kubernetes-RBAC 鉴权
- kubernetes-RBAC 鉴权
- 1、查看整个k8s集群内部有哪些资源
- 2、什么是鉴权
- 2.1、鉴权的目的
- 2.2、怎么去鉴权:RBAC
- 2.3、对鉴权的理解🌱
- 2.4、租户
- 3、对一些概念的解释
- 3.1、概念简述
- 3.2、账号类型:Useraccount和ServiceAccount介绍
- 3.3、SA(Service Account)
- 3.4、k8s集群中已经有很多role和clusterRole
- 3.5、SA(ServiceAccount)使用案例介绍
- 3.7、查看 cluster-admin 详细信息
- 3.8、自己创建一个role
- 3.9、整个绑定流程
- 3.10、普通用户去访问的流程
- 3.11、实验一下普通用户去访问k8s里的资源对象
kubernetes-RBAC 鉴权
1、查看整个k8s集群内部有哪些资源
[root@node-1 ~]# kubectl api-resources
NAME SHORTNAMES APIVERSION NAMESPACED KIND
bindings v1 true Binding
componentstatuses cs v1 false ComponentStatus
configmaps cm v1 true ConfigMap
endpoints ep v1 true Endpoints
events ev v1 true Event
2、什么是鉴权
鉴别权限 --》识别出某个主体(用户、组、服务账户)具有什么权限 —》鉴定权限
2.1、鉴权的目的
保障安全, 防止没有得到授权的用户访问我们的k8s资源,破坏k8s里的资源。
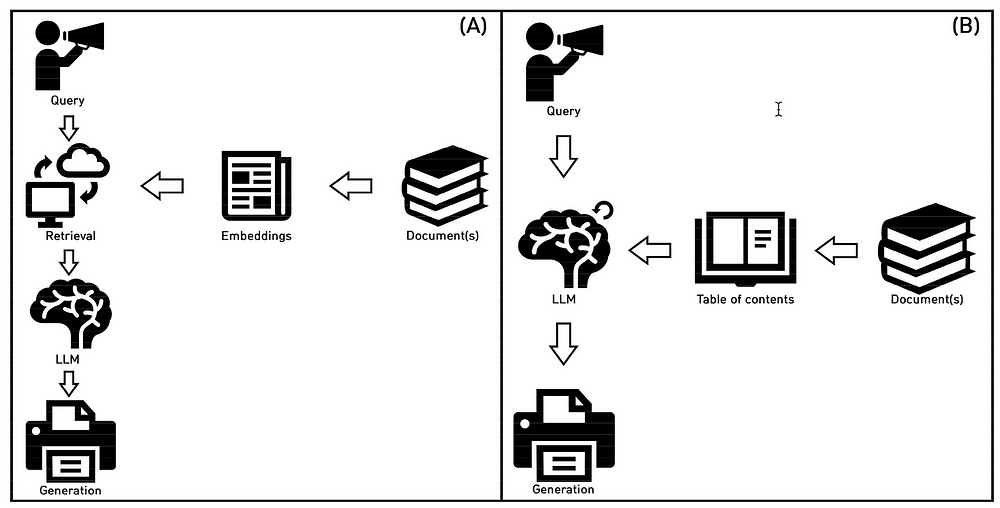
2.2、怎么去鉴权:RBAC
基于角色的访问控制(RBAC)是一种基于组织中各个用户的角色来调节对计算机或网络资源的访问的方法。
-
什么样的用户,就有什么样的角色,什么样的角色有特点的权限
-
用户 --》角色 --》权限–》资源对象
-
目的:防止k8s里的pod(会运行程序)能随意获取整个集群里的信息和访问集群里的资源
2.3、对鉴权的理解🌱
-
用户绑定一个角色—》演这个人—》这个角色有个权限—》比方说:省长 -
省长有看读的权限—》角色规定了你能看和利用什么资源

- 大红薯,漂亮团等租户去
租阿里云的k8s服务器集群 - 这个集群假设有1000台
node机器 - 不同的租户
启动pod来管理自己的业务 - 不同的租户创建一个不同的用户绑定到不同的k8s里的useraccount上
如何控制和隔离?
可以通过:
- 命名空间
- 鉴权: 控制不同的租户在k8s内部访问
不同租户启动pod去访问别人租户的pod里的业务—》安全性问题如何解决?
