monitoring:
# type: external # Whether to specify the external prometheus stack, and need to modify the endpoint at the next line.
endpoint: http://prometheus-operated.kubesphere-monitoring-system.svc:9090 # Prometheus endpoint to get metrics data.
es: # Storage backend for logging, events and auditing.
# elasticsearchMasterReplicas: 1 # The total number of master nodes. Even numbers are not allowed.
# elasticsearchDataReplicas: 1 # The total number of data nodes.
elasticsearchMasterVolumeSize: 4Gi # The volume size of Elasticsearch master nodes.
elasticsearchDataVolumeSize: 20Gi # The volume size of Elasticsearch data nodes.
logMaxAge: 7 # Log retention time in built-in Elasticsearch. It is 7 days by default.
elkPrefix: logstash # The string making up index names. The index name will be formatted as ks-<elk_prefix>-log.
basicAuth:
enabled: false
username: ""
password: ""
externalElasticsearchUrl: ""
externalElasticsearchPort: ""
console:
enableMultiLogin: true # Enable or disable simultaneous logins. It allows different users to log in with the same account at the same time.
port: 30880
alerting: # (CPU: 0.1 Core, Memory: 100 MiB) It enables users to customize alerting policies to send messages to receivers in time with different time intervals and alerting levels to choose from.
enabled: true # Enable or disable the KubeSphere Alerting System.
# thanosruler:
# replicas: 1
# resources: {}
auditing: # Provide a security-relevant chronological set of records,recording the sequence of activities happening on the platform, initiated by different tenants.
enabled: true # Enable or disable the KubeSphere Auditing Log System.
devops: # (CPU: 0.47 Core, Memory: 8.6 G) Provide an out-of-the-box CI/CD system based on Jenkins, and automated workflow tools including Source-to-Image & Binary-to-Image.
enabled: true # Enable or disable the KubeSphere DevOps System.
jenkinsMemoryLim: 2Gi # Jenkins memory limit.
jenkinsMemoryReq: 1500Mi # Jenkins memory request.
jenkinsVolumeSize: 8Gi # Jenkins volume size.
jenkinsJavaOpts_Xms: 512m # The following three fields are JVM parameters.
jenkinsJavaOpts_Xmx: 512m
jenkinsJavaOpts_MaxRAM: 2g
events: # Provide a graphical web console for Kubernetes Events exporting, filtering and alerting in multi-tenant Kubernetes clusters.
enabled: true # Enable or disable the KubeSphere Events System.
ruler:
enabled: true
replicas: 2
logging: # (CPU: 57 m, Memory: 2.76 G) Flexible logging functions are provided for log query, collection and management in a unified console. Additional log collectors can be added, such as Elasticsearch, Kafka and Fluentd.
enabled: true # Enable or disable the KubeSphere Logging System.
logsidecar:
enabled: true
replicas: 2
metrics_server: # (CPU: 56 m, Memory: 44.35 MiB) It enables HPA (Horizontal Pod Autoscaler).
enabled: false # Enable or disable metrics-server.
monitoring:
storageClass: "" # If there is an independent StorageClass you need for Prometheus, you can specify it here. The default StorageClass is used by default.
# prometheusReplicas: 1 # Prometheus replicas are responsible for monitoring different segments of data source and providing high availability.
prometheusMemoryRequest: 400Mi # Prometheus request memory.
prometheusVolumeSize: 20Gi # Prometheus PVC size.
# alertmanagerReplicas: 1 # AlertManager Replicas.
multicluster:
clusterRole: none # host | member | none # You can install a solo cluster, or specify it as the Host or Member Cluster.
network:
networkpolicy: # Network policies allow network isolation within the same cluster, which means firewalls can be set up between certain instances (Pods).
# Make sure that the CNI network plugin used by the cluster supports NetworkPolicy. There are a number of CNI network plugins that support NetworkPolicy, including Calico, Cilium, Kube-router, Romana and Weave Net.
enabled: true # Enable or disable network policies.
ippool: # Use Pod IP Pools to manage the Pod network address space. Pods to be created can be assigned IP addresses from a Pod IP Pool.
type: calico # Specify "calico" for this field if Calico is used as your CNI plugin. "none" means that Pod IP Pools are disabled.
topology: # Use Service Topology to view Service-to-Service communication based on Weave Scope.
type: none # Specify "weave-scope" for this field to enable Service Topology. "none" means that Service Topology is disabled.