鉴权: RBAC:基于角色的访问控制
- 给不同的租户创建不同的账号
- pod使用这些账号
- 不同的账号会绑定不同的角色
- 不同的角色能访问不同的资源和动作
2.4、租户
- 租别人东西的人 —》租阿里云/腾讯云/华为云的企业
ACK--->是阿里云提供的k8s服务
server: 服务器
- 容器服务 Kubernetes 版 ACK --》自己在阿里云上购买 k8s服务,你会有自己的node节点服务器,master节点 是阿里云提供的。
- 需要自己购买node节点服务器
serverless: 没有服务器
- 不需要购买k8s的node节点服务器了,直接购买已经搭建好的k8s集群的容器就可以了
- 只要将你的程序放到容器里直接运行就可以了,按时间和容器数量跟你计费

3、对一些概念的解释
3.1、概念简述
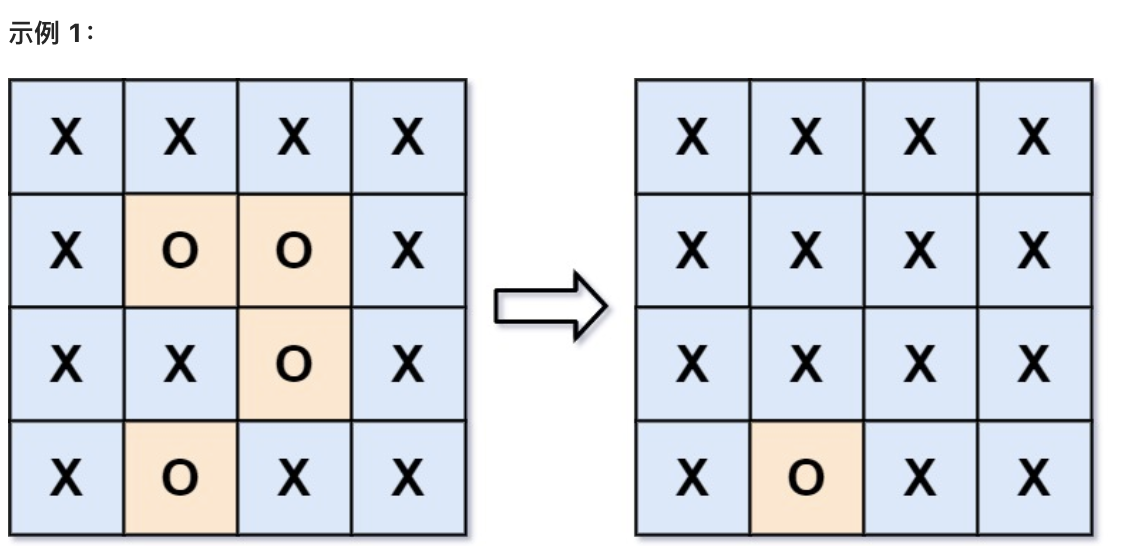
Rule:规则,一组属于不同 API Group 的操作集合;
Role:角色,用于定义一组对 Kubernetes API 对象操作的一组规则,范围限定在 namespace; --》省长
ClusterRole:集群角色,该角色不受 namespace 的限制; --》国家主席
Subject:对象,也就是规则作用的对象;
RoleBinding:将角色和对象进行绑定,范围限定在 namespace
ClusterRoleBinding:将集群角色和对象进行绑定,不受 namespace 限制
Serviceaccount: 服务账户–》pod–》apiserver
3.2、账号类型:Useraccount和ServiceAccount介绍
User Account :用于外部用户,代表了真实的人,通常通过用户名和密码或令牌进行身份验证。
Service Account: 用于集群内部的应用程序,代表了运行在Pod中的服务,通过自动生成的令牌进行身份验证。
在Kubernetes集群中,用户账户通过以下两种方式进行身份验证:
- **
基本身份验证(Basic Authentication):**这是最简单的身份验证方式,用户通过提供用户名和密码来访问API服务器。这种方式在Kubernetes集群的早期版本中较为常见。 - **
Bearer Tokens:**用户通过获取一个令牌(Token)来进行身份验证。这个令牌可以是一个访问令牌(Access Token),通常由OAuth服务器或类似的认证服务颁发。
用户账户通常与角色绑定(Role Binding)或集群角色绑定(Cluster Role Binding)结合使用,以便为用户分配特定的权限。这些权限定义了用户可以对集群中的资源执行哪些操作。
Service Account就像个通行证一样,有这个证件就可以实现很多事情
3.3、SA(Service Account)
SA(Service Account)---->植入到pod里,pod会以SA账号的身份去访问k8s集群内部的资源(api-server etcd ns pod等)
3.4、k8s集群中已经有很多role和clusterRole
[root@node-1 ~]# kubectl get roles -n kube-system
NAME CREATED AT
extension-apiserver-authentication-reader 2024-03-03T03:15:09Z
kube-proxy 2024-03-03T03:15:11Z
kubeadm:kubelet-config-1.20 2024-03-03T03:15:10Z
kubeadm:nodes-kubeadm-config 2024-03-03T03:15:10Z
system::leader-locking-kube-controller-manager 2024-03-03T03:15:09Z
system::leader-locking-kube-scheduler 2024-03-03T03:15:09Z
system:controller:bootstrap-signer 2024-03-03T03:15:09Z
system:controller:cloud-provider 2024-03-03T03:15:09Z
system:controller:token-cleaner 2024-03-03T03:15:09Z
您在 /var/spool/mail/root 中有新邮件
[root@node-1 ~]#
[root@node-1 ~]# kubectl get clusterrole
NAME CREATED AT
admin 2024-03-03T03:15:09Z
calico-kube-controllers 2024-03-03T03:34:42Z
calico-node 2024-03-03T03:34:42Z
cluster-admin 2024-03-03T03:15:09Z
edit 2024-03-03T03:15:09Z
kubeadm:get-nodes 2024-03-03T03:15:11Z
system:aggregate-to-admin 2024-03-03T03:15:09Z
system:aggregate-to-edit 2024-03-03T03:15:09Z
system:aggregate-to-view 2024-03-03T03:15:09Z
查看某个角色用能访问那些资源,能采取那些动作
[root@node-2 .kube]# kubectl describe roles kubeadm:kubelet-config-1.20 -n kube-system
Name: kubeadm:kubelet-config-1.20
Labels: <none>
Annotations: <none>
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
configmaps [] [kubelet-config-1.20] [get]
[root@node-2 .kube]#
3.5、SA(ServiceAccount)使用案例介绍
1.创建sa
[root@master ~]# kubectl create sa sa-lihaihui
serviceaccount/sa-lihaihui created
[root@master ~]#
[root@master ~]# kubectl get sa
NAME SECRETS AGE
default 1 18d
sa-lihaihui 1 47s
[root@master ~]#
2.创建pod
[root@master ~]# mkdir /RBAC
[root@master ~]# cd /RBAC/
[root@master RBAC]# ls
[root@master RBAC]#
[root@master RBAC]# vim sa-pod.yaml
apiVersion: v1
kind: Pod
metadata:
name: sa-lihaihui
namespace: default
labels:
app: sa-lihaihui
spec:
serviceAccountName: sa-lihaihui # pod use service accout
containers:
- name: sa-nginx
ports:
- containerPort: 80
image: nginx
imagePullPolicy: IfNotPresent
[root@master RBAC]#
[root@master RBAC]# kubectl apply -f sa-pod.yaml
pod/sa-lihaihui created
[root@master RBAC]# kubectl get pod
NAME READY STATUS RESTARTS AGE
sa-lihaihui 1/1 Running 0 4s
3.因为pod 会去访问k8s集群的apiserver,所以需要进入到pod里
[root@master RBAC]# kubectl exec -it sa-lihaihui -- bash
root@sa-lihaihui:/#
root@sa-lihaihui:/# cd /var/run/secrets/kubernetes.io/serviceaccount/
root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount# ls
ca.crt namespace token
root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount#
4.执行下面的命令去访问我们的apiserver
root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount# curl --cacert ./ca.crt -H "Authorization: Bearer $(cat ./token)" https://kubernetes/api/v1/namespaces/kube-system
{
"kind": "Status",
"apiVersion": "v1",
"metadata": {
},
"status": "Failure",
"message": "namespaces \"kube-system\" is forbidden: User \"system:serviceaccount:default:sa-lihaihui\" cannot get resource \"namespaces\" in API group \"\" in the namespace \"kube-system\"",
"reason": "Forbidden",
"details": {
"name": "kube-system",
"kind": "namespaces"
},
"code": 403
}root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount#
403了—》没有权限访问其他命名空间
5.对sa授权
cluster-admin 这是一个权力非常大的clusterrole 集群角色
cluster-admin—》集群管理员
[root@master RBAC]# kubectl create clusterrolebinding sa-test-lihaihui --clusterrole=cluster-admin --serviceaccount=default:sa-lihaihui
clusterrolebinding.rbac.authorization.k8s.io/sa-test-lihaihui created
[root@master RBAC]#
查看是否绑定成功
[root@master RBAC]# kubectl get clusterrolebinding sa-test-lihaihui
NAME ROLE AGE
sa-test-lihaihui ClusterRole/cluster-admin 3m5s
[root@master RBAC]#
[root@master RBAC]# kubectl get clusterrolebinding|grep lihaihui
sa-test-lihaihui ClusterRole/cluster-admin 5m47s
[root@master RBAC]#
6.再次请求,使用绑定好的集群角色
[root@master RBAC]# kubectl exec -it sa-lihaihui -- bash
root@sa-lihaihui:/# cd /var/run/secrets/kubernetes.io/serviceaccount/
root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount/
bash: root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount/: No such file or directory
root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount# curl --cacert ./ca.crt -H "Authorization: Bearer $(cat ./token)" https://kubernetes/api/v1/namespaces/kube-system
{
"kind": "Namespace",