openpitrix: # An App Store that is accessible to all platform tenants. You can use it to manage apps across their entire lifecycle.
store:
enabled: true # Enable or disable the KubeSphere App Store.
servicemesh: # (0.3 Core, 300 MiB) Provide fine-grained traffic management, observability and tracing, and visualized traffic topology.
enabled: true # Base component (pilot). Enable or disable KubeSphere Service Mesh (Istio-based).
kubeedge: # Add edge nodes to your cluster and deploy workloads on edge nodes.
enabled: false # Enable or disable KubeEdge.
cloudCore:
nodeSelector: {"node-role.kubernetes.io/worker": ""}
tolerations: []
cloudhubPort: "10000"
cloudhubQuicPort: "10001"
cloudhubHttpsPort: "10002"
cloudstreamPort: "10003"
tunnelPort: "10004"
cloudHub:
advertiseAddress: # At least a public IP address or an IP address which can be accessed by edge nodes must be provided.
- "" # Note that once KubeEdge is enabled, CloudCore will malfunction if the address is not provided.
nodeLimit: "100"
service:
cloudhubNodePort: "30000"
cloudhubQuicNodePort: "30001"
cloudhubHttpsNodePort: "30002"
cloudstreamNodePort: "30003"
tunnelNodePort: "30004"
edgeWatcher:
nodeSelector: {"node-role.kubernetes.io/worker": ""}
tolerations: []
edgeWatcherAgent:
nodeSelector: {"node-role.kubernetes.io/worker": ""}
tolerations: []
3、执行安装
kubectl apply -f kubesphere-installer.yaml
kubectl apply -f cluster-configuration.yaml
解决etcd监控证书找不到问题
kubectl -n kubesphere-monitoring-system create secret generic kube-etcd-client-certs --from-file=etcd-client-ca.crt=/etc/kubernetes/pki/etcd/ca.crt --from-file=etcd-client.crt=/etc/kubernetes/pki/apiserver-etcd-client.crt --from-file=etcd-client.key=/etc/kubernetes/pki/apiserver-etcd-client.key
4、查看安装进度
kubectl logs -n kubesphere-system $(kubectl get pod -n kubesphere-system -l app=ks-install -o jsonpath='{.items[0].metadata.name}') -f
POD全部显示running就好了
kubectl get pod -A
NAMESPACE NAME READY STATUS RESTARTS AGE
default nfs-client-provisioner-7c58cbf68b-ncqjv 1/1 Running 2 53m
istio-system istio-ingressgateway-7d7fd96b9-t7fv6 1/1 Running 1 53m
istio-system istiod-1-6-10-5c8cc86fb4-zhpxp 1/1 Running 2 95m
istio-system jaeger-collector-557f8795cb-n4zvd 1/1 Running 0 93s
istio-system jaeger-operator-79ddbc974-fkt4g 1/1 Running 0 9m51s
istio-system jaeger-query-667b645b7d-6xdgh 2/2 Running 0 92s
istio-system kiali-697755c579-zc5k4 1/1 Running 1 23m
istio-system kiali-operator-76cd67fb59-l7tp6 1/1 Running 1 26m
kube-system calico-kube-controllers-577f77cb5c-wt9jq 1/1 Running 3 3h24m
kube-system calico-node-g2m9w 1/1 Running 3 3h24m
kube-system calico-node-lvnsz 1/1 Running 4 3h24m
kube-system calico-node-tfzlf 1/1 Running 4 3h24m
kube-system coredns-5897cd56c4-7f62q 1/1 Running 3 3h25m
kube-system coredns-5897cd56c4-hz97p 1/1 Running 3 3h25m
kube-system etcd-k8s-master 1/1 Running 3 3h25m
kube-system kube-apiserver-k8s-master 1/1 Running 3 3h25m
kube-system kube-controller-manager-k8s-master 1/1 Running 12 3h25m
kube-system kube-proxy-99xl9 1/1 Running 3 3h24m
kube-system kube-proxy-c8xvh 1/1 Running 3 3h25m
kube-system kube-proxy-wzf5j 1/1 Running 4 3h24m
kube-system kube-scheduler-k8s-master 1/1 Running 12 3h25m
kube-system metrics-server-6497cc6c5f-zw4jz 1/1 Running 2 53m