"apiVersion": "v1",
"metadata": {
"name": "kube-system",
"uid": "d4855b44-8239-4180-84ea-243ea34d9006",
"resourceVersion": "11",
"creationTimestamp": "2024-03-03T03:15:08Z",
"managedFields": [
{
"manager": "kube-apiserver",
"operation": "Update",
"apiVersion": "v1",
"time": "2024-03-03T03:15:08Z",
"fieldsType": "FieldsV1",
"fieldsV1": {"f:status":{"f:phase":{}}}
}
]
},
"spec": {
"finalizers": [
"kubernetes"
]
},
"status": {
"phase": "Active"
}
}root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount#
3.7、查看 cluster-admin 详细信息
[root@k8smaster sa]# kubectl describe clusterroles cluster-admin
Name: cluster-admin
Labels: kubernetes.io/bootstrapping=rbac-defaults
Annotations: rbac.authorization.kubernetes.io/autoupdate: true
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
*.* [] [] [*]
[*] [] [*]
[root@k8smaster sa]#
Resources 代表这个角色可以访问的资源 . 代表任意命名空间里的任意资源
Verbs : 可以采取的动作 : get list watch
verbs: [“get”,“list”,“watch”,“create”,“update”,“patch”,“delete”]
3.8、自己创建一个role
[root@master RBAC]# vim role.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: Role
metadata:
namespace: default
name: pod-reader
rules:
- apiGroups: [""] # "" 标明 core API 组
resources: ["pods"]
verbs: ["get", "watch", "list"]
[root@master RBAC]# kubectl apply -f role.yaml
role.rbac.authorization.k8s.io/pod-reader created
[root@master RBAC]# kubectl get role
NAME CREATED AT
pod-reader 2024-03-21T12:58:46Z
[root@master RBAC]#
sa绑定role
[root@master RBAC]# kubectl create rolebinding sa-test-lihaihui --role=pod-reader --serviceaccount=default:sa-lihaihui
rolebinding.rbac.authorization.k8s.io/sa-test-lihaihui created
[root@master RBAC]#
查看已经绑定的rolebinding
[root@master RBAC]# kubectl get rolebinding
NAME ROLE AGE
sa-test-lihaihui Role/pod-reader 37s
[root@master RBAC]#
创建一个clusterrole
[root@master RBAC]# vim clusterrole.yaml
[root@master RBAC]# cat clusterrole.yaml
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
# "namespace" 被忽略,因为 ClusterRoles 不受名字空间限制
name: secret-reader
rules:
- apiGroups: [""]
# 在 HTTP 层面,用来访问 Secret 资源的名称为 "secrets"
resources: ["secrets"] #具体的资源对象
verbs: ["get", "watch", "list"] #动作
[root@master RBAC]# kubectl apply -f clusterrole.yaml
clusterrole.rbac.authorization.k8s.io/secret-reader created
[root@master RBAC]# kubectl get clusterrole|grep secret-reader
secret-reader 2024-03-21T13:03:51Z
[root@master RBAC]#
将sa-lihaihui 绑定到secret-reader 的集群角色上
[root@master RBAC]# kubectl create clusterrolebinding sa-test-lihaihui-2 --clusterrole=secret-reader --serviceaccount=default:sa-lihaihui
clusterrolebinding.rbac.authorization.k8s.io/sa-test-lihaihui-2 created
[root@master RBAC]# kubectl get clusterrolebinding|grep sa-test-lihaihui
sa-test-lihaihui ClusterRole/cluster-admin 37m
sa-test-lihaihui-2 ClusterRole/secret-reader 2m27s
[root@master RBAC]#
验证:
启动–>就是进入sa-lihaihui启动的pod,去访问apiserver里的pod资源和secret资源
[root@master RBAC]# kubectl exec -it sa-lihaihui -- bash
root@sa-lihaihui:/#
root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount# curl --cacert ./ca.crt -H "Athorization: Bearer $(cat ./token)" https://kubernetes/api/v1/pods
root@sa-lihaihui:/var/run/secrets/kubernetes.io/serviceaccount# curl --cacert ./ca.crt -H "Authorization: Bearer $(cat .token)" https://kubernetes/api/v1/secrets
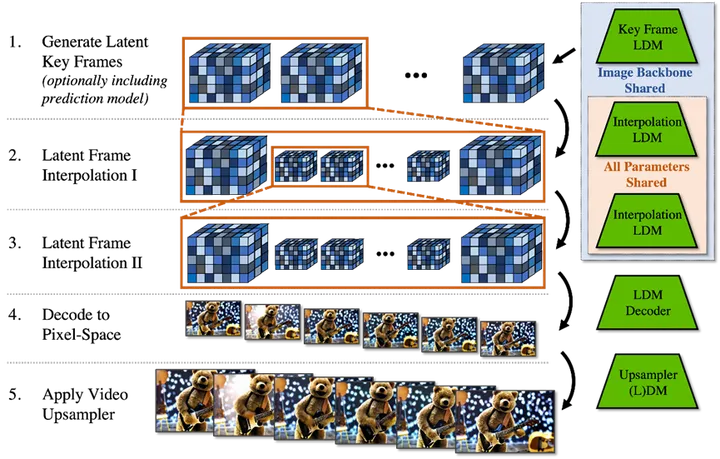
3.9、整个绑定流程
总结来说,这个流程描述了服务账号如何在Kubernetes集群中与资源对象交互,以及如何通过Role和ClusterRole来控制对这些资源的访问权限。通过RoleBinding和ClusterRoleBinding,服务账号被授予执行特定操作的权限,从而使得Pod中的应用程序能够安全地与Kubernetes集群的资源进行交互。
3.10、普通用户去访问的流程
人–》k8s客户端(一般用:kubectl) ------>API Server
gaohui–》linux系统–》k8s的useraccount–>gaohui(k8s中的用户)–>k8s客户端(一般用:kubectl) ------>API Server

3.11、实验一下普通用户去访问k8s里的资源对象
ssl认证:需要使用root用户去创建证书
1.生成一个证书—>保证安全性
(1)生成一个私钥
[root@master ~]# cd /etc/kubernetes/pki/
[root@master pki]# (umask 077; openssl genrsa -out gaohui.key 2048)
Generating RSA private key, 2048 bit long modulus
...........................+++
.........+++
e is 65537 (0x10001)
[root@master pki]#
(2)生成一个证书请求--->'相当于找个第三方机构认证'
[root@master pki]# openssl req -new -key gaohui.key -out gaohui.csr -subj "/CN=gaohui"
(3)生成一个证书
[root@master pki]# openssl x509 -req -in gaohui.csr -CA ca.crt -CAkey ca.key -CAcreateserial -out gaohui.crt -days 3650
Signature ok
subject=/CN=gaohui
Getting CA Private Key
[root@master pki]#
2.在kubeconfig下新增加一个gaohui这个用户
(1)把gaohui这个用户添加到kubernetes集群中,可以用来认证apiserver的连接
[root@master pki]# kubectl config set-credentials gaohui --client-certificate=./gaohui.crt --client-key=./gaohui.key --embed-certs=true
(2)在kubeconfig下新增加一个gaohui这个账号,相当于在~/.kube/config添加miqiang用户
[root@master pki]# kubectl config set-context gaohui@kubernetes --cluster=kubernetes --user=gaohui
(3)切换账号到miqiang,默认没有任何权限
kubectl config use-context gaohui@kubernetes
切换过去之后,去访问node
[root@master pki]# kubectl get node
Error from server (Forbidden): nodes is forbidden: User "gaohui" cannot list resource "nodes" in API group "" at the cluster scope
[root@master pki]#
发现gaohui这个k8s里的用户不能访问api server
发现没有任何权限,然后使用下面的命令切换回去kubernetes-admin@kubernetes用户
这个是集群用户,有任何权限👆
kubectl config use-context kubernetes-admin@kubernetes
3.把gaohui 这个用户通过rolebinding绑定到clusterrole上,授予权限,权限只是在gaohui这个名称空间有效
(1)把gaohui这个用户通过rolebinding绑定到clusterrole上
kubectl create ns gaohui-test
kubectl create rolebinding gaohui -n gaohui-test --clusterrole=cluster-admin --user=gaohui
'或者用下边这个命令↓'
kubectl create rolebinding gaohui --namespace gaohui-test --clusterrole=cluster-admin --user=gaohui
(2)切换到gaohui这个用户
kubectl config use-context gaohui@kubernetes
(3)测试是否有权限
[root@master pki]# kubectl get pods -n gaohui-test
No resources found in gaohui-test namespace.