kube-system snapshot-controller-0 1/1 Running 2 64m
kubesphere-controls-system default-http-backend-76d9fb4bb7-7chlt 1/1 Running 1 47m
kubesphere-controls-system kubectl-admin-776b98f44f-xtsht 1/1 Running 1 20m
kubesphere-devops-system ks-jenkins-65db765f86-kn5wd 1/1 Running 2 66m
kubesphere-devops-system s2ioperator-0 1/1 Running 1 27m
kubesphere-logging-system elasticsearch-logging-data-0 1/1 Running 0 2m46s
kubesphere-logging-system elasticsearch-logging-data-1 1/1 Running 0 95s
kubesphere-logging-system elasticsearch-logging-discovery-0 1/1 Running 0 2m42s
kubesphere-logging-system fluent-bit-5vlzk 1/1 Running 3 147m
kubesphere-logging-system fluent-bit-6twx5 1/1 Running 10 147m
kubesphere-logging-system fluent-bit-wdl99 1/1 Running 3 147m
kubesphere-logging-system fluentbit-operator-5576bbdcff-xpdl5 1/1 Running 2 53m
kubesphere-logging-system ks-events-exporter-74b5c8d8b7-spg59 2/2 Running 4 55m
kubesphere-logging-system ks-events-operator-76b99948b6-7n7x8 1/1 Running 1 47m
kubesphere-logging-system ks-events-ruler-5d75bddbff-njrq8 2/2 Running 2 55m
kubesphere-logging-system ks-events-ruler-5d75bddbff-z6p7m 2/2 Running 2 55m
kubesphere-logging-system kube-auditing-operator-7967969d69-htd2r 1/1 Running 1 47m
kubesphere-logging-system kube-auditing-webhook-deploy-85bbbbd9bb-2jnw2 1/1 Running 1 47m
kubesphere-logging-system kube-auditing-webhook-deploy-85bbbbd9bb-4jzpb 1/1 Running 1 47m
kubesphere-logging-system logsidecar-injector-deploy-5b484f575d-2mrzn 2/2 Running 2 47m
kubesphere-logging-system logsidecar-injector-deploy-5b484f575d-vm55b 2/2 Running 2 47m
kubesphere-monitoring-system alertmanager-main-0 2/2 Running 0 2m50s
kubesphere-monitoring-system alertmanager-main-1 2/2 Running 0 2m48s
kubesphere-monitoring-system alertmanager-main-2 2/2 Running 0 2m49s
kubesphere-monitoring-system kube-state-metrics-67588479db-jfng9 3/3 Running 3 55m
kubesphere-monitoring-system node-exporter-89cjb 2/2 Running 2 55m
kubesphere-monitoring-system node-exporter-bqlvj 2/2 Running 4 55m
kubesphere-monitoring-system node-exporter-mn72c 2/2 Running 2 55m
kubesphere-monitoring-system notification-manager-deployment-7bd887ffb4-9jgkf 1/1 Running 1 9m51s
kubesphere-monitoring-system notification-manager-deployment-7bd887ffb4-v494r 1/1 Running 1 9m51s
kubesphere-monitoring-system notification-manager-operator-78595d8666-ntsmt 2/2 Running 2 54m
kubesphere-monitoring-system prometheus-k8s-0 3/3 Running 1 2m47s
kubesphere-monitoring-system prometheus-k8s-1 3/3 Running 1 3m18s
kubesphere-monitoring-system prometheus-operator-d7fdfccbf-mzp5k 2/2 Running 2 55m
kubesphere-monitoring-system thanos-ruler-kubesphere-0 2/2 Running 0 3m18s
kubesphere-monitoring-system thanos-ruler-kubesphere-1 2/2 Running 0 3m17s
kubesphere-system ks-apiserver-6d86454ddf-wqfgl 1/1 Running 2 24m
kubesphere-system ks-console-6d6d765964-kcw9b 1/1 Running 2 98m
kubesphere-system ks-controller-manager-84f6bc569f-ksrv4 1/1 Running 3 24m
kubesphere-system ks-installer-54c6bcf76b-j85t9 1/1 Running 1 53m
kubesphere-system minio-f69748945-sqg7d 1/1 Running 0 9m51s
kubesphere-system openldap-0 1/1 Running 3 100m
kubesphere-system openpitrix-import-job-tth2d 0/1 Completed 0 29m
kubesphere-system redis-58f948c9b4-69gbk 1/1 Running 2 100m
访问任意机器的 30880端口
账号 : admin
密码 : P@88w0rd