[root@master pki]#
'成功了↑'
'有权限操作这个gaohui-test名称空间'
4.在linux操作系统里创建gaohui这个用户,可以用来登录k8s集群所在的linux系统
不同租户给与不同的linux系统账号,然后关联不同的k8s集群里的useraccout
添加一个gaohui的普通用户
[root@master pki]# useradd gaohui
cp -ar /root/.kube/ /home/gaohui/
chown -R gaohui.gaohui /home/gaohui/
修改/home/gaohui/.kube/config文件,把kubernetes-admin相关的删除,只留gaohui用户
[root@master .kube]# cd /home/gaohui/.kube/
[root@master .kube]# ls
cache config
[root@master .kube]#
'删除kubernetes-admin后相关的效果如下↓:'
[root@master .kube]# vim config
apiVersion: v1
clusters:
- cluster:
certificate-authority-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUM1ekNDQWMrZ0F3SUJBZ0lCQURBTkJna3Foa2lHOXcwQkFRc0ZBREFWTVJNd0VRWURWUVFERXdwcmRXSmwKY201bGRHVnpNQjRYRFRJME1ETXdNekF6TVRNek1Gb1hEVE0wTURNd01UQXpNVE16TUZvd0ZURVRNQkVHQTFVRQpBeE1LYTNWaVpYSnVaWFJsY3pDQ0FTSXdEUVlKS29aSWh2Y05BUUVCQlFBRGdnRVBBRENDQVFvQ2dnRUJBTHNpCmhWdjMzbnNvcW1LL1RJbWE1cnNxdExYVDFCcnZJeklGVEFFUEdRZExJVmYyYWZ0RTM3K21La0RUb29SNTRwQk8KY05oOFkrbzBwRDE4T09TUXowRE51cEpWK3hWOXNWY085WFE0K2FHdzcxL1FNMzRFQUdZZThYMnVEeHgrL29XdQpXaTVpMms3d01CUWNpUkNYV2xKWTVJdlBldE0xTW5ZRzNsYUhHNlozVVJMSE1XWVBZVGVqRnVKRnQxQ0JwNm9ZCmkvKzRnamZwUVc2Y2VHdVVBZFZ6Y2NuM05zTklRRlFiS1ZCeXRmZktENnFCZnZaellpVXhFVU5WemNnYW9DbWsKd0dqNDlhREtqd0JNSloyUVZ1SDZsR2xuMVBoYktjTnhWY0JaK2s5RUlqWnV4emNaZTVYejdOSG5mbGZzNm02SApUcElXdWJTSGVINkZKMUM3Z2pjQ0F3RUFBYU5DTUVBd0RnWURWUjBQQVFIL0JBUURBZ0trTUE4R0ExVWRFd0VCCi93UUZNQU1CQWY4d0hRWURWUjBPQkJZRUZLbExhdWp4NGsrYmxNZE8xalBHUHVaNEpxaHVNQTBHQ1NxR1NJYjMKRFFFQkN3VUFBNElCQVFCQzJQRjBIMDVTeUZFMERYNlpodTJSMlRJdDhZYlBZOG9SaU91a3Z5SzBJZWgyWkVwNgpnY0ppMG9SK2NyNjVWRU1IcWhJZy9mRi9LVUVpTS80YkZ5Q2ZWZXlzdjM1SVUvZmI0aFFkc0ZsNFRGdEtFQXFTCjBGQkV6YkRBUUF0bWpGUTR5UTZuZ3V0MGExTlNnTjJ1QXlmU2hYb1dmNHd0aWg4VkJ0aTFVdFBQYzliMEJYVVYKTEZydit3azhlSFA4RGJyd2tOWVFPSlZmc0RmSDNXejBhb1V1V1hSZnh0djFaY2hJck9HOU5nMzREdmRXVTJ2TQoxa1JoVmVYTW5kVU0rbEV5aFVnd3hoamlqNnhQZExwTEhhdG5uNHVVSXZGZ3ZTenpjdmFjR0tVcU1HTElVMHZqCjI2MGo3Y3pVY1h4dVR6YWxKZW9QeEFncTBCV2hHS2U4Mk9jaAotLS0tLUVORCBDRVJUSUZJQ0FURS0tLS0tCg==
server: https://192.168.182.133:6443
name: kubernetes
contexts:
- context:
cluster: kubernetes
user: gaohui
name: gaohui@kubernetes
current-context: gaohui@kubernetes
kind: Config
preferences: {}
users:
- name: gaohui
user:
client-certificate-data: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSUNvakNDQVlvQ0NRRDJKTTBGV0ZDY2N6QU5CZ2txaGtpRzl3MEJBUXNGQURBVk1STXdFUVlEVlFRREV3cHIKZFdKbGNtNWxkR1Z6TUI0WERUSTBNRE15TVRFME1qWXhNbG9YRFRNME1ETXhPVEUwTWpZeE1sb3dFVEVQTUEwRwpBMVVFQXd3R1oyRnZhSFZwTUlJQklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUFtNm8wCjF1N2RIYUdMa2MvQzhld2d5OUJTbTZtUzI1RjJEUWEzT052RloyWWdOOUhJY1VReHFldXBXVWVwbmpwMzhSMWUKcnd4WGpiaC9KVHV3cDFDbTE3TFk1Z05LeTVVNkswMDRvYXV5cVdDclNvOWQwVEd3ejRZQlFZM0JOQWVRUkNZMQpRZ3JlWitLM25haGxGeWx2VjdZaGsvZVNMRkl4QkM0clI0S2tWV0xpRUFNYlpad21TOXViSFFmMEJROC9hZTFMCnMvMEd6d3NnVDhOTE14YU1NOExrYXJoMzlCbkhsVHRxcmFiRFNvWlp0bU5RYVJ3aE96YjVsTG91c0pqeStlTHcKR2N2UUFtQ3RsVlNFSXVvMWc4d0VzK01MSlAwb0xDSjEwZXgrdTRtemVUTEx0dGY4eXMzOU9DUEM2QnJNeVFSdwo4OTduMlBScW5MQ2lHMU5LK1FJREFRQUJNQTBHQ1NxR1NJYjNEUUVCQ3dVQUE0SUJBUUNQVWVnUXpBQURlSUEzCm1GeDlXMm5UeVo2YmxNNUVjRFdXVmhzYStnN2tHdUQ5VzFjNUNEdHJPRFg0bTVYYTA5ZStwcGlhOHpHYWNnVWIKOEtzamtUaTFuNkdUam52d1lEck1rM1FFRGpFUzIrRTFhOWFPR1RJbElzU2NrMVlZUkZ1Z3FCWmdHWDdkRHVhLwpCUW9hOFd3SVRubUZqNXJVbFJ5SktQRFJqM1VpRVdpYWJRK2FwQTdlSGxuekhoMmFVU0hHc0laK28xZDBWVGNwCnhnY0QzY2g1T3ZQS08vanBTT0h6YjRsRkZCb3NwZVhHczJ2clVHQmsvVDJvSy83TC9kZGRaYitPSXhSZjdhNkMKVWowM1J2cW84S3A4d1NsaUZ4aXJFbzFVcGtGbWduMjZLZTBZbk5RNWo2VWtEaVZSbWJIT0NxckhSQnV2ZlBnVgp4bEd1M21XaAotLS0tLUVORCBDRVJUSUZJQ0FURS0tLS0tCg==
client-key-data: LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFb3dJQkFBS0NBUUVBbTZvMDF1N2RIYUdMa2MvQzhld2d5OUJTbTZtUzI1RjJEUWEzT052RloyWWdOOUhJCmNVUXhxZXVwV1VlcG5qcDM4UjFlcnd4WGpiaC9KVHV3cDFDbTE3TFk1Z05LeTVVNkswMDRvYXV5cVdDclNvOWQKMFRHd3o0WUJRWTNCTkFlUVJDWTFRZ3JlWitLM25haGxGeWx2VjdZaGsvZVNMRkl4QkM0clI0S2tWV0xpRUFNYgpaWndtUzl1YkhRZjBCUTgvYWUxTHMvMEd6d3NnVDhOTE14YU1NOExrYXJoMzlCbkhsVHRxcmFiRFNvWlp0bU5RCmFSd2hPemI1bExvdXNKankrZUx3R2N2UUFtQ3RsVlNFSXVvMWc4d0VzK01MSlAwb0xDSjEwZXgrdTRtemVUTEwKdHRmOHlzMzlPQ1BDNkJyTXlRUnc4OTduMlBScW5MQ2lHMU5LK1FJREFRQUJBb0lCQUQ4UDV6UWp0S1JxYTVaNApxcXREVTgzOTZWbHlpekkwYmJTOVFjRGhGOG5aejdlTlh6eXp1Y0x5MjdwMWs3dXNTQ2NBRlBtcGNGYlRwWDY1Ci9janFuWXpJd2FIOU4zSGVWS0J5T2owVXg5NWljVUpWYmxadllRZlJhL1RZcnFxYlhkQ2VBZmx0V2NpUVNuNnUKVjdYWWJXa0ZPZmt0MUtQcjhEdVhVS1U1d2NWdEZnWXFuQmtTSGJaRVBvM1k2UGxzSkVSMnZUNktQNVdqOXRLVAo4T1cxd1FSei9uYXJ1Q0ZBdzgrUjE5dlpEOWU3WUI4ZU80c2pIVTRVU2NvV1RET2NEYU9MZEhST1ZSVFZoZ0hSClQram5DRzdRcm9wTzdZWDhqK1dlZTJGeHVySFp1bU9Fa3VpbktGZnpMdGxXNjRpVmNkQUxHcnJVTU9Ubk1Tb0kKMUVlcFZIa0NnWUVBelI5aXM0RXhNU3Y0blREVFhNTE5nZG1NaGpUbGd1QU9XbSs0TFExcnRzZ1oraFpaeGZ3SwpzVXM4K2p0d0lueG1hVzVEMVZFd2hoNnUzckJWdWVQZElWZFhtVGZSc0FIL0tadDNQWXRPMWUrdk8rRFdaMiswCmxqRWJST2N4cVVvMHVNUDladXlGUEt0bzMvUVNTbjNBMklIVllOOG1EUjFUaCtXMjYwMFdYdGNDZ1lFQXdrWnEKcUdIY1RiR29YQWVPU3planZ5T3piVlhVQk5UU3BzT21RL3lIQ08xV1k0R1NHWDlVaFJNVFNvazY1Sm55NUVnMwpTbWdQVVBpSUd6ZGtPTmgwdzJNK0VTSXF5UTVxQXdjZWlXUWxxd0JPYU14Skl0eEdrTmRQVGhOWjdhL3N5SmhVCm9WbkhianNEeDBXWURDMVRnbWluRk01bkE2VFFjTEdZWFJJYWVxOENnWUJ5ckI4anR3L25LMnZiaE5aRXYycmcKTXR6S2tudlVoS25CaVQ5dmdGYzlZZlNUeVRiNjVnS2NSekdadXV6ZmVxaE9QS1NUZHNZbjFMTnlMeVpkdTdOOQoxalJVcGM0R0ZiZXViUWxtVUtFTUhPamNFc0FLSjNyUGxEaG9kczlla3V1U2Q0OE1vU0dEWDFoTUMwakdlREw5ClZ1Z1JOZTh4MmJrKytmOGU0SU9uRlFLQmdBeG41TDIxNmhTSUNNRS90a1YxV3g2RWtCdW1SSEMraW1rZHkwdEMKSC9sZzlvaEtLT001NzFMRUloSTdheWhYOEZ2RmhNcGFsTWZONXhzZDBXZVQ0dmpyS0haOW9RL1B2Tk5PckJPSAo4cVBWMUN2N0I1eVRSbXBQWllBTjJrdEVWYkdGa0xudytydytSb0orSGpTQTNIbFNaNEQ3b1RacFd1b25YUnhzCllJWi9Bb0dCQUpqS0wzblUvaHh5Zmk5SzJuWTJHQXBiUGtLZTRjclFNL010WkJPVytLSENndE9sbjZiWTcrTEkKbEtNQ3E3VGdqc1FOTENNUTVaaEFQYXh2bFpKNk5jT2JaNDhvOGY1cHdrQmVKblprRUkybU9NQlIyemdweXdCLwpqMnlCMUVxeW1mSmFrSjV2QjVEWGxvNklEYktjeEh2UG5jZVB1eVlyWWFZU1piejUvL3M3Ci0tLS0tRU5EIFJTQSBQUklWQVRFIEtFWS0tLS0tCg==
[root@master .kube]#
5.再次使用gaohui登录linux系统
[root@master .kube]# su - gaohui
[gaohui@master ~]$ kubectl get pods #不可以访问default命名空间
Error from server (Forbidden): pods is forbidden: User "gaohui" cannot list resource "pods" in API group "" in the namespace "default"
[gaohui@master ~]$
[gaohui@master ~]$ kubectl get pods -n gaohui-test #可以访问gaohui-test命名空间
No resources found in gaohui-test namespace.
[gaohui@master ~]$
退出gaohui用户返回到root用户,需要在把集群环境切换成管理员权限
[gaohui@master ~]$ exit
[root@master .kube]# kubectl config use-context kubernetes-admin@kubernetes #把集群环境切换成管理员权限
Switched to context "kubernetes-admin@kubernestes".
[root@master .kube]# kubectl get pod
NAME READY STATUS RESTARTS AGE
configmap-demo-pod 1/1 Running 11 2d5h
configmap-nginx 1/1 Running 1 2d5h
nginx 1/1 Running 1 2d5h
nginx-configmap-test 1/1 Running 1 2d4h
sa-lihaihui 1/1 Running 0 172m
sc-pv-pod-nfs 0/1 Error 0 2d6h
task-pv-pvc-pod 1/1 Running 1 2d11h
test-pd 1/1 Running 1 2d13h
test-pd-2 1/1 Running 1 2d13h
[root@master .kube]#






![[实践经验]: visual studio code 实用技巧](https://img-blog.csdnimg.cn/direct/c3f002412ee44b3c99a932380bd4115d.png)